Data Destruction Certification: A Business’s Guide for 2026

You’re probably in one of these situations right now. An office refresh is underway, racks are being emptied in a data center, or a department finally approved replacement laptops after years of delay. The new equipment is easy to focus on. The retired equipment is where the primary risk lies.
Old drives, servers, and network gear don’t stop being sensitive when they leave production. They become harder to track, easier to mishandle, and surprisingly difficult to defend in an audit if your disposal process is loose. That’s why data destruction certification matters. It turns disposal from a vague operational task into documented risk control.
Why Your Old Hard Drives Are a Modern Business Risk
Most IT teams know that deleting files isn’t enough. The practical problem is that many disposal workflows still act as if it is. A closet full of retired laptops, a pallet of failed drives, or a rushed move-out after an office closure can create a chain-of-custody gap before anyone notices.
A retired asset is still a live liability until it’s sanitized or destroyed in a way you can prove. That includes failed hard drives pulled from servers, surplus desktops from a branch shutdown, and storage arrays sent out during a decommissioning project. If your team can’t show what happened to each device, the business is exposed.
What actually goes wrong
In practice, the failures are usually operational, not technical.
- Assets sit too long because pickup is delayed, internal approvals stall, or no one owns end-of-life inventory.
- Inventory is incomplete when serial numbers aren’t captured before transport.
- Vendors provide weak paperwork that says a batch was destroyed without identifying the actual devices.
- Reusable media gets mixed with scrap and no one can prove which sanitization method was used.
That’s why a formal process for old hard drive disposal matters. It closes the gap between “we removed it from service” and “we can defend exactly how it was handled.”
Why this is a business issue, not just an IT task
A drive doesn’t have to be online to cause a breach problem. It just has to contain recoverable data and leave your control without defensible documentation.
Practical rule: If you can’t tie a specific asset to a specific destruction or sanitization record, assume you can’t prove compliance.
Many organizations often get stuck. They think of destruction as the last step in recycling. Compliance teams see it differently. They see disposal as the final control in the lifecycle of regulated or sensitive information.
What Is a Certificate of Data Destruction
A vendor loads 200 retired laptops onto a truck. Three months later, audit asks for proof that serial number ABC123 was sanitized under an accepted method, on a specific date, by an identified operator. A pickup receipt does not answer that question. A Certificate of Data Destruction does.
A Certificate of Data Destruction is the record that ties a specific asset to a specific destruction or sanitization event. Its job is not administrative. Its job is evidence. If legal, compliance, cyber insurance, or an external auditor asks how your organization handled end-of-life media, this document should let you prove the answer without reconstructing the event from emails, truck logs, and vendor assurances.
That matters because disposal failures create direct business liability. IBM’s Cost of a Data Breach Report found average breach costs reached $4.88 million per incident. A certificate will not prevent every breach, but it does prove your organization applied a documented control at the point where data left service, which is often the exact point auditors and regulators examine after an incident.
What a real certificate needs to show
A usable certificate should stand on its own. If the document forces your team to pull a separate spreadsheet to identify assets, or call the vendor to confirm the destruction method, it is weak evidence.
| Element | Why it matters |
|---|---|
| Asset serial numbers or unique identifiers | Proves which exact devices were handled |
| Date and timestamp | Establishes when the event occurred |
| Destruction or sanitization method | Shows whether the media was wiped, shredded, degaussed, or otherwise processed |
| Service location | Confirms where custody changed or destruction occurred |
| Operator, technician, or witness ID | Identifies who performed or verified the work |
| Standard or policy reference | Connects the action to NIST 800-88, ISO 27001, or internal control requirements |
The standards reference is especially important. It shows whether the vendor followed a recognized sanitization framework or used vague language such as “disposed” or “destroyed.” If your security program maps to an ISMS, this practical guide to ISO 27001 is useful context for understanding how destruction records support broader control evidence.
What the certificate does for liability
A strong certificate supports due diligence in a way a pickup ticket never will. It documents what happened, who handled it, and which assets were affected. That is the difference between “the vendor collected our drives” and “we can prove these drives were destroyed under a documented process.”
There is also a trade-off to manage. The more reusable equipment you process, the more important sanitization records become, because remarketing requires proof that data was cleared without damaging asset value. For media that cannot be reused safely, physical destruction records carry more weight. The certificate should reflect that operational decision instead of masking it behind one generic statement for the whole batch.
Use the document as a vetting tool, not just a file to archive. Before you sign with any ITAD or destruction provider, ask to review a real certificate of destruction form example. If the sample cannot support an audit at the device level, the service probably cannot either.
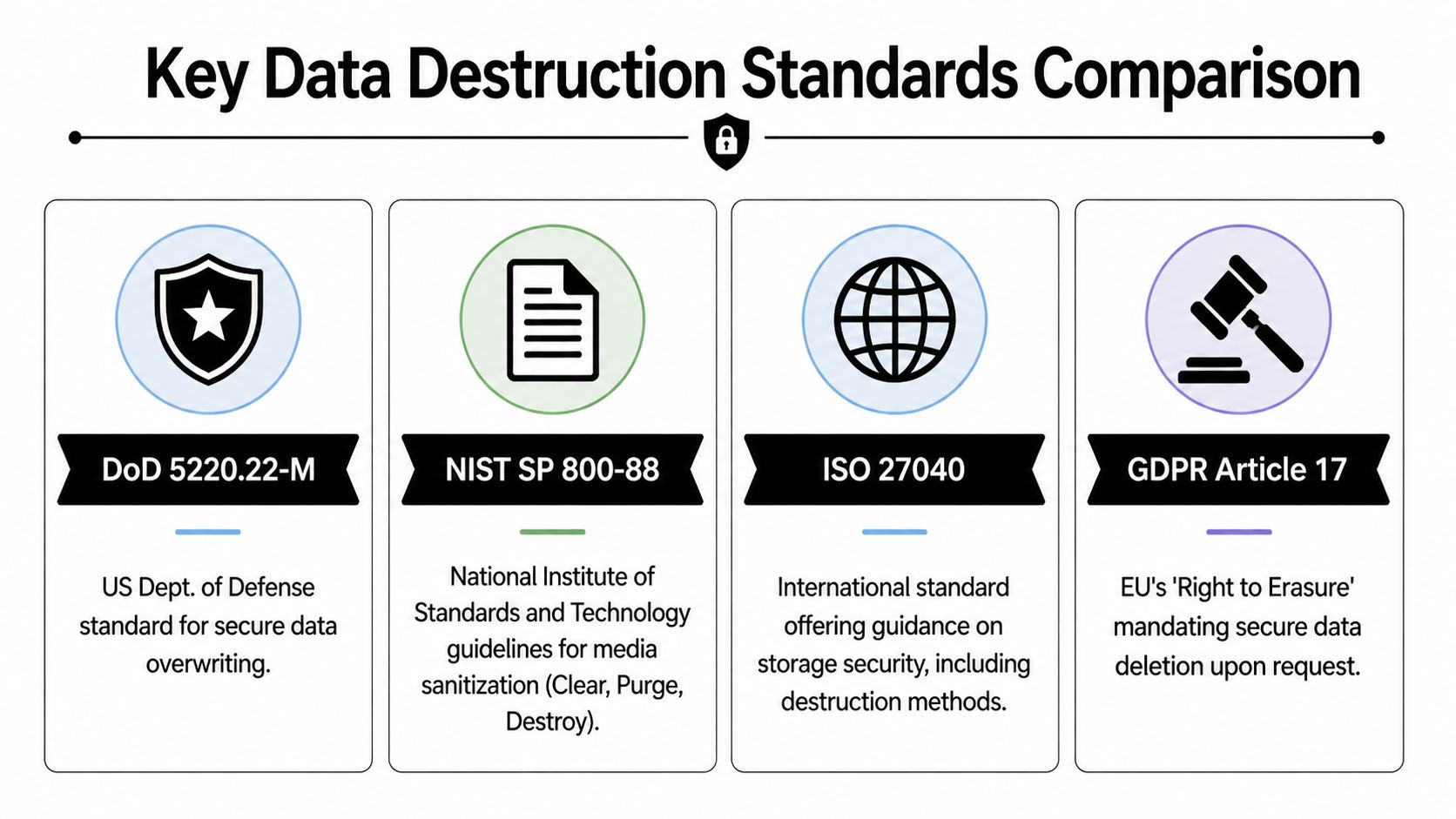
Decoding Key Data Destruction Standards
Most confusion in this area comes from treating every standard as if it does the same job. It doesn’t. Some standards define how media should be sanitized. Others validate who is performing the work and whether their operation is trustworthy. A few sit adjacent to destruction and matter because they support broader governance and environmental controls.
NIST 800-88 is the method benchmark
If you only remember one technical standard, make it NIST SP 800-88. As explained in this overview of NIST 800-88 and data destruction, NIST 800-88 was published in 2006 and classifies media sanitization into Clear, Purge, and Destroy, replacing DoD 5220.22-M as the benchmark for U.S. government contractors.
Those categories are practical:
- Clear fits lower-risk reuse cases where logical techniques remove data from user-addressable locations.
- Purge applies when you need stronger sanitization that makes recovery infeasible with advanced techniques.
- Destroy is the end state for media that shouldn’t be reused and must be physically rendered unreadable.
For IT managers, NIST is useful because it links the method to the media and the risk level. It’s not just “wipe everything” or “shred everything.” It’s a decision framework.
DoD 5220.22-M still shows up, but it’s historical
Many vendors still mention DoD 5220.22-M because buyers recognize it. That doesn’t make it the current benchmark. Its value today is mostly practical and historical. If a provider says they perform a DoD 5220.22-M 3-pass wipe, that tells you something about the overwrite process used for reusable media. It does not replace the broader, more current guidance of NIST.
That’s an important distinction in procurement language. Buyers often ask for “DoD wiping” when what they really need is a documented sanitization process aligned to present-day compliance expectations.
NAID AAA validates the vendor, not just the method
NIST tells you how data should be sanitized. NAID AAA tells you whether the vendor’s operation is disciplined enough to trust with sensitive assets.
NAID AAA focuses on the vendor’s security controls, chain of custody, audits, employee screening, destruction procedures, and documentation practices. It’s the vendor assurance layer. That makes it especially useful when you’re outsourcing destruction rather than handling every step internally.
How the standards fit together
Here’s the quickest way to separate them:
| Standard or framework | Primary role | What it answers | Best use |
|---|---|---|---|
| NIST 800-88 | Technical sanitization guidance | How should this media be sanitized? | Method selection and policy design |
| DoD 5220.22-M | Older overwrite approach | What legacy wiping method was used? | Legacy processes and reusable media workflows |
| NAID AAA | Vendor certification | Can this provider be trusted operationally? | Third-party vendor due diligence |
| ISO 27001 | Information security management | Does this process fit the organization’s control framework? | Governance and audit alignment |
| R2 or similar recycling controls | Downstream environmental responsibility | What happens after destruction or recovery? | Sustainability and responsible disposition |
If you’re mapping destruction controls into a wider security program, this practical guide to ISO 27001 is useful because it connects operational controls like asset handling, evidence retention, and supplier management back to the ISMS level.
The Business Impact of Data Destruction Compliance
A drive leaves your office during a relocation. Six months later, audit asks for proof of what was on it, who handled it, and how it was destroyed. If your file only shows a pickup receipt or a vendor invoice, the problem is no longer disposal. It is evidence.
That is why data destruction compliance matters at the business level. The risk is not limited to a lost asset. It extends to regulatory exposure, customer notifications, legal costs, failed audits, and the internal time required to reconstruct what should have been documented the first time.
Where companies get exposed
The failures I see are usually operational. Media is retired during a tight project window, equipment is stacked for pickup, and nobody captures enough detail to defend the process later.
Common exposure points include:
- Healthcare disposals where failed drives from imaging systems or nurse stations leave without serial-level tracking or destruction records
- Mergers, closures, and office moves where cleanup happens fast and retired hardware gets treated like surplus property
- Data center decommissions where volume is high, multiple parties are involved, and chain-of-custody gaps appear between rack removal and final destruction
- Outsourced recycling programs where the vendor can collect equipment but cannot produce documentation that satisfies legal, compliance, or customer review
Data destruction also belongs in third-party risk review. A recycler handling storage media creates the same kind of exposure as any other vendor with access to sensitive systems or information. These supply chain risk management strategies are useful for framing destruction providers inside the same vendor oversight process.
Why certification changes the outcome
Certification does not eliminate risk by itself. It gives your team a defensible process and records that stand up when someone asks hard questions later.
That matters in three ways.
First, it reduces ambiguity. Instead of arguing about whether a device was "probably destroyed," you have dated documentation tied to specific assets, methods, and custody events.
Second, it shortens audit response time. Compliance teams do not want a story. They want evidence they can file, cross-reference, and produce on demand.
Third, it shifts vendor oversight from trust to verification. If a provider cannot maintain documented controls around pickup, handling, destruction, and proof, the low invoice price stops looking attractive very quickly.
The cheapest disposal option often becomes the most expensive one when the records fail under audit.
A good destruction program protects more than data. It protects the organization’s ability to prove that retired media was handled correctly, by the right party, under controlled conditions, with records worth keeping.
Your Vendor Verification Checklist
Many IT teams quickly improve their vendor evaluation processes. They stop asking “Do you destroy drives?” and start asking questions that reveal whether the vendor can hold up under audit.
A strong starting point is NAID AAA. According to this review of NAID AAA versus other destruction certifications, NAID AAA requires scheduled inspections, unannounced audits by trained accredited security professionals, and three-level background screenings so employees with relevant access don’t have criminal records related to information theft.
Questions worth asking before pickup day
Use these in procurement, not after the truck arrives.
Can you provide current certification documentation?
Don’t settle for a logo on a website. Ask for the active certification scope and current supporting documents.Which NIST 800-88 methods do you apply to which media types?
HDDs, SSDs, tapes, and failed drives don’t all fit the same workflow. A serious vendor should answer this clearly.What does your chain of custody look like from pickup to final disposition?
Ask for the handoff points, transport controls, and how devices are reconciled against pickup inventory.What employee screening controls are in place?
This matters more than many buyers realize. Internal access is part of the risk model.What will the final documentation package include?
You want itemized certificates of destruction, chain-of-custody records, current certification evidence, and proof of insurance where relevant.
What a strong answer sounds like
The best vendors speak in specifics. They’ll tell you whether work is done onsite or offsite, whether serial numbers are captured at pickup, how failed media is isolated, and what the certificate will list.
A weak vendor stays vague. They talk about “secure recycling” but avoid naming the method, the standard, or the documentation.
Here’s a quick screen:
| Ask this | Strong signal | Warning sign |
|---|---|---|
| Show your certification | Current document and scope provided | “It’s on our website” |
| Describe media handling | Media-specific sanitization or destruction workflow | One method for everything |
| Explain chain of custody | Pickup, transport, intake, destruction, reporting are all documented | Gaps between pickup and destruction |
| Show sample reporting | Itemized serial-level output | Batch-only summary |
| Discuss insurance and audits | Clear, direct answer | Evasive or partial response |
If your team is building a shortlist, this guide on how to choose an electronic waste recycling company for your business pairs well with a compliance checklist because it pushes the conversation beyond simple hauling capability.
Ask vendors for the paperwork before you ask for pricing. It saves time and filters out the wrong partners fast.
Building an Audit-Proof Chain of Custody
A certificate at the end is important. It isn’t enough on its own. You need the full trail from the moment an asset leaves the office or rack to the moment it’s sanitized or destroyed.
Start with itemized pickup records
The first control is the pickup inventory. Every device that matters should be listed in a way that can be matched later. Serial numbers are the anchor. If a device can’t be tied back to an inventory line, your audit trail starts with a hole in it.
That inventory should follow the asset through transport and intake. If the load is sealed, logged, and reconciled at each handoff, you can show continuity. If not, the final certificate is carrying too much weight by itself.
The final certificate should be device-level evidence
The strongest documentation package includes the pickup inventory, transport or handoff records, and the certificate of destruction itself. The certificate should show serial number, date, time, location, method used, standards reference, and authorized signoff.
A generic batch report usually fails when an auditor asks a simple question: “What happened to this specific drive?”
For organizations managing regulated records in collaboration platforms and file systems, this SharePoint GDPR compliance guide is a useful parallel. It shows the same principle at work. Accountability depends on proving actions, not just claiming policy exists.
How to spot weak documentation
Watch for these red flags:
- No serial-level detail
- No method listed
- No destruction location
- No standards reference
- No named or authorized operator
- No connection to earlier chain-of-custody records
If you want a practical benchmark for what acceptable reporting looks like, review a sample certificate of destruction. The main thing to look for is whether the document stands on its own in an audit packet.
How Atlanta Computer Recycling Delivers Certified Destruction
For Atlanta-area organizations that need a local ITAD option, Atlanta Computer Recycling is one example of a provider workflow built around the controls discussed above. The company handles business-to-business collection, de-installation, packing, pickup, and downstream disposition for computers, laptops, servers, network gear, and data center equipment.
From a process standpoint, the relevant detail is straightforward. Reusable media can be wiped using the DoD 5220.22-M 3-pass method, while obsolete or non-functional media can be physically shredded. That gives IT managers a practical split between reuse-friendly sanitization and irreversible destruction, depending on the condition and risk profile of the device.
The documentation side is what matters most in a compliance setting. The service includes certificates of destruction with serial-number tracking, along with chain-of-custody support for organizations that need audit-ready records. That fits the needs of hospitals, schools, government offices, and enterprises that can’t rely on generic recycling receipts.
The operational advantage is less about branding and more about execution. If a vendor can collect assets securely, minimize disruption during pickup, apply the right sanitization or destruction method, and return itemized documentation, the program works the way it should.
Data Destruction Certification FAQs
Is a DoD 5220.22-M wipe still sufficient for compliance in 2026
It can still be part of a usable process for certain reusable media, but it shouldn’t be treated as the primary benchmark by itself. NIST 800-88 is the better reference point for policy because it maps sanitization choices to media type and risk. In practice, the right question isn’t “Do you do DoD wiping?” It’s “What method do you use for this device, and how do you document that choice?”
How long should we retain Certificates of Destruction
Retention should follow your regulatory, legal, and internal records schedule. Keep the certificate with the supporting chain-of-custody records, not as a standalone PDF in someone’s inbox. If your business operates in a heavily regulated environment, align destruction records with the same discipline you use for other audit evidence.
What are the trade-offs between onsite and offsite destruction
Onsite destruction gives direct visibility and can reduce anxiety around transport. Offsite destruction can be operationally efficient when the vendor’s facility controls are strong and the chain of custody is tight. The wrong choice isn’t always offsite. The wrong choice is any model that leaves documentation gaps.
How do we audit a vendor beyond the certificate
Ask for more than the final document. Review chain-of-custody records, current certification documentation, and evidence of how exceptions are handled. For projects involving data center decommissioning, a projection cited in this onsite data destruction discussion notes 15% U.S. hyperscale closures in 2025, and it highlights a documentation gap around auditing compliance beyond certificates. The same source also notes that layered defenses such as degaussing plus shredding reduced recovery risk to below 0.01% in forensic tests, while only 35% of providers offered multi-angle video in recent i-SIGMA surveys. That’s a good reminder that the final certificate is important, but not the whole proof set.
If your team needs a documented disposal process for servers, laptops, drives, or data center hardware, Atlanta Computer Recycling offers business ITAD services in the Atlanta metro area with wiping, physical destruction, pickup logistics, and certificate-based documentation that supports audit and compliance review.