A Practical Guide to Business Electronics Recycling in Atlanta

Disposing of old IT equipment used to be as simple as clearing out a storage closet. Not anymore. For any modern business, a formal business electronics recycling program is a non-negotiable part of your operational strategy. It’s what stands between your company and a costly data breach or a tangle of regulatory penalties.
This guide is your practical plan for turning retired assets from a liability into a secure, managed process.
Why E-Waste Is Now a Core Business Function
The way companies handle retired IT assets has fundamentally changed. What used to be a simple disposal task is now a complex function tied directly to data security, environmental compliance, and your brand's reputation. Every outdated server, laptop, and network switch your company owns is a container for sensitive corporate information and, in many cases, hazardous materials.
Improperly handling this equipment creates significant, measurable business risks. A single hard drive tossed in a dumpster could trigger a devastating data breach, leading to massive financial penalties and shattering the trust you've built with your customers. The modern business landscape demands a smarter, more secure approach.
The Shift from Disposal to Disposition
An effective IT Asset Disposition (ITAD) program isn't about just throwing things away. It's about strategically managing the entire end-of-life process for your technology. This shift in mindset acknowledges that every electronic device holds both potential value and potential liability until it's properly and verifiably handled.
A structured program ensures your business is covered in several key areas:
- Data Security: It guarantees that all proprietary, customer, and employee data is permanently destroyed before any asset ever leaves your control.
- Environmental Compliance: This is how you prevent toxic materials from ending up in landfills, which aligns with corporate responsibility goals and helps you avoid steep regulatory fines. You can learn more about the environmental impact of electronic waste in our detailed article.
- Financial Recovery: A professional ITAD program identifies assets that can be refurbished and resold, helping you recover value from your initial technology investment.
The core principle is simple: your company is responsible for its electronics from the moment of purchase to their final disposition. A certified recycling partner provides the auditable proof that you’ve managed that responsibility correctly.
The Growing Scale of E-Waste
On a global scale, business electronics recycling is quickly moving from a "nice-to-have" sustainability gesture to a core operational need, driven by sheer volume and increasing regulation.
In 2022, the world generated an incredible 62 million tonnes of e‑waste. Projections show that number climbing another 32% to 82 million tonnes by 2030. The real issue for businesses? Only 22.3% of this e‑waste was properly collected and recycled. For IT managers and compliance officers, this massive global gap has direct consequences, as customers, investors, and regulators now expect businesses to prove their assets are handled responsibly.
To truly understand how e-waste recycling fits into your operations, you need to look at it through the lens of risk management. For a broader perspective on building a solid foundation, this guide on creating a comprehensive business risk management framework is an excellent resource.
Creating Your Internal E-Waste Management Policy
Moving from chaotic, last-minute cleanouts toward a structured recycling program starts with a clear internal policy. A documented plan removes guesswork, turning business electronics recycling from a reactive chore into a predictable, secure part of your operations. This policy is your company’s official playbook, ensuring every department knows exactly how to handle retired IT assets safely and consistently.
Without a formal policy, you are relying on individual employees to make the right decisions on data security and environmental compliance. That’s not just inefficient—it’s a significant corporate risk. A solid policy ensures that every single piece of equipment is accounted for, whether it's a retiring employee’s laptop or an entire rack of decommissioned servers.
Defining the Scope of Your Policy
First, you need to outline precisely what this policy covers. Get specific about which devices fall under the guidelines to eliminate any confusion. A comprehensive scope prevents valuable or sensitive assets from slipping through the cracks.
Your policy should clearly identify all covered asset categories:
- Employee Workstations: This includes desktops, laptops, monitors, keyboards, mice, and docking stations.
- Network Infrastructure: The backbone of your operations, including routers, switches, firewalls, and wireless access points.
- Data Center Hardware: Servers, storage arrays (SAN/NAS), and uninterruptible power supplies (UPS) are critical and must be included.
- Mobile Devices: Company-owned smartphones and tablets are packed with sensitive data and must be managed carefully.
- Office Peripherals: Printers, scanners, and VoIP phones are all part of your IT ecosystem.
By detailing these categories, you create an instant inventory guide for your team. It also streamlines communication with a recycling partner, since they'll know exactly what kind of equipment to expect.
Assigning Ownership and Responsibility
A policy is only effective if someone is accountable for its execution. Assigning a clear owner—usually an IT Manager, Facilities Director, or Compliance Officer—is essential. This person or department becomes the central point of contact for all e-waste management activities.
Their duties should be explicitly defined in the policy. This includes overseeing the asset inventory, scheduling pickups with your vendor, and verifying all documentation is in order. The policy owner acts as the gatekeeper, ensuring no device leaves the building without following the proper data destruction and recycling protocols. This single point of ownership is key to maintaining a secure chain of custody.
A common mistake is creating a policy without assigning a specific owner. When everyone is responsible, no one is. Designating a single manager ensures the process is followed consistently and provides a clear point of contact for any audits or inquiries.
Setting a Predictable Retirement Schedule
Instead of waiting for a storage closet to overflow, establish a regular, predictable schedule for retiring old assets. This proactive approach aligns with your natural IT refresh cycles and makes the entire process far more manageable. For most companies, a quarterly or semi-annual pickup schedule works well.
A predictable schedule helps you budget for any service costs and prevents obsolete equipment from piling up. More importantly, it ensures that end-of-life assets containing sensitive data aren't left sitting in unsecured areas for months. This systematic approach is the cornerstone of a mature IT asset disposition (ITAD) program.
Key Elements for Your Policy Checklist
Your written policy must be a practical, working document, not a theoretical treatise. It must include specific, actionable requirements that guide both your internal team and your chosen recycling partner.
Here are the non-negotiable elements to include:
- Data Sanitization Standards: Be explicit about how data will be destroyed. Your policy should mandate that all storage media undergoes certified data destruction, whether that means multi-pass wiping or physical shredding. You can dive deeper into the specifics of secure data destruction to determine the right standard for your organization's needs.
- Asset Tracking Requirements: The policy must require a detailed inventory list, including serial numbers, to be created before any equipment is picked up. This is non-negotiable for creating audit trails and receiving a serialized Certificate of Data Destruction.
- Vendor Selection Criteria: Outline the minimum requirements for any recycling partner. This should include R2 or e-Stewards certification, proof of data breach insurance, and the ability to provide auditable reporting.
- Industry-Specific Compliance: This is where you tailor the policy to your business environment. A healthcare provider must explicitly reference HIPAA compliance for all patient data. A law firm's policy will need to emphasize protecting attorney-client privilege. This customization ensures your program meets your unique regulatory obligations.
Choosing the Right Data Destruction Method
With a policy in place, your next move is arguably the most critical: deciding how to destroy the data on your retired devices. Simply deleting files is insufficient. You need a verifiable, defensible process to ensure sensitive information is gone for good, and this choice directly impacts your security, compliance, and budget.
For most businesses, it comes down to two main options: certified software wiping or physical destruction. The right choice depends on your industry regulations, the type of data you handle, and whether the hardware itself has resale value. An incorrect decision here can lead to a serious compliance failure.
Understanding Software-Based Data Wiping
Software-based data wiping uses specialized programs to overwrite every sector of a hard drive with random data, making the original information completely unrecoverable.
The industry benchmark is DoD 5220.22-M, a 3-pass wiping method originally defined by the Department of Defense, where the drive is overwritten three separate times. For the vast majority of corporate IT assets—such as employee laptops or servers intended for refurbishment—this certified wiping process provides robust security. It sanitizes the drive while keeping the hardware intact for reuse, which benefits both your bottom line and your sustainability goals.
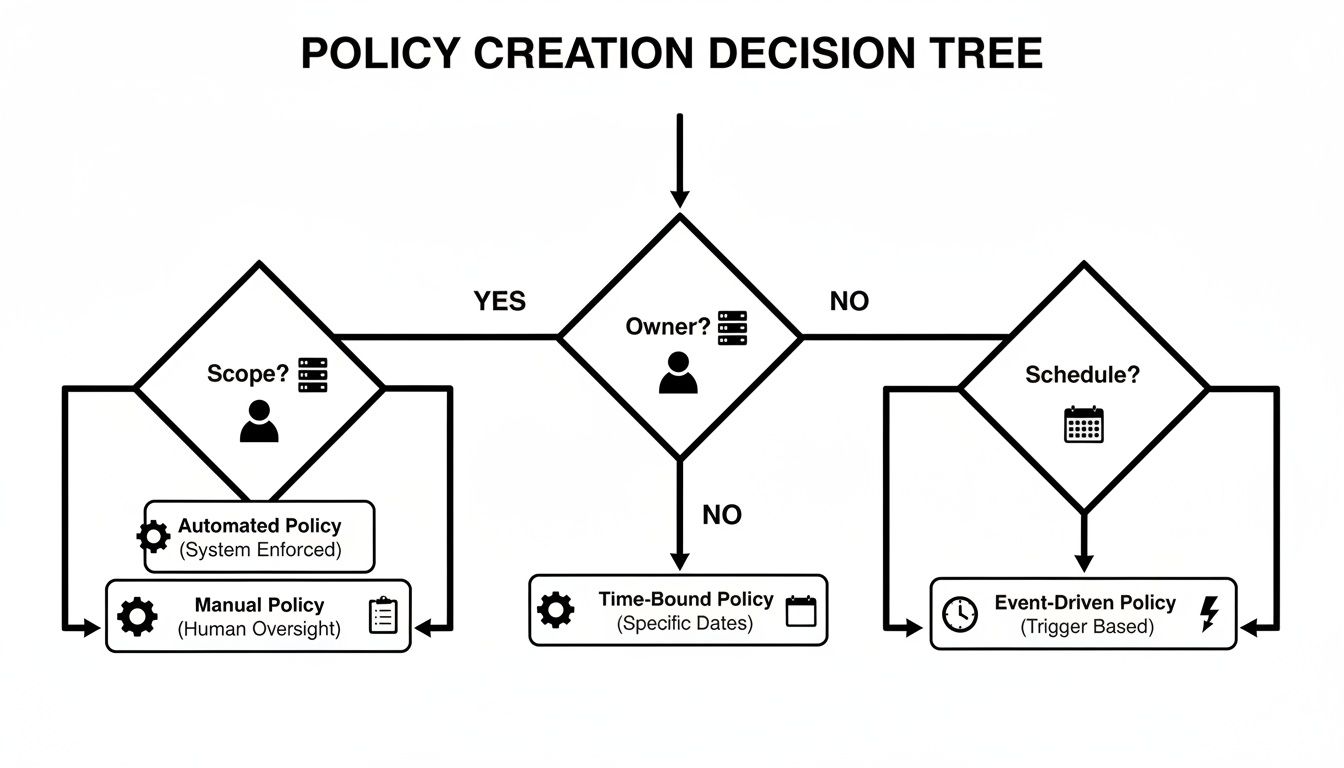
This flow helps visualize when to use which policy for different types of equipment.
As you can see, defining the scope, ownership, and timeline is the foundation of a solid IT asset disposal policy.
When Physical Destruction Is Non-Negotiable
While wiping is ideal for reusable hardware, physical destruction is sometimes the only option. This process involves feeding the drive through an industrial shredder that grinds it into small metal fragments, ensuring no data can ever be recovered.
Physical destruction is the required solution in a few key scenarios:
- Damaged or Non-Functional Drives: If a hard drive will not power on, wiping software cannot be run. Shredding is the only way to guarantee data destruction.
- Obsolete Media: For old drives with no resale value, shredding is an efficient and secure disposal method.
- Strict Compliance Mandates: Some industries or internal corporate policies require physical destruction for all storage media, without exception. If you’re handling highly sensitive information, our guide on on-site hard drive shredding dives deeper into this ultra-secure process.
The rule of thumb is simple: if a drive is functional and has resale value, secure wiping is the best choice. If it’s broken, outdated, or your compliance policy demands it, physical destruction offers absolute peace of mind.
For companies in healthcare, finance, or government, the intersection of e-recycling and data security has become a significant business risk. Global e-waste is growing five times faster than recycling efforts, and the penalties for data breaches are increasing. Industry forecasts for 2025 point to a "data-security arms race" where businesses will be expected to use certified wiping, on-site shredding, and airtight documentation for every retired IT asset.
This is especially critical in the U.S., as 25 states, including Georgia, still lack statewide e-waste recycling laws. This means the full liability for a data breach from an improperly discarded drive falls squarely on your company.
Data Destruction Methods Compared
Deciding between wiping and shredding means weighing your security requirements against costs and the potential to recover value from your assets. This side-by-side comparison can help you make the best choice for your business.
| Factor | Data Wiping (DoD 5220.22-M) | Physical Shredding |
|---|---|---|
| Security Level | High (forensically unrecoverable) | Absolute (media is physically destroyed) |
| Asset Resale | Yes, hardware is preserved for reuse | No, hardware is destroyed and sold as scrap |
| Best For | Laptops, servers, and functional hard drives with resale value | Damaged drives, obsolete media, and strict compliance needs |
| HIPAA/SOX Compliance | Generally compliant with a Certificate of Data Destruction | Fully compliant, often preferred for highly sensitive data |
| Cost | Typically lower, often included in recycling services | Can incur additional fees, especially for on-site services |
Ultimately, one method prioritizes reuse and value recovery, while the other offers absolute, irreversible destruction. Your ITAD partner can help you determine the right mix of services based on your specific inventory and compliance obligations.
How to Select an ITAD Partner in Atlanta
Choosing the right IT Asset Disposition (ITAD) partner is the final, and most critical, step in executing your business electronics recycling plan. Your vendor isn't just a pickup service—they're an extension of your data security and compliance team. In a major business hub like Atlanta, you have many options, but they are far from equal.
The wrong choice can undermine all your internal policies, creating compliance failures, data vulnerabilities, or environmental penalties. The goal is to find a partner who acts as a safeguard, delivering secure, transparent, and auditable services that shield your company from liability.
The Non-Negotiables: Certifications and Insurance
Before discussing pricing or logistics, there are two credentials any potential ITAD partner must have: industry certifications and proper insurance. These are the foundations that prove a vendor operates legally, ethically, and safely. If a company cannot produce these, they should not be considered.
Look for one of these two key certifications:
- R2 (Responsible Recycling): A globally recognized standard that audits a recycler's environmental, health, and safety practices.
- e-Stewards: This certification is known for its stringent standards, particularly its ban on exporting hazardous e-waste to developing nations.
Equally important is proof of insurance, specifically policies covering data breaches and environmental liability. Always request a Certificate of Insurance. This is your financial protection in the unlikely event a vendor error causes a data leak or an environmental issue traced back to your equipment.
Key Questions for Your Vendor Checklist
Once certifications and insurance are confirmed, it's time to vet their operational procedures. A professional partner will provide clear, confident answers. Vague responses or a lack of documentation are major red flags.
Use this checklist during your evaluation:
- What is your process for data destruction? They must detail their methods for both data wiping (using standards like DoD 5220.22-M) and physical shredding. Ask if they can perform shredding on-site at your facility for maximum security.
- Can you provide a complete chain-of-custody? This is the documented trail that tracks your assets from your office to their final disposition. It should include serialized asset lists and confirmation of secure, GPS-tracked transportation.
- What documentation will we receive? The two most important documents are a Certificate of Data Destruction and a Certificate of Recycling. These auditable reports, complete with serial numbers, are your official proof of compliance.
- How do you handle asset resale and value recovery? If you have newer equipment with resale value, ask about their process for testing, refurbishing, and remarketing assets. Ensure you understand their revenue-sharing model.
I always advise clients to focus on the provider's downstream accountability. Ask them: "Can you prove where every single component of my server ends up?" A top-tier partner can trace everything from the shredded aluminum to the recycled circuit boards.
Understanding the Atlanta Market
Working with a local Atlanta-based partner offers distinct advantages over a national provider whose nearest facility may be hundreds of miles away. A local company understands the unique logistics of the metro area, from navigating downtown traffic for a pickup in a high-rise to managing a large data center decommissioning in Alpharetta. You can learn more about the benefits of selecting a qualified electronic waste recycling company that specializes in the local market.
When vetting a local vendor, ask about their protocols for maintaining robust supply chain security to protect your assets from end to end. A local team can also be far more responsive, offering faster scheduling for on-site projects and providing a direct point of contact who knows your account personally.
Looking at the bigger picture, ITAD is no longer a niche service; it's a rapidly growing global industry. The e-waste management market is projected to grow from USD 70 billion in 2024 to USD 81.27 billion in 2025, with the ITAD segment alone expected to hit USD 36.4 billion by 2034. For business leaders, these figures signal a structural shift: retired electronics are now a managed asset class, and partnering with a specialized ITAD provider is simply a smart financial decision. You can find more details in this in-depth market report on electronics recycling.
Managing Pickup Logistics and Final Documentation
You've built the policy and selected a certified partner. The final stage is execution. Coordinating the physical removal of your old equipment and securing the proper documentation are the steps that close the loop on your business electronics recycling program. A smooth, well-managed process at this stage is your best defense against future liability.
Proper preparation before your vendor arrives is critical. This isn’t just about clearing space; it's about maintaining an unbroken chain of custody from the moment an asset is retired until you have a certificate proving it has been properly processed.
Preparing for a Secure Pickup
Before your ITAD partner arrives, your team must create a final, definitive inventory of every device being removed. This step is non-negotiable for accountability. An accurate asset list is the bedrock of your entire audit trail.
Your pre-pickup checklist should include:
- Asset Tagging: Ensure every device, from a server to a laptop, has its unique asset tag recorded.
- Inventory Creation: Log the item type, brand, model, and serial number for each asset in a spreadsheet. Your vendor will use this to reconcile the pickup.
- Secure Staging Area: Consolidate all equipment in one secure, designated area to prevent loss or theft before the scheduled pickup.
That initial inventory is absolutely crucial. Without a serialized list, your vendor cannot provide a serialized Certificate of Data Destruction, which is the key evidence proving those specific devices were properly sanitized. If you need assistance arranging these services, our guide on scheduling an electronic recycling free pick up has all the practical details for Atlanta businesses.
The Two Documents That Prove Compliance
Once your equipment is processed, your partner must provide two critical documents. These are more than just receipts; they are your legal proof that you have met your compliance obligations.
First is the Certificate of Data Destruction. This is a legal document confirming that all data-bearing devices were sanitized according to recognized standards. It must include a serialized list of every hard drive or SSD that was wiped or shredded, giving you concrete proof that your company’s sensitive information was irretrievably destroyed.
Second is the Certificate of Recycling. This document confirms that all non-data components and the raw materials from shredded devices were handled in an environmentally responsible manner, in accordance with all federal, state, and local regulations. It is your proof that your e-waste did not end up in a landfill.
Think of these certificates as your liability shield. In the event of an audit, these serialized documents prove that your organization followed a documented, secure, and compliant process for disposing of its IT assets.
Retaining Documentation for Audits and Liability
Receiving the certificates is only half the process; you must retain them as official company records. Regulations vary, but a good rule of thumb is to hold onto them for at least three to five years.
For businesses in regulated industries like healthcare (HIPAA) or finance (SOX), this documentation is essential for passing an audit. It provides a clear, third-party-verified trail demonstrating that you upheld your duty to protect sensitive data. Without these documents, you cannot prove you acted responsibly, leaving your company exposed to fines and legal action long after the equipment is gone.
Answering Your Corporate E-Waste Recycling Questions
Even with a solid plan, questions will arise. We hear them every day from IT directors and facility managers tasked with managing asset disposition without creating new operational burdens.
Here are straightforward answers to the most common questions from our business clients. Our goal is to clarify the process and explain what you should expect from a professional ITAD service.
What’s This Going to Cost My Business in Atlanta?
This is often the first question, and the answer is frequently better than expected.
For most businesses with a significant amount of reusable equipment—such as recent-generation servers, laptops, and networking hardware—we can often provide core services like pickup and certified data wiping at no charge. The value we recover by remarketing those assets is sufficient to cover our operational costs.
Of course, certain situations do involve a fee:
- Low-Value or No-Value Items: Older, heavier equipment with minimal resale value (like old CRT monitors, office printers, or scanners) incurs a cost to process responsibly. We charge a fee to cover the labor and recycling for these items.
- Specialized On-Site Services: For maximum security services, such as bringing our mobile shred truck to your facility for on-site hard drive shredding, a service charge applies.
- Small-Volume Pickups: If you only have a few items, the logistics costs might outweigh the recoverable value, so a small pickup fee may be necessary.
A reputable partner will always provide a clear, itemized quote upfront. When you weigh that predictable cost against a potential six- or seven-figure fine for a data breach, professional ITAD is not an expense—it's one of the smartest risk management investments your company can make.
What Kind of Business Electronics Can You Take?
A key advantage of working with a dedicated ITAD provider is that we can be your single-source solution. You don't need to manage multiple vendors for different types of equipment.
We handle the full range of corporate IT assets, including:
- Computers & Laptops: Desktops, laptops, docking stations, and all related peripherals.
- Servers & Data Center Gear: Rack servers, blade servers, SANs, NAS devices, and all associated infrastructure.
- Networking Equipment: Switches, routers, firewalls, and wireless access points.
- Office & Telecom Hardware: VoIP phones, business phone systems, and video conference units.
- Monitors & Displays: All standard LCD and LED flat-panel monitors.
While we accept nearly all business electronics, we do not handle items like large office appliances (microwaves, refrigerators) or other hazardous materials. If you have a question about a specific item, just ask. We will provide a quick and clear answer.
How Do We Know Our Company’s Data is Gone for Good?
This is the most critical question, and the answer is proof. You should never have to take a vendor's word for it. We provide auditable documentation that proves your data was permanently destroyed.
We use two primary methods, and your final documentation will detail exactly what happened to every single drive:
- Certified Data Wiping: For functional drives with resale value, we use a DoD 5220.22-M 3-pass wipe. This process overwrites every sector of the drive three times, making the original data unrecoverable with forensic tools.
- Physical Shredding: For failed drives, older media, or when a client's policy requires it, we shred the device into tiny metal fragments. Data recovery is physically impossible.
The most important part of this process is the Certificate of Data Destruction you receive. This is not a simple receipt. It’s a legal document listing the unique serial number of every single hard drive and SSD we processed. This serialized inventory is your definitive proof of compliance for any audit, whether for internal policy or a major regulation like HIPAA.
We’re Doing a Major Office Cleanout. Can You Handle That?
Absolutely. Large-scale projects are our specialty. Office moves, facility closures, and data center decommissioning projects are complex, high-stakes events. Our role is to manage the entire IT asset disposal process, freeing up your team to focus on other critical tasks.
We can manage the entire project, from on-site de-installation and asset tagging to secure packing and logistics. We will decommission servers from racks, inventory every device, and ensure everything is moved out securely and efficiently, with minimal disruption to your operations.
Ready to implement a secure, compliant, and cost-effective electronics recycling program for your business? At Atlanta Computer Recycling, we provide end-to-end ITAD services for companies across the metro area, ensuring your data is destroyed and your assets are handled responsibly.
Contact us today to schedule your free pickup and consultation.