A Business Leader’s Guide to Corporate Computer Recycling & Secure IT Asset Disposition
That collection of old computers, servers, and monitors in your storage closet is more than just clutter. It's a significant security, financial, and compliance risk for your company. A professionally managed corporate computer recycling program isn't a discretionary "green" initiative; it's a critical component of modern corporate risk management.
Beyond "Going Green": The Business Case for Professional ITAD
Treating retired IT assets as an afterthought is a common—and potentially catastrophic—mistake. Without a formal IT Asset Disposition (ITAD) strategy, your organization is exposed to consequences that far outweigh the cost of proper disposal.
Every retired laptop and server contains a digital history of your company's operations: sensitive client data, financial records, employee PII, and proprietary trade secrets. Simply deleting files or stockpiling hardware is not a security strategy; it's a liability. A single un-sanitized hard drive falling into the wrong hands can trigger a brand-damaging data breach, turning a routine hardware refresh into a corporate crisis.
The Real Costs of Inaction
The financial and legal stakes are substantial. Failure to comply with data protection regulations is a direct threat to your bottom line.
- Crippling Fines: A violation under frameworks like HIPAA or GDPR can result in fines reaching into the millions, depending on the severity of the data exposure.
- Data Breach Fallout: The average cost of a data breach is staggering, encompassing forensic investigations, legal fees, customer notifications, and credit monitoring services.
- Reputational Damage: Trust is a core business asset. A breach traced to negligent disposal practices can drive customers directly to your competitors.
A proactive recycling plan fundamentally shifts your perspective from disposal as a cost center to a strategic investment in risk mitigation. It’s about controlling the end-of-life for every asset to ensure it cannot become a future liability.
The table below outlines the specific business risks at stake.
| Key Risks of Neglecting a Formal ITAD Policy | ||
|---|---|---|
| Risk Category | Potential Impact on Your Business | How a Professional Partner Mitigates It |
| Data Security Breach | Unauthorized access to client data, financial records, or intellectual property, often leading to massive financial loss and legal action. | Certified data destruction (shredding or wiping) with a full chain-of-custody ensures no data is recoverable from retired drives. |
| Regulatory Non-Compliance | Fines from regulations like HIPAA, GDPR, or PCI-DSS can be severe. A single misstep can cost millions and trigger lengthy audits. | A certified vendor understands these complex laws and provides documentation (like Certificates of Destruction) to prove compliance. |
| Reputational Harm | Public trust is shattered. A data breach linked to poor disposal practices can destroy brand credibility and drive away loyal customers. | Working with a professional demonstrates a commitment to security and responsibility, protecting your brand's image. |
| Environmental Violations | Improperly dumping e-waste can lead to fines for violating environmental laws and contributes to a growing global pollution problem. | Certified e-recyclers ensure hazardous materials are handled safely and valuable components are recovered, not sent to a landfill. |
Failing to act isn't a passive choice; it's an active gamble with your company's future.
The E-Waste Mountain Keeps Growing
The sheer volume of electronics being discarded by businesses is a global challenge. In 2022, the world generated an astonishing 136 billion pounds of electronic waste.
The most alarming statistic? Nearly 78% of it was never formally collected or recycled. This uncontrolled growth not only strains the environment but also creates a vast, unregulated gray market for old electronics—and the sensitive corporate data they still contain.
This is precisely where a dedicated corporate computer recycling program proves its value. It’s not just about disposing of equipment; it's about executing a secure process that protects your company, your customers, and the planet. To learn more, see our detailed breakdown of the environmental impact of electronic waste.
By partnering with a certified recycling provider, you guarantee that every device is handled securely, all data is verifiably destroyed, and valuable materials are returned to the supply chain. You transform a potential liability into a documented, compliant, and responsible business process.
Developing Your Internal IT Asset Disposition Playbook
Waiting until a hardware refresh creates a pile of old equipment is not a strategy—it's a recipe for a data breach or compliance violation. A reactive approach to corporate computer recycling invites risk.
The solution is a documented, repeatable IT Asset Disposition (ITAD) playbook. This isn't just a manual on a shelf; it's a clear set of internal policies that govern every device from procurement to its final, secure disposal.
This process requires cross-functional collaboration and executive buy-in. Assemble a team of key stakeholders:
- IT Leadership: Owns the technical execution, from asset tracking to data sanitization.
- Finance Department: Tracks asset depreciation and any potential value recovery.
- Legal & Compliance: Ensures the playbook satisfies all regulatory requirements, such as HIPAA or GDPR.
Building a solid playbook aligns your internal processes with the broader requirements for effective data security and compliance.
This isn't about creating bureaucracy. It's about replacing disorganized risk with a structured, strategic approach that protects the entire organization.
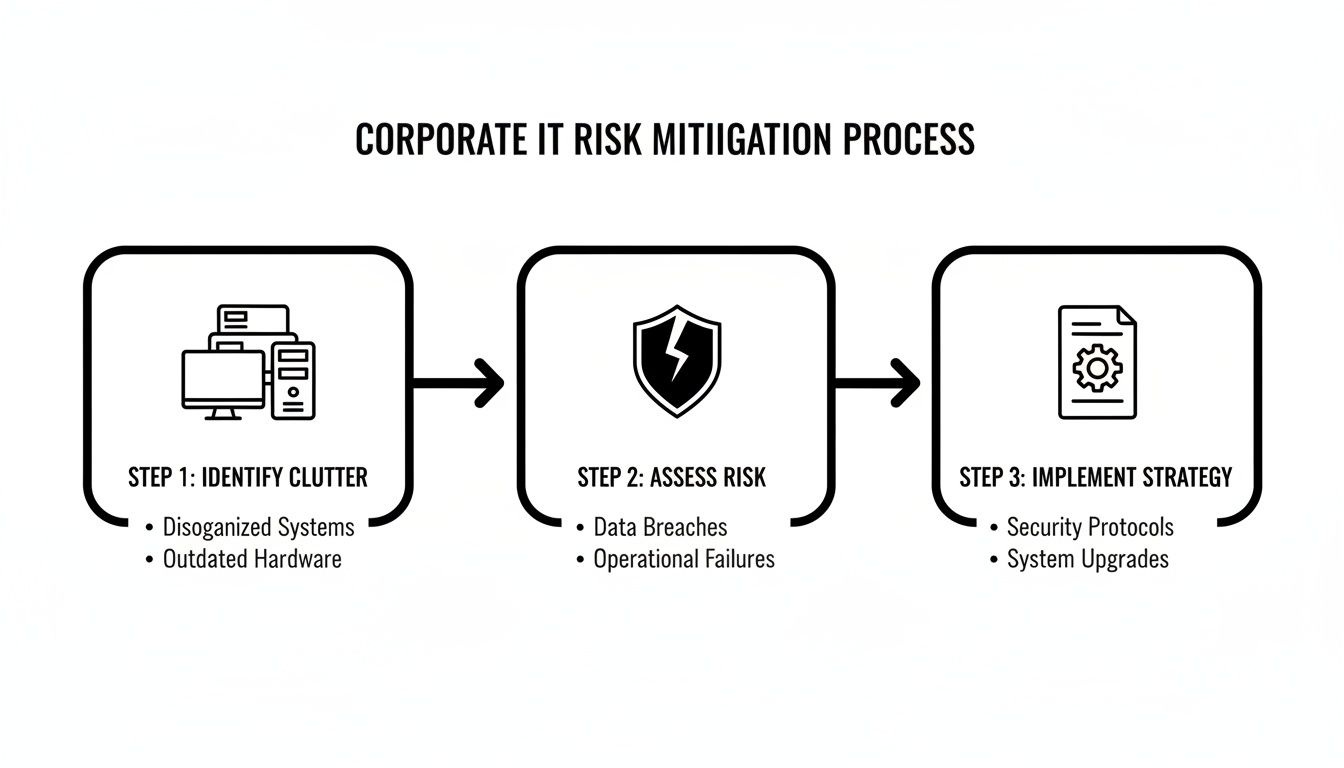
As the graphic illustrates, transitioning from vulnerability to a secure strategy requires a documented plan, not just good intentions.
Establishing Airtight Asset Tracking
You cannot protect what you do not track. An effective ITAD playbook begins the moment a new device is deployed, not when it is decommissioned. The objective is an unbroken chain-of-custody that follows every asset throughout its entire lifecycle.
Implement a robust inventory management system. Every laptop, server, and hard drive should receive a unique asset tag, which is scanned and logged into a central database. This record must capture essential details: serial number, assigned user, deployment date, and current status.
This level of detail makes it nearly impossible for a data-bearing device to "disappear" during a hardware refresh or office relocation. It provides an auditable trail that is invaluable for both internal security governance and external compliance audits. To understand the fundamentals, it's worth reviewing what IT Asset Disposition truly is and how it integrates into your operations.
Defining Your Data Destruction Standards
With a clear inventory of all assets, the next critical step is to define precisely how data will be destroyed. This policy must be specific, outlining different methods based on the asset type and its intended disposition.
Your playbook should provide a clear decision-making framework for your IT team.
- For devices intended for reuse or resale: A software-based data wipe using a recognized standard like DoD 5220.22-M 3-pass is the appropriate method. This process overwrites data multiple times, rendering it unrecoverable while preserving the hardware's functionality.
- For failed drives, obsolete hardware, or assets containing highly sensitive data: Physical destruction is the only method that guarantees total data annihilation. The drive is mechanically shredded into small, unsalvageable fragments.
Having these standards codified in your policy removes ambiguity. It ensures every team member follows the same secure procedure, eliminating risky ad-hoc decisions with company data. In an audit, this documented consistency is your best defense.
Choosing the Right Data Destruction Method for Your Assets
With an internal playbook established, the next decision is selecting the appropriate data destruction method for your retired computers. This is the most critical step for security, and a misstep can lead to significant legal and financial consequences. The objective is straightforward: ensure data is irretrievably destroyed.
Failure to properly sanitize equipment is not merely a technical oversight; it's a legal liability. As legal experts note, Business Litigation May Follow Data Breaches, making this step essential for protecting your company. The right method depends on the asset's condition, its future use, and your compliance requirements.
Software Wiping for Assets with a Second Life
For functional computers and hard drives intended for resale or redeployment, software-based wiping is the correct approach. This goes beyond simple file deletion; it uses specialized software to overwrite every sector of the drive with random data, making the original information unrecoverable.
The industry gold standard is the DoD 5220.22-M 3-pass wipe. Trusted by government agencies, this rigorous method involves:
- Pass 1: Overwriting the entire drive with zeros.
- Pass 2: Overwriting it again with ones.
- Pass 3: A final overwrite with random characters, followed by verification.
This layered sanitization ensures data is destroyed beyond the reach of recovery tools while leaving the hardware fully functional. It is the ideal method for extracting residual value from retired IT assets without compromising security. We provide a full breakdown of professional hard drive destruction services for further reading.
A DoD 3-pass wipe provides the security assurance needed to place assets into the secondary market. This allows your business to offset recycling costs by selling refurbished equipment, all while possessing a certificate proving data was destroyed to an accepted industry standard.
Physical Destruction for Total Data Annihilation
In certain situations, software wiping is not feasible or sufficient. For non-functional drives, older SSDs, or devices that stored highly sensitive data, physical destruction is the only method that provides 100% certainty of data elimination.
This approach is non-negotiable in several key scenarios. A software wipe cannot be performed on a drive that will not power on. It is also the recommended method for most Solid-State Drives (SSDs), as their flash memory architecture can make software wipes less reliable than with traditional magnetic disks.
Furthermore, stringent compliance frameworks like HIPAA often mandate the complete physical destruction of any media that contained protected health information. The two primary methods are:
- Degaussing: A powerful magnet scrambles the magnetic field on a traditional hard drive platter, instantly erasing the data. This is fast and effective but only works on magnetic media (not SSDs).
- Shredding: The most definitive method. An industrial shredder grinds the drive into small, mangled pieces of metal and plastic, making data recovery impossible.
Data Destruction Methods Compared
The choice between wiping and shredding is not about which is "better" but about applying the right tool for the specific asset, its data, and the associated risk profile. A robust recycling policy removes guesswork by clearly defining these rules for your IT team.
This table provides a simple framework to guide your decision-making.
| Method | Best For | Security Level | Allows for Reuse? | Typical Use Case |
|---|---|---|---|---|
| DoD 3-Pass Wipe | Functional HDDs | High | Yes | Laptops and PCs being refurbished and resold. |
| Degaussing | Functional HDDs | Very High | No | Quick destruction of magnetic drives with sensitive data. |
| Shredding | All drive types (HDDs, SSDs), non-functional media | Absolute | No | End-of-life drives, failed SSDs, HIPAA compliance. |
Ultimately, a clear, documented policy on data destruction ensures every retired asset is handled correctly, protecting your organization from the ground up.
How to Vet and Select a Certified Recycling Partner
Selecting the right partner for your corporate computer recycling program is the most critical decision in this process. You are not merely hiring a hauling service; you are entrusting a vendor with your company's sensitive data, its compliance posture, and its reputation. A qualified ITAD partner functions as an extension of your security and compliance teams.
Your vetting process must extend beyond a price comparison. While cost is a factor, it should never be the primary driver. A low-cost provider that compromises on data security or fails to provide a transparent chain of custody can expose your business to millions in fines and brand damage, nullifying any initial savings.
The electronics recycling market is expanding rapidly. The US Electronic Goods Recycling industry is projected to reach $27.7 billion in revenue by 2025, with over 800 businesses competing for your partnership. While large waste management firms participate, specialized ITAD companies often deliver the high-security, focused services that businesses require. You can learn more about the growth of the e-waste recycling market to understand the industry landscape.
Look for the Gold Standard in Certifications
In this competitive field, industry certifications are the clearest indicator of a vendor's commitment to security, safety, and environmental responsibility. They should be a non-negotiable requirement. These certifications are not mere marketing assets; they represent rigorous, ongoing audits by independent bodies.
At a minimum, your potential partners should hold one or both of these top-tier certifications:
- R2v3 (Responsible Recycling): This comprehensive standard covers environmental and worker safety, data security protocols, and downstream vendor management. An R2v3-certified facility has a proven, secure, and documented process for handling electronics from receipt to final disposition.
- e-Stewards: Widely considered the most stringent standard, e-Stewards enforces a zero-tolerance policy for exporting hazardous e-waste to developing nations. It also mandates the highest levels of data security and environmental protection.
A partner with these certifications has already invested significantly in building a trustworthy operation. This is the first and most critical checkpoint in your vetting process.
Essential Questions for Your Vetting Checklist
Once certifications are confirmed, delve into the specifics of their operations. A reputable partner will provide detailed, transparent answers to challenging questions. Evasiveness or an inability to provide clear documentation is a major red flag.
Use this checklist during your evaluation:
- Data Destruction Methods: Do you offer both DoD 5220.22-M software wiping and physical hard drive shredding? Is on-site shredding available to meet our security policy requirements?
- Chain-of-Custody Documentation: Provide a sample of your chain-of-custody paperwork. How are our assets tracked from our facility to final destruction?
- Employee Security: Are all employees handling our equipment background-checked and trained in data security protocols?
- Insurance and Liability: What are your liability insurance limits? Provide proof of policies covering data breaches, environmental impairment, and errors and omissions.
- Downstream Vendor Audits: How do you audit your downstream recycling partners? Can you provide assurance that no materials are illegally exported?
- Reporting and Certificates: What does a final report include? Will we receive serialized Certificates of Data Destruction and Certificates of Recycling for our compliance records?
Never execute a contract without satisfactory answers to these questions. A vendor's refusal to provide clear documentation on any of these points should be an immediate disqualifier. You are seeking a strategic partner, not just a pickup service.
A thorough vetting process is fundamental to mitigating your company's risk. By asking the right questions and demanding proof of certification, you can find an electronic waste recycling company that will safeguard your assets and your reputation.
Managing Logistics: From On-Site Pickup to Final Reporting
With a policy in place and a partner selected, successful execution hinges on flawless logistics. This is what transforms a plan into a secure, compliant, and fully auditable process. Every step, from the arrival of the pickup team to the delivery of final reports, is critical.
A professional ITAD team understands the importance of minimal disruption. Whether de-racking servers in a live data center or decommissioning workstations during an office move, the process should be efficient, quiet, and professional.
From Your Dock to Theirs: Secure Transport
The physical transit of retired assets is a high-risk point in the disposal lifecycle. A certified partner utilizes secure, company-owned vehicles, often equipped with GPS tracking. This is not an optional extra; it is the only way to guarantee a direct, monitored journey from your facility to their secure processing center.
The chain-of-custody documentation must begin at your loading dock. Before any equipment is loaded, a detailed manifest is generated, reconciled against your internal asset list, and signed by representatives from both parties. This document serves as the first piece of evidence that a secure transfer of liability has occurred.
The moment your assets leave your premises, you are placing immense trust in your vendor. Secure, GPS-tracked transport is a fundamental requirement for any company that prioritizes data security. It provides auditable proof that your equipment traveled directly to the intended destination without unauthorized stops.
The On-Site Experience: What to Expect
A professional pickup service is far more than manual labor; it is a coordinated logistical operation designed to minimize the burden on your staff. For businesses in the Atlanta metro area, these on-site services are invaluable. You can see how a professional team should manage a commercial computer pickup in our detailed guide.
A top-tier vendor will manage the entire on-site workflow:
- De-installation and Asset Tagging: Technicians disconnect equipment from desks or server racks, verifying serial numbers against the manifest as they work.
- Secure Packing: Assets are carefully packed into secure containers or palletized and shrink-wrapped on-site to prevent damage and ensure asset integrity during transit.
- Minimal Business Interruption: A professional team works around your operational schedule, offering after-hours or weekend services to avoid disrupting your employees and business activities.
This level of service frees your IT team from the labor-intensive task of preparing assets for disposal, allowing them to focus on value-added projects that drive your business forward.
The Final Reporting Package: Your Proof of Compliance
Once your assets have been processed, the final step is the delivery of a comprehensive reporting package. This is not merely a receipt; it is your legally defensible audit trail, proving that you followed a compliant and responsible disposal process. A vendor's inability to provide this is a critical failure.
Your final package must include three key documents:
- A Serialized Asset List: This report details every item received, reconciled against the serial numbers on the initial pickup manifest, confirming all assets were accounted for.
- Certificates of Data Destruction: A formal certificate must be issued for every data-bearing device. This document specifies the method of destruction (e.g., DoD 3-pass wipe or physical shredding) and is tied to the device's unique serial number.
- Certificates of Recycling: This final document confirms that all non-reusable materials were processed in an environmentally responsible manner, in full compliance with state and federal regulations.
This documentation is your ultimate defense. It provides the concrete, auditable proof required to satisfy internal stakeholders, external auditors, and government regulators, officially closing the loop on your ITAD project.
Answering Your Top Questions About Computer Recycling
Even with a robust plan, key questions often arise during a corporate computer recycling project. Given the high stakes, seeking clarity is essential. Here are direct answers to the most common questions from IT managers, compliance officers, and business owners.
Navigating the details of data security, value recovery, and vendor certification is complex. Having these answers helps you proceed with confidence, ensuring your program is secure, compliant, and efficient.
Data Security and Liability Concerns
A primary concern for any business leader is what happens after equipment leaves the facility. The potential impact of a data breach is significant, and understanding where your corporate responsibility ends is critical.
What happens if a data breach is traced back to my recycled equipment?
If a breach is linked to improperly disposed assets, your company could face severe regulatory fines under laws like HIPAA or GDPR, in addition to legal liability and significant brand damage.
This is precisely why selecting a certified partner with substantial liability insurance and a documented, auditable data destruction process is non-negotiable. Upon taking possession of your assets, they formally assume the liability.
Your partner's Certificate of Data Destruction is a critical legal document. It serves as your proof of due diligence and formally transfers data liability from your organization to theirs, protecting you from downstream risks.
Maximizing Value and Minimizing Costs
While security is paramount, the financial aspect of computer recycling is also a key consideration. Many businesses are unaware that their retired equipment may still hold residual value that can offset disposal costs. A strategic partner can help you recover it.
Can we get any money back for our old IT equipment?
Yes. Through a process known as IT Asset Value Recovery (ITAVR), a qualified ITAD partner will assess your retired assets for remarketing potential.
Functional equipment like newer laptops, servers, and networking hardware can be securely sanitized, professionally refurbished, and sold into the secondary market. Your partner then shares a portion of the revenue with your company, helping to offset the costs of recycling and data destruction for non-valuable items.
Clarifying Roles and Responsibilities
A common point of confusion is the level of preparation required from your internal team before the recycling partner arrives. A premier partner should make the process as seamless as possible, removing the logistical burden from your staff.
Do we need to wipe our hard drives before you pick them up?
While it's a sound internal security practice, it is not required when you work with a certified ITAD vendor. Their entire service is designed to provide guaranteed, documented data destruction at their secure facility. The chain-of-custody protocol ensures every data-bearing device is tracked from your facility to its final destruction, eliminating the need for your team to perform this work.
What’s the difference between R2 and e-Stewards certifications?
Both are top-tier certifications for responsible electronics recycling, but they have key distinctions.
- R2 (Responsible Recycling) is a broad standard covering environmental protection, health and safety, and data security.
- e-Stewards is generally considered more stringent, with a strict, absolute ban on exporting hazardous e-waste to developing countries.
The presence of either is an excellent indicator of a reputable vendor. The best-in-class partners often hold both certifications, demonstrating a comprehensive commitment to industry best practices.
Ready to implement a secure and compliant corporate computer recycling program? The experts at Atlanta Computer Recycling are here to help. We provide end-to-end ITAD services tailored for Atlanta businesses, ensuring your assets are handled responsibly from pickup to final reporting. Contact us today to schedule a secure pickup.