Electronic Recycling in Atlanta, GA: A Business Guide to IT Asset Disposition

For many Atlanta businesses, retiring old electronics feels like a facilities management task—another item to check off a long list. This perspective misses a critical risk: every outdated server, company laptop, and fleet of smartphones is a potential liability.
A formal IT Asset Disposition (ITAD) strategy isn't just about environmental responsibility; it's a fundamental component of modern corporate risk management. It’s about protecting your organization from the substantial threats of data breaches, significant compliance penalties, and lasting reputational damage.
Why Atlanta Businesses Need a Formal E-Waste Strategy
Simply storing obsolete computers or allowing an uncertified hauler to remove them creates unseen vulnerabilities. The moment an IT asset containing sensitive corporate or client data leaves your premises without a documented chain-of-custody, your business is exposed. These are not hypothetical scenarios; they are tangible threats with severe financial and public relations consequences.
Managing your electronic recycling in Atlanta, GA, through a structured plan directly addresses these critical issues. It transforms a logistical chore into a proactive security and financial strategy.
Here’s why a formal approach is essential for your business:
- Mitigate Data Breach Risks: End-of-life hard drives are prime targets for data thieves. A single drive can contain customer databases, financial records, employee PII, or proprietary trade secrets.
- Ensure Regulatory Compliance: Organizations in sectors like healthcare (HIPAA), finance (FACTA), and legal services face stringent data privacy mandates. Improper disposal can trigger audits and fines that can easily reach seven figures.
- Safeguard Your Brand Reputation: Clients, partners, and stakeholders expect corporate responsibility. A publicized data breach or environmental infraction can inflict long-term damage to your brand equity.
A Real-World Business Scenario in Atlanta
Imagine an Atlanta-based healthcare provider undergoing a routine compliance audit. The auditor requests documentation proving secure data destruction for a batch of 50 retired laptops. The office manager recalls a local "recycler" offering a low-cost pickup months prior but has no Certificate of Destruction.
Suddenly, the provider has no verifiable proof that protected health information (PHI) was handled correctly. They cannot account for the chain of custody for those 50 devices. This oversight places them in direct violation of HIPAA, exposing the organization to massive penalties and a data breach notification crisis.
This scenario highlights a critical business principle.
Your company's liability for the data on its devices does not end when the equipment leaves your facility. It concludes only when you possess a verifiable, documented Certificate of Destruction from a certified ITAD partner confirming its secure and permanent destruction.
Beyond Disposal to Strategic IT Asset Management
A formal e-waste strategy is fundamentally about control, foresight, and value recovery. It establishes a clear, repeatable process for IT asset retirement, from initial inventory to final reporting. This ensures every department understands the protocol, eliminating the operational gaps that create security vulnerabilities.
Furthermore, not all retired electronics are "waste." Many assets, such as newer servers or laptops, retain significant residual value. A professional ITAD partner can test, refurbish, and remarket this equipment. This can generate a financial return to offset or even exceed the recycling costs for non-functional assets.
You can learn more about the broader environmental impact of electronic waste to see why this kind of responsible management is so crucial. Ultimately, it transforms your e-waste process from a cost center into a potential value-recovery opportunity for your Atlanta business.
Conducting Your Initial IT Asset Inventory
Before engaging a vendor or requesting a quote, you must have a precise understanding of the assets slated for disposition. An initial IT asset inventory is the foundational step that informs every subsequent decision in your e-waste strategy.
Attempting to plan without a clear inventory is like trying to budget without financial statements—you cannot secure an accurate quote or guarantee regulatory compliance.
This process involves more than a simple count of desktops in a storage closet. A proper inventory is a methodical audit of every end-of-life electronic device your business owns. The objective is to create a detailed record that serves logistical planning and, more critically, your security and compliance obligations.
This corporate responsibility also connects to a larger community effort. While Atlanta collected approximately 19,800 tons of residential curbside recycling in FY2023, business e-waste operates under a different, more stringent set of rules due to hazardous materials and data security requirements. Certified processors are essential for navigating these complexities and keeping Atlanta businesses compliant.
Categorizing Your End-of-Life Assets
Begin by sorting equipment into logical categories. This clarifies the scope of the project and helps prioritize high-risk items. It also enables a vendor to provide a more accurate and competitive proposal for your electronic recycling in Atlanta, GA.
We recommend the following breakdown:
- Data-Bearing Devices: This is your highest-risk, top-priority category. It includes servers, desktops, laptops, company smartphones, and tablets—any device that has stored corporate or customer data.
- Networking and Infrastructure Gear: This category contains switches, routers, firewalls, and server racks. While some may hold configuration data, the risk is generally lower than a hard drive containing financial records.
- Peripherals and Accessories: This includes all other items: monitors, keyboards, mice, printers, and cables. While non-data-bearing, they contain materials that require responsible recycling.
Assessing for Resale Versus Recycling
Once assets are categorized, perform a high-level assessment of their condition and potential for reuse. This evaluation determines whether an asset can be remarketed for a financial return or is destined for secure destruction and materials recovery.
Pro Tip: Do not assume older equipment is worthless. We frequently see companies generate significant returns from three-year-old servers or fleets of recent-model laptops. This revenue can substantially offset your overall project costs.
A professional ITAD partner will provide a formal valuation, but your initial notes are invaluable for planning. For each major asset, record its condition—functional, minor cosmetic damage, or non-functional. This simple detail is critical for budgeting and internal records. For a deeper dive, explore our guide on IT asset management best practices.
Building Your Inventory Checklist
A simple spreadsheet is the most effective tool for this task. This document becomes the single source of truth for vendor engagement, internal auditing, and compliance verification.
Ensure your inventory captures the following key data points for each asset:
- Asset Type: (e.g., Laptop, Server, Monitor)
- Manufacturer and Model: (e.g., Dell Latitude 7400, Cisco Catalyst 9300)
- Serial Number: Non-negotiable for tracking and chain-of-custody reporting.
- Internal Asset Tag: Include if your company uses an internal tagging system.
- Physical Location: (e.g., Storage Closet B, Data Center Rack 12)
- Condition: (e.g., Functional, Minor Damage, Non-functional)
- Data-Bearing: A simple "Yes" or "No" to flag items requiring certified data destruction.
With this detailed checklist, you are fully prepared to request accurate quotes and ensure every device is accounted for throughout the disposition process.
How to Select a Certified Recycling Vendor in Atlanta
Choosing the right partner for your IT Asset Disposition is the most critical decision in this process. A search for "electronic recycling Atlanta" yields numerous options, but they are not created equal. The distinction between a certified ITAD partner and a basic scrap hauler can be the difference between full compliance and a multi-million-dollar data breach.
You are not merely finding a service to remove old equipment. You are entrusting a vendor with your company's sensitive data and its reputation. This requires a level of due diligence that protects your organization long after the assets have left your facility.
The Importance of R2v3 and e-Stewards Certifications
When vetting vendors, the primary qualifying criteria should be their certifications. These are not merely marketing logos; they represent proof of rigorous, third-party audits that validate a recycler's processes for data security, environmental safety, and operational accountability.
- R2v3 (Sustainable Electronics Reuse & Recycling): This is the leading global standard for the ITAD industry. It ensures a vendor adheres to strict best practices for data sanitization, worker safety, environmental protection, and downstream material tracking. An R2v3-certified partner has been audited on their entire operational workflow.
- e-Stewards: This standard is renowned for its stringent environmental protocols. It enforces a zero-tolerance policy against exporting hazardous e-waste to developing countries, guaranteeing your materials are processed responsibly.
Selecting a vendor with one or both of these certifications provides an immediate baseline of trust and professionalism. It confirms they have invested in the necessary infrastructure and procedures to manage your assets to the highest industry standards. For any business serious about electronic recycling in Atlanta, GA, this is the essential first filter.
Questions to Ask Every Potential Vendor
With a shortlist of certified vendors, it's time for deeper vetting. A true professional will welcome detailed questions and provide clear, documented answers. Vague responses should be considered a significant red flag.
Key questions to ask include:
- What are your specific data destruction methods? Do you offer on-site and off-site physical shredding? Do you provide DoD 5220.22-M 3-pass data wiping for remarketable assets?
- Can you provide a complete, serialized chain-of-custody report? This is non-negotiable. The report must track every asset by serial number from your facility to its final disposition—be it resale, reuse, or recycling.
- What does your insurance coverage include? Request proof of liability insurance that specifically covers data breaches. This is your financial backstop in the unlikely event of a security incident while assets are in their care.
- Do you handle on-site logistics and de-installation? A true ITAD partner offers more than dock pickup. Inquire about their capabilities for de-installing servers from racks, secure packing, and palletizing to minimize the burden on your IT team.
- How do you determine and share asset resale value? If you have remarketable equipment, understand their process. A transparent partner will have a clear system for assessing value and providing revenue sharing.
Using an RFP checklist can be invaluable when formally evaluating e-waste partners. For more detail on what differentiates a basic pickup from a strategic partnership, our guide on choosing a professional electronic waste recycling company offers further insight.
Your data liability doesn't end when the truck leaves your dock; it ends when you have a Certificate of Destruction from a certified partner.
This single document is your ultimate proof of compliance. It certifies that the data on specified devices has been permanently destroyed according to industry standards. Without it, you lack verifiable evidence for an audit, leaving your business exposed. Any reputable vendor provides this as a standard part of their service.
Understanding Your Data Destruction Options
With a detailed inventory of your IT assets, the next critical decision involves the secure destruction of the sensitive data they contain. For any Atlanta organization, this is where your risk management strategy is truly tested. Simply deleting files is insufficient; you need a verifiable and permanent method to eradicate that data.
The choice comes down to two proven methodologies: software-based data wiping and physical destruction. The optimal approach depends on the asset's age, condition, potential resale value, and the sensitivity of the data it holds.
Software-Based Data Wiping for Asset Remarketing
Software wiping is a process where specialized programs overwrite every sector of a hard drive with random data, rendering the original information completely unrecoverable. This method follows stringent standards, such as the DoD 5220.22-M 3-pass wipe, to ensure data sanitization.
The primary advantage is that the hard drive and the device remain fully functional. This makes it the ideal solution for newer, high-value equipment with remaining operational life, such as:
- Laptops and desktops that are only a few years old
- Enterprise-grade servers suitable for the secondary market
- High-end networking gear with significant resale value
By choosing data wiping, you preserve the asset's value. This allows your ITAD partner to refurbish and resell the equipment, generating a financial return that can significantly offset or even exceed the cost of your entire disposition project.
Physical Shredding for Absolute Security
In some cases, the objective is not value recovery but absolute, indisputable proof that data has been eliminated. Physical shredding accomplishes this by using powerful, industrial machinery to grind hard drives, solid-state drives, and other storage media into small, irrecoverable fragments of metal and plastic.
This is the preferred method for:
- Older, obsolete, or non-functional hard drives with no resale value.
- Drives containing highly sensitive data—such as trade secrets, patient records, or financial data—where zero risk is the only acceptable tolerance.
- Corporate policies that strictly mandate physical destruction for all data-bearing assets.
The primary benefit of shredding is the complete peace of mind it provides. Witnessing a hard drive reduced to a pile of metal fragments leaves no doubt regarding the secure fate of your data.
For Atlanta companies subject to strict compliance frameworks like HIPAA, physical shredding offers a simple, verifiable end to data liability. To understand the operational specifics, you can learn more about professional hard drive destruction service and the differences between on-site and off-site processes.
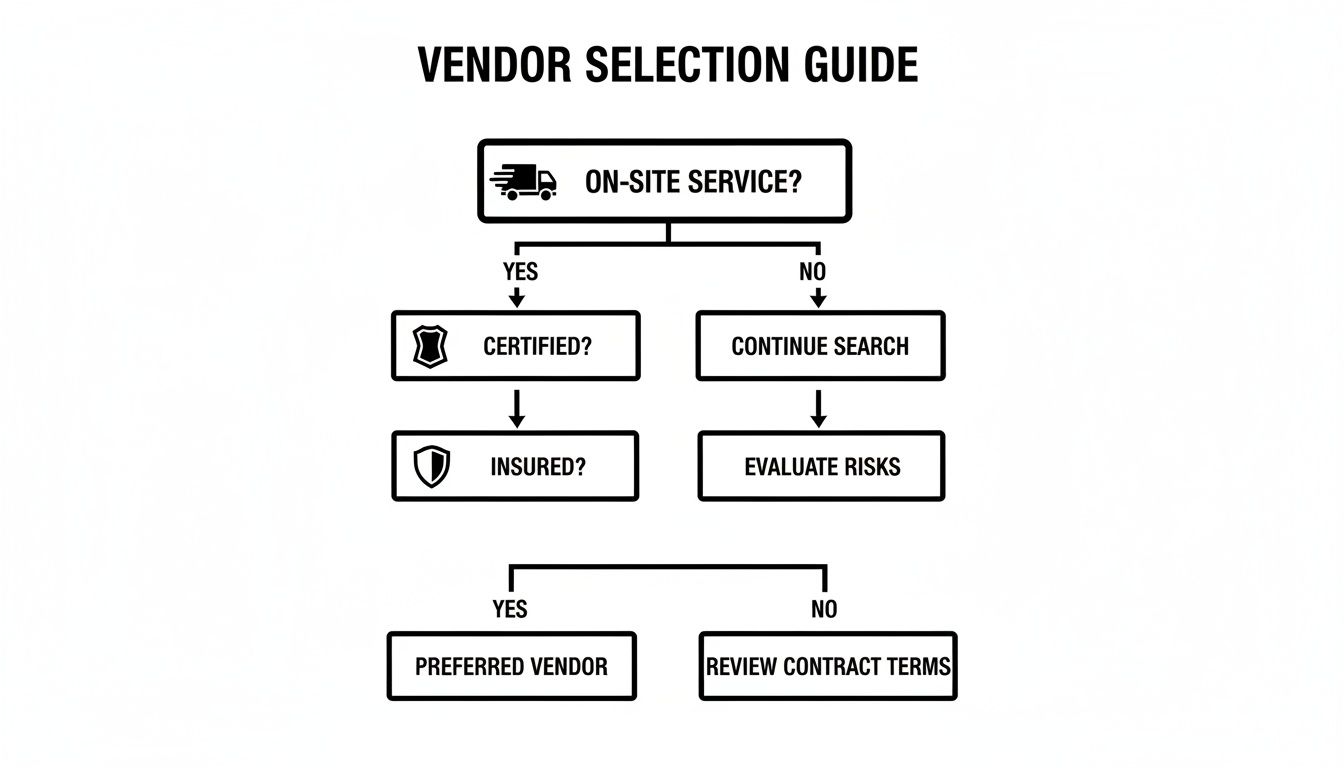
This flowchart provides a simple framework for selecting a vendor equipped to meet your specific data security requirements.
The key is to partner with a vendor offering both services. This allows them to tailor a solution that aligns with your specific asset portfolio and security policies, rather than imposing a one-size-fits-all approach.
Data Destruction Method Comparison for Atlanta Businesses
This table provides a straightforward comparison to help you decide on the appropriate data destruction method for different asset types, outlining the primary benefits and drawbacks of each.
| Method | Best For | Pros | Cons | Typical Cost |
|---|---|---|---|---|
| Software-Based Wiping | Newer, functional devices (laptops, servers) with resale value. | Preserves asset value, enables remarketing, generates financial return, eco-friendly. | Takes more time than shredding; not suitable for damaged or non-functional drives. | Often offset or covered by resale value of the asset. |
| Physical Shredding | Old, obsolete, or non-functional devices; assets with highly sensitive data. | Fast, provides absolute and visual proof of destruction, ideal for compliance. | Destroys any potential resale value of the asset and its components. | Per-drive or per-pound fee, varies by volume and location. |
Ultimately, a flexible ITAD partner in Atlanta will collaborate with you to develop a blended strategy. This approach maximizes your return on valuable assets while guaranteeing the absolute destruction of data on obsolete ones. They should analyze your inventory and recommend the most secure and cost-effective plan, whether it involves specialized software or powerful various shredding equipment to execute the job correctly.
Wrapping It Up: Logistics, Reporting, and Peace of Mind
While the physical removal of old IT assets from your office is a milestone, the project is not complete. For any Atlanta business that prioritizes compliance and risk management, the engagement concludes only upon receipt of final documentation. This final phase—encompassing logistics, chain-of-custody, and reporting—is what elevates a simple pickup to a secure, audit-proof disposition process.
This paperwork serves as your definitive proof of due diligence. Without it, you create a significant gap in your compliance records, exposing your organization to future liabilities.
Nailing the On-Site Pickup and Logistics
A seamless handover is the hallmark of a professional ITAD partner. They arrive with a detailed operational plan, not just a truck. Their team should be equipped to handle all logistical requirements, from carefully de-installing servers in a live data center to securely packing and palletizing assets directly at your facility.
This organized approach minimizes disruption to your daily operations and ensures every asset is accounted for from the outset. The process should be efficient and secure, culminating in a detailed manifest created before any equipment leaves your premises. You can see how a well-planned service operates by exploring options for a secure electronic recycling pickup.
The Unbreakable Chain-of-Custody
Chain-of-custody is the documented, unbroken trail that follows every one of your assets from your Atlanta facility to its final disposition. It is the core of a secure ITAD process, not an abstract promise.
Each device is assigned a serialized record, which is scanned and logged at every critical transfer point:
- Upon pickup from your location.
- Upon arrival at the secure processing facility.
- Immediately following data destruction.
- At its final destination, whether refurbishment, resale, or recycling.
This meticulous tracking eliminates the risk of an asset "disappearing" and provides a transparent, verifiable history for every piece of equipment. For any organization with a serious data security posture, this is a non-negotiable requirement.
This detailed documentation is your shield in an audit. When a regulator asks for proof of secure disposal, a comprehensive chain-of-custody report and a Certificate of Destruction are your definitive answers.
Your Final Compliance Reports: The Last Piece of the Puzzle
Upon completion of processing, your vendor will deliver two critical documents. These represent the final, official record of your e-recycling project and should be archived with your other compliance documentation.
Certificate of Destruction (CoD)
This is your official proof of data sanitization. It certifies that the data on specific hard drives and media has been permanently destroyed according to industry standards. The certificate lists the device serial numbers, the destruction method used (e.g., shredding, DoD 3-pass wipe), and the date of completion.
Serialized Asset Report
This comprehensive report details the final outcome for every asset in the project. It itemizes what was recycled, what was resold (including any revenue share), and confirms data destruction across the board. It is an invaluable tool for internal asset management and external audits.
These documents are also increasingly important for corporate responsibility initiatives. Many Atlanta businesses leverage these reports in their Environmental, Social, and Governance (ESG) records to demonstrate a tangible commitment to sustainability. While corporate efforts are vital, they exist within a broader context; an independent audit noted Atlanta's household recycling rate at about 23%, below federal benchmarks. The full analysis on how Atlanta's recycling rates are measured and can be improved provides valuable perspective on the region's overall goals.
Answering Your Questions About Business E-Waste Recycling in Atlanta
When it comes to managing end-of-life IT assets, Atlanta businesses have practical questions regarding cost, logistics, and data security. Below are straightforward answers to the most common inquiries we receive.
How Much Does Business Electronic Recycling Cost in Atlanta?
The cost is variable, as it depends on the composition of your assets and logistical requirements. For electronic recycling in Atlanta, GA, there is no flat rate. In many cases, an ITAD project can actually generate a net positive financial return for your company.
Key factors that influence a final quote include:
- Asset Remarketing Value: If your inventory includes newer, functional equipment like recent-model laptops or enterprise servers, these can be refurbished and resold. The revenue generated from these sales can often offset or even exceed the recycling costs for obsolete items.
- Logistical Complexity: A project requiring on-site de-installation of servers from a data center will have different labor costs compared to a simple, palletized pickup from a loading dock.
- Data Destruction Method: Physical shredding typically incurs a per-drive or per-pound fee. In contrast, the cost of software-based data wiping for remarketable assets is often absorbed into the overall project value.
The only way to determine a firm cost is to request a custom quote based on your detailed asset inventory.
What Types of Electronics Do You Take?
A professional ITAD partner manages virtually every type of electronic equipment found in a corporate environment, providing a single-source solution for your business.
We handle a comprehensive range of assets, including:
- IT Infrastructure: Servers, server racks, data center equipment, and UPS battery backups.
- Networking Gear: Switches, routers, firewalls, modems, and access points.
- Office Equipment: Desktops, laptops, docking stations, printers, copiers, and scanners.
- Communication Devices: VoIP phones, business cell phones, and tablets.
- Peripherals: Monitors (CRT and LCD), keyboards, mice, and all associated cables.
If a device was used in your business and plugs into a wall or runs on a battery, a certified recycler can almost certainly manage its secure and responsible disposition.
Is My Company’s Data Really Secure During This Process?
Absolutely. For a professional ITAD vendor, data security is the foundational principle of the service. We provide security not as a promise, but through audited, documented processes that protect your data at every stage.
From the moment our team arrives on-site, a strict chain-of-custody protocol is initiated. Every data-bearing asset is tracked by serial number from pickup at your Atlanta office to its final, certified destruction, ensuring there are no gaps in security.
We utilize industry-standard data destruction methods to ensure complete data eradication. This includes DoD 5220.22-M 3-pass data wiping for remarketable devices and physical shredding for obsolete, damaged, or highly sensitive drives. Upon completion, you receive a Certificate of Destruction, providing official, auditable proof that your data has been securely and permanently destroyed.
Can We Just Donate Our Old Computers?
Donating functional computer equipment to Atlanta-area schools and non-profits is a commendable community initiative. However, for a business, this path requires extreme caution from a data security perspective.
Before donating any device, your organization is 100% responsible for ensuring that all sensitive corporate and customer data has been professionally sanitized and verified. Simply deleting files is insufficient. If a data breach is traced back to one of your donated assets, the liability rests solely with your company.
The safest approach is to engage an ITAD vendor first. We can perform certified data wiping on the equipment slated for donation. Once the data is verifiably destroyed and documented, you can proceed with the donation, confident that you have fulfilled your security obligations while still supporting the community. It is the optimal way to protect your business and contribute charitably.
Ready to implement a secure and compliant e-waste strategy for your Atlanta business? Contact Atlanta Computer Recycling today for a no-obligation quote and see how our certified ITAD services can protect your data and simplify your asset retirement process. Visit us at https://atlantacomputerrecycling.com to get started.