Marietta Computer Recycling: A Strategic Guide for IT Asset Disposition
For any Marietta business, decommissioning old computers and IT hardware is a mission-critical operation. This isn't just about clearing out a storage room; it's about certified data destruction, regulatory compliance, and maximizing operational efficiency. Improper disposal of IT assets isn't just a cleanup failure—it's a strategic misstep that exposes your organization to significant financial and reputational risks.
Crafting Your IT Asset Disposition Strategy
As an IT manager, operations lead, or C-level executive, you understand the technology lifecycle: new assets are procured and deployed, while old ones must be retired. That final phase, IT Asset Disposition (ITAD), carries immense responsibility. A robust ITAD plan is not an afterthought; it is a formal strategy aligned with your core business objectives. Before engaging a partner for Marietta computer recycling, you must define what a successful project outcome looks like for your company.
Is the primary driver to ensure absolute data security to comply with regulations like HIPAA or GLBA? Are you decommissioning entire server rooms as part of a data center consolidation or office relocation? Or is the objective to maximize the recovery value from still-viable equipment? Establishing these priorities upfront will inform every subsequent decision in the disposition process.
Defining Your Project Objectives
Before contacting a recycling partner, it's vital to align your internal stakeholders. This step ensures everyone from the IT department to the CFO understands the project's goals and metrics for success.
Most commercial clients we serve focus on these key objectives:
- Data Security Assurance: Guaranteeing that every byte of sensitive corporate, customer, or patient data is forensically and permanently destroyed. This is a zero-tolerance requirement.
- Regulatory Compliance: Satisfying all local, state, and federal regulations for both data privacy and environmental e-waste disposal to mitigate the risk of severe penalties.
- Operational Efficiency: Executing the equipment removal with minimal disruption to daily business operations and internal workflows.
- Asset Value Recovery: Identifying newer or high-value assets suitable for refurbishment and resale, thereby generating ROI to offset project costs.
A well-defined strategy transforms ITAD from a logistical challenge into a streamlined, auditable business process. It provides a clear roadmap, ensuring security and compliance are addressed before a single asset is taken offline.
Knowing your goals enables you to ask the right questions and select a partner capable of meeting your specific requirements.
The Importance of a Detailed Inventory
With your objectives defined, the next phase is creating a detailed inventory of every asset slated for disposition. This goes beyond a simple count like "50 computers." It requires documenting the make, model, serial number, and asset tag of each individual unit.
Consider a Marietta-based law firm upgrading its office technology. A simple list of "50 desktops" is insufficient. A detailed manifest is required for chain-of-custody tracking. Furthermore, every device containing a hard drive or SSD must be flagged for certified data destruction.
This meticulous inventory process delivers several key benefits:
- It provides an accurate scope for generating precise quotes and planning logistics.
- It helps identify which assets may have residual market value.
- It forms the foundation of a secure and fully documented chain of custody.
The final element is proper asset tagging. By assigning a unique identifier to each item, you can track a specific desktop from an employee's desk, through transit, to the recycling facility, and confirm its data destruction on the final certificate. For maximum efficiency, this ITAD plan should be integrated with a comprehensive IT Asset Management (ITAM) strategy. Proper upfront planning is the key to a secure, compliant, and cost-effective disposition project.
Executing a Seamless Equipment Decommissioning
Once your strategy is finalized, it's time for execution. This is where the plan transitions from paper to physical reality—where IT assets are disconnected, prepared for transport, and staged for pickup. The objective is precise execution with zero disruption to your business while ensuring every asset, from a single mouse to an entire server rack, is handled securely.
For many businesses, the primary challenge is decommissioning equipment within a live operational environment. Imagine a busy Marietta healthcare clinic needing to replace dozens of workstations. Unplugging cables during patient hours is not an option. This makes scheduling paramount, often requiring the work to be performed during off-hours or on weekends to avoid interrupting critical business functions.
A clear, well-communicated schedule is your most valuable tool. Informing department heads of the timeline for their areas helps prevent operational chaos and ensures a smooth process.
The Art of On-Site De-Installation
The physical process of disconnecting and removing equipment varies dramatically based on the asset type and its location. Removing a few desktops from an administrative office is straightforward; decommissioning a full server rack is a complex technical procedure. Servers are heavy, intricately cabled, and often housed in tight data closets, making their removal a task for trained specialists.
Let's break it down by asset type:
- Workstations: This typically involves a systematic process of disconnecting peripherals (monitors, keyboards, mice), unplugging the tower, and bundling all associated cables.
- Server Racks: This is a highly technical task. It requires powering down servers in a specific sequence, carefully disconnecting a complex web of network and power cables, and physically un-mounting each heavy chassis. This is a task best left to a professional team to prevent damage to the equipment, your facility, or your personnel.
A qualified partner for Marietta computer recycling will collaborate with your team to develop a de-installation plan tailored to your specific environment. For large-scale projects, like a full data center clean-out, a detailed project plan is essential. You can find excellent guidance in this server decommissioning checklist that outlines the entire process.
Best Practices for Packing and Staging
After disconnection, hardware cannot simply be piled in a corner. Proper packing and staging are crucial to protect assets from damage and ensure an efficient pickup. Damaged equipment loses all potential resale value and can pose a safety risk.
Consider a school district refreshing a computer lab with 300 new laptops. The retired units must be packed securely to prevent screen and case damage during transit. The industry standard for handling large quantities involves using sturdy pallets and shrink wrap to create stable, transportable units.
Your staging area should be a designated, low-traffic location with easy access for the logistics crew. This prevents the equipment from becoming a workplace hazard and guarantees a rapid, organized removal.
Here’s a real-world example: A Marietta-based software company relocating its headquarters needed to clear out its entire server room. They coordinated with their ITAD partner to schedule the de-installation for a Saturday. The professional team arrived, systematically dismantled the racks, palletized all servers and networking hardware, and staged everything by the loading dock.
This strategic planning meant that on Monday morning, the logistics crew could load the pallets onto the truck without interfering with the company’s other moving activities. It is this level of coordination that prevents logistical bottlenecks and keeps your project on schedule and within budget.
Guaranteeing Absolute Data Security and Destruction
Once your equipment is decommissioned and staged, the project moves to its most critical phase: data destruction. For any business handling sensitive information—especially in the healthcare, financial, or legal sectors—this is not merely about disposing of old hardware. It is about the irrefutable destruction of data to protect your company, your clients, and your brand reputation.
Many assume that hitting "delete" or reformatting a hard drive is sufficient. It is not.
These methods leave data remnants that are easily recoverable, creating a significant liability. A single data breach can result in millions in fines and penalties, but the damage to customer trust can be irreparable. This is why a verifiable, certified data destruction process is non-negotiable. It is the only way to meet strict compliance standards like HIPAA and obtain documented proof that your sensitive data has been permanently eliminated.
DoD Wiping vs. Physical Shredding
When it comes to permanent data erasure, there are two industry-standard methods. The optimal choice depends on the condition of your storage media and your organization's internal security policies.
- DoD 5220.22-M 3-Pass Data Wiping: This is a software-based sanitization process that overwrites the entire hard drive with specific patterns of ones and zeros multiple times. It is the ideal solution for functional hard drives that may be resold or redeployed, as it preserves the hardware's value while rendering the original data completely unrecoverable.
- Physical Shredding: For drives that are end-of-life, non-functional, or hold no resale value, physical destruction is the definitive solution. We use industrial shredders to grind the media into small, mangled pieces of metal, making data recovery physically impossible.
Your data security strategy should be guided by a formal data retention policy. This internal governance document specifies how long different types of data must be kept before it can be securely destroyed, ensuring both compliance and organizational discipline.
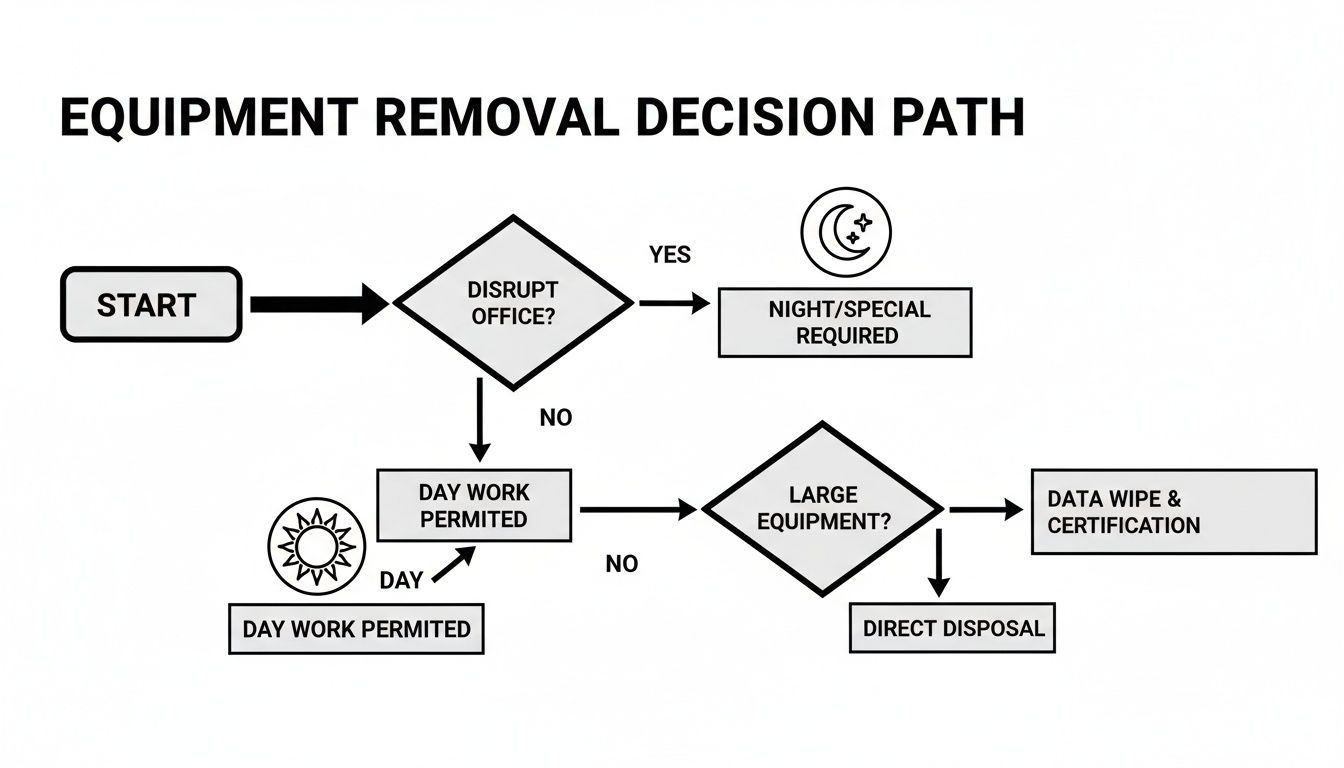
Sometimes, the simplest logistical decisions make the biggest difference. The decision tree below shows how we think through equipment removal to minimize disruption to your office.
As you can see, planning for things like working after hours or on weekends can make the entire project run smoothly without interrupting your team.
Choosing between wiping and shredding depends entirely on your needs. Here's a quick comparison to help you decide.
Data Destruction Methods Compared
| Method | Best For | Compliance Level | Key Benefit |
|---|---|---|---|
| DoD 5220.22-M Wiping | Functional HDDs and SSDs intended for reuse or resale. | High (Meets HIPAA, FACTA, SOX, etc.) | Preserves the hardware's value for remarketing. |
| Physical Shredding | Non-functional, damaged, or obsolete drives. | Absolute (Exceeds all compliance standards) | Complete physical destruction, leaving no doubt. |
Ultimately, both methods deliver certified, compliant results. Wiping allows for potential value recovery, while shredding provides ultimate finality.
The Power of Certified Proof
Regardless of the method chosen, the process is incomplete without proper documentation. A reputable ITAD partner will always provide a Certificate of Data Destruction upon completion. This is not a mere receipt; it is a legal document that serves as your official record of compliance and due diligence.
This certificate is your ultimate safeguard.
Should you ever face a regulatory audit, this certificate is your definitive proof that you adhered to industry best practices and fulfilled your data security obligations. It closes the chain of custody loop and transfers liability away from your organization.
For organizations that demand absolute certainty, we offer full transparency. You can learn more about our specific processes for secure data destruction and see exactly how we deliver peace of mind. Without certified documentation, you leave your business exposed. It’s the final, crucial step in protecting your data.
Staying Compliant and Environmentally Responsible
When you transfer custody of your retired IT equipment, you are entrusting a partner with your company's commitment to legal and ethical standards. For any business in Marietta, computer recycling is a mandatory process governed by a complex framework of data privacy laws and environmental regulations.
Non-compliance carries severe consequences. A single improperly sanitized hard drive can lead to a catastrophic data breach, resulting in crippling fines, litigation, and irreparable damage to your brand. Furthermore, electronic assets cannot be disposed of in landfills; they contain hazardous materials regulated by strict environmental laws.
The High Stakes of Data Privacy Compliance
For regulated industries, the rules are non-negotiable. A healthcare provider in Marietta, for example, must adhere to the Health Insurance Portability and Accountability Act (HIPAA), a federal law mandating the protection of all patient health information (PHI)—a requirement that extends through the device's entire lifecycle to its final disposal.
A breach of PHI can trigger fines reaching into the millions. This makes your choice of an ITAD partner critical; they must demonstrate a deep understanding of and adherence to HIPAA's stringent data destruction protocols. The same applies to law firms, financial institutions under GLBA, and any business handling sensitive customer data (PII).
The true cost of a data breach extends far beyond the initial fine. It includes long-term loss of customer trust, protracted legal battles, and reputational damage that can take years to rebuild.
This is precisely why a documented chain of custody and a certified proof of data destruction are indispensable. They provide tangible evidence that you have met your legal duty to protect sensitive information.
Facing the Global E-waste Challenge
Beyond data security, a growing environmental crisis makes responsible disposal an ethical imperative. Electronic waste (e-waste) is one of the fastest-growing waste streams on the planet, containing toxic materials like lead, mercury, and cadmium. If landfilled, these substances can leach into soil and groundwater.
The scale of this issue is staggering. The U.S. generates 6.92 million tonnes of e-waste annually—the second-highest total globally—yet our recycling rate is only about 15%. This is not only a major environmental problem but also represents a massive loss of valuable, recoverable resources. You can learn more about the environmental impact of electronic waste and why corporate responsibility matters.
Why R2 and E-Stewards Certifications Matter
How can you verify that a partner for Marietta computer recycling is handling your assets correctly? The answer lies in third-party certifications. These credentials are the definitive indicator that a recycler adheres to the highest industry standards for both data security and environmental stewardship.
The two most respected certifications are:
- R2 (Responsible Recycling): This certification establishes a comprehensive set of standards covering worker health and safety, data security protocols, and a documented chain of custody. An R2-certified facility undergoes regular, rigorous audits to verify its compliance.
- e-Stewards: Often considered the gold standard, e-Stewards places a strong emphasis on preventing the illegal export of hazardous e-waste to developing nations and maintains extremely strict requirements for data destruction and environmental protection.
Partnering with a certified recycler provides assurance. You know your retired assets will not end up in a landfill or be improperly exported, and you can trust that your data is being managed by professionals held accountable by stringent, independent audits. These certifications are your guarantee that your company is part of a responsible, global solution.
Why an ITAD Partnership is an Investment, Not an Expense
When Marietta businesses consider computer recycling, the first question is often about cost. While understandable, viewing this service purely as an expense misses the larger strategic value.
Engaging a professional IT Asset Disposition (ITAD) partner is a strategic investment in your company's security, compliance, and risk management framework. It protects you from liabilities that are far more costly than any recycling project.
Beyond a Simple Pickup Service
A standard hauling service will remove old equipment from your office. In contrast, a true ITAD partnership provides a documented, secure, and auditable process from the moment we enter your facility to the final disposition report. This is the critical distinction between merely disposing of assets and actively protecting your organization.
A professional partner delivers certified services that shield you from the financial and reputational damage of data breaches and environmental non-compliance.
Here’s what differentiates a dedicated ITAD partner from a basic hauler:
- Asset Tracking: We inventory and track every serialized asset, creating a secure and unbroken chain of custody from your site to its final destination.
- Certified Data Destruction: You receive verifiable proof that all data has been permanently destroyed using methods like DoD 5220.22-M wiping or physical shredding. This is a core component of the service, not an optional add-on.
- Detailed Reporting: We provide comprehensive documentation, including serialized reports and Certificates of Data Destruction, which are essential for audits and internal compliance records.
The true value of an ITAD partnership lies in risk transference. By hiring a certified expert, you offload the immense liability associated with data security and environmental regulations, freeing your team to focus on core business activities.
The demand for this level of secure, accountable service is growing. Regulatory scrutiny is intensifying, and e-waste volumes are skyrocketing. The global electronic waste recycling market is projected to reach USD 251.9 billion by 2034, driven largely by these regulatory pressures. Industry analysis reveals a clear trend: businesses are shifting from simple disposal to professional, accountable ITAD solutions.
Breaking Down the Costs and Finding the ROI
The cost of a professional ITAD project is based on several key factors. Understanding these variables allows you to see the value proposition and how the project can align with your budget.
Three main factors typically determine the cost:
- Scope and Complexity of Equipment: The total volume of hardware is a primary driver, but so is its complexity. Decommissioning a single server rack, for example, is more labor-intensive than collecting 50 desktop computers.
- Logistical Requirements: Does the project require our team to perform on-site de-installation? Are the assets located across multiple floors or within a secure data center? These logistical details influence the time and labor required.
- Asset Value Recovery: This is where you can realize a direct return on investment. Newer, functional equipment can often be refurbished and sold on the secondary market. The revenue generated from remarketing can significantly offset—and in some cases, completely cover—the costs of the project.
By working with an ITAD specialist, you gain access to established remarketing channels that maximize the return on your retired assets. To offset project costs, it is prudent to explore your options for Atlanta IT asset liquidation and determine the potential value hidden in your IT inventory.
Ultimately, investing in a secure, compliant ITAD program is not about avoiding fines. It's about protecting your brand, your data, and your bottom line.
Your Marietta Computer Recycling Questions, Answered
When you are ready to engage a professional partner for IT asset disposition, several key questions invariably arise. From IT managers to operations directors here in Marietta, all stakeholders need assurance they are making the right decision for their company's security, compliance, and budget.
We understand that every ITAD project is unique. Our goal is to provide the clarity you need to proceed with confidence, knowing every detail will be handled professionally. Here are the answers to the questions we hear most frequently from our commercial clients.
What Types of Electronic Equipment Can You Recycle?
This is typically the first question we receive. The short answer is: we manage the entire spectrum of corporate IT assets. Our services are designed specifically for commercial clients, focusing on the equipment that powers your business.
We securely and responsibly manage the disposal of:
- Computers and Laptops: Desktops, workstations, and notebooks of all manufacturers.
- Servers and Data Center Gear: Rack-mounted servers, blade servers, storage area networks (SANs), network-attached storage (NAS), and related infrastructure.
- Networking Equipment: Switches, routers, firewalls, hubs, and wireless access points.
- Peripherals and Monitors: LCD monitors, printers, scanners, keyboards, and mice.
- Mobile Devices: All corporate-owned smartphones and tablets.
If it was part of your IT infrastructure, we have a secure, documented process for its end-of-life management.
How Do You Ensure Our Data Is Completely Destroyed?
Data security is the cornerstone of our service, not just a feature. We guarantee complete data destruction using proven, industry-standard methods and provide the auditable documentation to prove it.
We offer two primary options. For functional hard drives, we employ a DoD 5220.22-M 3-pass data wipe. This sanitization process securely erases all information, allowing the hardware to be safely remarketed. For drives that are obsolete, damaged, or cannot be wiped, we provide physical shredding, which demolishes the device and makes data recovery impossible.
Regardless of the method chosen, we issue a formal Certificate of Data Destruction for your records. This is your official proof of compliance—a critical document for any audit that confirms you have met your due diligence in protecting sensitive data.
Our entire process is designed to meet or exceed the requirements of major data privacy regulations, including HIPAA.
Is Your Service Compliant with Regulations Like HIPAA?
Yes, absolutely. Our entire operational framework is built to support your compliance requirements. We understand the significant risks faced by organizations in healthcare, finance, and other regulated sectors.
Our secure chain of custody, tracked logistics, and certified data destruction methods are all structured to protect you from data breaches and ensure alignment with regulatory mandates. We provide all the necessary documentation to prove your IT assets were handled in a compliant manner from the moment they left your facility to their final disposition.
What Is the Cost Associated with Your Services?
Pricing for a Marietta computer recycling project is tailored to the specific scope of work. The final cost depends on factors such as the volume and type of equipment, the logistics of the pickup, and the need for on-site services like de-installation.
It is best to view this as an investment in risk mitigation. Core services like certified hard drive wiping are often included in our service packages. Furthermore, newer assets may possess residual value that can be recovered through remarketing to offset the project's cost. We always provide a clear, transparent quote upfront, ensuring there are no surprises.
The challenge of managing e-waste is a global issue. In 2022, the world generated a staggering 62 million tonnes of e-waste, an 82% increase from 2010. Projections show that number surging to 82 million tonnes by 2030. Alarmingly, only 22.3% of that e-waste was properly collected and recycled. You can read the full research about these e-waste findings to grasp the scale of the problem. By choosing a certified recycler, your business becomes a leader in responsible corporate citizenship.
Ready to implement a secure and compliant IT asset disposition strategy for your Marietta business? Contact Atlanta Computer Recycling today to schedule a consultation and receive a transparent quote for your project. Visit us at https://atlantacomputerrecycling.com to get started.