Sample Certificate of Destruction: Essential for ITAD Compliance
A sample certificate of destruction isn't just a piece of paper—it's your legally-binding proof that sensitive data or physical assets have been permanently and securely destroyed. For any business serious about risk management, this document is an essential tool, creating an auditable record that demonstrates you’ve met your data protection obligations.
What a Certificate of Destruction Is and Why Your Business Needs One
When your company upgrades its servers, laptops, and other IT equipment, what happens to the legacy devices? They are often liabilities, packed with years of sensitive data—customer lists, financial records, and proprietary trade secrets. Simply deleting files is insufficient, as that data is often easily recoverable. This is exactly where a Certificate of Destruction (CoD) becomes mission-critical.
Think of a CoD as more than just a receipt from your IT asset disposition (ITAD) vendor; it's your legal shield. It provides official, verifiable proof that every byte of data has been irretrievably destroyed according to recognized industry standards. This document is a cornerstone of any robust data security policy, protecting your business from the crippling financial and reputational fallout of a data breach.
The Role of a CoD in Risk Management
For any organization that handles sensitive information, a CoD is a non-negotiable step in the asset lifecycle. It’s the concrete evidence that you performed your due diligence in protecting data, which is invaluable during an audit or legal inquiry. Without this proof, your company is exposed to significant liability.
A properly executed CoD delivers:
- Legal Protection: It demonstrates compliance with stringent regulations like HIPAA for healthcare or government standards for handling classified information.
- Audit Trail: It establishes a clear chain of custody, detailing precisely what was destroyed, the method used, and who is accountable.
- Peace of Mind: It confirms that retired assets won't re-emerge as the source of a devastating data leak.
This screenshot from Wikipedia shows a typical example of what a Certificate of Destruction might look like.
Note the key fields—company details, a description of the materials, the date, and signatures. These elements are all vital for creating a complete and defensible record of destruction.
A Rapidly Growing Industry Need
The demand for certified destruction is exploding. The global electronics recycling market is projected to grow from USD 43.2 billion in 2025 to a massive USD 147.9 billion by 2035. With PCs and laptops comprising 45% of this market, it’s clear why professional ITAD partners are essential for managing this surge of e-waste securely. You can read the full research about the electronics recycling market to better understand these trends.
Ultimately, a Certificate of Destruction closes the loop on your data security responsibilities. It transforms a potential liability—a legacy hard drive full of sensitive information—into a documented and verified non-threat. You can learn more about how a certificate of destruction works and its importance in our detailed guide. This document isn't just paperwork; it’s a fundamental component of modern corporate governance.
The Essential Checklist for a Compliant Certificate of Destruction
Receiving a document titled "Certificate of Destruction" is not enough to protect your business. A vague or incomplete certificate is a major liability, leaving critical gaps in your audit trail right where you need solid proof. To be truly audit-proof, every sample certificate of destruction must contain specific, non-negotiable details that forge an unbreakable chain of custody.
Consider the analogy of a vehicle title. A document that just says "a blue car" is worthless. You need the VIN, make, model, and year for it to be legally valid. A Certificate of Destruction operates on the same principle—precision gives it authority and shields your company from compliance penalties or the fallout from a data breach.
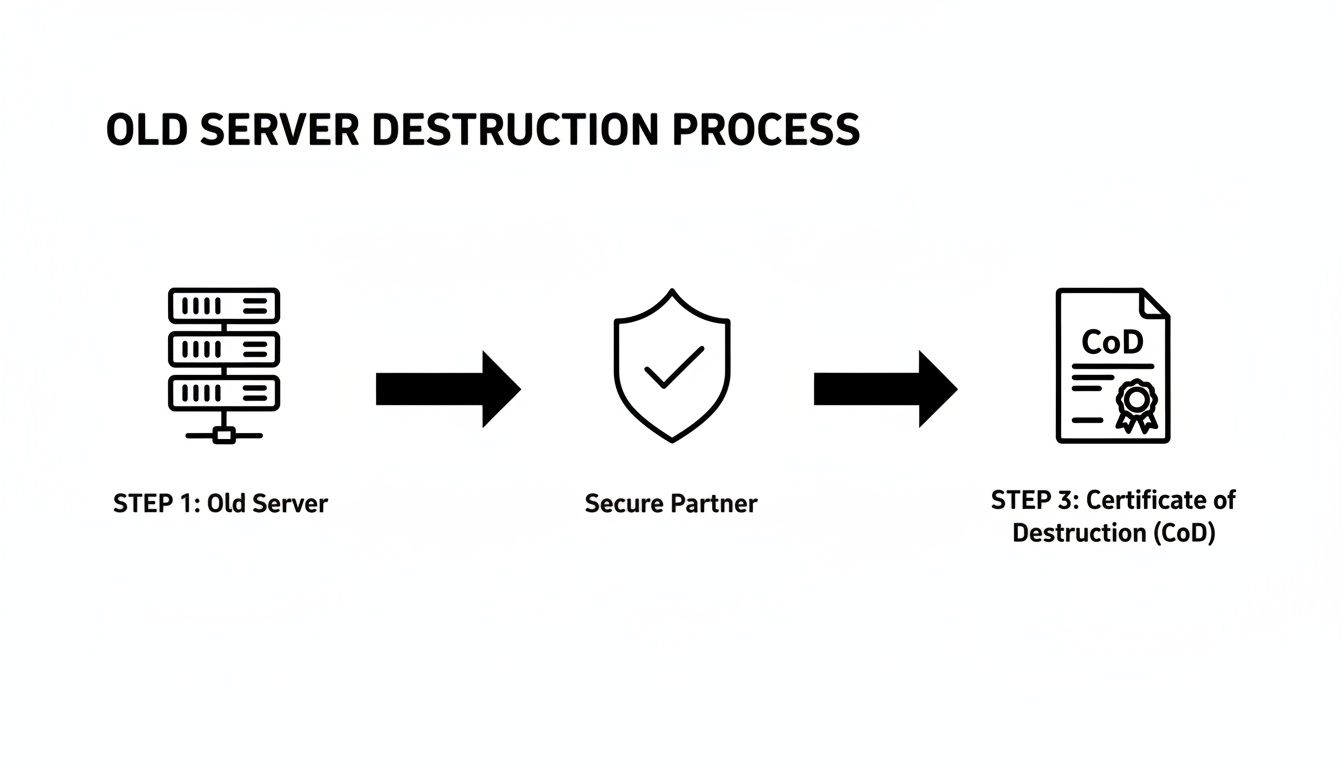
The process is straightforward when you engage the right partner. This diagram illustrates how a legacy server transitions from being a risk in your data center to a documented, non-existent threat.
As you can see, a trusted ITAD partner acts as the bridge between retiring an asset and achieving certified security, with the CoD serving as the final, critical step.
Core Components of an Audit-Proof Certificate
To ensure the document you receive will stand up to scrutiny, it must contain several key fields. Each one plays a vital role in proving the disposition of your IT assets and the sensitive data they once held. An incomplete certificate is a major red flag that should cause you to question your vendor's entire process.
Here’s a breakdown of the essential information every IT manager should demand on a CoD. Use this as your compliance checklist.
| Component | What It Is | Why It's Critical for Your Business |
|---|---|---|
| Unique Certificate ID | A one-of-a-kind serial number for the certificate itself. | Prevents fraud and simplifies tracking and referencing within your internal records and asset management systems. |
| Client & Vendor Details | Full legal names, addresses, and contact information for both your company and the vendor. | This clearly establishes responsibility and accountability for the entire destruction process. |
| Detailed Asset List | A specific inventory of every item destroyed, including its type, make, and model. | This is non-negotiable. It proves exactly what was destroyed, preventing any ambiguity during an audit. |
| Serial Numbers / Asset Tags | The unique manufacturer serial number and/or your internal asset tag for each individual device. | A generic list like "50 hard drives" is unacceptable. This links the CoD directly to a specific asset in your inventory. |
| Method of Destruction | A clear description of how the data was destroyed (e.g., shredding, wiping to a specific standard). | Proves compliance with standards like HIPAA or DoD. "Shredding" is not enough; it should be "Physical shredding to 9mm particle size." |
| Date of Destruction | The exact date the assets were physically destroyed. | Creates a definitive timeline for your records and officially closes the asset's lifecycle in your books. |
| Authorized Signature | The printed name, title, and signature of the vendor’s authorized representative. | This is the vendor's legal attestation that the work was performed as described, finalizing the chain of custody. |
Each of these elements works together to create a legally defensible record that protects your organization.
Documenting the Destruction Method and Accountability
Beyond just listing what was destroyed, a proper certificate must specify how and when it happened. This level of detail is what demonstrates compliance with specific data security regulations like HIPAA or DoD standards.
You need specifics. Was the method listed as "Data Wiping" or a much stronger "DoD 5220.22-M 3-pass wipe"? Details matter because they provide irrefutable proof. The more precise the description, the stronger your compliance position.
Finally, the document must be validated with signatures and dates. It must clearly state the exact date of destruction and include the printed name, title, and signature of an authorized representative from the destruction company. That signature is their legal guarantee, officially closing the loop on your retired assets.
To see how these standards are put into practice, you can learn more about our secure data destruction services and how we align our processes with industry best practices.
Download Your Free IT Asset Destruction Certificate Template
Understanding the theory is one thing, but having a practical tool is what makes a difference. To help you elevate your data security documentation, we’re offering a free, downloadable sample certificate of destruction template built specifically for IT asset disposal. Think of it as more than just a form—it's a benchmark for your entire security process.
You can use this template to evaluate the certificates your current vendors provide, or you can adopt it for your own in-house destruction processes. It’s far easier to spot a weak or incomplete document from a third party when you know exactly what a robust one looks like.
Download Your Free Template Now
Get a head start on creating audit-proof records. Click the link below to grab our customizable IT Asset Destruction Certificate template.[Download Your Free Certificate of Destruction Template – Word Doc]
This editable document is designed to ensure you capture every critical detail we've discussed. It’s your indisputable record, protecting your company from the operational and financial headaches of non-compliance. In fact, a 2023 study found that over 78% of North American businesses now require a formal CoD for asset disposal, a significant increase that shows how critical this documentation has become.
A Quick Guide to the Template Fields
Our template includes clearly marked sections for every piece of information you need, ensuring nothing is missed. It functions as a checklist, guiding you through the process of creating a complete and defensible record every time you retire a piece of hardware.
When you open the file, you'll find dedicated fields for:
- Unique Certificate ID: Enables easy tracking and referencing for specific jobs.
- Client & Vendor Information: Clearly outlines who is responsible for what.
- Detailed Asset Inventory: Columns for make, model, and the all-important serial numbers.
- Method & Date of Destruction: Pinpoints exactly how and when the destruction was completed.
- Authorized Signatures: The final sign-off that completes the chain of custody.
This structured format removes guesswork and maintains consistency in your documentation. For a deeper dive into the different kinds of CoDs, check out our guide on the certificate of destruction for hard drives. Our template provides the solid foundation you need to turn a simple document into a powerful legal and operational shield for your business.
How a CoD Reinforces Your Data Compliance Strategy
A Certificate of Destruction (CoD) is far more than just a receipt for disposal; it’s a critical component of your company's compliance framework. For any business in a regulated industry, this document is your tangible, legally defensible proof that sensitive data was permanently and properly destroyed in accordance with all relevant laws.
Without it, you leave your organization exposed to audit failures, steep fines, and significant legal challenges.
Think of the CoD as the final, official link in your data's chain of custody. It closes the loop on retired IT assets, transforming a potential security liability into a documented, verified non-issue. A solid Certificate of Destruction is a cornerstone of effective data compliance and plays a key role in your broader risk compliance management strategy by demonstrating due diligence.
Satisfying HIPAA, DoD, and Privacy Law Requirements
Different industries face different regulatory pressures, and a well-executed CoD helps you meet them head-on. It isn't a generic, one-size-fits-all form. It’s a precise instrument that provides the exact proof auditors and legal teams demand.
This documentation has become essential as data security concerns grow. In 2022 alone, the world generated an incredible 136 billion pounds of e-waste—approximately 17 pounds for every person on the planet. What's truly alarming is that 78% of it was not formally recycled. With that number projected to climb to 181 billion pounds yearly by 2030, the pressure on IT managers to secure proof of destruction is immense.
A Certificate of Destruction is your definitive answer when an auditor asks, "How can you prove that patient data on those legacy servers was properly destroyed?" It shifts the burden of proof from your word to a legally binding document.
Your Shield Against Non-Compliance Penalties
Let's break down how a CoD directly addresses specific regulations and what that means for your business.
- HIPAA Compliance: For healthcare organizations, a CoD is non-negotiable. It provides concrete evidence that Protected Health Information (PHI) was destroyed in a way that makes it "unreadable, indecipherable, and otherwise unable to be reconstructed," as the HIPAA Security Rule mandates.
- DoD 5220.22-M Standard: If your business is a government contractor or handles sensitive federal information, you must adhere to strict media sanitization guidelines. A CoD that specifies this DoD-standard wiping method confirms you've met these rigorous protocols.
- General Data Privacy Laws: Regulations like GDPR and various state-level privacy acts require businesses to securely dispose of consumer data once it's no longer needed. The certificate is your proof of compliance with the "right to be forgotten."
By providing this critical documentation, a CoD effectively shields your company from the severe consequences of non-compliance. Our professional Atlanta data destruction services are designed to deliver the detailed, audit-proof certification needed to satisfy these stringent requirements.
Choosing an ITAD Partner That Guarantees Secure Destruction
Selecting the right IT Asset Disposition (ITAD) partner is as important as understanding the certificate itself. A perfect sample certificate of destruction is meaningless if the issuing company has a flimsy, unverified process. Your partner is the last line of defense for your data, and a poor choice can expose your business to the very risks you are trying to mitigate.
Consider it like hiring a security firm to protect your facilities. You wouldn't simply choose the lowest bidder; you would investigate their training, protocols, and track record. The same level of scrutiny applies here, because their actions directly impact your legal and financial standing.
Key Questions to Ask Potential Vendors
Before you entrust a vendor with a single hard drive, you need to ask pointed questions—the kind that separate true experts from unqualified operators. Their answers will reveal how seriously they take security and compliance. When choosing an ITAD partner, it's vital to ensure they uphold robust security for data centers and other facilities where your IT assets are processed.
Here are the non-negotiable questions every IT manager should be asking:
- What are your specific destruction methodologies? Have them walk you through their process for both data wiping (like DoD 5220.22-M) and physical shredding. Vague answers are a major red flag.
- Can you describe your chain-of-custody protocol? How do they track your assets from the moment they leave your premises to their final destruction? Look for details about locked trucks, secure facilities, and serialized tracking logs.
- Are your facilities certified? Inquire about certifications like R2v3 or NAID AAA. These credentials prove adherence to high industry standards for both security and environmental responsibility.
- Can you provide a sample Certificate of Destruction? Compare their document to the best practices we've outlined. Ensure it includes unique serial numbers, specific destruction methods, and authorized signatures.
The stakes are incredibly high, especially with the volume of electronics being retired. With e-waste projected to exceed 60 million metric tons in 2025, and global recycling rates expected to decline, unverified disposal is an unacceptable risk. Enhancing responsible collection and certified destruction isn't just a compliance task; it’s a critical business necessity.
How Atlanta Computer Recycling Delivers Peace of Mind
At Atlanta Computer Recycling, we have structured our services to answer these crucial questions before you even need to ask. We understand that your top priority is absolute data security, backed by undeniable proof.
Our process is built on transparency and accountability. We don’t just destroy your data; we provide a certified, auditable trail that proves it, delivering the documentation needed to satisfy any compliance requirement.
We directly address the strict demands of Atlanta’s businesses by offering:
- Free DoD-Standard Wiping: We utilize the DoD 5220.22-M 3-pass standard to sanitize hard drives, delivering a top-tier level of data security at no additional cost.
- Secure Physical Shredding: For non-functional drives or obsolete media, our physical shredding services ensure the data is 100% unrecoverable.
- Detailed Certification: Our Certificates of Destruction are meticulous. We list every single asset by its serial number and specify the exact method and date of destruction.
By partnering with a dedicated electronic waste recycling company, you guarantee that every step is handled with professional care. We provide the confidence you need to make an informed decision that protects your organization from top to bottom.
Your Certificate of Destruction Questions Answered
When you're managing IT asset disposition, the documentation is the final, crucial step. Even if you understand why a sample certificate of destruction is important, practical details can still be a source of confusion. This is where the process moves from theory to reality.
Let’s address some of the most common questions we hear from IT managers and compliance officers. Consider this your quick-reference guide for finalizing the details and ensuring your process is airtight, compliant, and defensible.
Is a Digital Certificate of Destruction as Valid as a Paper Copy?
Yes, absolutely. In the modern business environment, digital certificates are not only valid but are the industry standard. A PDF is as legally sound as a physical document, provided it contains all the critical, verifiable information we’ve covered—asset serial numbers, method of destruction, dates, and an authorized signature.
In fact, most businesses prefer digital copies for several key reasons:
- Efficient Storage: They can be filed securely on a server or in the cloud without consuming physical space.
- Rapid Retrieval: Finding a specific certificate for an audit becomes a simple keyword search, not a time-consuming hunt through filing cabinets.
- System Integration: Digital CoDs can be imported directly into your company’s asset management or compliance software, centralizing your records.
At Atlanta Computer Recycling, we provide secure, easy-to-archive digital certificates for all our destruction services. This ensures your records are always organized, accessible, and ready for any audit.
How Long Should Our Company Keep Certificates of Destruction?
Retention periods depend on your industry and its specific regulations. For healthcare organizations governed by HIPAA, for example, records must be kept for a minimum of six years. For most other businesses, the general best practice is to retain these certificates for three to seven years.
However, here’s some practical advice: since digital storage is inexpensive and data-related litigation is extremely costly, many companies now opt to keep these certificates indefinitely. They become a permanent part of the IT asset’s lifecycle record.
We always recommend consulting with your own legal or compliance team. They can help you establish a formal retention policy that aligns with your industry's requirements and your company's risk tolerance.
What Is the Difference Between Data Wiping and Physical Destruction?
This is a critical question because the answer directly impacts both your security and your budget. Both are legitimate methods of data destruction, but they are used for different reasons.
Data Wiping (Sanitization): This is a software-based method. Specialized programs are used to overwrite every sector of a hard drive with random data, often multiple times. A well-known and trusted standard is the DoD 5220.22-M 3-pass wipe, which makes the original information completely unrecoverable. The significant benefit is that the drive remains functional and can be safely reused or resold, allowing you to recover some of its value.
Physical Destruction: This is exactly as it sounds—shredding, crushing, or degaussing (using powerful magnets to scramble the data). This method is absolute. It demolishes the storage media, making data recovery physically impossible. This is the only option for drives that are already non-functional or when corporate policy demands total annihilation of the asset.
The right choice depends on your internal security policy and whether your retired IT assets still hold any resale value. We offer both services and provide a detailed Certificate of Destruction that clearly states which method was used for every single asset.
Ready to build a secure, compliant, and fully documented IT asset disposition strategy? The team at Atlanta Computer Recycling is here to provide the certified data destruction services your business needs, backed by the audit-proof documentation that delivers complete peace of mind.
Secure Your Data and Get Your Certificate of Destruction with Atlanta Computer Recycling