A Business Guide to IT Asset Destruction and Data Security
When corporate technology reaches the end of its lifecycle, IT asset destruction is the formal process of ensuring that device—and the sensitive data on it—is permanently and verifiably eliminated. It’s the critical final step in rendering retired hardware completely unusable and its data unrecoverable.
This is not a simple cleanup task; it's a strategic business function. A professional IT asset destruction program permanently erases sensitive company data, protecting your organization from a catastrophic breach while ensuring old hardware is disposed of in a compliant and environmentally sound way. It goes far beyond simply deleting files, providing a secure, auditable, and final chapter for your technology's lifecycle.
What IT Asset Destruction Really Means for Your Business
When a company server, laptop, or hard drive is no longer needed, simply hitting "delete" or storing it in a closet is a massive security gamble. A retired server is a locked filing cabinet stuffed with your most sensitive client information, financial records, and intellectual property. Leaving it unattended is an open invitation for a data breach.
Professional IT asset destruction is the equivalent of putting that entire filing cabinet through an industrial shredder—not a single piece of data can ever be recovered. It’s a core business strategy, not a janitorial task, and it rests on three critical pillars.
The Three Pillars of Secure ITAD
A robust IT asset disposition (ITAD) plan protects your organization by addressing security, compliance, and environmental responsibilities simultaneously. A failure in any one of these areas can lead to severe consequences. You can learn more about these fundamentals in our guide on what is IT asset disposition.
Here’s what a proper ITAD strategy delivers for your business:
- Safeguarding Against Data Breaches: Every retired device is a potential data breach. Secure destruction eliminates that risk—permanently.
- Navigating Complex Compliance: Regulations like HIPAA and FACTA don't just recommend secure disposal; they mandate it. The penalties for non-compliance are steep.
- Upholding Environmental Responsibility: Certified ITAD partners ensure hazardous e-waste is recycled responsibly, keeping toxic materials out of landfills and protecting your corporate reputation.
This intense focus on security and sustainability is driving major market trends. The global ITAD market has already hit USD 17.5 billion as technology turnover accelerates and e-waste regulations tighten. This is no longer a niche service; it's a worldwide shift toward professional solutions that neutralize the dual risks of data exposure and environmental harm.
An ITAD partner provides an essential layer of security and peace of mind. It transforms the complex task of hardware disposal into a managed, auditable process that protects your brand, your customers, and your bottom line.
To get the full picture, remember that ITAD is the final, critical step in a well-managed IT Asset Management (ITAM) lifecycle. A strong ITAM strategy tracks your technology from procurement to retirement, guaranteeing that assets are disposed of with the same security and diligence they were maintained with.
Choosing Between Data Wiping and Physical Destruction
Once an IT asset is officially retired, you face the most important decision in its lifecycle: how to handle the data it holds. The choice boils down to two core methods of it asset destruction: software-based data wiping or outright physical destruction.
Each path serves a different business purpose. The right one for your company will depend on the asset's condition, its remaining value, and your organization's specific security policies.
Think of professional data wiping as meticulously sanitizing a whiteboard. It’s not a single swipe. Instead, the entire surface is overwritten with random data, multiple times, following strict protocols like the DoD 5220.22-M standard. The original information becomes completely unrecoverable, but the hardware itself is left intact and ready for reuse.
Physical destruction, on the other hand, is like putting a confidential corporate file through an industrial shredder. The information is gone for good because the media it was stored on has been turned into fragments. There’s no coming back from that—both the device and its data are permanently eliminated.
When to Choose Data Wiping
Data wiping is your best option when you want to preserve the physical hardware. It’s the go-to method for assets that still have functional or monetary value, allowing your business to recover costs through resale or redeploy the equipment internally. By sanitizing the drive, you prepare it for a secure second life.
This approach is ideal for:
- Newer, functional equipment like laptops, servers, and computers that can be refurbished and sold.
- Leased hardware that must be returned to the leasing company with all proprietary data securely erased.
- Internal redeployment where a device is being passed from one employee or department to another.
The key benefit of wiping is the balance between top-tier security and value recovery. You meet your data protection obligations while contributing to a circular economy and improving your IT budget. For more on the technical process, see our guide on how to properly wipe a hard drive.
When Physical Destruction is Non-Negotiable
In certain situations, a software wipe isn't sufficient—or even possible. In these cases, physical destruction is the only way to guarantee complete and total data elimination. This method provides absolute certainty that sensitive information can never be accessed again, making it essential for your highest-risk assets.
Physical destruction is the ultimate failsafe in the IT asset destruction process. When compliance demands irrefutable proof of elimination or the hardware itself is compromised, shredding provides the final, definitive answer.
This more aggressive approach is required for:
- Failed or damaged hard drives that will not power on, making a software wipe impossible.
- Outdated storage media like old magnetic tapes, CDs, or legacy hard drives with no resale value.
- Strict company policies or compliance mandates (such as certain government or healthcare regulations) that explicitly require physical destruction for specific data types.
Deciding between wiping and shredding has become a critical business decision. With data destruction now leading the IT asset disposition market with a USD 5 billion valuation, it's clear where corporate priorities lie. This focus is a direct response to rising threats, as the global cost of data breaches skyrockets toward $10.5 trillion, with experts expecting a 15% annual increase.
Data Wiping vs. Physical Destruction at a Glance
To make the decision clearer, here’s a straightforward comparison for your business. Consider each asset’s condition, your security requirements, and your budget to determine the appropriate path.
| Attribute | Data Wiping (e.g., DoD 5222.22-M) | Physical Destruction (Shredding/Degaussing) |
|---|---|---|
| Asset Reuse | Yes. The hardware remains intact and fully functional for resale or redeployment. | No. The asset and its components are completely destroyed and cannot be used again. |
| Cost Recovery | High. Enables resale of valuable equipment, generating revenue. | None. The value of the asset is lost; you are paying only for the destruction service. |
| Security Level | Extremely high. Renders data unrecoverable using software-based methods. | Absolute. Physically eliminates the possibility of data recovery by destroying the media. |
| Best For | Functional laptops, servers, smartphones, and leased equipment. | Failed/damaged drives, obsolete media (tapes, CDs), and high-security compliance needs. |
| Proof | A Certificate of Data Erasure verifies the process and serial numbers. | A Certificate of Destruction confirms the physical elimination of the media. |
| Environmental | Promotes reuse and extends the asset's life, supporting the circular economy. | Materials are recycled as scrap metal/e-waste after destruction. |
Ultimately, choosing the right method is a strategic risk assessment. By evaluating each asset individually, your organization can build a secure, compliant, and financially smart plan for every piece of technology you retire.
Navigating Data Security and Compliance Mandates
Failing to properly manage IT asset destruction isn't just a technical oversight—it's a direct violation of powerful data security laws. These regulations are not suggestions; they are strict, enforceable rules designed to protect sensitive information. For any business, compliance is non-negotiable.
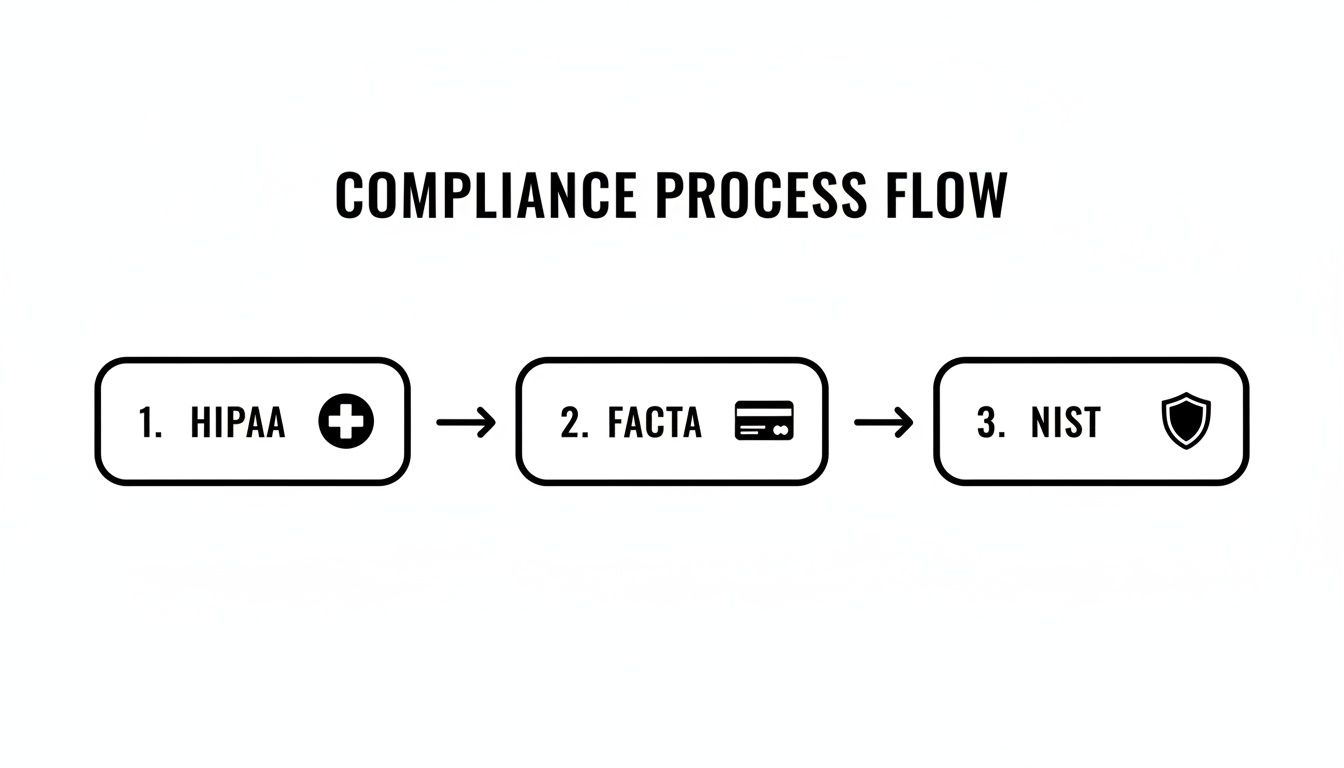
The array of acronyms like HIPAA, FACTA, and NIST can seem intimidating. But their purpose is simple: ensure data is protected throughout its entire lifecycle, especially at disposal. Ignoring these mandates can lead to crippling financial penalties, legal action, and a loss of customer trust that can take years to rebuild.
The Heavy Hitters of Data Regulation
While numerous rules govern data, a few stand out for their stringent requirements on how businesses must handle end-of-life IT assets. These laws make professional IT asset destruction a core business function.
Here are the key mandates your business needs to know:
- HIPAA (Health Insurance Portability and Accountability Act): For any organization handling patient health information (PHI), HIPAA is the gold standard. It demands that data on retired medical equipment, servers, or company laptops be rendered completely unreadable, unrecoverable, and indecipherable.
- FACTA (Fair and Accurate Credit Transactions Act): This federal law was enacted to combat identity theft. It requires businesses to destroy any documents or devices containing consumer credit information before disposal. This makes professional shredding or wiping a legal necessity.
- NIST 800-88: While technically a set of guidelines from the National Institute of Standards and Technology, NIST 800-88 is the definitive guide for media sanitization. It outlines specific procedures for clearing, purging, and destroying data to meet various security levels and is widely adopted as a best practice.
A huge part of staying compliant involves understanding privacy and data collected by your organization in the first place. This knowledge forms the bedrock of any intelligent disposal strategy, ensuring you know exactly what sensitive information requires protection.
Turning Compliance into a Defensible Process
Meeting these legal requirements comes down to one thing: creating a documented, auditable, and defensible process. In the event of a data breach, auditors and investigators will demand hard proof that you followed a secure procedure for every single asset.
This is where a certified ITAD partner is invaluable. A professional vendor transforms compliance from a burden into a fully managed service. They provide the two most critical pieces of evidence your business needs to demonstrate due diligence.
The backbone of any compliant IT asset destruction strategy is irrefutable proof. A secure chain of custody and a formal Certificate of Destruction are not just paperwork—they are your legal defense, proving you took every necessary step to protect sensitive data.
The chain of custody is an unbroken, documented trail. It tracks each asset from the moment it leaves your facility to its final destruction, recording every handoff so nothing gets lost or compromised.
Once the destruction is complete, you receive a Certificate of Destruction. This legally binding document is your official receipt, listing every asset by serial number and confirming the exact date and method of destruction. You can see a sample Certificate of Destruction to understand what this critical final document looks like. It’s your ultimate proof of compliance, closing the loop on the asset's life and protecting your business from future liability.
The IT Asset Destruction Process from Start to Finish
Proper IT asset destruction isn’t a single event—it’s a carefully managed process designed to shield your organization from risk at every stage. Following a retired server through its end-of-life journey reveals a series of secure handoffs that create an unbreakable, auditable trail.
This structured workflow is how a potential liability is converted into a closed security loop, giving IT managers total confidence that retired assets won't become a future problem. The entire process is built on documentation and verifiable actions.
Step 1: Initial Asset Inventory and Secure Tagging
The moment an asset is taken offline, the security process begins. It's not enough to simply unplug a server. The first step is to formally identify and log the device in your asset management system, noting its make, model, and serial number.
Immediately after, the asset is physically tagged with a unique ID number. This tag acts as its passport, connecting the physical hardware to its digital record. This establishes the first link in the chain of custody, ensuring the device is trackable from this point forward.
Step 2: Secure Logistics and Transportation
Once tagged, the asset must be moved securely. Whether the final destruction occurs at your facility or a specialized plant, transportation is a major vulnerability. That’s why professional ITAD partners use locked, GPS-tracked vehicles and trained, background-checked personnel to handle the logistics, eliminating the risk of theft or loss in transit.
This secure transport protocol maintains the chain of custody before the data is even touched. For a closer look at these logistics, see our guide on secure electronics disposal.
Step 3: Certified Data Destruction
This is the core of the IT asset destruction process. Upon arrival at a secure facility (or when a mobile unit arrives on-site), the data-bearing components are destroyed according to your company’s policies and compliance requirements. This may involve software-based wiping that adheres to NIST 800-88 standards or physical shredding for failed drives or higher security needs.
Every action is verified and recorded. The destruction method, the date, and the technician responsible are all logged against the asset’s unique serial number.
The goal here is absolute, total data elimination. Certified destruction gives you irrefutable proof that your sensitive information is gone for good, meeting the tough demands of regulations like HIPAA and FACTA.
This flowchart illustrates how different compliance needs direct the destruction process.
It clarifies that whether you're dealing with healthcare (HIPAA), financial (FACTA), or government (NIST) data, the end result must always be certified, documented data destruction.
Step 4: Responsible Recycling or Remarketing
Once the data is verifiably destroyed, the physical hardware is addressed. The path forward depends on the asset's age, condition, and value.
- Remarketing: If a server or component is still functional and holds market value, it is refurbished and resold. This allows your organization to recover a portion of its original investment.
- Recycling: For obsolete or broken equipment, the asset is de-manufactured. It is carefully broken down into its base materials—metals, plastics, circuit boards—which are then sent into certified recycling streams for a zero-landfill outcome.
This final stage fulfills your corporate environmental stewardship duties, preventing hazardous e-waste from ever reaching a landfill.
Step 5: Final Audit-Ready Reporting
The process concludes with the delivery of critical documentation. Your organization receives a Certificate of Destruction, a legally binding document that details every asset destroyed by serial number, date, and method used.
This report, along with the complete chain-of-custody log, provides the audit-ready proof needed to satisfy compliance officers, auditors, and regulators. It is the official record that closes the loop on an asset's lifecycle, serving as definitive proof that you have met your obligation to protect company data and dispose of technology responsibly.
How to Select the Right IT Asset Destruction Partner
Choosing a partner for your IT asset destruction is a high-stakes decision. You are not just hiring a disposal service; you are entrusting a vendor with your company’s sensitive data, legal compliance, and brand reputation.
The right partner acts as an extension of your security team, while the wrong one can expose your business to catastrophic risk. A smart choice requires looking beyond a simple price quote. A cheap service that cuts corners is no bargain when a single data breach can cost millions.
Key Certifications to Look For
Industry certifications are the fastest way to vet a potential vendor. They serve as a baseline for any trustworthy ITAD provider. These credentials are not just logos on a website; they represent a commitment to rigorous, third-party audited standards for security, safety, and sustainability.
When evaluating partners, ensure they hold one or both of these top-tier certifications:
- R2v3 (Responsible Recycling): This is the leading global standard for electronics recycling, covering environmental protection, worker safety, and data security. An R2v3 certified company has proven it adheres to best practices for every stage of the disposal process.
- e-Stewards: Often considered the most stringent standard, e-Stewards certification guarantees that no hazardous e-waste is exported to developing nations. It also mandates robust requirements for data destruction and employee safety.
These certifications provide strong assurance that a vendor operates ethically and securely, significantly reducing your own due diligence burden.
Critical Questions Every Business Should Ask
Once you've confirmed a vendor holds the right certifications, it's time to dig deeper into their operational procedures. Their answers will reveal their true capabilities and their ability to meet your specific security and compliance needs. A professional partner will welcome these questions and provide clear, documented answers.
A vendor's willingness to provide transparent, detailed answers about their security protocols and chain of custody is a direct indicator of their reliability. If they are vague or dismissive, consider it a major red flag.
When you’re ready to evaluate a potential partner, it’s critical to ask the right questions. This checklist covers the essentials for ensuring they meet your security, compliance, and environmental standards.
Vendor Selection Checklist for IT Asset Destruction
| Evaluation Criteria | Key Questions to Ask | Why It Matters |
|---|---|---|
| Chain of Custody | "Can you provide a detailed, auditable chain-of-custody document?" | This is non-negotiable. It should track every asset by serial number from your facility to final destruction, with signatures at every handoff. |
| Data Destruction | "What are your specific data destruction methods and standards? Do you follow NIST 800-88?" | Confirm they offer both on-site and off-site shredding, plus multi-pass wiping. Vague answers here are a warning sign. |
| Liability & Insurance | "What level of liability insurance do you carry specifically for data breaches?" | A reputable vendor carries significant insurance to protect you if the unthinkable happens while assets are in their possession. |
| Environmental Policy | "Do you have a zero-landfill policy? Can I see documentation of your downstream recycling partners?" | True environmental stewardship means nothing goes to a landfill. This proves they handle all materials responsibly. |
Asking these direct questions helps you separate the true professionals from the rest. A solid partner won’t just have the answers; they’ll have the documentation to back them up.
If you are evaluating vendors in the Atlanta area, our guide on choosing among local electronic waste disposal companies offers additional insights. Selecting the right partner ensures your IT asset destruction program is secure, compliant, and sustainable from start to finish.
Answering Your Top Questions About IT Asset Destruction
As technology reaches its end-of-life, key questions arise for business leaders and IT managers. Getting clear answers on IT asset destruction is what separates a secure, compliant process from a risky one. Here are the most common questions we address for our corporate clients.
How Can I Be Sure Our Company's Data Is Gone for Good?
You need more than a vendor's promise—you need a rock-solid, legally defensible paper trail. Proof comes from the meticulous documentation provided by a certified ITAD partner, which creates an unbroken audit trail for every device.
Look for these two non-negotiable documents:
- Chain-of-Custody Record: This document tells the story of your asset's journey, tracking each device from your facility to its final destruction and logging every handoff.
- Certificate of Destruction: This is your official, legally binding proof. It lists every device by serial number and confirms the exact method and date of destruction. This is your primary evidence for auditors.
For businesses requiring the highest level of assurance, some partners offer video documentation of the physical shredding process. This provides an indisputable visual record, closing any possible compliance gaps and delivering total peace of mind.
Is It Safer to Destroy Assets On-Site or Off-Site?
Both methods are highly secure when handled by a certified professional, but they address different business needs. The right choice depends on your company's risk tolerance, internal security policies, and logistical requirements.
On-site destruction offers maximum transparency. A mobile shredding truck comes directly to your facility, allowing you to witness your hard drives being destroyed. This is the preferred option for organizations with the strictest security mandates or policies that prohibit data-bearing devices from leaving the premises intact.
Off-site destruction occurs at a secure, access-controlled facility designed for high-volume processing. It is often more efficient and cost-effective for large-scale projects, such as a full data center decommissioning or a company-wide hardware refresh. Any reputable partner will use locked, GPS-tracked vehicles for transport and provide the same certified documentation as on-site services.
Ultimately, the security of either method hinges on the vendor's process. A trustworthy partner provides the same certified reporting, chain-of-custody, and verifiable destruction regardless of location.
What Happens to the Hardware After the Data Is Destroyed?
Once the data is verifiably eliminated, the focus shifts to environmental stewardship and, where applicable, value recovery. The goal is to adhere to a strict zero-landfill policy, handling the physical materials in a way that is both sustainable and financially prudent.
The hardware itself follows one of two paths:
- Remarketing and Reuse: If equipment still has functional value—such as newer servers, laptops, or networking gear—it is tested, refurbished, and sold on secondary markets. This not only supports a circular economy but can also generate revenue to offset disposal costs.
- Responsible Recycling: For obsolete, broken, or valueless equipment, the de-manufacturing process begins. Devices are carefully disassembled into their core components—metals, plastics, circuit boards, and glass. These raw materials are then sent to certified downstream partners to be processed and used in new products.
This final step ensures hazardous e-waste is kept out of landfills and helps your organization meet its environmental, social, and governance (ESG) goals. True IT asset destruction is not just about protecting your data; it’s about protecting the planet and your corporate reputation.
For businesses in the Atlanta metro area, Atlanta Computer Recycling provides certified, secure, and sustainable ITAD solutions tailored to your compliance needs. Contact us to learn how we can protect your data and manage your end-of-life assets responsibly at https://atlantacomputerrecycling.com.