Atlanta E-Waste Disposal: A Business Guide To Secure ITAD
For any business, handling Atlanta e-waste disposal correctly is about much more than just recycling old tech. It’s a vital strategy for protecting your most sensitive data, staying on the right side of regulations, and avoiding serious financial and reputational liabilities. A professional IT Asset Disposition (ITAD) plan isn't a luxury—it's a critical component of your risk management framework.
Why Smart E-Waste Disposal Is A Critical Business Decision
That collection of old electronics gathering dust in a storage closet? It's not just clutter. It's a significant—and often completely overlooked—business liability. Every retired server, laptop, and hard drive holds a detailed history of your operations, from client lists and financial records to intellectual property. Improperly disposing of these assets is a direct threat to your organization's security and bottom line.
Think of each old asset as a locked digital filing cabinet. Without a certified process to permanently destroy what's inside, you're essentially leaving the key in the lock for anyone to find. Cutting corners here can lead to a world of trouble:
- Costly Data Breaches: Data recovered from carelessly discarded drives can expose customer information, trade secrets, and internal communications. The financial and reputational fallout can be devastating.
- Regulatory Fines: If your business is in healthcare (HIPAA), finance (GLBA), or handles consumer data (FACTA), data protection regulations are ironclad and apply to end-of-life equipment. A compliance misstep can trigger hefty penalties.
- Environmental Non-Compliance: Federal EPA regulations are clear about how to handle the hazardous materials found in most electronics. Improper disposal isn't just irresponsible; it can lead to significant fines.
The Scale Of The Challenge In Atlanta
The need for a professional approach is even more clear when you look at the waste management challenges right here in our city. Recent audits paint a bleak picture, showing a local recycling rate of just 23%. That means a staggering 77% of all collected materials are simply treated as garbage. This systemic issue makes it absolutely crucial for businesses to take control of their own e-waste stream.
This is where a strategic ITAD plan changes the game. It turns a liability into a controlled, secure, and documented process. It’s not just about "being green"—it’s about protecting your business from the ground up by managing the complete lifecycle of your IT assets.
By viewing e-waste through a lens of risk management, companies can safeguard their most valuable asset—data—while upholding their commitment to corporate responsibility. A proper disposal plan is an investment in security and peace of mind.
Ultimately, partnering with a professional ITAD provider is just sound business strategy. Beyond doing the right thing for the environment, smart e-waste management can also help you reduce operational costs. To really get a handle on the bigger picture, you can explore the full environmental impact of electronic waste and see why this issue demands executive-level attention.
Navigating Georgia's E-Waste Compliance Landscape
Understanding your legal responsibilities is the first step in any smart Atlanta e-waste disposal plan. For many businesses here, the rules can feel murky. There’s a common—and dangerous—misconception that since Georgia doesn’t have a state-level e-waste law, the regulatory burden is light.
That assumption couldn't be more wrong.
While it’s true there’s no specific Georgia mandate forcing electronics recycling, your business is absolutely not off the hook. You’re still bound by powerful federal regulations, and they come with serious penalties. Think of these federal rules as the non-negotiable baseline for every company in the country.
Federal Regulations: The Bedrock Of Compliance
The main law you need to know is the Resource Conservation and Recovery Act (RCRA), which is enforced by the EPA. The simplest way to think about RCRA is as the official rulebook for managing hazardous waste. The thing is, a lot of common electronics—especially older CRT monitors and certain batteries—are packed with materials like lead and mercury, which the EPA classifies as hazardous.
Tossing these items into a dumpster is a direct violation of RCRA. It means your business has a legal duty to make sure those toxic materials are handled and disposed of correctly. Skip this step, and you could be facing fines that make the cost of professional disposal look like pocket change.
But the EPA is only part of the story. Industry-specific rules add another critical layer of compliance, and these focus on something that keeps executives up at night even more than environmental fines: data security.
For most businesses, the biggest risk isn't an environmental penalty—it's a data breach that starts with a retired piece of equipment. Compliance isn't just about checking a box; it's about actively defending your organization from a catastrophic fallout.
Industry-Specific Mandates Like HIPAA
For many industries, the data protection laws are even stricter than the environmental ones. If your organization handles any kind of sensitive information, your legal duties cover the entire life of the devices that store it, right up to the very end.
- HIPAA (Health Insurance Portability and Accountability Act): For any healthcare provider, insurer, or related business in Atlanta, HIPAA is the law of the land. It demands that all Protected Health Information (PHI) on any device be made completely unrecoverable before disposal. Just hitting "delete" won't cut it, and a breach can trigger fines running into the millions.
- FACTA (Fair and Accurate Credit Transactions Act): Any company that handles consumer credit reports falls under FACTA. The act requires the secure destruction of that consumer data to head off identity theft.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions are required to have a formal security plan to protect client information, and that absolutely includes how it's disposed of when the hardware is retired.
The scale of the global e-waste problem really brings these risks home. Projections show we're on track to generate over 60 million metric tonnes of e-waste worldwide, but less than 25% of it is properly recycled. For a business, that massive, uncontrolled stream of discarded electronics is a minefield of potential data breaches.
Trying to navigate this web of federal and industry rules on your own is a huge challenge. Working with a certified ITAD provider is simply the most effective way to ensure you're meeting every single legal requirement. A professional service gives you a clear chain of custody and a Certificate of Destruction—the auditable proof you need to show you’ve done your due diligence and protected your business from risk. For a deeper dive into the specifics, check out our guide on electronic recycling in Atlanta, GA.
The Secure ITAD Process: From Your Office To Final Disposition
What really happens to your old equipment after it leaves your facility? For too many Atlanta businesses, that process is a black box, full of uncertainty and risk. A professional IT Asset Disposition (ITAD) workflow isn't just about hauling away old gear; it’s a transparent, secure, and fully documented journey designed to give you complete peace of mind.
Think of it like decommissioning a secure facility. You wouldn't just leave the doors unlocked and walk away. You’d follow a strict protocol to account for every asset, secure every entry point, and ensure no sensitive information is left behind. We apply that same level of rigor to your retired electronics, turning a potential liability into a controlled, predictable operation.
The entire procedure is built on a foundation of accountability. From the moment our team arrives at your location to the final certificate of destruction, every step is tracked and verified with security as the top priority. This systematic approach eliminates guesswork and gives you a clear, auditable trail for your compliance records.
Step 1: On-Site Assessment And De-Installation
The journey begins right at your office, data center, or storage facility. A true ITAD partner doesn’t just show up with a truck; we start with a careful on-site inventory and assessment. Our technicians work directly with your IT team to catalog every single asset slated for disposal—from servers and laptops to networking gear and peripherals.
During this phase, we identify which items might still hold recoverable value for remarketing and which are destined for secure recycling. This initial audit is critical for establishing the chain of custody that will follow each device from start to finish.
Once the inventory is locked down, our team handles the secure de-installation of the equipment. We do this with precision to minimize disruption to your ongoing operations. We can manage everything from de-racking servers in a live data center to systematically unplugging workstations during an office move.
Step 2: Secure Logistics And Bonded Transport
With the equipment disconnected and cataloged, the next step is ensuring its safe and secure transit. This is absolutely not a job for a standard moving company. We use bonded and insured logistics to move your assets from your location to our secure processing facility.
This step is crucial for maintaining an unbroken chain of custody. Every pallet of equipment is sealed and tracked, guaranteeing that nothing gets lost or compromised between your door and ours. This secure transport protocol is a non-negotiable part of any compliant Atlanta e-waste disposal program.
The moment an asset leaves your direct control, its security becomes paramount. A documented chain of custody is not just a best practice; it is your primary defense against downstream liability and potential data breaches.
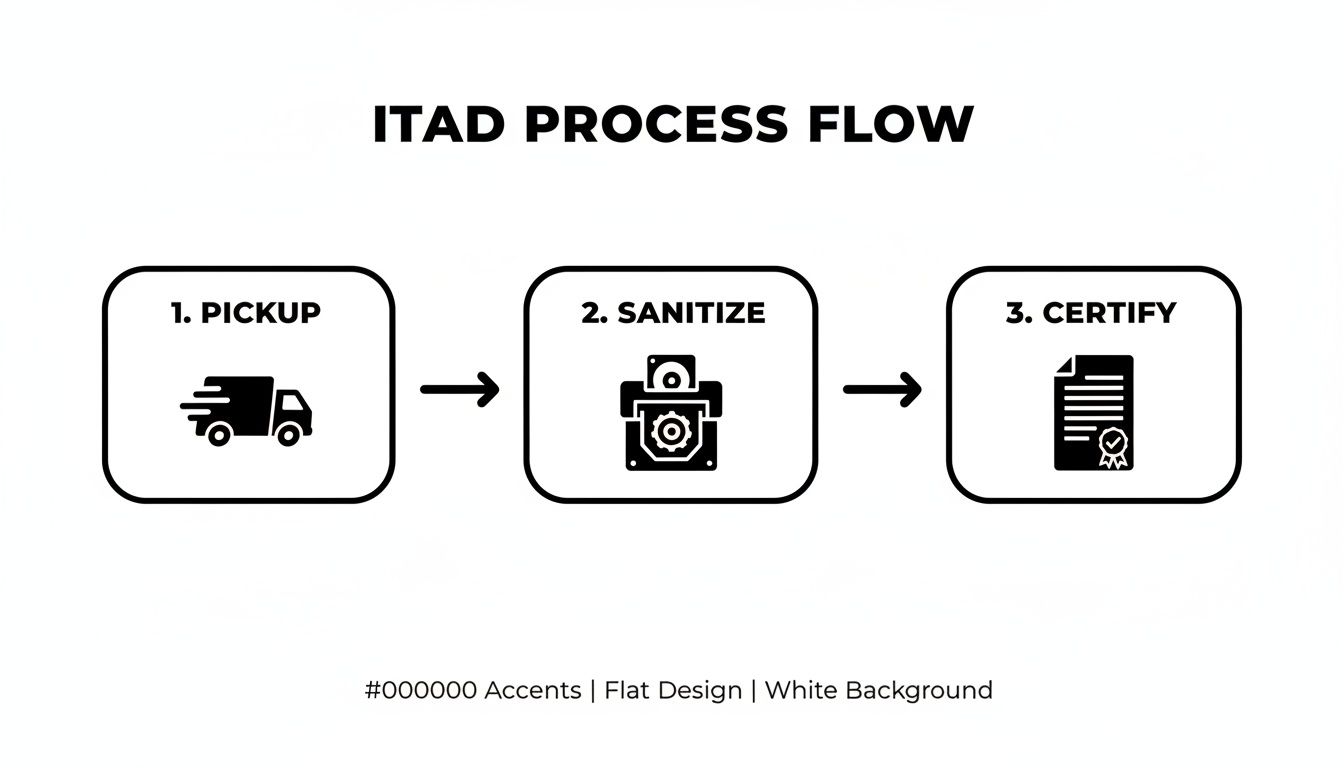
This visual shows the simplified, core workflow of a secure ITAD process from pickup to final certification.
Each of these steps is a critical control point designed to protect your data and ensure regulatory compliance.
Step 3: Data Sanitization And Final Disposition
Upon arrival at our facility, the assets are received and the inventory is checked against the on-site catalog. Now, the most critical phase begins: certified data sanitization. Every device containing a hard drive or solid-state storage is subjected to rigorous, documented data destruction protocols.
We use methods that align with standards like DoD 5220.22-M for data wiping. For drives that are non-functional or when required for maximum security, we perform physical shredding, which grinds the media into tiny, irrecoverable fragments.
After all data has been verifiably destroyed, the assets are sorted for their final disposition.
- Remarketing: Functional, late-model equipment is refurbished and prepared for resale, capturing any residual value for your organization.
- Responsible Recycling: End-of-life or obsolete electronics are de-manufactured. Components are separated into base commodities like steel, plastic, and precious metals, which are then sent to certified downstream processors to be reused in new products.
This final step ensures that nothing ends up in a landfill. By understanding what happens to recycled electronics, you can appreciate how a professional ITAD service not only protects your data but also contributes to a circular economy.
For quick reference, here's a breakdown of how we recommend handling common IT assets to ensure both data security and proper environmental stewardship.
IT Asset Disposal Recommendations
| Asset Type | Key Concern | Recommended Data Sanitization | Final Disposition |
|---|---|---|---|
| Servers & SANs | High-density sensitive data | On-site or off-site physical shredding | Responsible Recycling |
| Laptops & Desktops | Employee, customer, and IP data | DoD 5220.22-M wipe or shredding | Remarketing or Recycling |
| Network Gear | Configuration data, access logs | Factory reset and firmware wipe | Remarketing or Recycling |
| Mobile Devices | PII, corporate access credentials | Factory reset and physical shredding | Responsible Recycling |
This table provides a solid baseline for your IT retirement policy, but every project is unique. A good ITAD partner will help you customize the process to fit your specific compliance needs.
Data Destruction: The Most Important Step In E-Waste Disposal
There’s a dangerous misconception that can cost a business dearly: thinking a deleted file is a destroyed file. It's not.
Simply dragging documents to the trash bin or even reformatting a hard drive leaves behind a ghost of the original data. These digital remnants can be easily recovered by someone with basic forensic tools, turning a retired server or laptop into an open gateway to your company's most sensitive information.
This is why guaranteed data destruction is, without question, the most critical part of any professional IT asset disposal plan. It’s the one step that directly protects you from the catastrophic fallout of a data breach. The risk isn't just theoretical; it’s a constant threat lurking on every retired hard drive, server, and mobile device your company no longer uses.
To properly secure your business, you need to understand the two primary, industry-accepted methods for eliminating this risk. Each serves a specific purpose, and choosing the right one is essential for compliance and complete peace of mind.
Software Wiping Versus Physical Shredding
Imagine your hard drive is a library full of books containing confidential information. One way to secure it is to go through every single book and meticulously black out every word on every page, multiple times, until it’s all illegible. That's the principle behind software-based data wiping.
- Software Wiping: This method uses specialized programs to overwrite every sector of a hard drive with random ones and zeros. Standards like DoD 5220.22-M require multiple "passes" to ensure the original data is rendered completely unrecoverable. It's an excellent option for sanitizing functional drives that may be refurbished and resold, maximizing asset value recovery.
Now, imagine a different approach. Instead of blacking out the books, you throw the entire library into an industrial shredder that turns every page into confetti. That’s physical destruction.
- Physical Shredding: This is the most absolute form of data destruction. The hard drive or solid-state media is mechanically ground down into tiny, unrecognizable metal fragments. This is the only acceptable method for non-functional drives or for organizations that require the highest level of security assurance. There is zero possibility of data recovery.
Choosing between these methods often comes down to your industry's compliance rules and your internal security policies. For many Atlanta businesses, a combination of both is the ideal strategy for a comprehensive Atlanta e-waste disposal program.
Your Legal Proof Of Compliance
After the data is destroyed, how do you prove it? This is where the single most important document in the entire ITAD process comes into play: the Certificate of Destruction.
Think of this certificate as the official death certificate for your data. It is your formal, legal proof that you fulfilled your due diligence in protecting sensitive information, providing an auditable record that can be presented to regulators, auditors, or legal counsel.
This document is not just a receipt. A proper Certificate of Destruction is a detailed record that should include:
- A unique serial number for tracking.
- The date the destruction was completed.
- The specific method used (e.g., DoD 5220.22-M wipe or physical shredding).
- An inventory or serial number list of the assets that were sanitized.
Without this certificate, you have no verifiable evidence that your company's data was properly handled and destroyed. It closes the loop on the chain of custody, shifting liability from your organization to your certified ITAD partner. As you can see, the methods and documentation for secure data destruction are detailed and precise for a reason—they are your ultimate protection against future risk.
How To Choose The Right ITAD Partner In Atlanta
Picking a partner for your company's Atlanta e-waste disposal is about a lot more than just getting a price quote. Not all recycling services are created equal, and the company you choose is literally holding your data security and corporate reputation in their hands. A low-cost vendor that cuts corners can expose you to staggering liabilities, from data breach lawsuits to steep regulatory fines.
Think of it like hiring a security firm to decommission a sensitive facility. You need a team with proven credentials, transparent processes, and an ironclad commitment to protecting your interests. A quick, surface-level check just won't cut it; you have to dig deeper to find a partner who can truly safeguard your business.
This means moving past glossy brochures and asking the tough questions that separate a simple hauler from a genuine security partner. Your goal is to find a provider who operates as a natural extension of your own risk management and compliance team.
The Non-Negotiable Credentials
Before you even look at a quote, any potential partner has to meet a baseline of industry-recognized standards. These certifications aren't just logos for a website—they're proof of rigorous, third-party audits that verify a company’s commitment to security, environmental responsibility, and operational integrity.
Your checklist of non-negotiables should include:
- Industry Certifications: The vendor absolutely must hold a current R2 (Responsible Recycling) or e-Stewards certification. These are the gold standards in the ITAD world, ensuring a recycler sticks to the highest protocols for data security, environmental safety, and worker protection.
- Adequate Insurance: Ask for their certificate of insurance. Specifically, you need to see policies covering data breach liability, errors and omissions, and pollution liability. A standard general liability policy is not nearly enough to protect you if something goes wrong.
- Transparent Chain of Custody: The provider must show you a clear, documented chain-of-custody process. This is the paper trail that tracks your assets from the second they leave your office to their final destruction, providing an unbroken line of accountability.
If a vendor is missing any of these foundational elements, they shouldn't even be in the running. These are the essential qualifications that prove a company is serious about professional, secure asset management.
Choosing an uncertified vendor to handle your sensitive IT assets is like hiring an unlicensed security guard. You might save a few bucks upfront, but the potential cost of a breach or compliance failure is exponentially higher.
Critical Questions To Ask Potential Vendors
Once a company has proven its basic credentials, it's time to dig into their day-to-day operations and security posture. The answers to these questions will tell you everything about the true quality and reliability of their service. Treat this conversation like a critical job interview—because it is.
Here are the essential questions you need to ask any potential ITAD partner in Atlanta:
- "Can you detail your on-site security procedures during pickup?" A professional team will show up in uniform, drive marked vehicles, and be able to walk you through their process for securing and inventorying assets before they're even loaded onto the truck.
- "How do you track our assets from pickup to final destruction?" You're looking for a clear answer involving serialized inventory reports, sealed and secured transport, and a formal check-in process at their facility. Vague responses are a huge red flag.
- "What are your specific data destruction methods and standards?" They should be able to clearly explain their software wiping protocols (like DoD 5220.22-M) and their physical shredding capabilities. Ask if you can witness the destruction, either in person or via video.
- "Can we see a sample of your Certificate of Destruction?" This document is your legal proof of compliance. Review a sample to make sure it includes all the necessary details, like asset serial numbers and the specific destruction methods used for each item.
The quality and confidence of their answers will tell you everything you need to know. A partner you can trust will welcome this level of scrutiny and give you detailed, transparent responses. For more insight on what to look for, learning more about a top-tier electronic waste recycling company can provide a great benchmark for your evaluation.
Handling Large-Scale Projects Like Data Center Decommissioning
Everyday Atlanta e-waste disposal is one thing. But decommissioning an entire data center or navigating a company-wide tech refresh? That's a different challenge altogether. These are high-stakes operations where the risks of data exposure, logistical chaos, and operational downtime are magnified a hundredfold. A simple pickup service just won’t cut it. You need a strategic partner who can manage a complex project with absolute precision.
Think about a common scenario: a large Atlanta company is moving its primary data center. They're dealing with hundreds of servers, storage arrays, and networking switches that need to be retired securely. This isn't just about unplugging a few cords—it's a massive undertaking with serious security and logistical hurdles.
A professional ITAD team turns this potential headache into a controlled, streamlined process. The project starts not with a truck, but with a detailed plan built hand-in-hand with your IT staff to ensure zero disruption to live systems.
A Case Study In Secure Decommissioning
Let’s walk through how a project like this actually works. Imagine the client is an established financial services firm. They cannot afford even the slightest risk of sensitive data leaving their facility. For our team, the first step is always on-site data destruction. Before a single server is un-racked, our technicians bring portable, industrial-grade shredders right onto the data center floor.
Under the watchful eye of the client’s security team, every single hard drive and solid-state drive is removed, its serial number is scanned into an inventory list, and it’s immediately fed into the shredder. This approach completely eliminates the chain-of-custody risk that comes with transporting live data. The information is turned into irrecoverable fragments before it ever leaves the building.
For high-security environments like data centers, on-site data destruction is the only acceptable protocol. It moves the point of destruction from a remote facility directly to your secure perimeter, providing absolute verification and peace of mind.
Once the data is neutralized, the real logistical work begins. Our team systematically de-racks hundreds of servers, disconnects networking gear, and untangles the complex web of power and data cables. It’s not just about pulling wires; it involves careful labeling and organization to prevent damage and leave the space clean and ready for its next phase.
From Chaos To Control
After all the hardware is de-installed, it’s professionally palletized, shrink-wrapped, and prepped for secure transport. The inventoried assets—now completely free of any data—are loaded onto a GPS-tracked truck for the trip to our processing facility. This documented process ensures every piece of equipment is accounted for, from your server room to our doorstep.
This is the real value an ITAD partner brings to the table. We handle the intense labor, the complex logistics, and the critical security protocols. This frees up your internal teams to focus on their core responsibilities, like getting the new systems online. The result is a seamless transition, not a chaotic scramble.
Finally, the client receives a comprehensive project report. This includes the full inventory list and the all-important Certificate of Destruction, providing a complete, auditable record of the entire project. It's the final step that proves compliance and formally closes the lifecycle of every retired asset. What could have been a logistical nightmare becomes a documented success.
Answering Your Questions About Business E-Waste Disposal
When it's time to retire your company's old tech, you're bound to have questions. Getting it right is crucial for security and compliance. Here are some straightforward answers to the questions we hear most often from IT managers and business leaders here in Atlanta.
What Kind of Electronics Do You Take?
We focus exclusively on the complete range of corporate IT assets for commercial clients. Think servers, laptops, desktops, networking gear like switches and routers, data storage arrays, and all the peripherals that go with them. Our entire process is built from the ground up to handle business-grade equipment securely.
Is There a Fee for Business Pickup?
Yes, professional IT Asset Disposition (ITAD) is a secure service, and that comes with associated costs. The final price for your Atlanta e-waste disposal project really depends on a few things: the amount and type of equipment you have, where you're located, and any special services you need, like having us destroy data on-site at your facility.
We provide clear, transparent quotes that reflect the real value of secure, compliant, and fully documented disposal. It’s an investment that protects you from the much, much higher costs of a data breach or a regulatory fine down the road.
How Can I Be Sure My Data Is Actually Destroyed?
This is the most important question, and we provide a definitive answer. Once the job is done, we issue a formal Certificate of Destruction to your organization. This is a legal document that serves as your auditable proof that you did your due diligence to protect sensitive information.
This certificate isn't just a piece of paper; it officially details:
- A manifest of the items that were processed.
- The exact data destruction method we used—whether it was multi-pass wiping to DoD standards or physical shredding.
- A documented transfer of liability from your company to ours.
This document is the final, essential step. It closes the loop on your asset's lifecycle and gives you the hard evidence you need to satisfy any audit, internal or external, confirming your company’s data is gone for good.
Ready to handle your company's e-waste with confidence? Atlanta Computer Recycling provides secure, compliant, and documented ITAD services for businesses across the metro area. Get a transparent quote and ensure your data is protected by visiting https://atlantacomputerrecycling.com.