Atlanta Computer Recycling: Secure ITAD Services in Sandy Springs

When managing corporate electronics in Sandy Springs, the process goes far beyond simple disposal. For any local organization, from the bustling offices in Perimeter Center to critical medical facilities, a secure and compliant IT Asset Disposition (ITAD) strategy is a non-negotiable component of corporate risk management. It's the critical step that separates responsible asset retirement from a catastrophic data breach.
The Strategic Approach to Commercial Electronics Recycling
Let's be pragmatic. When your office undergoes a tech refresh or a data center decommissions servers, that retired equipment cannot simply be discarded. These devices are repositories of proprietary business information, client records, or protected health information (PHI). A single misstep in handling these Sandy Springs electronics can lead to significant financial penalties and irreparable damage to your corporate reputation.
The primary threat isn't the physical hardware but the residual data contained within. Consider the implications—a single misplaced hard drive from a legacy server could expose your entire client database. This is precisely why a strategic approach to ITAD is not merely an operational expense; it is a fundamental security investment.
Beyond Disposal: A Focus on Corporate Risk Management
Viewing e-waste as a simple disposal task is one of the most common—and dangerous—oversights businesses make. A more astute framework is to treat it as a core component of your company's risk management and corporate responsibility initiatives. A well-executed ITAD program addresses several critical business objectives simultaneously:
- Data Security: It guarantees that every byte of sensitive data is permanently sanitized or destroyed, shielding your business from costly breaches.
- Regulatory Compliance: It provides the essential documentation, such as Certificates of Destruction, required to satisfy auditors and adhere to standards like HIPAA, SOX, and PCI DSS.
- Environmental Responsibility: It ensures hazardous materials are managed safely and valuable resources are recovered, bolstering your company's sustainability and ESG (Environmental, Social, and Governance) goals.
- Value Recovery: It identifies functional equipment that can be refurbished and resold, creating a revenue stream that can offset—or even exceed—the program's costs.
For a deeper dive into the entire process, resources on IT Asset Lifecycle Management offer a comprehensive overview, covering technology from procurement to end-of-life.
The core of a successful ITAD strategy lies in a simple mindset shift: from "disposing of old equipment" to "securely and responsibly retiring corporate assets." This approach protects your data, your brand, and your bottom line.
Who Requires a Professional ITAD Partner?
Any organization that manages sensitive information or handles a significant volume of technology requires a professional partner. This encompasses a broad spectrum of businesses throughout the Sandy Springs area.
To provide a clearer picture, we've outlined our core ITAD services and the business profiles they are designed for.
ITAD Service Overview for Sandy Springs Businesses
| Service Component | Description & Benefit | Ideal For |
|---|---|---|
| Secure Logistics & Pickup | We manage on-site de-installation and secure, chain-of-custody transport of your assets, freeing up your internal teams. | Law firms, corporate headquarters, and any business executing a technology refresh. |
| Certified Data Destruction | We provide documented, irreversible data sanitization (NIST/DoD standards) and physical shredding to eliminate all data security risks. | Medical centers, financial institutions, and government contractors with stringent compliance mandates. |
| Asset Recovery & Resale | We test, grade, and refurbish functional equipment, sharing the remarketing revenue back with you to maximize your ROI. | Companies with large volumes of newer, high-value IT assets such as servers, laptops, and networking gear. |
| Responsible Recycling | All non-reusable materials are processed through R2 or e-Stewards certified channels, ensuring environmental compliance. | Any organization committed to achieving its corporate social responsibility (CSR) and sustainability targets. |
This table provides a high-level overview, illustrating how a tailored ITAD program addresses specific business challenges.
For example, a medical practice near Northside Hospital must ensure patient data is destroyed to maintain HIPAA compliance. A financial services firm in the Concourse Corporate Center requires a fully auditable process to protect client data during an office-wide computer upgrade. Our specialized programs for business electronics recycling are engineered for these exact scenarios. This guide will detail the practical steps to implement such a program.
Asset Acceptance: Our B2B Specialization
To ensure your electronics recycling project in Sandy Springs is executed efficiently, it is crucial to understand the types of equipment we handle. This is not merely a checklist; it's about aligning our specialized B2B services with your corporate assets to prevent logistical complications and operational delays.
Our focus is exclusively on business-to-business (B2B) IT asset disposition. Our infrastructure is designed to manage the technology that powers your organization, which means we do not process residential items like personal televisions or consumer appliances. Our expertise lies in managing the end-of-life cycle for corporate IT hardware, ensuring data security and responsible recycling at scale.
Core Business IT Assets We Manage
The majority of equipment we process for corporate clients falls into several key categories. Our systems are optimized to handle these assets in bulk, recover maximum value where possible, and ensure compliant disposal for all remaining materials. If your Sandy Springs office is decommissioning any of the following, we are the right partner for you.
- Computers and Laptops: All enterprise-grade desktops, towers, all-in-ones, and notebooks.
- Servers and Data Center Equipment: This includes rack-mounted servers, blade servers, storage area networks (SANs), and related data center infrastructure.
- Networking Equipment: Enterprise switches, routers, firewalls, and access points that form your company's network backbone.
- Standard Office Peripherals: Business-grade assets like keyboards, mice, docking stations, and LCD/LED computer monitors.
Understanding our core focus allows you to compile a more accurate inventory, making our initial consultation significantly more productive.
The objective is clarity from the outset. By defining our scope of accepted assets, we help you accurately inventory your retired technology, leading to a faster quote, a more organized pickup, and a seamless project from start to finish.
Clarifying Service Scope and Exclusions
Not all electronics are created equal, and certain equipment falls outside our B2B IT specialty. For instance, we typically do not accept large industrial machinery, consumer appliances, or hazardous materials like CRT monitors, as they require distinct handling and disposal protocols. Our operations are fine-tuned for the high-density data and materials found in corporate IT equipment.
This distinction is important—it optimizes efficiency for both parties. Attempting to recycle non-IT industrial equipment through an ITAD provider is inefficient. Similarly, co-mingling residential e-waste complicates the secure chain of custody that is paramount for protecting corporate assets.
Here is a quick reference for items that often require clarification:
| Item Type | Our Acceptance Policy | Rationale & Guidance |
|---|---|---|
| Specialized Medical Devices | Case-by-case basis. We accept IT components (computers, monitors) but not the core diagnostic machinery itself. | Medical equipment often has unique decontamination and disposal regulations. We manage the integrated IT hardware and can direct you to specialists for the core medical units. |
| Printers & Copiers | Accepted. We process office printers, scanners, and large multi-function copiers. | These are standard business assets. We ensure any internal hard drives are securely sanitized or destroyed to protect sensitive scanned or printed data. |
| Mobile Devices | Accepted. We process smartphones and tablets in bulk. | These devices store significant corporate data and require the same level of certified data destruction as laptops or servers. |
| Industrial Control Systems | Generally Not Accepted. This includes PLCs, SCADA systems, and large-scale manufacturing robotics. | These fall under industrial recycling, which involves different logistics and dismantling processes than standard Sandy Springs electronics. |
By clarifying these points, we empower IT and facility managers to build a precise inventory list. For a complete and detailed breakdown, you can review our full guide on accepted items for recycling, which provides further specifics. This preparation is key to a successful partnership and ensures every piece of equipment is routed through the proper, compliant channels.
Choosing the Optimal Data Destruction Method
When your Sandy Springs business retires its electronics, the most critical step is ensuring the absolute and permanent eradication of all stored data. Simply deleting files is insufficient, as that data is often easily recoverable. Professional data security relies on two primary methods: software-based data sanitization and physical destruction. The optimal choice depends on the type of assets, your security requirements, and your value recovery objectives.
This decision is more critical than ever. The ITAD field is expanding in response to demands for stricter data security and environmental compliance. The global e-waste management market is projected to grow from USD 70 billion in 2024 to USD 81.27 billion in 2025—a 16.1% year-over-year increase reflecting the seriousness with which businesses now approach data security.
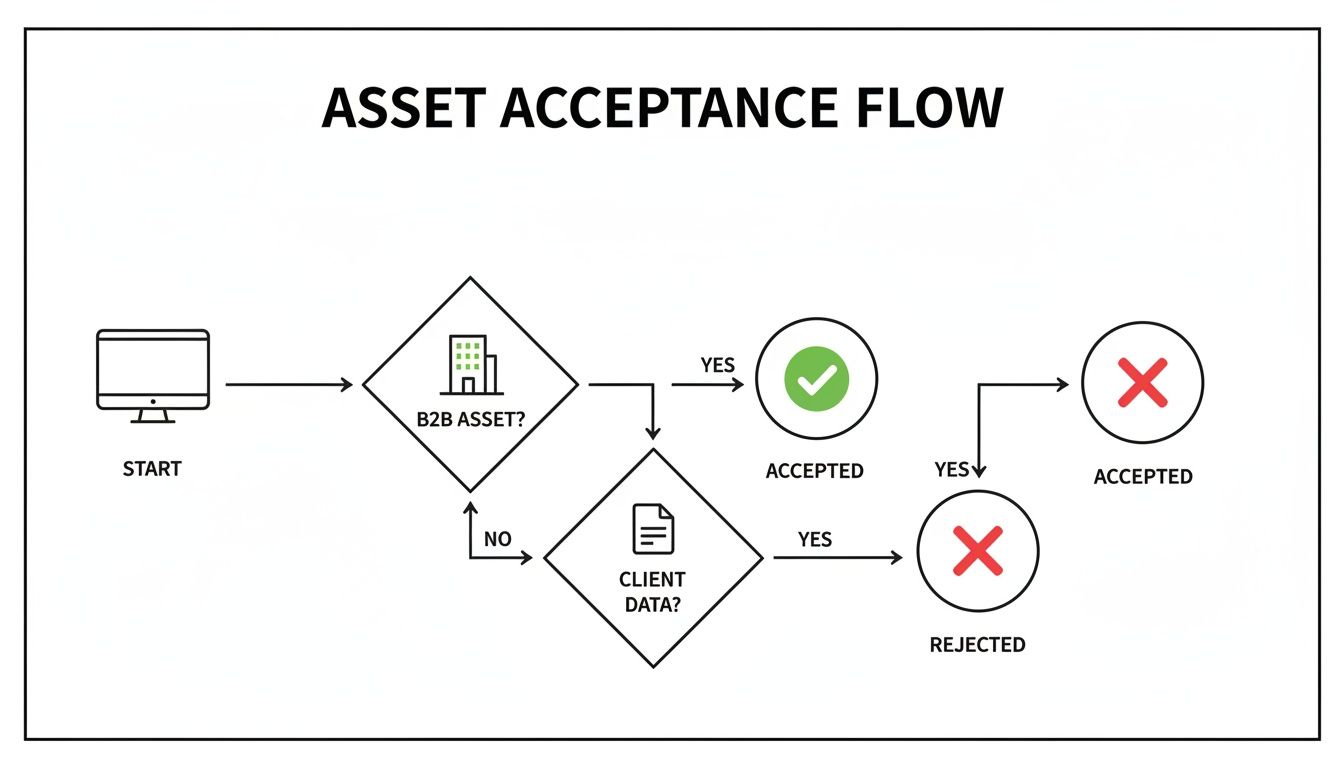
This flowchart illustrates our B2B asset intake process, the first step before any data destruction occurs.
As shown, our process is designed to rapidly identify and accept commercial IT hardware, moving it directly into the secure data destruction phase.
When to Utilize Data Sanitization
Data sanitization, or wiping, uses specialized software to overwrite every sector of a storage device with random data. We adhere to the DoD 5220.22-M 3-pass standard or NIST 800-88 guidelines, rendering the original data forensically unrecoverable. This is the ideal approach for newer, functional hard drives and solid-state drives (SSDs).
This method preserves the hardware's integrity, making it a crucial step for assets that retain resale value.
- Scenario 1: Corporate Technology Refresh: A software company in Perimeter Center replaces 100 two-year-old developer laptops. The hardware is functional and holds market value.
- Solution: DoD-standard sanitization is the optimal choice. It guarantees all proprietary code and internal documents are obliterated while keeping the hardware intact for refurbishment and resale. This allows the company to recoup a significant portion of its initial investment.
- Scenario 2: Educational Institution Upgrade: A local school system is retiring a computer lab of iMacs. The machines are functional but being replaced with current models.
- Solution: Sanitization ensures all student and administrative data is securely removed. The computers can then be resold to help fund new technology, maximizing the district's budget.
The key benefit is the strategic balance between absolute data security and financial return, transforming a disposal cost into a revenue opportunity.
The Definitive Solution: Physical Shredding
In cases where hardware preservation is not a priority or the security risk is paramount, physical destruction is the solution. This process employs an industrial shredder to reduce hard drives, SSDs, backup tapes, and other media into small, irrecoverable fragments. It is the only 100% foolproof method of data destruction.
Shredding provides undeniable proof of compliance.
For organizations handling highly sensitive information governed by regulations like HIPAA or Sarbanes-Oxley, physical shredding is often the mandated or preferred method. It eliminates all doubt and provides a clear, auditable trail of destruction.
Shredding is the necessary choice in these situations:
- Non-functional or Damaged Drives: If a hard drive has failed or is physically damaged, software-based sanitization may not be possible. Shredding is the only way to guarantee data destruction.
- Strict Compliance Mandates: A healthcare provider near Northside Hospital retiring servers containing electronic Protected Health Information (ePHI) must adhere to HIPAA's stringent disposal rules. Physical shredding offers the highest level of security and provides a Certificate of Destruction that satisfies any audit.
- End-of-Life Corporate Policy: Many organizations have internal security policies that mandate physical destruction for all data-bearing devices, regardless of age or condition. This zero-risk approach simplifies compliance and eliminates any possibility of a data leak.
Selecting between these two methods is a core component of responsibly managing your Sandy Springs electronics. Our experts can help you analyze your inventory and determine the most secure and cost-effective path for every asset. You can find more details on our approach to secure data destruction and how we tailor it to meet your specific business requirements.
Managing Logistics and Compliance Documentation
Successfully retiring your company's electronics involves more than just equipment removal. For IT and facility managers in Sandy Springs, the critical work lies in managing logistics and securing the correct compliance documentation. This paperwork serves as your official record, proving that you have handled every asset in accordance with legal and corporate standards.
The entire process, from pickup at your facility to final certification, is a carefully orchestrated logistical operation. Understanding the basic principles of logistics management helps contextualize how each step—scheduling, transport, documentation—interconnects to create a secure and fully auditable trail for your retired Sandy Springs electronics.
This methodical approach is increasingly important. The global electronics recycling market, valued at USD 43.2 billion in 2025, is projected to reach USD 147.9 billion by 2035. This growth brings heightened regulatory scrutiny, making it crucial to partner with a certified vendor who understands the compliance landscape.
The Documentation That Protects Your Business
In the event of an audit, verbal assurances are insufficient—documented proof is required. In any ITAD project, two documents are indispensable.
-
Chain-of-Custody Records: This document provides a chronological record of your assets. It tracks your equipment from the moment it leaves your Sandy Springs facility to its final disposition, detailing who handled it, where it was transported, and when it was processed. An unbroken chain of custody is essential for proving you maintained control over sensitive data at all times.
-
Certificate of Destruction (CoD): This is the definitive legal document. It officially confirms that data-bearing devices were securely and permanently destroyed. It lists the serial numbers of the shredded hard drives and confirms the date and method of destruction, making it a non-negotiable requirement for meeting standards like HIPAA and SOX.
These documents are not mere formalities; they are your legal shield. Failure to produce them can result in severe fines, particularly for businesses in regulated industries like healthcare, finance, or government contracting. You can learn more about what a properly executed Certificate of Destruction entails and why it is the cornerstone of any compliant ITAD strategy.
View your compliance paperwork as an insurance policy. You hope you never need it for a legal dispute or audit, but if you do, it is the one thing that will definitively prove you acted responsibly.
On-Site Logistics Designed for Zero Business Disruption
We understand that your business operations cannot be interrupted for a technology upgrade. Our on-site logistics are designed to work around your schedule, not interfere with it. Our team manages every aspect of the physical removal process.
Here is what our service entails:
- Professional De-installation: Our technicians will safely disconnect and remove equipment from server racks and workstations. This frees your IT staff from the labor-intensive task of unplugging and moving heavy, cumbersome gear.
- Organized Packing and Palletizing: We arrive with all necessary materials—pallets, bins, and shrink wrap—to securely pack your assets on-site. This ensures an orderly and efficient loading process.
- Scheduled and Secure Pickup: We coordinate a pickup time that minimizes disruption to your team and daily operations. Our trained drivers and secure vehicles ensure your assets are protected from the moment we arrive.
A Real-World Scenario in Sandy Springs
Imagine your company is relocating its office within the Perimeter Center. You are left with dozens of old desktops, a server rack of outdated hardware, and boxes of networking gear. Your facility manager is already managing multiple vendors under a tight deadline.
This is where our coordinated approach excels. Our team would:
- Schedule a pre-move site survey to assess the inventory and building access.
- Arrive on the agreed-upon day with a crew to handle de-installation and packing, working in designated zones to avoid interfering with movers.
- Securely load all equipment and provide you with an initial chain-of-custody document before leaving the premises.
- Transport the assets to our secure facility for data destruction and processing.
- Deliver the final Certificate of Destruction within a few business days, closing the compliance loop well before your team has finished unpacking at the new location.
What could have been a major logistical challenge becomes a simple, checked-off item on your relocation project plan.
Understanding Project Timelines and Pricing Models
When planning for IT asset disposition, two questions are always top of mind: "How long will this take?" and "What will it cost?" For any business in Sandy Springs, budgeting and scheduling are paramount. The answer depends on project specifics, and we believe in complete transparency about how we determine those specifics.
A one-size-fits-all price does not exist because no two projects are identical. The primary drivers for both your timeline and cost are the scope and complexity of the engagement. A straightforward pickup of fifty laptops from a ground-floor office is fundamentally different from decommissioning five full server racks in a secure, high-rise data center.
Factors That Determine Project Cost
The price for managing your retired Sandy Springs electronics is a careful calculation based on the labor, logistics, and specific services required to ensure your business remains secure and compliant.
Here are the primary factors we assess when developing your quote:
- Quantity and Type of Equipment: Is this a single pallet of desktops or a full data center cleanout with servers, switches, and UPS units? Heavier, bulkier items like server racks require more personnel and specialized equipment for safe de-installation and transport.
- On-Site Services Required: If your team has already handled the disconnection and palletizing of assets, your costs will be lower. However, most clients require our crew to perform the full de-installation, which involves more on-site time and technical expertise.
- Building Accessibility: Logistics are a significant cost factor. A pickup from an office with a dedicated loading dock is far simpler than a project on the 20th floor of a downtown building with restricted service elevator access. We always factor in these on-site conditions.
- Data Destruction Method: Your security requirements dictate the method, which in turn impacts the cost. While both our software-based sanitization and physical shredding are completely secure, the processes and labor involved differ, and this is reflected in the pricing structure.
It is important to view professional ITAD as an investment in data security and regulatory compliance, not just a disposal fee. The cost directly reflects the resources required to shield your business from tangible risk.
The Impact of Asset Value Recovery
This is where the financial equation can shift significantly in your favor. For many businesses, a professional electronics recycling project can become cost-neutral or even generate revenue through asset value recovery.
We are experts at identifying equipment in your inventory that, despite being retired, retains market value. Newer-generation laptops, servers, and networking gear can be securely sanitized, refurbished, and sold on the secondary market. A portion of the revenue generated is shared back with you, which can offset—or sometimes entirely cover—the cost of recycling older, zero-value assets. This transforms a necessary expense into a strategic financial decision.
A Sample Timeline for a Sandy Springs Office Cleanout
To illustrate how a typical project unfolds, let’s review a timeline for a mid-sized office cleanout involving 100 desktops, a few servers, and associated peripherals.
- Initial Quote & Consultation (1-2 Business Days): The process begins when you provide an inventory list. We will conduct a brief consultation call to discuss your needs, clarify required services like on-site de-installation, and provide a detailed, itemized quote.
- Scheduling the Pickup (2-3 Business Days): Upon quote approval, we coordinate directly with your office or facility manager to schedule a pickup date that minimizes disruption to your business operations.
- On-Site Service & Transport (1 Day): Our uniformed, professional team arrives on the scheduled day to manage all de-installation, packing, and secure loading. You will receive the initial chain-of-custody documentation before we depart.
- Processing & Data Destruction (3-5 Business Days): At our secure facility, every asset is inventoried and sorted. All data-bearing devices are then sanitized or physically shredded according to the agreed-upon plan.
- Final Reporting & Certification (1-2 Business Days): To complete the project, we issue the official Certificate of Destruction and a final settlement report detailing any asset value recovery.
From the initial call to receiving your final documentation, a standard project of this nature is typically completed within 7 to 10 business days. We have refined this process for maximum efficiency, ensuring your retired assets are handled securely and without becoming a lingering operational burden.
How to Initiate Your Recycling Project
Initiating a responsible recycling plan for your company’s Sandy Springs electronics is a straightforward process that begins with a simple consultation. We will learn about your specific needs, and you will learn how we can securely manage your end-of-life assets. No complex forms or technical jargon—just a clear, direct path to a solution.
The process begins the moment you contact us. A rough inventory of the equipment you need to dispose of—such as desktops, servers, or monitors—is always helpful. Even approximate counts enable us to prepare a faster, more accurate quote tailored to your specific project. Our objective is not just to pick up equipment; it is to serve as a partner, answering every question you have throughout the process.
A staggering 62 million tonnes of e-waste was generated globally in 2022, yet only 22.3% was properly collected and recycled. This gap represents not only an environmental issue but also a significant security risk for any business without a compliant disposal strategy, as highlighted by the Global E-waste Monitor 2024.
From our initial conversation, we will work with you to design a solution that meets all your criteria—security, logistics, and budget. Taking the first step toward responsible electronics disposition should be simple. To begin the process, you can easily schedule a pickup online.
Frequently Asked Questions
When retiring corporate technology, asking detailed questions is a sign of due diligence. It indicates a serious approach to data security, compliance, and responsible disposal. Here are some of the most common questions we receive from businesses in Sandy Springs regarding IT asset disposition.
Is There a Cost for Business Electronics Recycling?
For most corporate clients, our services are either low-cost or generate a net positive return. The final cost depends on the volume and, more importantly, the resale value of the equipment. Newer assets, like recent-generation laptops and servers, often possess sufficient market value to offset the entire cost of the service through revenue sharing.
Conversely, items with no resale value that require manual de-manufacturing—such as old printers or obsolete peripherals—may incur a nominal processing fee. We always provide a transparent, itemized quote upfront, ensuring there are no surprises. This allows for clear budgeting for your Sandy Springs electronics disposition project.
The key takeaway is that value recovery from newer assets can often render the entire project cost-neutral. What may appear as an expense can become a strategic financial move, enabling you to recoup value from retired hardware.
How Do You Ensure HIPAA Compliance for Medical Facilities?
We adhere to a strict, documented chain-of-custody protocol to ensure HIPAA compliance, from the moment we arrive at your facility until the final certificate is delivered. Any device or media that could potentially contain electronic Protected Health Information (ePHI) is handled with the highest level of security.
For absolute certainty and to meet HIPAA's stringent requirements, we always perform and recommend physical hard drive shredding. This process makes data 100% irrecoverable by any means and creates a clear, auditable trail. Upon completion, we issue an official Certificate of Data Destruction, which serves as your verifiable proof of compliance for any future audit.
What Happens to Our Electronics After Pickup?
Our entire process is founded on the "reuse, recover, recycle" hierarchy, and we maintain a zero-landfill policy for all e-waste we handle.
Here is a brief overview of our process:
- Audit and Triage: Upon arrival at our facility, we audit every asset to determine its potential for reuse.
- Reuse and Remarketing: Functional equipment is securely sanitized using DoD or NIST standards. It is then refurbished and sold into secondary markets, extending its useful life.
- Responsible Recycling: Any non-functional or zero-value equipment is carefully de-manufactured. Commodities like steel, aluminum, plastic, and precious metals are separated and sent to our certified downstream partners to be refined back into raw materials.
This comprehensive approach not only protects your sensitive data but also helps your organization achieve its corporate sustainability goals by transforming end-of-life technology back into a valuable resource.
Ready to manage your retired IT assets with a secure, compliant, and cost-effective strategy? The team at Atlanta Computer Recycling is here to help your business.
Learn more and schedule your consultation at https://atlantacomputerrecycling.com.