Atlanta Computer Disposal A Guide to Secure and Compliant ITAD for Businesses
For Atlanta businesses, professional computer disposal isn't just about getting rid of old equipment. It's the process of securely and sustainably retiring IT assets like servers, laptops, and desktops.
This is a critical business function for any organization handling sensitive corporate or client information. A proper disposal service prevents data breaches through certified data destruction and ensures you stay compliant with environmental regulations, turning a potential liability into a managed, secure process.
Why Smart Computer Disposal Is Non-Negotiable in Atlanta
Letting old IT assets pile up in a storage closet isn't just a space issue—it's a massive financial, legal, and reputational risk waiting to happen.
For businesses in Atlanta's fast-paced tech and healthcare sectors, outdated equipment is more than just clutter. It contains a detailed history of sensitive company and client data. A formal disposal strategy isn't just "good practice"; it's a crucial business function that actively protects your organization from severe consequences.
Without a documented plan, your company is exposed on multiple fronts. The most immediate threat is a data breach. A single retired hard drive that hasn't been properly sanitized can expose confidential financial records, employee information, or protected health information (PHI), leading to catastrophic results.
The Real Costs of Improper Disposal
The financial penalties for mismanaging data are steep. Regulations like the Health Insurance Portability and Accountability Act (HIPAA) impose fines that can easily cripple a business.
Beyond regulatory penalties, the cost of a data breach includes legal fees, customer notification expenses, and long-term damage to your brand's reputation. Rebuilding client trust after a breach is an uphill battle that many companies never fully win.
There's a substantial environmental cost, too. Illegally dumping electronics in a landfill releases hazardous materials like lead and mercury, which contaminate our soil and water. As global e-waste continues to grow, businesses have a corporate responsibility to manage their environmental footprint. Learn more about the environmental impact of electronic waste in our detailed guide.
Atlanta’s Unique E-Waste Challenge
This challenge is especially acute in the bustling Atlanta metro area, where tech hubs and data centers fuel rapid technology refresh cycles. This constant turnover contributes to a global e-waste problem that's projected to exceed 60 million metric tons annually by 2025.
Atlanta has made strides, doubling its overall recycling rate to 23% in 2022, but we still lag behind the national average. For IT managers, this local context means improper disposal risks not only HIPAA violations but also contributing to the 20% of contaminated recyclables found in city audits. For more details, you can discover more insights about Atlanta's recycling progress on resource-recycling.com.
By partnering with a certified IT Asset Disposition (ITAD) expert, you transform this complex challenge from a potential liability into a secure, streamlined, and compliant process. It's the essential first step toward safeguarding your organization’s future.
Building Your IT Asset Disposition Project Plan
A successful computer disposal project is won long before a single piece of equipment leaves your office. Proper planning is the difference between a secure, seamless process and a logistical nightmare riddled with security risks. Frankly, it’s the only way to get an accurate quote, establish clear accountability, and build a real partnership with your ITAD vendor.
The foundation of any good plan is a detailed inventory. This isn't just about counting devices; it's a strategic assessment of every asset you're retiring. Think of it as triage for your technology.
Cataloging Your Retiring IT Assets
Start by creating a comprehensive spreadsheet of all equipment slated for disposal. Your list needs to go way beyond "50 laptops" to be useful for an accurate quote. The more detail, the better.
- Categorize by Type: Group items like servers, desktops, laptops, networking gear (switches, routers), and peripherals.
- Note the Condition: Is the equipment functional? Does it just need a minor repair, or is it non-operational? This detail directly impacts its potential for resale and value recovery.
- Flag High-Value Items: Modern servers, enterprise-grade switches, or even newer laptops might still hold significant residual value. Identifying these early helps your ITAD partner focus on maximizing your return on investment.
This detailed catalog is the single most important document you’ll create for this project. It’s what drives the scope of work, the logistics plan, and your potential for value recovery.
A well-documented inventory doesn't just streamline the quoting process. It becomes the first official record in your chain-of-custody documentation, giving you a clean audit trail right from the start.
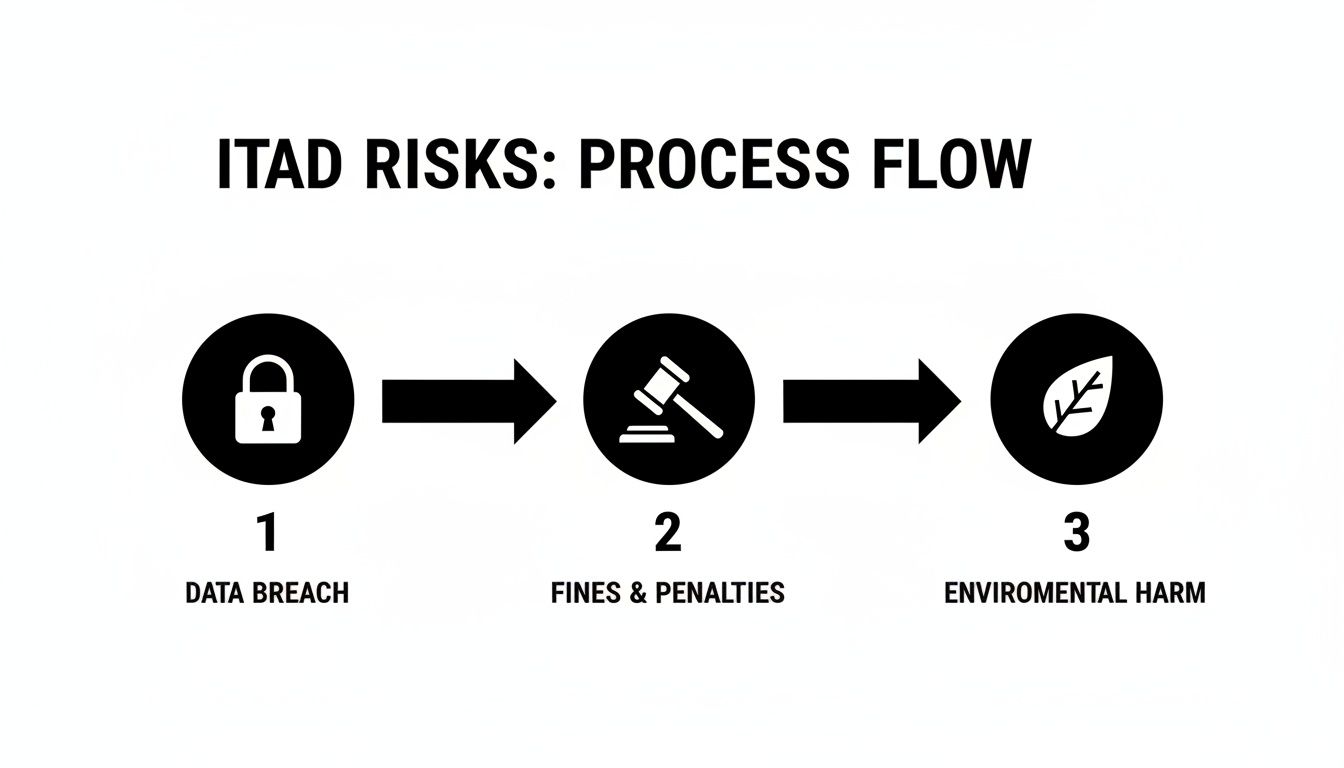
Skipping the planning phase opens the door to a whole cascade of risks, from painful data security breaches to serious regulatory fines and environmental damage. The consequences are real, and they can be costly.
As you can see, a simple data exposure can quickly snowball, leading directly to major financial penalties and lasting reputational harm.
Coordinating Project Logistics
Once your inventory is nailed down, you can start coordinating the physical removal of the assets. This part is all about careful internal planning to minimize disruption to your business operations—something that’s absolutely critical in active environments like hospitals or data centers. For a broader perspective, it can be helpful to consult an ultimate office relocation checklist, as these often cover the disposal of all types of business assets.
Work with your department heads to schedule a pickup window that avoids your busiest hours. For a large-scale project, like decommissioning a data center or clearing an entire office floor, you might need to plan for a weekend or after-hours service.
Be crystal clear with your ITAD partner about the logistics. Are the assets already palletized and waiting on a loading dock? Or will their team need to come in and de-install servers from racks on the third floor? These details are vital for a smooth, surprise-free execution.
For businesses that want an expert to handle the details from start to finish, professional IT asset disposal services provide the structure and security needed to get the job done right.
How to Choose the Right Atlanta ITAD Partner
When it comes to Atlanta computer disposal, selecting a vendor is about much more than just finding the lowest quote. This decision is a critical one, directly impacting your company's data security, legal standing, and even your reputation in the community.
Think of a true IT Asset Disposition (ITAD) partner as a risk management shield. They are your first line of defense against the very real threats that come with retiring old technology.
With your sensitive data and compliance on the line, you can't afford to take chances. The absolute first step? Verifying their certifications. This is non-negotiable.
Verifying Certifications and Security Protocols
Look for established, third-party audited certifications that prove a vendor is serious about security and environmental responsibility. Anything less is a gamble you shouldn't be making.
- R2v3 (Responsible Recycling): This is the gold standard. It means the vendor follows a strict set of rules for data sanitization, environmental safety, and worker health, covering the entire lifecycle of your old equipment.
- e-Stewards: Often seen as the most stringent certification, e-Stewards enforces a zero-landfill policy and strictly prohibits the export of hazardous e-waste to developing nations.
But certifications are just the start. You need to dig into their day-to-day security practices. Ask pointed questions like, "Can you perform on-site data destruction?" and "What does your serialized chain-of-custody documentation look like?" The confidence—or hesitation—in their answers speaks volumes.
For a deeper dive, check out our guide on how to choose an electronic waste recycling company for your business.
Here’s a pro tip: If a vendor can't immediately show you proof of their certifications, liability insurance, or sample chain-of-custody reports, that's a massive red flag. Real professionals have this documentation ready to go because they know it’s the bedrock of trust.
To help you compare potential partners, we've put together a checklist of what we look for when evaluating an ITAD provider.
Key Vendor Evaluation Checklist
This table breaks down the crucial factors to consider when you're vetting potential ITAD vendors in the Atlanta area. It's designed to help you ask the right questions and make a choice that truly protects your business.
| Evaluation Criteria | What to Look For | Why It Matters for Your Business |
|---|---|---|
| Certifications | R2v3 and/or e-Stewards certifications. Ask for their certificate numbers. | These prove the vendor adheres to the highest industry standards for data security and environmental compliance, reducing your risk. |
| Data Destruction | On-site and off-site shredding/wiping options; NIST 800-88 compliance. | You need flexible and verifiable methods to ensure your sensitive data is 100% irrecoverable, protecting you from breaches. |
| Chain of Custody | Detailed, serialized tracking from pickup to final disposition. | A clear paper trail is your proof of compliance. It shows exactly what happened to every single asset, which is critical for audits. |
| Insurance | Proof of general liability, errors and omissions, and pollution liability insurance. | This protects your business from financial loss in the rare event of a data breach or environmental incident during the disposal process. |
| Industry Experience | A track record with businesses in your sector (e.g., healthcare, finance). | An experienced partner understands your specific compliance needs (like HIPAA or SOX) and is prepared to meet them. |
| Logistics & Scope | Ability to handle the scale and logistics of your project (e.g., multi-site pickups, data center decommissions). | You need a partner who can manage the physical realities of your project without disrupting your operations. |
Ultimately, choosing the right partner comes down to finding a team that not only has the credentials but also understands your unique operational needs.
Aligning Vendor Capabilities with Your Industry Needs
Finally, make sure their experience aligns with your industry. A healthcare provider dealing with HIPAA-protected data has completely different compliance headaches than a K-12 school district or a financial services firm.
A partner with a solid history in your sector already knows the challenges you face. They’ll be ready to sign a Business Associate Agreement (BAA) for a healthcare client or manage the tricky logistics of a multi-floor office cleanout. This kind of specialized knowledge ensures your Atlanta computer disposal project isn't just done—it's done right.
Understanding Data Destruction Waving vs Shredding
When it comes to Atlanta computer disposal, nothing is more important than securing your company’s sensitive data. Once those IT assets leave your facility, you need absolute certainty that your information is gone for good.
This is where data destruction comes in. The two primary methods are software-based wiping and physical hard drive shredding. Choosing the right one isn't just a technical detail; it's a critical business decision that impacts your security, compliance, and even your bottom line. Let's break down which one is right for your equipment.
When to Choose Software-Based Data Wiping
Software wiping, also known as data sanitization, uses specialized programs to systematically overwrite a hard drive with random data, making the original information completely irrecoverable.
This approach is perfect for functional hard drives and computers that still hold resale value. By preserving the hardware, you can often recover a portion of your initial investment and contribute to a circular economy. It's a win-win for your budget and sustainability goals.
A professional ITAD partner will use methods that meet or exceed government standards, most notably NIST 800-88. This isn't just a simple delete command; it's a forensically sound process that ensures data is unrecoverable. For a deeper dive into the technical side, this guide explains how to delete a hard drive permanently.
When your ITAD partner issues a Certificate of Data Destruction, it verifies that every single serialized drive was successfully wiped to these exacting standards. This document is a critical piece of your audit trail for regulations like HIPAA.
While your focus is on making data disappear, understanding iPhone data recovery can highlight just how persistent data can be and why professional destruction on all device types is so crucial.
When Physical Shredding Is the Only Option
Sometimes, wiping simply isn't an option. Physical shredding is exactly what it sounds like: a powerful industrial machine grinds hard drives, SSDs, and other media into tiny, unrecognizable pieces of metal and plastic.
This is the only secure method in a few key scenarios:
- Failed or Damaged Drives: If a hard drive won't spin up or has malfunctioned, wiping software can't run on it. Shredding is the only way to guarantee destruction.
- Solid-State Drives (SSDs): The wear-leveling technology in SSDs can make traditional wiping methods less reliable. Shredding offers definitive, foolproof destruction for these modern drives.
- Strict Compliance Policies: For many organizations in healthcare, finance, or government, internal policies or regulations may mandate the physical destruction of all data-bearing media, no matter its condition.
Ultimately, the choice comes down to balancing security requirements, compliance rules, and the potential to recover asset value. A trusted Atlanta ITAD partner will assess your inventory and recommend the best, most secure approach for each device, ensuring your data is protected without compromise.
Managing On-Site Logistics and Chain of Custody
The moment your IT assets cross the threshold of your building is one of the most vulnerable points in the entire disposal process. This is where a well-laid plan can either come together perfectly or fall apart completely. Professional Atlanta computer disposal isn’t just about a truck showing up; it’s about a secure, documented, and efficient logistical operation that protects your equipment and your daily business.
A true ITAD partner manages this entire sequence, from carefully de-installing servers in a live data center to packing and palletizing hundreds of desktops spread across multiple office floors. The main goal is always to minimize disruption. An experienced crew works around your schedule—after hours or on weekends if needed—to make sure the project doesn't get in the way of your business.
Establishing an Unbroken Chain of Custody
The single most important document during the pickup phase is the chain of custody. This isn't just a simple receipt. It's a legal, auditable trail that tracks every single asset by its serial number from the second it leaves your control.
Think of this document as your proof of responsible transfer. It records who handled the equipment, when it was picked up, where it was taken, and confirms its safe arrival at the secure ITAD facility. Without this unbroken chain, you're left with a massive gap in your compliance and security records.
Imagine a multi-floor office cleanout in a downtown Atlanta high-rise. An experienced logistics team doesn't just pull up to the curb. They arrive with a clear plan, asset tags for every machine, secure bins for loose hard drives, and the right team to safely move everything without damaging your property or exposing sensitive gear.
The chain of custody is your assurance that nothing gets lost, misplaced, or mishandled between your office and the secure processing facility. For any business concerned with compliance, this serialized documentation is non-negotiable.
From Your Door to Final Disposition
The entire logistics process is built on accountability. A professional team makes sure every asset on your initial inventory list is accounted for before a single box is loaded onto the truck. This on-site verification prevents any discrepancies later on.
Once loaded onto a secure, GPS-tracked vehicle, your assets are transported directly to the processing facility. Upon arrival, the items are checked in again, reconciling the shipment against the original chain-of-custody record. This dual-verification process is what keeps the audit trail intact.
This meticulous tracking is what allows for the creation of the final documents you need for your records, including the all-important Certificate of Destruction. You can learn more about its critical role in compliance and why it’s so essential. This systematic approach turns a complex logistical headache into a smooth, secure, and fully documented event.
Answering Your Questions About Computer Disposal
When it comes to handling your company's old tech, we know you've got questions. Getting it right means protecting your data, staying compliant, and doing right by the environment. Here are some straightforward answers to the questions we hear most often from businesses in the Atlanta area.
What Types of Business Equipment Do You Accept?
Our focus is squarely on commercial IT assets—the kind of gear that runs your business. We're set up to handle enterprise-grade equipment, not residential electronics.
Think of us for things like:
- Computers and Laptops: Any desktops, workstations, or notebooks from your office.
- Servers and Data Center Gear: This includes rack servers, blade servers, storage arrays (SANs), and all the related hardware.
- Networking Hardware: We take enterprise switches, routers, firewalls, and access points.
- Office Peripherals: LCD monitors, keyboards, mice, and docking stations are all on the list.
Since we are a dedicated B2B service, we can't accept consumer electronics, kitchen appliances, or hazardous waste like loose alkaline batteries. The best first step is always to send over an inventory list so we can confirm exactly what we can take off your hands.
What Is the Cost of Professional Computer Disposal?
There’s no simple, one-size-fits-all price tag for IT asset disposition. The final cost depends on the unique scope of your project. For many companies, the service is surprisingly low-cost, and in some cases, it can even generate a return if your old equipment still has resale value.
A few key factors will shape your quote:
- Volume and Type: A truckload of newer servers has a totally different value and cost profile than a small pile of ten-year-old desktops.
- Logistical Needs: Is everything already palletized and sitting on your loading dock? Or do our technicians need to de-install servers from racks spread across three different floors?
- Data Destruction Services: Your choice of data destruction makes a difference. On-site physical hard drive shredding, for example, is priced differently than software-based wiping at our facility.
To get a clear picture of the cost, the best move is to request a custom quote based on your specific needs and inventory.
A detailed asset list is the key to an accurate quote. The more you can tell us upfront about makes, models, and general condition, the tighter our proposal will be. No surprises, no guesswork.
Is a Certificate of Destruction Enough for HIPAA Compliance?
A Certificate of Data Destruction is absolutely vital for HIPAA compliance, but it’s just one piece of the puzzle. It's the official, auditable proof that data on specific devices was properly destroyed, but it doesn't work in a vacuum.
To truly satisfy HIPAA's requirements, you need to prove you did your due diligence every step of the way. That means partnering with a vendor who provides a secure, documented chain of custody from start to finish. Crucially, that vendor must also be willing to sign a Business Associate Agreement (BAA).
The combination of a signed BAA and a detailed Certificate of Destruction creates the robust, defensible position you need to protect your organization.
Can We Drop Off Our Old Office Computers?
To ensure a secure, unbroken chain of custody from your door to ours, all our services are based on scheduled, on-site pickups. For that reason, we don't operate a public drop-off location.
This B2B pickup model is by design. It allows us to meet the strict security, logistical, and documentation requirements that businesses, schools, and healthcare facilities need. We handle all the logistics—from secure packing to transportation—to deliver a fully accountable and seamless service for our commercial clients.
Ready to handle your Atlanta computer disposal with a certified, secure, and reliable partner? Atlanta Computer Recycling is here to help. We provide end-to-end ITAD services tailored for Atlanta businesses, ensuring your data is destroyed and your equipment is recycled responsibly. Get your custom quote today!