Atlanta Falcons vs Rams: Your IT Disposal Game Plan

Monday starts with a familiar kind of pressure for Atlanta IT teams. A storage room has turned into a graveyard of retired laptops. A rack of old servers still holds drives that nobody wants to touch without a plan. Finance wants value recovery. Legal wants proof. Security wants certainty. Operations wants it gone without disrupting the week.
That’s why the atlanta falcons vs rams matchup works as more than a sports reference. It’s a useful frame for a business problem that rewards preparation and punishes sloppy execution. In secure IT asset disposition, the win doesn’t go to the team with the most activity. It goes to the team with the better plan, cleaner execution, and stronger control over field position.
A rushed pickup, incomplete chain of custody, or vague destruction record is the ITAD version of a turnover in your own territory. A disciplined process, on the other hand, protects sensitive data, supports compliance, and keeps obsolete equipment out of the wrong downstream channel.
The High-Stakes Game Plan Every Atlanta Business Needs
An Atlanta IT manager usually isn’t dealing with one disposal decision. They’re dealing with five at once. User devices from a refresh cycle. Network gear pulled during an upgrade. A compliance deadline. A facilities team asking when the old equipment will leave. An executive team that assumes “recycled” automatically means “secure.”
That assumption causes trouble.
Secure electronics recycling is a business process, not a loading dock task. If your team treats it like after-hours cleanup, the weak spots show up fast. Asset records get messy. Hard drive handling becomes inconsistent. Equipment with resale potential gets shredded too early, while devices with high data sensitivity sit too long in closets and staging rooms.
A smarter approach starts by treating disposition like a game plan. You define what’s leaving, what data sits on it, what can be reused, what must be destroyed, and who signs off at each handoff. That’s where many Atlanta organizations realize they need a more structured local process for commercial IT asset handling in Atlanta.
| Business pressure | What fails in practice | What works better |
|---|---|---|
| Budget pressure | Mixing valuable and scrap assets in one batch | Triage equipment before pickup |
| Security pressure | Assuming deletion equals destruction | Match sanitization method to media risk |
| Compliance pressure | Keeping incomplete records | Require serialized tracking and final documentation |
| Space pressure | Waiting until storage is full | Schedule recurring pickups tied to refresh cycles |
| Sustainability pressure | Calling everything “recycled” | Separate reuse, remarketing, and certified recycling |
Where businesses usually fumble
The biggest mistake isn’t bad intent. It’s vague ownership.
If nobody owns the final disposition workflow, everyone assumes someone else validated serials, removed tagged assets from inventory, or confirmed what happened to failed drives. That gap is where risk grows. Not dramatically at first, but subtly enough to create expensive problems later.
Practical rule: If your disposal process can’t show who handled the device, how the data was destroyed, and where the material went next, it isn’t a controlled process.
Football fans understand this instinctively. A close game turns on field position, clock management, and discipline. ITAD works the same way. The organizations that stay out of trouble don’t rely on good intentions. They run the playbook.
Falcons vs Rams A Rivalry Defined by Strategy and Stakes
A Monday morning asset pickup can feel routine until someone asks a basic question: Which devices are in scope, which still hold regulated data, and who can prove chain of custody if an auditor asks next quarter? That is the Atlanta business version of Falcons vs Rams. The pressure is familiar, the margin for error is small, and execution decides the outcome.
The rivalry works as a useful frame because long contests are won by preparation, not by one highlight. IT asset disposition follows the same pattern. A breach, a missing laptop, or a failed audit rarely starts at the loading dock. It starts earlier, with weak intake, poor inventory discipline, unclear ownership, or a pickup scheduled before the asset list is clean.
The long game is operational discipline
Atlanta IT managers usually do not lose control in one dramatic moment. They lose it in small gaps that stack up over a quarter or over a fiscal year. Devices move between offices. Storage rooms become overflow zones. One team updates the CMDB, another handles packing, and a third assumes the recycler will sort out the exceptions.
That operating model creates preventable exposure.
Strong ITAD planning treats retirement events as part of a repeatable control system. Asset lists are reconciled before pickup. Media handling rules are set before anything leaves the site. Exceptions are documented while people still remember what happened. Companies that need Atlanta ITAD service options with serialized tracking and documented disposition usually benefit from that structure because it reduces guesswork at the exact point where mistakes get expensive.
Execution changes outcomes
Falcons vs Rams games have turned on matchup decisions, field position, and who stayed disciplined under pressure. Secure electronics recycling works the same way. The better plan on paper does not matter if assets leave the building without verified serials, if drives are mixed into a general load, or if downstream processing cannot be documented later.
For Atlanta businesses, the primary opponent is usually internal:
- operational delays that leave retired equipment sitting too long
- data exposure from media that was collected but not verified
- compliance gaps between inventory records and final disposition documents
- sustainability claims that cannot be backed by downstream reporting
I have seen organizations focus on pickup speed and miss the larger risk. Fast removal feels productive, but speed without control creates rework, documentation problems, and hard questions during audits.
The better lesson from this rivalry is simple. Winning comes from assignment-sound execution over time. In ITAD, that means every retired asset follows a defined path, every handoff is recorded, and every result can be proven after the fact.
Offensive Plays vs Defensive Stands Your ITAD Tactics
Most ITAD decisions sit on a tension point. You want to recover value where it makes sense, but you can’t let value recovery weaken your security posture. That’s where the football metaphor becomes useful. Some assets call for offense. Others demand defense.
For organizations reviewing ITAD service options in Atlanta, this is usually the first real planning question. Which assets should be pushed through a value-recovery lane, and which should move straight into a hard-security lane?
Offense means recovering value with discipline
Offensive ITAD is proactive. The goal is to move equipment before it becomes dead inventory and to preserve useful value without losing control of the process.
That usually works best for recent laptops, desktops, tablets, servers with useful component value, and network gear that still has a secondary market. Timing matters. If you wait too long, condition drops, specs age out, batteries degrade, and cosmetic issues multiply.
A practical offensive playbook often includes:
- Early triage: Separate reusable devices from scrap before packing starts. Don’t let a mixed pallet decide your outcome.
- Component-aware evaluation: A complete server might not hold the same downstream value as selected parts, depending on age and demand.
- Refresh-cycle alignment: Schedule retirement around procurement and deployment, not whenever storage runs out.
- Data handling before remarketing: Never let the value discussion outrun the sanitization decision.
What doesn’t work is chasing residual value on every item. Some teams spend too much labor trying to extract return from gear that has already crossed into low-value or no-value territory.
Defense means reducing the chance of a costly mistake
Defensive ITAD starts with a different question. If something goes wrong with this asset, how bad is the consequence?
That’s the right lens for failed drives, obsolete storage media, devices from regulated environments, and hardware that has uncertain custody history. In those cases, the job is not to maximize return. It’s to reduce uncertainty.
A strong defensive stance includes several layers:
- Choose sanitization based on media condition. Functional media may qualify for software-based wiping in some environments. Damaged, obsolete, or non-functional media often belongs in physical destruction.
- Control chain of custody. Document movement from rack, closet, or endpoint location through final processing.
- Separate compliance-sensitive batches. Healthcare, finance, legal, and public sector assets shouldn’t be mixed casually with general office refresh material.
- Verify records at handoff. If serial lists don’t reconcile at pickup, the process is already weaker than it should be.
If an asset’s risk profile is high, convenience is the wrong decision criterion.
The balance most organizations need
The best programs use both mindsets at once. They recover value where the hardware and custody record support it, and they move aggressively to destruction where the risk profile says stop.
Here’s the practical contrast:
| ITAD mindset | Primary goal | Best fit | Common mistake |
|---|---|---|---|
| Offensive | Preserve asset value | Newer, functional business equipment | Waiting so long that value evaporates |
| Defensive | Eliminate data and compliance risk | Regulated, damaged, or uncertain-custody media | Using a lighter process than the asset requires |
Teams get into trouble when they treat every asset the same. Uniform handling sounds efficient. In practice, it creates the wrong type of efficiency. It either destroys value unnecessarily or preserves risk for too long.
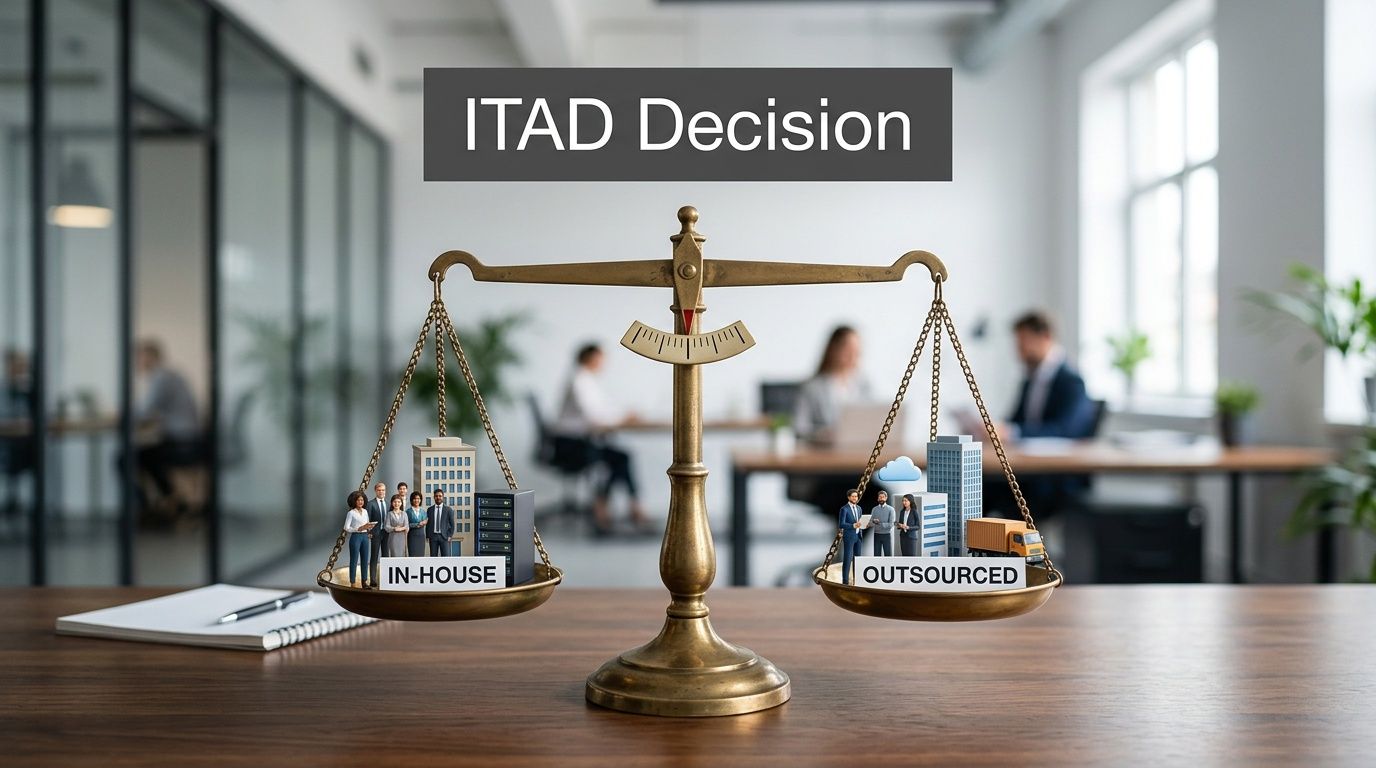
The Critical Matchup In-House vs Outsourced ITAD
Some organizations still assume in-house ITAD gives them more control. On paper, that sounds reasonable. In practice, it often means the internal team inherits every hard part of the process and none of the scale advantages.
When companies review an electronics recycling partner for business equipment, the primary concern isn’t whether internal staff can move old hardware out of a building. Of course they can. The question is whether they can execute disposition with consistent documentation, secure handling, and minimal disruption while still doing their actual jobs.
What in-house usually gets wrong
Internal teams know the environment. That helps with asset identification and coordination.
But the weak points show up fast:
- Competing priorities: Endpoint support, infrastructure work, migrations, and user issues always outrank disposal tasks.
- Process inconsistency: One batch gets logged carefully, the next one is handled during a rushed move or after-hours cleanup.
- Storage sprawl: Retired equipment lingers because nobody wants to create a separate pickup workflow for a smaller load.
- Unclear downstream control: Internal staff may know how equipment leaves, but not always how each category is processed after that.
The result is a process that looks manageable until someone asks for proof.
Why outsourcing is usually the better call
Outsourcing works because it separates specialized work from general IT workload. The disposal process gets its own chain of custody, logistics motion, and reporting path instead of competing with daily operations.
That doesn’t mean every outsourced provider is equal. The right partner should match pickup planning to your environment, handle on-site logistics without creating operational drag, and document final disposition clearly enough for audit review and internal reporting.
Internal IT should decide policy, approval, and risk thresholds. They shouldn’t spend their week acting as a disposal warehouse team.
There’s also a liability point that many companies miss. If your staff improvises packing, media handling, and transport under pressure, you haven’t really kept control. You’ve spread accountability across people who weren’t hired or trained to run a secure disposition program at scale.
The strongest model is usually hybrid. Internal teams retain governance. A specialist executes collection, handling, sanitization, and downstream processing. That keeps ownership where it belongs and puts operational work in experienced hands.
Winning Plays for Healthcare Education and Data Centers
Fourth quarter. A server room has to be cleared before Monday clinic hours. A university wants old lab hardware out between semesters. A data center team has one approved change window to pull retired gear without creating a chain-of-custody mess. The opponent is different in each case, but the pressure feels the same. Timing is tight, mistakes travel fast, and weak execution shows up later in audits, privacy reviews, and disposal costs.
That is why sector-specific ITAD planning matters. Atlanta businesses cannot run healthcare, education, and data center retirements from one generic playbook and expect clean results.
Healthcare needs red-zone discipline
Healthcare programs break down when teams treat every retired device as a resale question first. In hospitals and clinics, the first question is whether the asset touched protected health information, local patient records, imaging data, or credentials that can reopen access later.
A stronger healthcare process starts with triage.
- Separate clinical assets at intake: Nursing station PCs, diagnostic devices, tablets, and storage media should move through a dedicated stream from the start.
- Use clear media-destruction rules: If a drive’s history, condition, or encryption status is uncertain, send it to destruction instead of holding up the project over residual value.
- Map records to compliance owners: Privacy, security, and audit teams should be able to review what happened to each data-bearing asset without rebuilding the timeline.
- Confirm application retention before pickup: Some devices are retired physically before the underlying records can be released operationally.
For teams balancing disposal with broader infrastructure planning, it can help to explore IT solutions tailored for the healthcare industry so retirement workflows line up with clinical operations, support models, and security controls.
Education and government win on coordination
Schools, colleges, and public agencies rarely fail on intent. They fail on orchestration. Equipment is spread across buildings, departments, labs, storage closets, and satellite offices. One pickup date does not fix poor inventory discipline.
The better approach is to treat the project like a field-position battle. Gain control of each location before collection day.
- Build asset lists by site, building, or department.
- Mark which items contain storage media and which do not.
- Assign a local owner for each staging area.
- Schedule removals around academic breaks, office moves, and access windows.
- Hold questionable assets for review instead of letting them disappear into mixed pallets.
That structure reduces missed devices, shortens loading time, and gives public-sector teams a cleaner trail for internal review. It also prevents the common problem of discovering after pickup that one department staged monitors, another staged laptops with drives, and a third forgot the locked closet full of old desktops.
Data centers need tempo and control
Data center retirements have a different failure mode. The risk is not scattered inventory. The risk is speed without order.
A dense decommission can involve servers, switches, rails, PDUs, storage arrays, and labeled drives coming out in a sequence that affects both uptime and accountability. If teams remove gear faster than they document release, serial-level tracking breaks. If they document everything but let retired equipment sit in cages for days, physical security weakens and the project drags.
| Environment | Primary concern | Best operational move |
|---|---|---|
| Healthcare | Protected data exposure | Segregated handling and strict destruction rules |
| Education and government | Distributed asset volume | Building-based collection and scheduled bulk removal |
| Data centers | Rapid secure decommissioning | Detailed runbook, staged removal, and chain-of-custody control |
For data centers, the winning play is a written de-install sequence, named custody checkpoints, and immediate transfer into a secured disposition stream. The proof matters as much as the pull. Teams should leave the project with serial tracking, disposition status, and documentation that supports internal review, customer obligations, and downstream recycling claims. A clear certificate of destruction process and supporting audit records helps close that gap.
Your Post-Game Report Proving Compliance and Sustainability
A Falcons coach does not walk into Monday review with, "We moved the ball well." He walks in with film, assignments, missed reads, and proof of execution. Atlanta IT leaders need the same standard after an ITAD event.
The pickup is only one play. The report is what closes the possession.
What useful documentation actually looks like
Good post-disposition reporting should answer the questions an auditor, privacy officer, or operations lead will ask without forcing your team to reconstruct events from email threads.
- What assets were collected
- Which serials were processed
- What happened to the data-bearing devices
- Which items were reused, remarketed, or recycled
- What proof exists for internal and external review
That is why strong programs rely on a documented certificate of destruction process and related documentation. The form matters. The operating discipline behind it matters more. I have seen clean PDFs attached to weak custody practices, and that paperwork does not hold up once legal, compliance, or procurement starts asking for timestamps, serial exceptions, or downstream disposition detail.
Compliance and sustainability meet in the same record
The best post-game report does two jobs at once. It shows that data-bearing assets were handled under control, and it shows that retired equipment reached a documented reuse, recycling, or destruction outcome.
That combination matters for Atlanta businesses because security and sustainability are often reviewed by different stakeholders but depend on the same evidence set. If the serial log is incomplete, your security story weakens. If downstream disposition is vague, your environmental claims weaken too.
Teams that want a broader view of how regulated environments handle this often review industry commentary on Compliance IT to compare internal controls, documentation habits, and operational accountability.
The report leadership needs is not a verbal recap. It is a record set that can survive audit review, customer scrutiny, and sustainability reporting without gaps.
Securing Your Win Against E-Waste Risks
A close Falcons vs. Rams game usually turns on a few disciplined decisions late. IT asset disposition works the same way for Atlanta businesses. The win comes from control at the point where old equipment leaves your environment.
The football metaphor matters because this is not about hype or rivalry history. It is about execution under pressure. An IT manager can have budget approval, a refresh schedule, and a recycling vendor on paper, then still lose the possession with one weak handoff, one undocumented pickup, or one laptop that leaves the building without verified data destruction.
That is why e-waste risk belongs on the same play sheet as security and compliance. The wrong disposal path can expose regulated data, create audit problems, and leave the company explaining why retired assets ended up in the wrong downstream channel. The right path protects data first, then recovers value where it makes business sense, and documents the environmental outcome well enough to stand up to internal review.
For Atlanta organizations building that case internally, the broader environmental impact of electronic waste on organizations and communities helps frame the operational risk in practical terms.
Treat retirement events like field position management. Every device should have a defined next step, a controlled transfer, and a documented final outcome. That is how Atlanta businesses cut avoidable exposure and finish the ITAD process with a result they can defend.