Georgia Fulton County: Secure ITAD & E-Waste Guide

A lot of Fulton County IT managers are dealing with the same scene right now. A server closet or storage room has turned into a holding area for retired laptops, failed drives, old switches, monitors, and equipment pulled during upgrades that nobody wants to touch because the disposal decision carries risk.
That backlog is not just a space problem. It is a data security issue, a compliance issue, and for many organizations, a procurement and documentation issue. In georgia fulton county, those pressures show up faster because the county combines dense business activity, major healthcare operations, public institutions, and large-scale infrastructure growth in one long operating corridor.
Your Guide to IT Asset Disposal in Fulton County
The practical problem usually starts small. A refresh cycle finishes. A department moves floors. A clinic replaces imaging workstations. A school swaps classroom devices. Then the retired equipment sits because nobody wants to sign off on the wrong disposal path.
That hesitation makes sense. Fulton County is Georgia's most populous county with 1,066,710 residents as of the 2020 U.S. Census, representing about 10% of the state's population and a 15.9% increase from 2010. It was created on December 20, 1853, expanded in 1932, and now stretches 70 to 80 miles as a major business corridor for enterprises, healthcare systems, and public institutions that all generate retired IT assets that need disciplined handling (Fulton County background).
Why local scale changes the ITAD conversation
In a smaller market, an informal process sometimes survives longer than it should. In georgia fulton county, it breaks down quickly.
A hospital may have servers with protected health information. A university may have mixed inventories spread across departments. A county contractor may need property controls, serial tracking, and proof of final disposition. A data center team may be working against a strict decommissioning schedule.
Those are not the same job. They require one process framework with different controls depending on the asset class, the data type, and the owner.
What works and what does not
What works is a documented IT asset disposition process with inventory, custody controls, sanitization decisions, transportation rules, and final reporting. That is the standard business approach behind professional IT asset disposal services.
What does not work is the common shortcut list:
- Storing gear indefinitely: Delayed decisions increase loss, mix working assets with scrap, and make audit trails weaker.
- Letting departments self-dispose: Decentralized drop-offs and ad hoc handoffs create custody gaps.
- Treating all devices the same: A monitor, a network switch, and a patient-data server do not need the same controls.
- Relying on verbal confirmation: If a vendor cannot document what happened to each asset class, your organization carries the risk.
The best ITAD programs remove ambiguity before pickup day. They decide who approves release, how assets are labeled, what gets wiped, what gets shredded, and what records the organization keeps.
Fulton County’s size and mix of industries turn IT disposal into an operational discipline. If your retired equipment is sitting in a room waiting for someone to “deal with it later,” you already have the first warning sign.
Understanding the Business Risks of Improper E-Waste Disposal
An unsecured hard drive is not e-waste. It is a file cabinet full of records with the drawer left open on the curb.
That is the mistake many organizations make. They see retired equipment as a facilities issue or a recycling task. In reality, improper disposal exposes the business in three directions at once: data, legal accountability, and reputation.
Data exposure starts before the equipment leaves the building
Risk does not begin at a landfill. It begins the moment an asset is removed from service without controls.
A laptop waiting in an unlocked office. A desktop moved to a loading area without an asset tag. A stack of drives set aside for “later wiping.” Those are the points where chain of custody usually fails.
The most dangerous assumption is that deletion equals destruction. It does not. If the device still contains recoverable data, the organization still owns the exposure.
The cheapest disposal option is often the most expensive decision
Price-only buying leads organizations into bad vendor choices. If the provider cannot explain sanitization standards, transport security, downstream handling, and reporting, low cost means risk has been transferred back to you.
That matters for boards, counsel, compliance teams, and procurement officers because they will ask basic questions after an incident:
- Who released the asset
- Where it went
- Whether the data was sanitized
- Who verified final destruction or recycling
- What documentation exists today
If your team cannot answer those questions with records, your defense becomes weak very quickly.
Environmental mishandling creates business problems too
Improper e-waste disposal also damages procurement credibility and sustainability commitments. Electronics contain components that require responsible downstream handling, and organizations that treat disposal casually often discover that “recycling” was little more than a pickup followed by poor segregation or undocumented export channels.
That is why environmental controls belong in the same conversation as data security. Responsible electronic waste management practices support both compliance and operational discipline.
The reputational cost is often harder to repair than the operational mistake
Customers, patients, students, donors, and public stakeholders rarely distinguish between a cyber incident and a disposal failure. They only see that the organization lost control of sensitive information or failed to handle equipment responsibly.
A technical team can recover from a rushed refresh project. Recovering trust is harder.
If your disposal process depends on memory, goodwill, or one employee “keeping an eye on it,” it is not a secure process. It is an unmanaged exception.
The trade-off is simple. A structured ITAD process takes more planning up front. A weak process creates bigger costs later, usually when the organization has the least room for error.
Navigating Data Compliance Rules for Fulton County Organizations
Compliance in ITAD is not about collecting acronyms. It is about proving that retired assets were handled in a way an auditor, regulator, or internal review team can defend.
For many organizations in georgia fulton county, that starts with healthcare. In Fulton County, 10.1% of the population is uninsured and significant areas are designated as Health Professional Shortage Areas, which makes secure decommissioning of servers and medical devices containing patient data especially important for HIPAA risk control (Fulton County H&H Initiative context).
What HIPAA looks like in disposal operations
HIPAA does not become easier because a device is old. If a retired workstation, server, copier drive, or clinical device still stores protected data, the organization has to treat the disposal event as part of information security.
In practice, that means:
- Asset identification: Know which devices contain or may contain patient information.
- Controlled release: Only authorized staff can approve removal from service.
- Sanitization choice: Use certified erasure when the device remains functional and the media supports it. Use physical destruction when reuse is not appropriate or the media cannot be reliably sanitized.
- Documentation: Keep records that tie the asset list to the destruction or erasure result.
- Vendor oversight: A third party does not remove accountability. It adds a vendor-management obligation.
A clinic closure is where mistakes often happen. People focus on furniture, movers, and reopening dates. The copier, check-in kiosk, and old backup device get overlooked.
Other rules that matter in the same workflow
Healthcare is not the only regulated environment. Fulton County organizations also operate under financial, retail, education, contractual, and public-sector obligations.
A defensible process usually addresses these questions:
| Requirement area | What auditors care about | What your ITAD records should show |
|---|---|---|
| Healthcare data | Whether PHI stayed protected through retirement | Manifest, sanitization logs, certificates, custody records |
| Payment and financial data | Whether storage media was removed from circulation securely | Device list, method used, exception handling |
| Public sector records | Whether property and disposal procedures were followed | Approval trail, pickup records, final disposition summary |
| Contractual security terms | Whether your vendor followed required controls | Service scope, chain of custody, proof of destruction |
Defensible means repeatable and documented
A defensible disposal process has four features.
First, it is repeatable. Teams know the steps and do not invent the process each quarter.
Second, it is traceable. You can tie each asset or batch to a person, date, and disposition path.
Third, it is proportionate. A failed drive destined for shredding does not need the same remarketing workflow as a reusable laptop, but both still need documentation.
Fourth, it is reviewable. Someone outside the project can inspect the records and understand what happened without relying on oral explanation.
Good compliance records answer the obvious question without follow-up. What was the asset, who handled it, how was data addressed, and where did it end up?
Universal waste rules still matter
Data compliance and environmental compliance meet in the same workflow. Once the organization classifies retired electronics for shipment and processing, it also has to manage the material responsibly under applicable waste-handling requirements. Teams that ignore this side often overfocus on wiping and underdocument storage, packaging, and downstream processing.
A useful baseline for operations and facilities staff is understanding how universal waste handling affects electronics disposition.
The strongest Fulton County programs do not separate privacy, security, and environmental handling into isolated tasks. They treat them as one controlled release process.
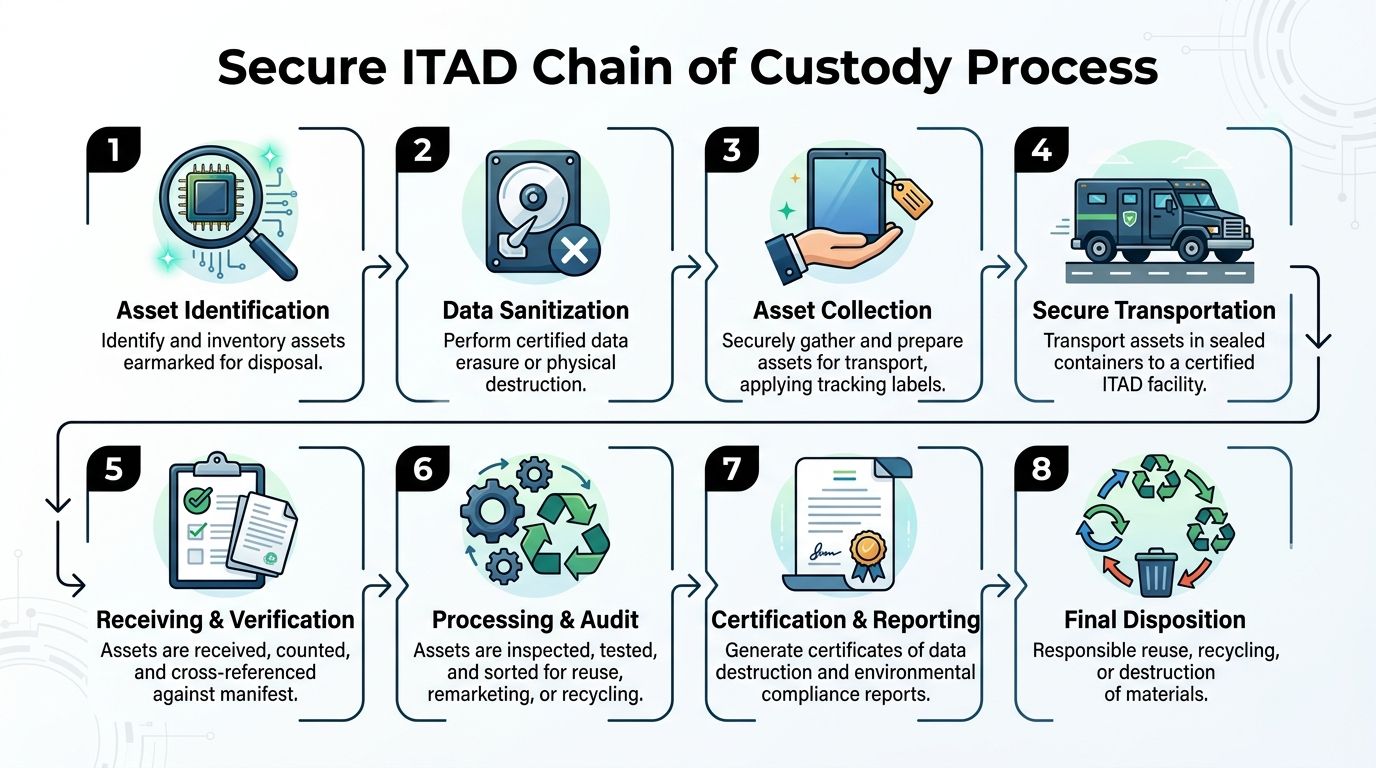
A Step-by-Step Guide to Secure ITAD Chain of Custody
Chain of custody in ITAD works like evidence handling. If you cannot show where the item was, who touched it, and what happened to it at each stage, the process has a credibility problem.
That matters even more in South Fulton decommissioning work. Atlanta’s data center leasing activity topped the U.S. in 2024, and these projects often require DoD 5220.22-M 3-pass wiping and physical shredding under tight timelines tied to construction and decommissioning schedules (South Fulton data center context).
The eight points where control is won or lost
Identify the assets early
Build the inventory before movers, facilities crews, or project contractors enter the space. Capture device type, location, ownership, and whether the asset is likely to contain sensitive data.Choose the data method before pickup
Functional systems may be eligible for certified erasure. Failed media, heavily regulated devices, and equipment with uncertain storage history often belong in a destruction path. Waiting to decide later creates exceptions.Tag and segregate equipment
Keep reusable equipment separate from scrap, and keep data-bearing assets separate from peripherals. Mixed pallets slow verification and increase error rates.Package for controlled movement
Sealed containers, documented counts, and pickup signoff matter. A rushed hallway transfer is one of the most common weak points.
What a clean handoff looks like
At pickup, the organization should be able to hand over a manifest that matches the actual load. The receiving side should verify counts against that manifest, not against memory.
For internal security teams, this is also where governance intersects with operations. Teams working through broader GRC cyber security programs usually get better ITAD outcomes because disposal is tied to policy, evidence, and risk ownership rather than treated as a one-off facilities task.
Processing decisions need rules, not improvisation
Once assets reach the processing site, they should go through a controlled verification and disposition review.
Use this simple decision model:
- Certified erasure path: Appropriate for functional devices where reuse is allowed and the media can be sanitized reliably.
- Physical destruction path: Appropriate for damaged media, obsolete storage, non-functional drives, or assets where policy requires destruction.
- Parts recovery and recycling path: Appropriate only after data-bearing components are addressed first.
Wiping is not automatically better than shredding. Shredding is not automatically better than wiping. The correct method depends on media condition, compliance obligations, and whether the device will be reused.
Final records are part of the security process
A secure process ends with records, not with a truck leaving the property.
Keep these items together for each project:
| Record | Why it matters |
|---|---|
| Asset manifest | Proves what left your control |
| Pickup and custody log | Shows who transferred and received the load |
| Sanitization or destruction result | Shows how data risk was addressed |
| Exception list | Documents missing tags, failed drives, or variances |
| Final certificate package | Supports audit, procurement, and legal review |
If you need a benchmark for the final document set, review what a formal certificate of destruction form should include and compare it to your current vendor output.
The organizations that avoid disposal disputes are rarely the ones with the cheapest process. They are the ones with the fewest custody gaps.
ITAD Solutions for Healthcare, Education, and Data Centers
A hospital network, a school district, and a data center operator can all say they need ITAD. In practice, they need different controls, different scheduling, and different paperwork.
That is where many disposal plans fail. They use one generic workflow for every sector, then spend the project handling exceptions manually.
Healthcare needs low-disruption, high-control execution
Hospitals, specialty clinics, imaging centers, and outpatient sites usually care about one thing first. Patient data must remain controlled without interrupting operations.
The disposal challenge is broader than servers. It often includes nurse station workstations, tablets, copier drives, storage appliances, biomedical support systems, and devices sitting in clinics that are being consolidated or renovated.
Healthcare teams should focus on:
- On-site preparation: Devices should be identified and staged by area so clinical operations do not have to pause while the ITAD team sorts equipment.
- Role-based release approvals: Biomed, IT, compliance, and facilities should not assume another team signed off.
- Destruction rules for edge cases: Old specialty devices and failed media should not linger because no one is sure what to do with them.
- Audit-ready records: The compliance office should be able to match the project paperwork to the site and date without asking the infrastructure team to reconstruct events.
If your privacy officer is formalizing controls, a practical tool like this HIPAA risk assessment template can help frame disposal-related questions before assets are released.
Education has volume, timing, and custody challenges
For K-12 schools and universities in Fulton County, secure ITAD is complicated by educational inequities and logistical challenges. As institutions refresh aging classroom computers, they still have to protect student records through certified data wiping, even though that control is often overlooked in public-sector e-waste plans (Fulton County community health assessment context).
School systems and higher education environments usually generate a wider mix of assets than expected. Desktop labs, teacher laptops, library systems, point-of-sale systems, access control devices, and department-owned servers all age out on different schedules.
The operational pressure points are different from healthcare:
- Summer refresh windows are short.
- Assets are distributed across many buildings.
- Ownership can be decentralized by department or grant program.
- Procurement and surplus rules may require extra approvals.
What works for education is centralized planning with decentralized collection. Each campus or building can stage equipment locally, but the district or institution should own the inventory format, release criteria, and destruction reporting standard.
A common mistake is treating student devices as low-risk because they look low-value. The hardware value is not the issue. The issue is whether the device, account history, or attached storage still contains student information.
Data centers need precision and sequencing
Data center work in South Fulton is a different category. These projects often involve racks, network gear, storage arrays, backup systems, and large quantities of high-density equipment moving under strict deadlines.
The disposal risk is not just data. It is sequencing.
If asset extraction happens out of order, the team can create delays for facilities contractors, demolition crews, lessors, or incoming operators. If drives are not separated early, the sanitization workflow bottlenecks. If reusable and scrap equipment are mixed, value recovery and reporting both suffer.
A solid data center decommissioning plan usually includes:
- Pre-project site walk
- Rack-by-rack inventory logic
- Media handling rules before hardware movement
- Staging zones for wipe, shred, and recycle paths
- Final reconciliation against the original scope
In data center work, speed only helps if the chain of custody stays intact. Fast removal without reconciliation creates cleanup work later.
Essential ITAD Documentation by Sector
| Document | Purpose | Required For |
|---|---|---|
| Asset inventory and manifest | Identifies what is being released and tracked | Healthcare, education, data centers, public sector |
| Chain of custody log | Documents each transfer of control | Healthcare, education, data centers, public sector |
| Data destruction report | Shows erasure or destruction outcome for media | Healthcare, education, finance, enterprises |
| Certificate of destruction | Formal proof of final destruction event | Regulated industries, legal review, procurement files |
| Recycling and downstream disposition report | Confirms environmental handling path | Public sector, ESG reporting, enterprise sustainability teams |
| Exception report | Records missing assets, unreadable labels, failed media, or scope changes | Large refreshes, campus projects, decommissions |
Sector-specific planning beats generic recycling
The strongest Fulton County ITAD programs treat disposal as part of operations, not a cleanup step after a refresh. Healthcare needs compliance-sensitive logistics. Education needs centralized control across distributed locations. Data centers need exact sequencing and evidence that survives project turnover.
A generic pickup vendor can remove equipment. A sector-aligned process protects the organization.
How to Select a Compliant E-Waste Recycling Partner
Most vendor evaluations start in the wrong place. They start with price, truck availability, or whether the company says it “does recycling.” Those are not useless factors, but they are not the decision criteria that protect your organization.
The better question is simpler. If something goes wrong, will this partner’s process help prove that your team acted responsibly?
What to verify before you approve a vendor
Start with evidence, not promises.
- Certifications and standards: Ask what certifications the vendor maintains and how those standards affect downstream handling, data destruction, and reporting.
- Sanitization methods: Require a clear explanation of when the vendor uses certified wiping, when it uses physical shredding, and how exceptions are documented.
- Chain of custody controls: Review sample manifests, handoff logs, serialized tracking methods, and receiving procedures.
- Insurance and liability posture: Confirm the vendor carries appropriate coverage and can explain responsibility during transport and processing.
- Local operational capability: A provider serving Fulton County should understand office pickups, hospital constraints, school scheduling, and data center timing.
Ask for documents, not marketing language
A compliant vendor should be comfortable showing examples of operational paperwork. You are not asking for slogans. You are checking whether the process exists beyond the sales conversation.
Use this quick review grid:
| Vendor question | Strong answer | Weak answer |
|---|---|---|
| How do you document pickups | Provides sample manifest and custody workflow | Says the driver “keeps track of it” |
| How do you handle failed drives | States destruction path and reporting method | Says they decide later at the warehouse |
| What does final reporting include | Lists destruction, recycling, and exception records | Promises a generic receipt |
| How do you support audits | Explains record retention and retrieval | Says no client has asked before |
Red flags that usually signal trouble
Some warning signs appear early.
One is vagueness. If the provider cannot describe its process in sequence, the process is probably inconsistent.
Another is overconfidence. “We handle everything” is not a useful answer if nobody can explain the controls.
The last is resistance to scrutiny. A serious ITAD vendor expects detailed questions from IT, legal, compliance, and procurement.
A good partner makes your internal review easier. A weak one asks you to trust undocumented habits.
Why local familiarity matters in georgia fulton county
A vendor can be technically capable and still be a bad fit if it does not understand the local operating environment. Fulton County organizations often need coordinated pickups at active sites, controlled access windows, public-sector documentation, or discreet work around patient care and academic schedules.
The best partner is not just the one with a truck and a price sheet. It is the one whose controls match your risk profile, whose records stand up in review, and whose team can execute without creating work for your staff.
Building a Sustainable and Secure Tech Lifecycle
Retired equipment should not be the least-defined part of your technology program. It sits too close to security, compliance, procurement, and sustainability for that.
A mature ITAD strategy does three things well. It protects data, it creates a clear custody record, and it channels equipment toward reuse or responsible recycling instead of informal disposal. That combination reduces operational friction because the organization no longer has to improvise every time a refresh, relocation, or closure happens.
The strongest programs treat disposal as lifecycle management
If your team waits until the storage room is full, the process is already late. Better organizations assign disposal rules when assets are deployed, not when they are finally retired.
That means procurement, IT, compliance, and facilities should agree on a few basics:
- Who approves asset retirement
- What data destruction method applies by device type
- What records must be retained
- How reusable equipment is separated from scrap
- How environmental handling supports broader sustainability goals
Responsible disposition is part of a larger circular model. Teams that want to align secure handling with reuse and material recovery should understand how the circular economy for electronics fits into business operations.
Security and sustainability support each other
Organizations sometimes frame this as a choice between strict controls and environmental responsibility. It is not.
The right process does both. It wipes or destroys data-bearing media appropriately, preserves reusable assets when policy allows, and sends non-recoverable material into documented recycling channels. That is what a modern business in georgia fulton county should expect from its IT lifecycle.
Good ITAD is not a cleanup task. It is a control point in your security and operations program.
If your current process depends on temporary storage, informal handoffs, or limited reporting, this is the right time to fix it before the next refresh cycle starts.
Atlanta Computer Recycling helps Fulton County organizations handle secure, compliant IT asset disposition with business-focused support for pickups, de-installation, hard drive wiping, shredding, and responsible electronics recycling. If your team needs a practical review of its current process, contact Atlanta Computer Recycling to discuss a safer and more efficient plan for retired IT assets.