Atlanta Falcons vs Buffalo Bills: A Strategic Review

If you're responsible for a server refresh, office closure, or data center cleanup in Atlanta, the hardest part usually isn't identifying what has to go. It's controlling what happens next. Assets move. Drives leave secure rooms. compliance requirements don't pause because a project is rushed. One weak handoff can turn a routine refresh into an audit problem.
That's why the recent atlanta falcons vs buffalo bills matchup is more useful than it looks. It wasn't just an upset. It was a clean example of how disciplined execution beats raw firepower when the environment is volatile and mistakes get punished quickly. For IT leaders, that's the key lesson. Strong outcomes come from sequencing, containment, and finishing the job under pressure.
From the Gridiron to the Data Center
An Atlanta IT manager closing part of a floor or retiring a server row faces the same kind of pressure a coaching staff faces before a major game. The inventory is spread across teams. Legal and compliance want certainty. Operations want speed. Finance wants visibility into what can be reused, recycled, or retired. Security wants chain of custody locked down from the first touch.
That doesn't feel like housekeeping. It feels like game management.
A good football team enters a high-stakes matchup with clear assignments, situational awareness, and a plan for when the first script breaks. Enterprise IT needs the same discipline. A data center shutdown with no documented runbook invites missed devices, unsecured media, and handoffs nobody can reconstruct later. A structured data center decommissioning process does the opposite. It turns a messy event into a controlled operation.
What works when the stakes are high
The teams that handle these projects well usually do a few things consistently:
| Area | Strong execution | Weak execution |
|---|---|---|
| Asset visibility | Known inventory and role-based ownership | Partial lists and assumptions |
| Data handling | Documented destruction decision for each asset class | Erase later, decide later mindset |
| Logistics | Coordinated removal windows and controlled staging | Ad hoc pickups and unsecured holding areas |
| Compliance | Evidence retained for audit and internal review | Verbal confirmation with no paper trail |
| Business disruption | Work sequenced around production needs | Shutdowns that create avoidable downtime |
The point isn't to make ITAD feel dramatic. It's to treat it with the seriousness it deserves. In football, a broken assignment becomes a free runner at the quarterback. In infrastructure work, a broken process becomes an exposed drive, a missing server, or a compliance gap that gets discovered at the worst possible time.
Practical rule: If an asset contains data, its end-of-life process should be defined before anyone unplugs it.
That mindset changes the whole project. Instead of reacting to risk after equipment starts moving, you control the field first.
Why the sports analogy actually holds up
The Falcons-Bills game matters here because it showed how disciplined execution can dictate the environment. That's the same standard IT managers should apply during disposals and decommissions. You don't need a flashy plan. You need one that survives pressure, handoffs, and surprises.
A Rivalry Defined by Strategic Execution
The historical record in atlanta falcons vs buffalo bills isn't lopsided. That's what makes it useful. Across 14 games, Atlanta holds a narrow 8-6 all-time lead, and the Falcons have averaged 21.7 points per game in the series, according to Football Database's Falcons-Bills head-to-head record. That isn't dominance by volume. It's the profile of a matchup where key moments matter.
For business leaders, that's a familiar pattern. Most competitive environments don't reward perfection. They reward the team that controls the key exchanges. In IT, that might be vendor selection, device tracking, transport security, or evidence of destruction. A project can run smoothly for days and still fail if one critical checkpoint is weak.
Why close series matter more than blowouts
A rivalry like this tells you something simple. Small advantages compound when the contest stays tight.
- Preparation matters more than reputation: A better-known brand or a larger budget doesn't guarantee cleaner execution.
- Consistency travels: The Falcons' series scoring average points to repeatable offensive competence rather than one isolated spike.
- Critical moments decide outcomes: In close environments, the side that handles pressure better usually writes the result.
That logic mirrors mature security risk management programs. The strongest organizations don't assume risk disappears. They identify where exposure concentrates, then build controls around those moments.
A lot of IT managers miss this point when they think about disposition. They focus on the big visible task, such as clearing a room, ending a lease, removing racks. The actual risk often lives in the narrow moments between tasks. Who verified serials. Who approved media handling. Who confirmed destruction method. Who signed off at release.
Long-term performance usually comes down to whether a team handles the few moments that can swing everything else.
That same lens helps when reviewing the Falcons' broader history against Buffalo. Atlanta's edge wasn't built on overwhelming superiority. It was built on enough successful decisions, enough clean finishes, and enough execution in the right windows to come out ahead over time.
The lesson for Atlanta operators
Enterprise infrastructure projects work the same way. If you want a useful local analogy, this view of the Atlanta Falcons fits well. Strong operations don't need to win every snap. They need to protect the moments that can create irreversible loss.
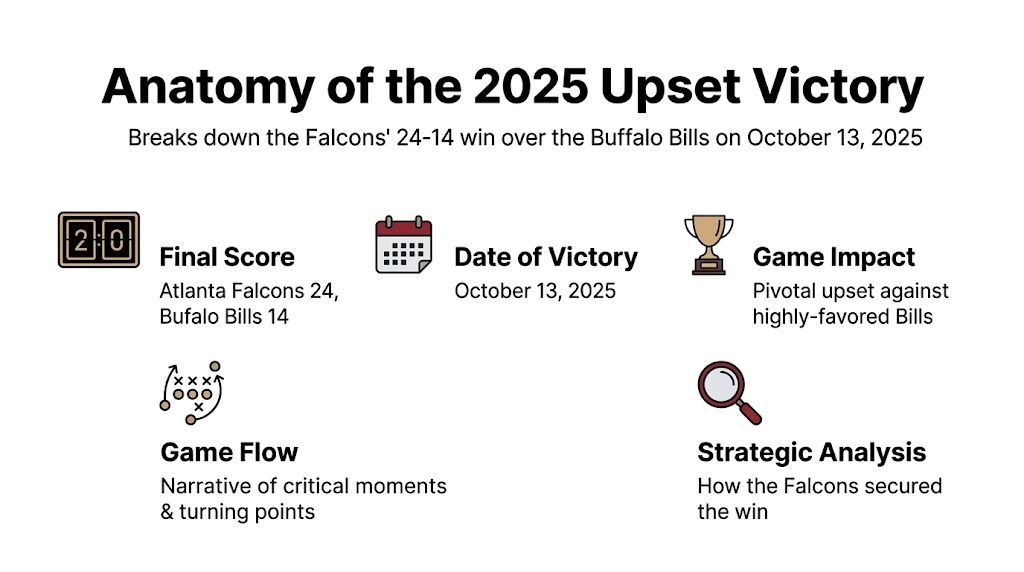
Anatomy of the 2025 Upset Victory
The most instructive recent chapter in atlanta falcons vs buffalo bills came on October 13, 2025, when Atlanta beat Buffalo 24-14 as the underdog, according to ESPN's game recap of Bills at Falcons. The result mattered because Buffalo entered with momentum and had produced at least 356 offensive yards in every prior game that season, a run Atlanta stopped cold in this matchup.
This wasn't a lucky finish driven by one bounce. Atlanta changed the terms of the game. They made Buffalo play from a less comfortable script and forced the Bills to solve problems on Atlanta's timeline, not their own.
What the upset tells business teams
A lot of organizations lose difficult projects before the work begins because they accept the other side's assumptions. The assumptions might be timeline pressure, budget pressure, staffing gaps, or the belief that secure retirement has to slow everything down. Atlanta's win is a reminder that you can reset the environment if the plan is coherent.
Three features of the game stand out from a strategy perspective:
| Strategic element | What Atlanta did | IT parallel |
|---|---|---|
| Tempo control | Dictated game flow instead of chasing Buffalo's pace | Control project sequencing instead of reacting to deadlines |
| Constraint | Broke Buffalo's prior yardage pattern | Limit where risk can spread during disposition |
| Finish | Turned discipline into a clear margin | Convert process discipline into audit-ready outcomes |
What works in an upset
Underdogs usually don't win by trying to match strengths head-on. They win by narrowing the game to a smaller set of controllable variables.
In IT operations, that often means:
- Reducing moving parts: fewer handoffs, fewer storage points, fewer unknown devices.
- Defining the decision path early: wipe, shred, redeploy, resell, recycle.
- Protecting the middle of the process: most failures happen after planning and before final documentation.
The Falcons did the football version of that. They didn't need to out-hype Buffalo. They needed to execute a game plan that denied Buffalo an easy rhythm and preserved Atlanta's own.
When a favored team loses control of pace, the talent gap matters less. The same thing happens in infrastructure projects.
That's why this result still resonates beyond sports. It shows how a disciplined operator can beat expectations by controlling sequence, not by improvising harder.
Winning the Battle at the Line of Scrimmage
Most NFL games are decided before the highlight clip goes viral. They turn in the less glamorous exchanges. Blocking angles. Gap discipline. Physical advantage. That's exactly why the Falcons' ground success against Buffalo is the best on-field analogy for secure asset handling. The visible result gets attention. The controlled process underneath is what made it possible.
According to ESPN's box score and game detail for Bills at Falcons, Bijan Robinson rushed for 170 yards, including an 81-yard touchdown, and Atlanta's offensive line created 4.2 yards before contact. That's the kind of detail practitioners pay attention to. It shows the run game wasn't just a product of one player's talent. The front created space before the defender could even interfere.
Individual brilliance versus process design
Leaders often misread successful projects the same way fans misread explosive rushing performances. They see the star output and miss the system.
Compare the two views:
| Lens | Superficial reading | Operational reading |
|---|---|---|
| Robinson's yardage | Great back had a big night | Blocking and design put him in favorable lanes |
| Long touchdown | One explosive play changed the game | Repeated trench wins made the explosive play available |
| Offensive success | Skill overcame resistance | Unit execution removed friction early |
That distinction matters in ITAD. If a decommissioning project finishes on time, it's tempting to credit hustle. But hustle isn't a repeatable control. Process is. Clean outcomes come from inventory discipline, packaging standards, media handling rules, and trackable movement from origin to final disposition.
What line-of-scrimmage discipline looks like in IT
The football parallel is direct. At the line, every player has an assignment. In secure retirement, every device should too.
- Known ownership: Someone must own the asset decision. Ambiguity creates exposure.
- Defined handling path: A laptop doesn't need the same retirement path as a failed storage array.
- Verified movement: The chain matters as much as the final destination.
A strong IT asset tracking software workflow supports that discipline because it reduces guesswork at exactly the point where projects tend to get messy. If your team can't answer where a device was, who touched it, and what happened to its data, then your process is relying on memory instead of control.
The cleanest projects look boring from the outside. That's usually a sign the underlying controls are doing their job.
What doesn't work
I've seen teams treat end-of-life handling like cleanup after main work is done. That's the equivalent of assuming the running back will create yards with defenders already in the backfield. It puts pressure on the last person in the process to solve a problem the organization should've prevented earlier.
What fails most often is familiar:
- assets staged without clear labels,
- mixed media types handled under one blanket instruction,
- late decisions about destruction,
- and undocumented exceptions because the schedule tightened.
The Falcons didn't win in the trenches by being vague. They won by giving a valuable asset a protected path. That's exactly how mature IT teams should think about retired equipment carrying sensitive data.
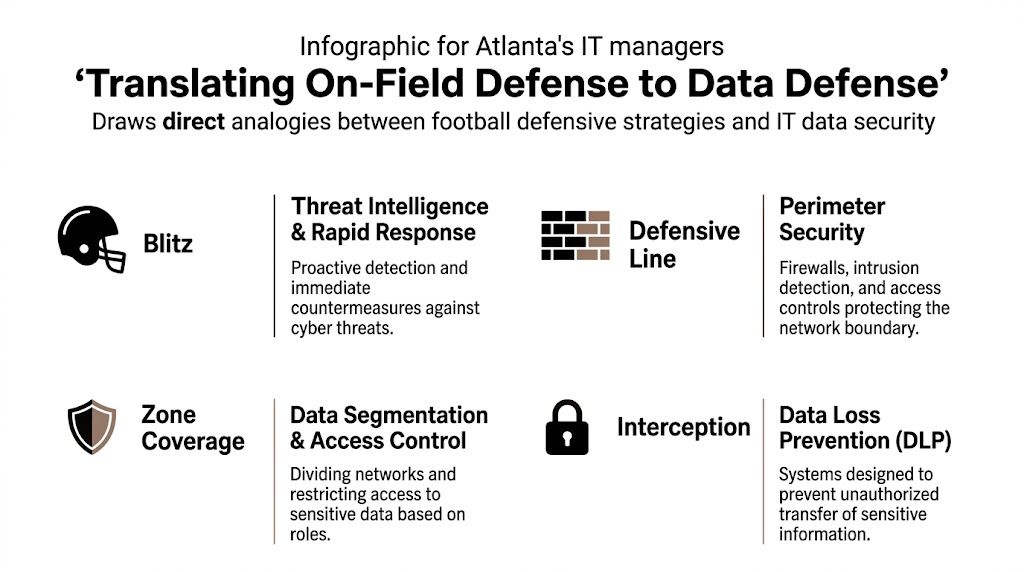
Translating On-Field Defense to Data Defense
Defense in football isn't just about force. It's about denying clean reads, compressing time, and making the other side operate under stress. That's why the Falcons' pass-pressure approach against Buffalo maps so well to data security during asset retirement. The objective is the same. Reduce opportunity. Force control. Prevent recovery.
A useful detail from the game often gets overlooked. NFL video coverage of Atlanta's pressure on Josh Allen ties the result to pressure, noting that Josh Allen's QBR drops 25% against defenses that blitz over 35% of the time, and that Atlanta's plan in this game helped force two turnovers while holding Buffalo to 14 points. That's a practical lesson for IT leaders. Pressure changes outcomes when it's targeted and timely.
Your blitz package for retired assets
In IT, the "blitz" isn't panic. It's a set of proactive controls that close gaps before data can escape governance.
Here are the strongest equivalents:
| Football concept | Data security equivalent | Why it matters |
|---|---|---|
| Blitz pressure | Immediate containment and verified destruction workflows | Reduces the window where data can leak |
| Tight coverage | Access control and segmented handling authority | Prevents casual or unauthorized handling |
| Forced turnover | Capturing assets into controlled custody | Moves risk from unknown space into governed space |
A weak IT retirement process gives risk too much time. Devices sit in hallways. Drives wait in cages. Teams assume someone else approved the wipe. That delay is where loss happens. A stronger model assigns handling authority early, separates reusable equipment from obsolete media, and makes destruction evidence part of the workflow rather than a follow-up task.
What resilient teams do differently
Legal teams increasingly treat technology retirement as part of resilience planning, not janitorial work. That broader view is worth adopting. This perspective on Business Planning for Digital Security and Resilience is useful because it reinforces a point IT managers already feel in practice. Security isn't only about active systems. It's also about what leaves the environment and how.
For Atlanta organizations, the practical controls are straightforward:
- Constrain access early: Once devices are marked for retirement, handling rights should narrow, not expand.
- Choose destruction paths before pickup: Teams make fewer mistakes when the decision isn't deferred.
- Document exceptions: Edge cases are where audits become painful.
- Close the proof loop: If destruction occurred, someone should be able to prove it without hunting through email.
A formal secure data destruction program matters because it converts intent into evidence. That's the difference between hoping a risk was addressed and knowing it was closed.
Security controls are strongest when they remove discretion from the riskiest moment.
The Allen lesson for IT leaders
Quarterbacks struggle when the picture changes after the snap and the pressure arrives on time. Organizations struggle the same way when retirement projects expose hidden weaknesses in governance. The answer isn't to move slower. It's to make the process harder to break.
That means fewer informal decisions, tighter custody, and destruction methods that stand up to scrutiny. In football terms, the best defense doesn't wait for the offense to settle in. It disrupts the play before it develops.
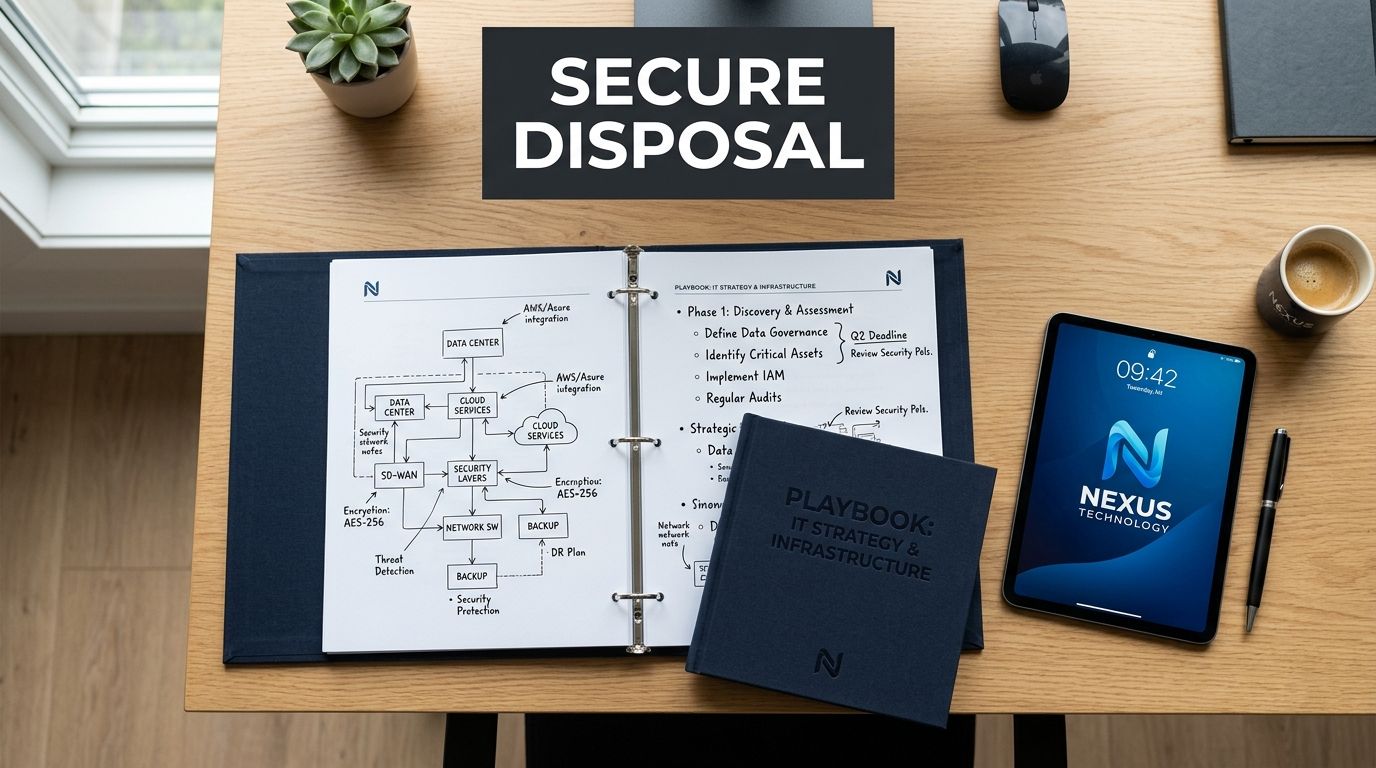
Your Playbook for Secure IT Asset Disposition
By the time equipment reaches end of life, most business value has already been extracted from the hardware. The remaining value sits somewhere else. It sits in risk reduction, proof of compliance, continuity of operations, and the confidence that no one will revisit the project later because a drive, server, or network appliance slipped through the cracks.
That's where many organizations get the decision wrong. They optimize for removal speed and treat security as a box to check after the truck leaves. The better approach is to judge every disposition plan by one standard. Can it produce a secure, documented, low-disruption outcome under real operating conditions?
That standard fits the final defensive lesson from this Falcons-Bills game. A video breakdown of Atlanta's win over Buffalo notes that the Falcons held the Bills to 285 total yards, extending their run as the NFL's only unit to keep every opponent under 300 yards per game. That kind of consistency is what security leaders should want from asset disposition. Not occasional excellence. Reliable execution under pressure.
A practical decision framework
If you're evaluating your own process, start with these questions:
Can you account for every asset scheduled for removal?
If not, the project has an inventory problem before it has a recycling problem.Is the data outcome defined per device type?
Servers, laptops, failed drives, and network gear shouldn't all ride the same generic instruction.Can you show evidence without reconstructing it manually?
If your audit trail lives in spreadsheets, screenshots, and inbox threads, it won't hold up well when timing matters.Will the process interrupt business operations more than necessary?
A strong plan works around production realities instead of forcing teams into avoidable downtime.
What strong ITAD execution usually includes
The right IT asset disposal plan doesn't need to be complicated. It needs to be precise.
- On-site coordination: Equipment removal should be staged around access windows, operational constraints, and facility requirements.
- Clear media decisions: Reusable devices and obsolete storage media need different handling paths.
- Documented custody: Every movement should reduce uncertainty, not create more of it.
- Final accountability: The process should end with proof, not assumptions.
What doesn't work is the opposite approach. Loose staging areas. Last-minute sorting. Mixed pallets. Unclear wipe-versus-shred decisions. Those shortcuts save a little effort up front and create larger risk later.
One rule to keep: If a process depends on everyone remembering what to do, it isn't a secure process yet.
Why this matters for Atlanta organizations
Hospitals, school systems, government offices, and large enterprises all retire equipment under different constraints. The common issue is that sensitive data doesn't become harmless just because the device is old. The retirement event is often the last point where your controls can fail publicly.
That makes disposition a leadership issue, not just an operations task. The strongest teams treat it like a managed playbook. Roles are assigned. Movement is controlled. Proof is built in. The finish is as disciplined as the start.
The Falcons showed what that looks like in competitive form. They didn't just survive a dangerous opponent. They kept the opponent from establishing rhythm at all. That's the model worth borrowing.
Atlanta businesses that need a disciplined partner for secure IT asset retirement can work with Atlanta Computer Recycling. The company supports commercial ITAD, data center decommissioning, secure data destruction, and responsible electronics recycling across the Atlanta metro area, with a process built for organizations that need compliance, custody, and operational efficiency handled correctly from first pickup to final disposition.