Atlanta Data Destruction: A C-Suite Guide to Secure ITAD
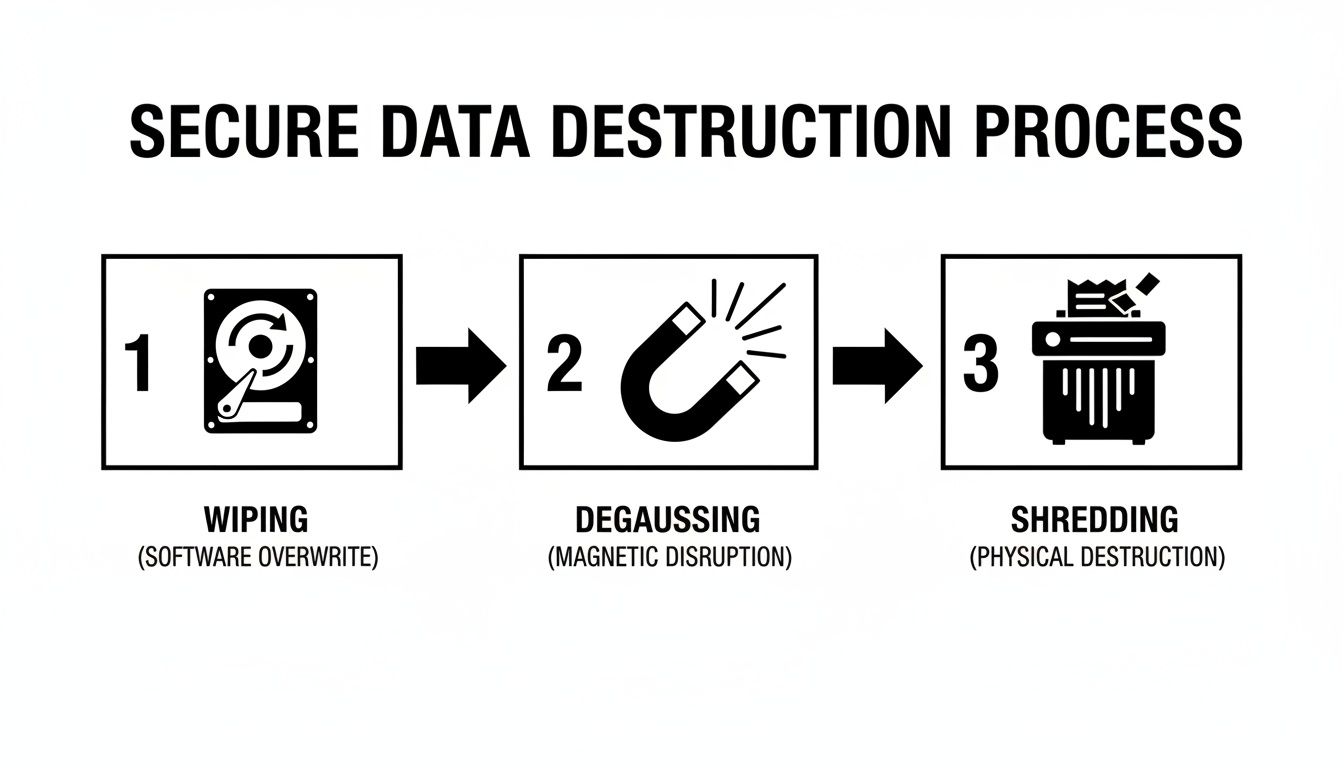
Data destruction is the certified process of ensuring information stored on your decommissioned IT assets is permanently and irretrievably destroyed. This goes beyond simple file deletion. Professional data destruction involves validated methodologies such as software-based wiping, physical shredding, or degaussing to permanently eliminate data on retired IT assets.
Why Secure Data Destruction Is Non-Negotiable for Atlanta Businesses
In Atlanta's competitive business landscape, your company’s data is a critical asset. However, if compromised, it becomes a significant liability. The outdated hard drives, servers, and corporate mobile devices residing in your storage closets are not just obsolete hardware—they are latent security risks.
It's tempting to deprioritize asset disposition, but Atlanta-based enterprises face tangible threats and stringent regulatory pressures that demand a proactive strategy.
Many local corporations, particularly in the healthcare and financial sectors, are governed by strict compliance mandates. Regulations like the Health Insurance Portability and Accountability Act (HIPAA) and the Fair and Accurate Credit Transactions Act (FACTA) have zero tolerance for improper handling of sensitive data. A single mishandled hard drive can trigger substantial fines, regulatory audits, and litigation that can severely impact your company's financial health and market reputation.
The Real-World Consequences of a Data Breach
This is not a theoretical risk. Atlanta has witnessed the devastating impact of a data security failure firsthand. The 2018 Atlanta ransomware attack served as a stark wake-up call, becoming the largest successful breach of its kind against a major American city.
The attack incurred $2.7 million in direct recovery costs and, more critically, resulted in the permanent loss of years of vital city data, including legal records and police dashcam footage. It is a powerful case study on why a robust, secure IT asset disposition (ITAD) plan is an essential component of corporate risk management.
The initial alert from that incident underscores how rapidly a security crisis can escalate, causing immediate and severe operational disruption. The fallout from such events extends far beyond the initial financial outlay.
Protecting More Than Just Your Data
Ultimately, professional Atlanta data destruction is a core function of modern corporate governance. It is not merely about checking a compliance box; it is about safeguarding your company's most invaluable assets: its reputation and customer trust.
When a data breach makes headlines, the financial cost is only the beginning. The long-term damage to your brand equity can be far more significant.
A proactive data destruction strategy is one of the most effective safeguards against both regulatory penalties and reputational harm. It transforms a potential liability into a controlled, secure, and documented process, giving you complete peace of mind.
Consider secure ITAD as an insurance policy for your data integrity. It guarantees that from the moment a device is designated for retirement until its final disposition, your sensitive information is secured. This encompasses everything from server hard drives to any data-bearing device, all managed within a responsible electronics disposal framework.
The process establishes a clear, auditable chain of custody that proves your company performed its due diligence—an invaluable asset in today's security-conscious business environment. By prioritizing secure data destruction, you are actively mitigating the tangible risks present in the Atlanta market.
Your Data Destruction Options Explained
When retiring corporate technology, selecting the appropriate data destruction method is a critical business decision. For any Atlanta enterprise, the choice hinges on two key factors: the residual value of the hardware and the sensitivity of the data it contains.
You have two primary options: software-based wiping, which preserves the hardware for remarketing, and physical destruction, which offers absolute data security. Making the right strategic choice is crucial. One path maximizes the return on your IT investment. The other provides indisputable security. An incorrect decision can be costly—either in lost revenue or, more critically, a catastrophic data breach.
Software Wiping for Asset Remarketing
For functional servers, laptops, or computers with residual market value, software wiping is the optimal solution. This process utilizes specialized programs to overwrite every sector of a storage device with random characters, rendering the original data completely irrecoverable. The hardware remains fully intact and ready for resale or redeployment.
The industry standard for secure data erasure is the DoD 5220.22-M 3-pass wipe. This U.S. Department of Defense protocol is a proven, thorough methodology.
- Pass 1: Overwrites the drive with a specific character.
- Pass 2: Overwrites with the complement of that character.
- Pass 3: Overwrites with random characters and verifies the entire process was successful.
This is the ideal approach for typical equipment refresh cycles. When upgrading technology that still holds value, data wiping allows you to capture that value securely. For a deeper technical overview, review our guide on how to securely wipe a computer hard drive. It’s a secure, auditable process that satisfies most corporate governance policies while contributing positively to your IT budget.
Physical Shredding for Ultimate Security
For certain data, there is no acceptable margin of error. When a hard drive is end-of-life, damaged, or contained data so sensitive that even a negligible risk is unacceptable, physical destruction is the only viable option. This method doesn't just erase data; it annihilates the physical media, providing absolute, irreversible proof that the data is permanently gone.
Industrial shredders take hard drives, SSDs, backup tapes, and other storage media and reduce them to small, irrecoverable fragments. For Atlanta’s robust healthcare and financial sectors, this is a non-negotiable requirement. Regulations like HIPAA do not merely recommend secure disposal—they mandate it.
There is no recovery from physical shredding. It is the most secure form of data destruction available, providing a clear, permanent, and defensible end to the media's lifecycle. It delivers absolute peace of mind when data sensitivity outweighs asset value.
Comparing Data Destruction Methods for Your Business Needs
The decision to wipe or shred must be made on an asset-by-asset basis, aligned with your strategic goals. This comparison provides a clear framework for your IT and finance teams to make informed decisions, ensuring each device is processed appropriately.
| Method | Best For | Compliance Suitability | Key Benefit |
|---|---|---|---|
| DoD 3-Pass Wiping | Functional assets with resale or reuse value, such as laptops, servers, and desktops. | Meets most corporate governance and data privacy standards like GLBA and SOX. | Preserves Asset Value: Allows for remarketing or internal redeployment, generating ROI. |
| Physical Shredding | End-of-life, damaged, or non-functional hard drives, SSDs, and backup tapes. | The highest standard, ideal for HIPAA, FACTA, and protecting top-secret data. | Absolute Security: Offers undeniable proof of destruction, eliminating all recovery risk. |
Ultimately, this is a strategic decision, not just an operational one. A technology firm decommissioning a server farm can wipe the drives and recoup a significant portion of its initial investment. A hospital retiring patient-facing terminals must shred them to ensure HIPAA compliance.
A qualified Atlanta data destruction partner will assist in asset segregation and apply the correct methodology to each device, creating an ITAD plan that is both economically efficient and regulatorily sound.
Building Your IT Asset Disposition Playbook
A reactive approach to IT asset disposition is a significant business vulnerability. Waiting until a data center is decommissioned or an office lease expires creates unnecessary risk and logistical challenges. A proactive IT Asset Disposition (ITAD) playbook is your most effective defense, transforming a potential crisis into a controlled, secure, and fully auditable business process.
This playbook serves as a standard operating procedure for your IT and facilities management. It should detail every step, from the moment an asset is identified for retirement to the final receipt of the Certificate of Destruction. The goal is not to create rigid bureaucracy but to establish a clear, repeatable process that insulates your business from data breaches and compliance failures. For any enterprise operating in Georgia, a well-defined strategy for Atlanta data destruction is a fundamental aspect of modern corporate governance.
To build a truly robust ITAD playbook, you must consider the entire asset lifecycle. For a comprehensive overview, this guide on understanding Asset Lifecycle Management provides an excellent strategic framework.
The Initial Inventory and Segregation
The first step in any ITAD project is a comprehensive asset inventory. This requires a detailed audit of every asset slated for disposal—servers, desktops, laptops, networking equipment, and mobile devices.
This inventory must capture critical data points for the process to be effective:
- Asset Tag or Serial Number: Essential for precise tracking and chain-of-custody documentation.
- Device Condition: Document whether the asset is functional, damaged, or non-operational.
- Data Sensitivity Level: Classify devices based on the data they housed (e.g., public, internal, confidential, or regulated data like PII or PHI).
- Potential Resale Value: Identify newer, high-value equipment that is a candidate for data wiping and remarketing to maximize ROI.
Once inventoried, the assets must be physically segregated. Designate distinct pallets or secure areas for assets marked "for remarketing" versus those tagged "for destruction." This fundamental organizational step prevents costly errors, ensuring a high-value server isn't accidentally destroyed and a drive containing sensitive financial data isn't merely wiped.
Coordinating Logistics and Vendor Pickup
With assets inventoried and segregated, the next phase is coordinating the physical removal with your chosen ITAD vendor. This stage requires clear communication to minimize disruption to your business operations. A professional IT Asset Disposition partner will work with your team to schedule a pickup that aligns with your operational timeline.
Your primary responsibility is to ensure the vendor has clear, secure access to the equipment. Consolidate all assets in a single, secure location to streamline the pickup process. Your ITAD partner should provide the necessary logistics, including pallets, secure containers, and trained personnel for safe packing and loading. This is also the official start of your documented chain of custody.
Before any asset leaves your premises, ensure your vendor provides a signed transfer of custody document. This initial paperwork should detail the number of pallets or containers being removed and serves as the first link in an unbroken audit trail.
Chain of Custody: The Unbreakable Audit Trail
The chain of custody is unequivocally the most critical component of your ITAD playbook. It is the chronological documentation that tracks the possession, control, transfer, and final disposition of your assets. This is not just a best practice; for regulated industries, it is a legal requirement.
Your vendor must scan the serial number of every data-bearing device as it is processed at their secure facility. This meticulous audit reconciles the initial pickup manifest with the final disposition report, ensuring zero asset loss.
This diagram illustrates the secure pathways your assets will take, from software wiping to physical shredding.
As shown, the workflow demonstrates how different asset types are routed to the appropriate destruction method, all under the strict governance of the chain of custody.
The Certificate of Destruction: Your Proof of Compliance
The final deliverable in any secure data destruction project is the Certificate of Destruction (CoD). This document is your official, legally defensible proof that your data was destroyed in accordance with industry standards and regulatory requirements.
A legitimate CoD is more than a simple receipt. It must contain:
- A unique certificate serial number.
- The exact date the assets were processed and destroyed.
- The specific destruction method utilized (e.g., DoD 5220.22-M wiping, physical shredding).
- A detailed, serialized list of every hard drive or device destroyed.
- A statement of compliance, affirming the process adheres to regulations like HIPAA or FACTA.
This document formally closes the loop on your ITAD process. It should be archived indefinitely as your primary evidence of due diligence in the event of an audit or legal inquiry. Your corporate playbook must specify the storage and retention policy for these critical certificates.
Finding the Right Data Destruction Partner in Atlanta
Your IT asset disposition playbook is only as effective as the partner you select to execute it. Choosing the right firm for your Atlanta data destruction needs is the most critical decision in this entire process. Opting for the lowest bidder is a common but dangerous shortcut that can expose your organization to significant risk.
A qualified partner should be viewed as an extension of your security and compliance teams, not merely a disposal service. They are the final, crucial link in your data's lifecycle. A vulnerability at this stage can compromise your entire chain of custody, potentially leading to data breaches and severe regulatory penalties.
Look Beyond Price to Essential Certifications
When vetting potential vendors, your initial filter should be their industry certifications. These are not merely marketing logos; they represent a commitment to rigorous, third-party audited standards for security, environmental responsibility, and operational integrity.
For any enterprise in the Atlanta region, two certifications are non-negotiable:
- NAID AAA Certification: This is the undisputed gold standard for the data destruction industry. A NAID AAA certified partner has passed stringent, unannounced audits covering their hiring practices, facility security, destruction protocols, and insurance coverage. It is your assurance that they operate at the highest level of security.
- R2 (Responsible Recycling) Certification: This certification focuses on environmental compliance and worker safety. An R2 certified partner guarantees that your e-waste is managed ethically and sustainably, ensuring your retired assets do not end up in landfills or contribute to illegal overseas dumping.
When a vendor holds both NAID AAA and R2 certifications, you can be confident that your data security and corporate social responsibility objectives are fully met.
Vetting a Vendor: A Checklist for Atlanta Businesses
Once you have shortlisted partners with the necessary credentials, it's time to conduct due diligence on their processes. A reputable provider will welcome detailed questions and be fully transparent about their operational procedures.
Here are the critical questions every Atlanta business should ask a potential ITAD partner:
- Describe Your Chain-of-Custody Protocol in Detail. They should be able to articulate a comprehensive, documented process that tracks every asset by serial number from your facility to its final disposition. Inquire about secure, GPS-tracked vehicles, access-controlled facilities, and employee background checks.
- Do You Offer Both On-Site and Off-Site Destruction Services? A flexible partner can accommodate your specific security requirements. On-site shredding provides maximum transparency for highly sensitive data, while secure off-site processing is often more efficient for large-scale projects.
- What Are the Specifics of Your Liability Insurance? A professional vendor will carry substantial professional liability insurance that explicitly covers data breaches. This is your financial protection in the unlikely event of a security incident.
- May I Review a Sample Certificate of Destruction? Scrutinize their documentation. A proper certificate is a legally binding document that details every destroyed serial number, the method used, and includes a signed statement of compliance.
- How Do You Manage Assets Designated for Resale? If you plan to remarket equipment, inquire about their data wiping process. They must use verifiable, auditable software meeting standards like the DoD 5220.22-M wipe and provide serialized erasure reports.
Don't underestimate the value of local expertise. A partner based in the Atlanta metro area understands the local logistics—from navigating a pickup in a downtown high-rise to servicing a sprawling corporate campus in the suburbs. This local knowledge ensures a smoother, more reliable service experience.
Vendor selection is a high-stakes decision. The right Atlanta data destruction partner delivers more than a service; they deliver certified peace of mind. By prioritizing certifications, process transparency, and robust insurance, you can secure a partner that truly protects your organization.
Handling Large-Scale Data Destruction Projects
Managing the disposition of a few dozen laptops is a routine task. Decommissioning an entire data center or executing a district-wide technology refresh presents a challenge of a different magnitude.
For large corporations, healthcare systems, and data centers in Atlanta, the complexities of data destruction are amplified by scale. These large-scale projects demand a level of logistical precision, security oversight, and project management that standard ITAD services cannot provide. A single procedural failure can result in a major data breach, compliance violations, and operational disruption. Success requires a strategic partner with proven experience in large-scale Atlanta data destruction.
The Intricacies of Data Center Decommissioning
Data center decommissioning is one of the most complex, high-stakes operations an IT organization will undertake. It involves the secure removal and sanitization of hundreds, or even thousands, of data-bearing assets. Every device, from server hard drives and storage arrays to switches and routers, must be meticulously inventoried and tracked.
The process requires a robust project management framework to ensure a seamless transition without impacting live operations. A qualified partner will assign a dedicated project manager to coordinate every detail.
- On-site Asset Inventory: Technicians create a detailed manifest on-site, capturing serial numbers for every drive and device before any equipment is moved.
- Secure Equipment Removal: A specialized logistics team handles the de-installation and packing of heavy, sensitive server equipment according to industry best practices.
- Guaranteed Data Sanitization: Every storage device is processed according to predefined security protocols, whether that involves DoD-standard wiping for remarketing or on-site shredding for maximum security.
For executives navigating this complex undertaking, our guide on the data center decommissioning process provides a clear, strategic roadmap.
Managing Bulk IT Refresh Cycles
Large corporations and educational institutions are familiar with the logistical challenges of bulk IT refresh cycles. Every few years, thousands of assets reach their end-of-life simultaneously, creating a significant logistical and security burden. Managing this influx requires a partner with the capacity for high-volume processing and impeccable accuracy.
The key to success is a scalable, repeatable process that ensures every single device is accounted for and sanitized. This diligence prevents former employee laptops or student devices from becoming the source of a future data breach.
A successful bulk refresh project hinges on an unbroken chain of custody. From the moment devices are collected from multiple locations to their final certified destruction, every asset must be tracked by serial number to ensure 100% accountability.
Planning for Physical and Digital Risks in Atlanta
Atlanta-based businesses face a unique combination of digital and physical risks. Beyond cyberattacks, regional weather patterns pose a tangible threat to IT infrastructure. According to NOAA's National Centers for Environmental Information, Georgia has experienced 134 weather and climate disasters since 1980, each causing over $1 billion in damages.
These events underscore why a professional ITAD strategy is a critical component of any business continuity and disaster recovery plan.
Consider a scenario where a severe storm damages your facility or data center. Your disaster recovery plan is activated, but what is the protocol for the compromised, water-damaged servers and hard drives? Leaving them unsecured during the chaos of recovery presents a massive security vulnerability. A reliable ITAD partner can be deployed to securely remove and destroy these compromised assets, ensuring a physical disaster does not escalate into a digital one. This is the kind of strategic foresight that protects an organization when it is most vulnerable.
Your Atlanta Data Destruction Questions Answered
Even with a well-defined ITAD strategy, specific questions often arise during implementation. Based on our experience with Atlanta businesses, several key queries frequently emerge. We have compiled these common questions to provide clear, actionable answers, enabling you to execute your plan with confidence.
Addressing these details ensures the integrity of your data security posture. Let's eliminate any potential weak links in your process.
What Is the Difference Between Wiping and Shredding?
This is the most common question we receive, and the answer is determined by the intended final disposition of the hard drive.
Data wiping, or sanitization, is a software-based process. It overwrites all data on a hard drive with random characters, making the original information completely irrecoverable. The drive itself remains physically intact and functional. This is the appropriate choice for assets intended for resale, donation, or internal redeployment.
Physical destruction is the complete physical obliteration of the device. We use industrial shredders to reduce the media to small fragments, making data retrieval impossible. This is the definitive end-of-life solution for obsolete or damaged drives, or for media containing data so sensitive that absolute proof of destruction is required.
Is On-Site or Off-Site Service Better?
The optimal choice depends entirely on your organization's security policies, compliance requirements, and logistical constraints.
-
On-site destruction offers the highest level of security and transparency. A mobile shredding vehicle comes to your Atlanta location, allowing your team to witness the physical destruction of your assets. For organizations in healthcare, finance, or government, where regulations like HIPAA demand an unbroken chain of custody, this is often the mandated option.
-
Off-site destruction is typically more cost-effective and operationally efficient, particularly for large-volume projects like a data center decommission or a company-wide refresh. When partnering with a certified vendor, your devices are securely transported in locked, GPS-tracked vehicles to a monitored, access-controlled facility for processing. A robust, documented chain of custody is essential for this service.
Why Do I Need a Certificate of Destruction?
A Certificate of Destruction is not merely a receipt; it is your legally defensible proof of compliance. In the event of an audit or legal inquiry, this formal document serves as your primary evidence that you took proactive and appropriate measures to protect sensitive data.
A proper Certificate of Destruction creates an unbroken, auditable trail from your facility to the final disposition of your assets. It should be archived indefinitely as a core component of your company's risk management and compliance records.
This document details precisely what was destroyed, the method used, the date of destruction, and includes a serialized inventory of every processed asset. To understand the critical components, you can review the elements of a Certificate of Destruction.
How Do I Ensure Regulatory Compliance?
Achieving compliance with standards like HIPAA, FACTA, or GLBA requires more than just selecting a destruction method. It demands a fully documented and auditable process from start to finish.
The single most critical step is to partner with a certified Atlanta data destruction provider—specifically, one that holds a NAID AAA certification. These vendors are experts in regulatory requirements. They have audited and verified processes for secure chain-of-custody, meticulous asset tracking, and detailed certification. This partnership provides the complete, defensible audit trail necessary to protect your organization from significant fines and legal exposure.
Ready to implement a secure and compliant ITAD program for your Atlanta business? Atlanta Computer Recycling provides certified, reliable data destruction services tailored to your security needs. Contact us today to schedule your secure pickup.