Corporate e-waste recycling: Secure, compliant programs for your business

When your company's electronics reach their end-of-life, the next step is more than a simple disposal task—it's a critical business process that directly impacts your data security, regulatory compliance, and brand reputation.
Properly managing retired IT assets means implementing a secure, compliant, and environmentally sound system for their disposition.
Why Smart E-Waste Recycling Is a Business Imperative
Handling outdated electronics is no longer just about "getting rid of old gear." It has become a core component of modern corporate risk management.
For businesses in regulated industries like healthcare, finance, or legal services, a single improperly discarded hard drive can become a million-dollar liability, triggering staggering fines and a public relations disaster. This is why a structured IT Asset Disposition (ITAD) program has moved from a backroom IT task to a boardroom-level strategic concern. It is no longer an operational chore; it's a strategic necessity.
Without a formal policy, you're leaving your company exposed to significant vulnerabilities. A well-defined corporate e-waste recycling plan is your first and best line of defense.
Protecting Your Bottom Line and Reputation
The consequences of mishandling electronic assets extend far beyond environmental concerns. For any business, the two most immediate threats are data breaches and non-compliance penalties.
Consider a common scenario in Atlanta's thriving healthcare sector. A local hospital system retires dozens of older computers but skips certified data destruction to reduce costs. If protected health information (PHI) is later recovered from one of those drives, that organization faces severe HIPAA violations, mandatory public disclosure, and a catastrophic loss of patient trust.
A formal recycling program ensures every single device is tracked, sanitized, and properly processed. It’s a direct investment in protecting your company’s finances and the trust you’ve built with your customers.
The real cost of ignoring e-waste isn't just in potential fines; it's in the erosion of customer confidence. A single data breach can undo years of brand-building and customer loyalty, making proactive ITAD a powerful investment in business continuity.
The Growing Challenge of E-Waste
The volume of electronic waste is expanding at an alarming rate, driven by rapid technology refresh cycles. This isn't just an environmental talking point; it's a massive global challenge, and businesses are major contributors.
The Global E-waste Monitor 2024 reported a staggering 62 million tonnes of e-waste was generated in 2022. The truly shocking part? Only 22.3% of it was properly collected and recycled. This means an incredible amount of material—containing both valuable recoverable resources and hazardous substances—is being improperly managed.
This ever-growing mountain of discarded technology makes it clear why partnering with a professional recycler is non-negotiable for any company serious about data governance and corporate responsibility.
Key Business Drivers for a Formal Policy
Implementing a formal e-waste policy is about shifting from a reactive, ad-hoc process to a proactive, managed one. It transforms a potential liability into a predictable and secure operational workflow.
Here are the primary business drivers for establishing a formal program:
- Data Security: The absolute requirement to ensure all proprietary company and sensitive customer data on retired devices is permanently and verifiably destroyed.
- Regulatory Compliance: Maintaining adherence to laws like HIPAA, FACTA, and GLBA to avoid crippling fines and legal action.
- Brand Protection: Demonstrating corporate responsibility and avoiding the negative publicity that accompanies a data breach or environmental incident.
- Cost Management: A structured process eliminates the hidden costs of storing obsolete equipment or dealing with last-minute, non-compliant disposal emergencies.
Understanding the environmental impact of electronic waste often reinforces the urgency and importance of a responsible disposition program.
Building Your Corporate E-Waste Policy Framework
Without a formal policy, disposing of old company electronics is often a chaotic fire drill for the IT department. A well-defined corporate e-waste policy changes that. It transforms a potential liability into a predictable, secure, and strategic part of your operations.
Think of it as your official playbook. It provides a clear blueprint for every step of a device's end-of-life journey, from the moment it's taken offline to its final, documented disposition. This isn't just about environmental stewardship—it's about protecting your data, ensuring compliance, and establishing clear accountability across your organization.
Defining The Scope: What Exactly Are We Getting Rid Of?
First, you must clearly define what your policy covers. You need to identify every type of electronic asset your company utilizes, because anything not on the list can easily fall through the cracks. Specificity here eliminates ambiguity and future headaches.
Your scope should explicitly include major asset categories:
- End-User Devices: Laptops, desktops, monitors, tablets, and all company-issued smartphones.
- Data Center & Infrastructure Hardware: Servers, storage arrays (SANs/NAS), and networking equipment like switches, firewalls, and routers.
- Office Equipment: Printers, multifunction copiers, VoIP phones, and audiovisual hardware.
- Removable Media: Don't forget the small but critical items, including external hard drives, legacy backup tapes, and USB flash drives.
By creating a comprehensive list, you’ve established exactly what falls under the policy, simplifying every future IT retirement decision for your team.
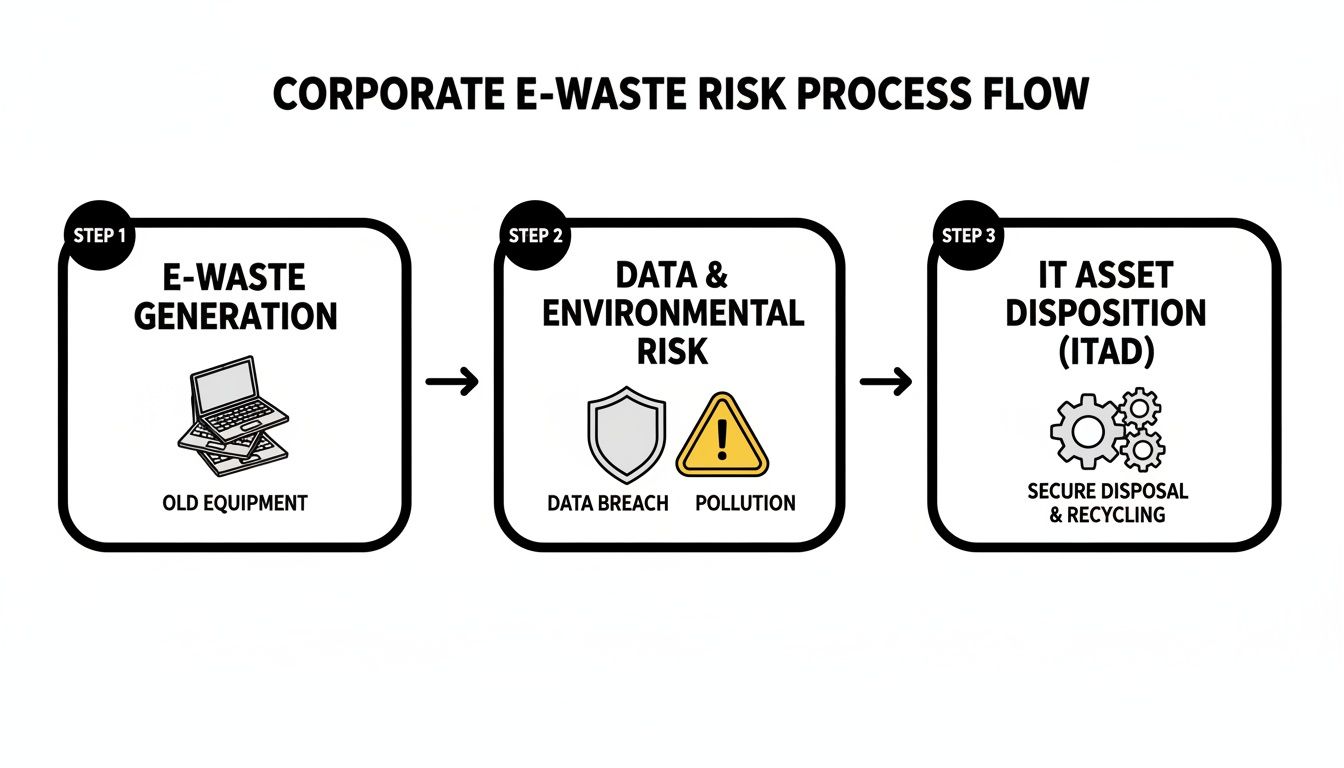
The flowchart below illustrates how unmanaged e-waste can quickly become a major business risk—and how a formal ITAD program provides critical controls.
As you can see, what starts as a pile of old tech can become a source of data breaches and compliance fines. A certified ITAD partner is your shield against that.
To help you get started, we've created a checklist of the essential components your e-waste policy must include. This is a road map to building a framework that truly protects your organization.
Essential Components of a Corporate E-Waste Policy
| Policy Component | Key Considerations | Example Action Item |
|---|---|---|
| Scope & Applicability | Which devices, departments, and locations are covered? | List all asset types (laptops, servers, etc.) and specify the policy applies to all US-based offices. |
| Roles & Responsibilities | Who owns the process? Who handles logistics? Who signs off? | Designate the IT Director as the Program Owner, responsible for vendor management and final reporting. |
| Data Destruction Standard | What is the minimum acceptable method for data sanitization? | Mandate NIST 800-88 compliant data erasure for all hard drives, with physical shredding for failed media. |
| Asset Inventory & Tracking | How will assets be tracked from desk to disposition? | Require all retiring assets to be logged in the asset management system with their final Certificate of Destruction number. |
| Vendor Requirements | What certifications must your recycling partner hold? | State that all vendors must possess active R2v3 or e-Stewards certification. |
| Reuse vs. Recycle Criteria | How do you decide if an asset can be remarketed or must be destroyed? | Define a guideline: "Assets less than 3 years old may be evaluated for reuse; all older assets will be recycled." |
| Reporting & Auditing | What documentation is required to prove compliance? | Require serialized Certificates of Data Destruction and Recycling for every pickup, to be reviewed quarterly. |
This table serves as a robust starting point. By addressing each of these areas, you ensure your policy is not just a document, but a functional tool that guides real-world actions and decisions.
Assigning Roles and Responsibilities
A policy is only effective when people are assigned to execute it. To give your framework operational teeth, you need to designate specific roles and responsibilities. This creates a clear chain of command and ensures accountability.
A typical breakdown of responsibilities includes:
- IT Department: The primary drivers of the process. They identify assets for retirement, manage inventory lists, and serve as the main point of contact for the recycling vendor.
- Facilities Management: Often handles the physical logistics—collecting packaged equipment, staging it in a secure area, and coordinating the scheduled pickup.
- Legal/Compliance Officer: This role is critical for governance. They review the policy to ensure it aligns with data privacy laws like HIPAA or GDPR and any relevant environmental regulations.
- Finance Department: Tracks the financial aspects of ITAD, including asset depreciation and any potential revenue generated from remarketing newer equipment.
When these roles are clearly defined, there’s no confusion. When a data center refresh or office-wide laptop upgrade occurs, everyone knows their part.
A strong e-waste policy is built on the principle of "verifiable security." It's not enough to simply hand over your old equipment; you must have a documented, auditable trail that proves every single data-bearing device was handled securely from your door to its final destruction.
Integrating Data Security Protocols
This is, without question, the most critical component of your entire policy. Your procedures for destroying data cannot be vague—they must be explicit, mandatory, and aligned with industry best practices.
Your policy needs to spell out exactly how data will be permanently wiped or destroyed. It should mandate a certified process, leaving no room for error or interpretation. You can explore various options that meet strict compliance standards by learning more about professional secure data destruction services. This is not an area to cut corners; the risk of a data breach is simply too high.
The key is to integrate these protocols directly into your existing IT workflows. Make certified data destruction a standard, required step in your employee offboarding checklist or your hardware refresh cycle. When security becomes a default action instead of an afterthought, you've built the foundation of a truly responsible and legally defensible e-waste program.
Mastering Secure Data Destruction and Compliance
When your company retires a server or laptop, you're not just disposing of hardware. The most valuable—and potentially dangerous—asset you're managing is the data stored on it. In any corporate e-waste program, mastering secure data destruction isn't just a best practice; it's a non-negotiable step to protect your business from catastrophic risk.
For businesses in Atlanta’s booming healthcare and financial sectors, the stakes are even higher. Regulations like the Health Insurance Portability and Accountability Act (HIPAA) don't just suggest data protection—they legally mandate it with severe penalties for non-compliance. A single improperly wiped hard drive from a clinic's old workstation could expose sensitive patient records, leading to crippling fines and irreversible damage to your reputation.
This is why certified data destruction must be the centerpiece of your IT asset disposition (ITAD) strategy. It is the formal process of ensuring that stored information is completely and permanently unrecoverable, by any means.
Choosing Your Destruction Method Wisely
Not all data destruction methods are created equal, and the right choice depends entirely on the asset's end-of-life path. Your two primary options are software-based wiping and physical destruction.
Software-Based Data Wiping
This method uses specialized software to overwrite a hard drive's entire surface with random data, effectively erasing the original information. The process typically adheres to rigorous standards like the Department of Defense DoD 5220.22-M or, more commonly today, NIST 800-88.
- When to use it: This is the ideal choice for newer, functional equipment that you plan to resell or redeploy internally. Wiping preserves the hard drive's functionality, which is essential for maximizing the asset's potential resale value while ensuring complete data security.
- Real-world scenario: Your sales team is receiving a laptop upgrade. Their three-year-old machines still hold significant value on the secondary market. A certified partner can wipe the drives to NIST standards, allowing you to recoup a portion of your initial investment.
Physical Destruction (Shredding)
This method is exactly as it sounds. Hard drives, backup tapes, and other storage media are fed into an industrial shredder that grinds them into small, unrecognizable pieces. It is the most definitive form of data elimination.
- When to use it: Shredding is the required method for non-functional, damaged, or obsolete media. It's also the best practice for devices containing highly sensitive intellectual property or regulated data where there can be no margin for error.
- Real-world scenario: A data center is decommissioning a ten-year-old storage array. The drives have no resale value and contain years of business data. Physical shredding provides the most absolute, final, and foolproof form of data destruction.
The decision between wiping and shredding comes down to one question: Does this asset have remaining financial value? If yes, wipe to preserve that value. If no, or if the data is too sensitive to risk, shredding provides ultimate peace of mind.
The Power of Proof: The Certificate of Data Destruction
Handing your e-waste to a recycler and hoping for the best is not a defensible strategy. If you ever face an audit or a legal challenge, you must be able to prove you took the proper steps. This is where the Certificate of Data Destruction becomes one of your most valuable legal documents.
This certificate is your official, auditable record confirming that your data was destroyed in a compliant and verifiable manner. A legitimate certificate from a certified ITAD partner will always include critical details:
- Unique serial numbers of every hard drive that was wiped or shredded.
- The specific method of destruction used (e.g., NIST 800-88 3-pass wipe, physical shred).
- The date and location where the destruction took place.
- A statement of liability transferring custody and responsibility from your business to the vendor.
This document is your shield. Understanding the importance of a Certificate of Destruction is vital for any IT manager, as it provides the concrete evidence needed to demonstrate due diligence and satisfy compliance auditors.
Connecting Compliance Frameworks
Your data destruction policy does not exist in a vacuum; it is a key component of your company's broader compliance posture. To build a more robust program, it is helpful to understand how other security frameworks address these requirements, such as those found in a SOC 2 compliance checklist. These frameworks all share a common theme: demanding verifiable proof of security controls.
Beyond compliance, the value locked within retired IT assets is gaining significant attention. In 2022, poor global recycling rates left an estimated US$62 billion in recoverable resources like gold and copper simply wasted. The electronics recycling market is projected to skyrocket to US$147.9 billion by 2035, with business hardware accounting for roughly 40% of that demand. This highlights the growing economic case for professional e-waste recycling. Choosing a partner who can both secure your data and maximize material recovery isn't just good for the planet—it's a smart financial move.
How to Choose the Right ITAD Partner in Atlanta
Selecting an IT Asset Disposition (ITAD) vendor is a high-stakes decision that directly impacts your company’s security, compliance, and reputation. You are not just looking for a service to haul away old equipment; you need a strategic partner. The gap between a certified, professional recycler and a basic scrap hauler is massive, especially when you require legally defensible, auditable processes to protect your business.
In the Atlanta market, you have options, but they are not created equal. Making the right choice requires due diligence. You must ask the tough questions and demand specific credentials that prove a vendor can handle your assets securely from the moment they leave your facility.
Start with the Non-Negotiable Certifications
Before you review a price quote, your first filter must be industry certifications. These are not just logos for a website; they are hard-earned proof that a recycler meets the highest standards for environmental safety, data security, and worker protection.
Look for these two gold-standard certifications:
- R2v3 (Responsible Recycling): This is the leading global standard for the electronics recycling and repair industry. An R2v3 certified facility has passed rigorous, independent audits on everything from their data security methods and environmental controls to how they manage their downstream vendors.
- e-Stewards: This is another highly respected certification with a particular focus on preventing the illegal export of hazardous e-waste to developing nations. It’s a guarantee that your electronics won’t end up in a landfill or an unsafe processing site overseas.
If a potential vendor cannot provide a current, valid certificate for at least one of these, they should not be considered for your corporate business. It's a major red flag that signals they likely lack the audited, documented processes required to shield your company from liability.
Questions to Uncover a Vendor’s True Capabilities
Once you have confirmed a vendor holds the right credentials, it's time to probe their operational capabilities. Their answers to the following questions will reveal everything about how they manage security, logistics, and transparency. A top-tier ITAD partner will provide clear, confident answers for every one.
To help you compare potential partners in the Atlanta area, we've developed a practical checklist for your RFP process or initial vetting calls.
ITAD Vendor Evaluation Checklist
This checklist is designed to cut through sales pitches and get to the core of a vendor's capabilities. Use these questions to ensure you're covering all your bases, from data security to environmental accountability.
| Evaluation Criteria | Questions to Ask | Why It Matters |
|---|---|---|
| Data Destruction Protocols | "What specific data wiping standard do you use, like NIST 800-88? Can you provide on-site shredding services? How do you handle failed or solid-state drives?" | This confirms they use industry-recognized methods to destroy data permanently, addressing different media types and providing the highest level of security when needed. |
| Secure Logistics & Chain of Custody | "Describe your process for secure transportation. Are your trucks GPS-tracked and your drivers background-checked? What documentation is provided at pickup?" | A secure chain of custody is vital. This ensures your assets are tracked and protected from your door to their facility, minimizing the risk of theft or loss in transit. |
| Reporting & Documentation | "What will our final documentation package include? Do you provide serialized Certificates of Data Destruction and Recycling? Can we access our reports through a portal?" | Comprehensive, serialized reporting is your legal proof of due diligence. It’s what you’ll show an auditor to prove every single asset was handled correctly and securely. |
| Downstream Vendor Management | "How do you vet your downstream partners for materials like plastics or circuit boards? Can you provide a full downstream accountability report?" | A certified recycler is responsible for where every component ends up. This ensures no part of your e-waste is sent to uncertified, irresponsible handlers. |
| Value Recovery & Remarketing | "What is your process for evaluating assets for resale? How is the revenue shared, and what are your fees? How do you ensure data is destroyed before resale?" | For newer equipment, remarketing can offset costs. A transparent process ensures you get a fair return while guaranteeing data security remains the top priority. |
Think of this as your playbook for vetting vendors. A quality partner won't just have answers; they will have detailed processes and sample reports ready to back them up.
The single most important question you can ask a potential ITAD vendor is: "Can you provide me with a complete, serialized audit trail from pickup to final disposition?" A confident "yes" backed by sample reports is a strong indicator of a trustworthy partner.
Spotting the Red Flags
Knowing what to look for is only half the battle; you also need to know what to avoid. During your evaluation, be on guard for practices that might signal a less-than-reputable operator. A lowball price can be tempting, but it often comes with hidden risks that could cost you far more down the line.
Watch out for these warning signs:
- Vague answers about data security: If they can't immediately name their wiping standard (NIST 800-88 is the one you want to hear) or hedge on providing serialized certificates, walk away.
- No transparency on downstream partners: A responsible recycler is proud of their audited downstream network. Secrecy is a major red flag.
- Charging by weight without detail: While weight is a factor, a professional service is focused on security and documentation, not just the poundage of the load.
- No physical facility to tour: A legitimate recycler has a secure, professional operation. If they won’t let you see it, you have to ask what they might be hiding.
Finding the right local partner is crucial. For any business operating in the Atlanta metro, working with an experienced electronic waste recycling company means you're getting a team that understands local logistics and compliance, giving you a secure and reliable solution for your end-of-life IT assets.
Executing a Seamless E-Waste Pickup and Recycling Project
Once you’ve selected a certified IT Asset Disposition (ITAD) partner, it’s time to execute the plan. A professional e-waste engagement is not just a pickup; it's a fully managed project. It begins with logistics and scheduling and concludes with the detailed compliance reporting that officially closes the loop on your assets' lifecycle.
Success hinges on solid planning. Applying effective project planning strategies from the outset makes a world of difference. It transforms a potentially chaotic cleanout into a smooth, minimally disruptive operation.
Your ITAD partner should function as your project manager. They will walk you through every step, defining the scope, setting clear timelines, and outlining exactly what their team—and yours—will be doing on the ground.
On-Site Logistics and Asset Handling
On pickup day, a professional ITAD team arrives prepared and equipped. This is where you see the value of a certified partner versus a generic hauler. Their entire process is built around security, inventory control, and minimizing disruption to your business operations.
Here’s what that looks like in a typical office cleanout:
- Asset Tagging and Inventory: Before any equipment is moved, the team scans serial numbers or applies asset tags. This creates a detailed manifest at the source, establishing the first link in the chain of custody.
- Secure Packing and Transport: Assets are then carefully packed into sealed, secure containers or onto pallets. The team uses proper equipment to move heavy items safely. Look for company-owned, GPS-tracked vehicles and background-checked employees—this demonstrates that security is maintained door-to-door.
For large-scale projects like a data center decommissioning, these capabilities are even more critical. A professional team can handle everything from de-installing servers from racks to disconnecting network gear, all while working around your schedule to minimize downtime.
Behind the Scenes at the Recycling Facility
Once your equipment leaves your site, it is transported to a secure recycling facility. This is where the sorting, final data destruction, and material recovery take place. While you won't see this part firsthand, it is the core of a compliant corporate e-waste recycling program.
The process is methodical and includes several key stages:
- Receiving and Check-In: The sealed containers are opened, and the inventory is meticulously reconciled against the on-site manifest. Every asset must be accounted for.
- Triage and Sorting: Technicians separate equipment into different streams—items slated for data destruction, those with potential for remarketing, and devices heading directly to recycling.
- Data Destruction: This is a critical checkpoint. Hard drives and other storage media are processed according to your requirements, whether through wiping to NIST 800-88 standards or physical shredding.
- Dismantling and Recovery: All other equipment is carefully dismantled. Raw materials like steel, aluminum, copper, and plastics are separated and prepared for their journey back into the commodity markets.
This structured approach ensures nothing is overlooked. Every component is handled responsibly, maximizing resource recovery and guaranteeing your data is permanently destroyed.
The professionalism of the on-site team is a direct reflection of the vendor's overall quality. A team that is uniformed, efficient, and focused on secure handling from the start gives you confidence that the entire downstream process will be managed with the same level of care.
Final Reporting and Project Closure
The project is not finished when the truck departs. The final, and arguably most important, deliverable is your documentation package. This is your proof of compliance—the official record demonstrating your company's due diligence.
A complete reporting package must include these three elements:
- A Certificate of Data Destruction: This document lists the unique serial number of every drive and media device and confirms the destruction method used.
- A Certificate of Recycling: This certifies that all non-reusable assets were processed in an environmentally responsible manner, adhering to R2v3 or e-Stewards standards.
- A Finalized Asset Report: A detailed inventory list that serves as a complete audit trail, matching the initial on-site manifest to the final disposition of each item.
Reputable vendors, particularly those in the Atlanta area, often make the logistics incredibly simple. For Atlanta-based businesses, it’s worth exploring options for a hassle-free electronic recycling free pick-up. Receiving your final documentation is what provides the peace of mind and legal protection that defines a truly professional ITAD partnership.
Got Questions? We've Got Answers.
Even with a well-structured plan, questions about e-waste recycling often arise. We get it. Here are some of the most common inquiries from IT managers and business owners in Atlanta, with straightforward answers to help you move forward.
What’s the single most important thing to look for in a recycling partner?
If you focus on only one thing, make it verifiable certification.
Your partner must hold either an R2v3 (Responsible Recycling) or e-Stewards certification. These are not marketing badges; they are proof of rigorous, third-party audits that verify everything from data security protocols and environmental safety to the tracking of downstream materials.
A certified partner provides a legally defensible, documented process. It is your best protection against the significant risks of improper electronics disposal. Without that certification, you are operating on hope, not assurance.
Is there a real difference between wiping and shredding a hard drive?
Yes, a significant one. The choice comes down to one simple business question: does the equipment have remaining market value?
Data Wiping (Erasure): A software-based process that overwrites drives according to strict standards like NIST 800-88. It completely sanitizes the drive but leaves it physically intact, making it ideal for newer equipment you intend to resell.
Physical Shredding: The drive is ground into small fragments, making data recovery physically impossible. This is the required method for old, failed, or non-functional drives, or for devices containing highly sensitive data where 100% certainty is required.
A good ITAD partner will not just ask you to choose; they will consult with you on which method makes the most sense for each asset category.
Choosing the right data destruction method isn't just a technical decision—it's a financial one. Wiping preserves the value of remarketable assets, helping to offset the cost of your recycling program, while shredding provides the ultimate security for obsolete hardware.
How much does corporate e-waste recycling actually cost?
The cost varies based on several factors: the type and volume of equipment, the need for on-site services like de-installation, and transportation logistics.
However, many businesses find that a professional program is more affordable than they anticipate.
While some items like old CRT monitors may have a recycling fee due to their hazardous materials, newer equipment—like recent-model laptops and servers—often has resale value. This value can generate a return that significantly reduces or even completely covers the total service cost. A trustworthy vendor will provide a transparent quote detailing all potential fees and value-recovery credits upfront.
What kind of paperwork should I get at the end of the project?
The job isn't done until you have the documentation to prove it. This paperwork is your official record of compliance and due diligence. A complete reporting package from a certified recycler is non-negotiable and must include three key documents:
- Certificate of Data Destruction: A serialized report listing every single hard drive and confirming how its data was destroyed (wiped or shredded).
- Certificate of Recycling: This document certifies that your assets were processed in an environmentally sound way, following strict R2 or e-Stewards standards.
- Final Asset Report: A detailed inventory list that acts as a full audit trail, matching every asset we picked up from your location to its final outcome.
Without these three documents, you have no verifiable proof to provide to an auditor, legal counsel, or your leadership team that your company handled its retired IT assets responsibly.
Juggling data security, environmental regulations, and logistics is our expertise. At Atlanta Computer Recycling, we provide Atlanta-area businesses with secure, certified, and straightforward solutions for their IT asset disposition needs. Let us help you build a program that protects your company, your data, and your budget.
Ready to schedule a pickup or discuss your company's e-waste strategy? Contact us today to get started.