Secure Business Computer Disposal Atlanta GA: A 2026 Guide for Your Company
For Atlanta businesses, that closet full of old computers isn't just clutter—it's a significant corporate liability. Every retired workstation, server, and laptop is a repository of sensitive data, from confidential client information to proprietary financial records. A single improperly disposed hard drive can trigger a devastating and costly data breach.
This guide outlines the essential steps for establishing a secure, compliant, and responsible IT Asset Disposition (ITAD) strategy for your organization.
Why Secure Disposal Is a Critical Business Function
When your company refreshes its technology, the old equipment doesn't just become obsolete. It becomes a container filled with your digital history—proprietary documents, customer information, trade secrets, and more.
Many believe that formatting a drive is sufficient data protection. This is a dangerous misconception. Data from formatted drives can often be recovered with basic software, creating a direct path for unauthorized access to your company's most confidential files. For any business in Atlanta, overlooking this final step of the IT lifecycle is an unacceptable risk.
The Real Risks of Improper Disposal
The fallout from a data breach caused by discarded electronics extends far beyond data loss. The consequences are severe, impacting your organization's financial stability, legal standing, and public reputation.
Consider the potential damages:
- Crushing Compliance Fines: Regulations like HIPAA, SOX, and GLBA carry substantial penalties for non-compliance. A single breach can lead to fines that climb into the millions.
- Lost Customer Trust: Reputation is a core business asset. A public data breach shatters the trust you've worked to build, sending clients to competitors and damaging your standing in the Atlanta business community.
- Heavy Financial Hits: Beyond fines, your organization faces the direct costs of forensic investigations, credit monitoring for affected parties, legal battles, and potential class-action lawsuits.
A retired hard drive isn't just old hardware; it's a locked file cabinet full of your company's secrets. Improper disposal is like leaving that cabinet wide open on the street. Secure business computer disposal in Atlanta, GA isn't an expense—it's essential risk management.
The Growing Challenge of E-Waste
Beyond data security, there is the staggering volume of electronic waste. As far back as 2007, the EPA reported that Americans discarded over 63 million computers annually—a figure that has only grown.
The environmental cost is equally significant. Manufacturing a single desktop computer requires over 530 pounds of fossil fuels and a ton of water. This reality makes responsible, secure recycling a critical component of modern corporate responsibility. You can learn more about our commitment to environmental stewardship at Atlanta Computer Recycling.
This is why partnering with a certified IT Asset Disposition (ITAD) expert is crucial. A professional service transforms this potential liability into a secure, documented, and responsible process, ensuring your data is destroyed, your company is compliant, and your environmental commitments are met.
Preparing Your IT Assets for Secure Pickup
Before scheduling a pickup, the most critical phase of a secure IT disposal project occurs within your facility. Proper preparation ensures a smooth process, eliminates security gaps, and maintains complete control and accountability from start to finish.
This internal process sets the stage for a clean, auditable handoff to your disposal partner.
Your First Move: A Rock-Solid Asset Inventory
It all begins with a detailed inventory of what you are decommissioning. A disorganized pile of equipment in a storage room is a security blind spot. The first step we advise our clients to take is creating a comprehensive inventory list.
This is more than a simple count; it's about creating a master document—the single source of truth for the entire disposition project. Without it, you have no way to verify that every asset was accounted for and properly sanitized or destroyed.
Your inventory must track the following for each device:
- Asset Tag Number: Your company's internal identifier.
- Serial Number: The manufacturer's unique identifier.
- Device Type: Be specific (e.g., Dell Latitude 7490 Laptop, HP EliteDesk 800 G4 Desktop).
- Condition: Note if it’s functional, non-functional, or damaged.
- Location: The last department or office where it was deployed.
This detailed manifest is your primary tool for accountability. It allows you to cross-reference your list against the final certificate of destruction, proving nothing was lost or overlooked.
This inventory list serves as your official record. Think of it as a manifest for a valuable shipment—you wouldn't dispatch a truck full of your company's products without one, so you must not dispatch a truck full of your company's data without one either.
Confirm Your Data is Safe and Sound
This step may seem obvious, but it is often rushed. Before any device is designated for disposal, you must be 100% certain that all critical data has been successfully migrated or backed up. More importantly, you must validate that the backup is functional.
Do not rely solely on a "backup complete" message from your software. Perform a test restore. Select several random files from the backup and confirm they can be opened and that the data is intact. The worst time to discover a corrupted backup is after the original hard drive has been shredded.
Once you have confirmed the data is secure, the device is officially cleared for sanitization. For businesses requiring logistical support, our commercial computer pickup services are designed to streamline this entire process.
Sort Your Assets for Their Final Destination
Not all retired technology is treated identically. Some newer machines may be suitable for refurbishment and resale, while older or damaged equipment is destined for physical destruction. Sorting assets beforehand saves significant time and ensures process integrity.
Establish distinct, clearly labeled areas or pallets in your consolidation zone:
- Wipe & Resell: For newer, functional equipment. These assets hold recoverable value and will be securely wiped according to NIST 800-88 standards while remaining physically intact.
- Physical Destruction: For older, broken, or non-functional devices. This is also the designated stream for any drives containing highly sensitive intellectual property or data that corporate policy dictates must be physically destroyed.
This simple organizational step places you in full control. It provides clear instructions to your vendor, leaving no room for error. When our team arrives, we can operate with maximum efficiency, ensuring a flawless secure business computer disposal Atlanta GA workflow from the moment we enter your facility.
Data Wiping vs. Physical Shredding
Once your IT assets are inventoried and prepared, you must decide on the method of data destruction. For Atlanta businesses, this decision is central to protecting your company, your clients, and your reputation.
You have two primary options: software-based data wiping or complete physical shredding. The appropriate choice depends on your security policies, hardware age, and whether you aim to recover value from the equipment. It is a strategic decision that directly impacts both data security and your bottom line.
Understanding Data Wiping Standards
Data wiping, or data sanitization, is a software-driven process that overwrites every sector of a hard drive with random data, rendering the original information forensically unrecoverable. Critically, the drive itself remains functional.
This method must adhere to strict, verifiable standards. The two most recognized are:
- DoD 5220.22-M: The long-standing Department of Defense standard, which utilizes a 3-pass overwrite method trusted for decades.
- NIST 800-88: The current gold standard from the National Institute of Standards and Technology. It offers a comprehensive framework with "Clear," "Purge," and "Destroy" levels to meet specific security needs.
The primary advantage of wiping is hardware preservation. If your company is upgrading a fleet of recent-model servers or laptops, wiping allows that equipment to be safely resold. This recovers value that can offset the cost of your IT refresh project.
When Physical Shredding Is the Only Answer
In some cases, overwriting data is insufficient—absolute physical obliteration is required. Physical shredding achieves this by feeding hard drives, SSDs, backup tapes, and other media into an industrial shredder that grinds them into small, unsortable fragments.
This is a brute-force method that offers the ultimate guarantee that your data is gone forever.
Shredding is the mandatory choice in many scenarios. A healthcare provider retiring systems with patient records, for example, will almost always opt for shredding to eliminate any possibility of liability. It is also the only viable option for old or damaged hard drives that cannot be powered on for wiping.
When a drive is physically shredded, the chance of data recovery is zero. This method provides total peace of mind and is often required by corporate policy for devices that stored top-tier intellectual property or sensitive PII.
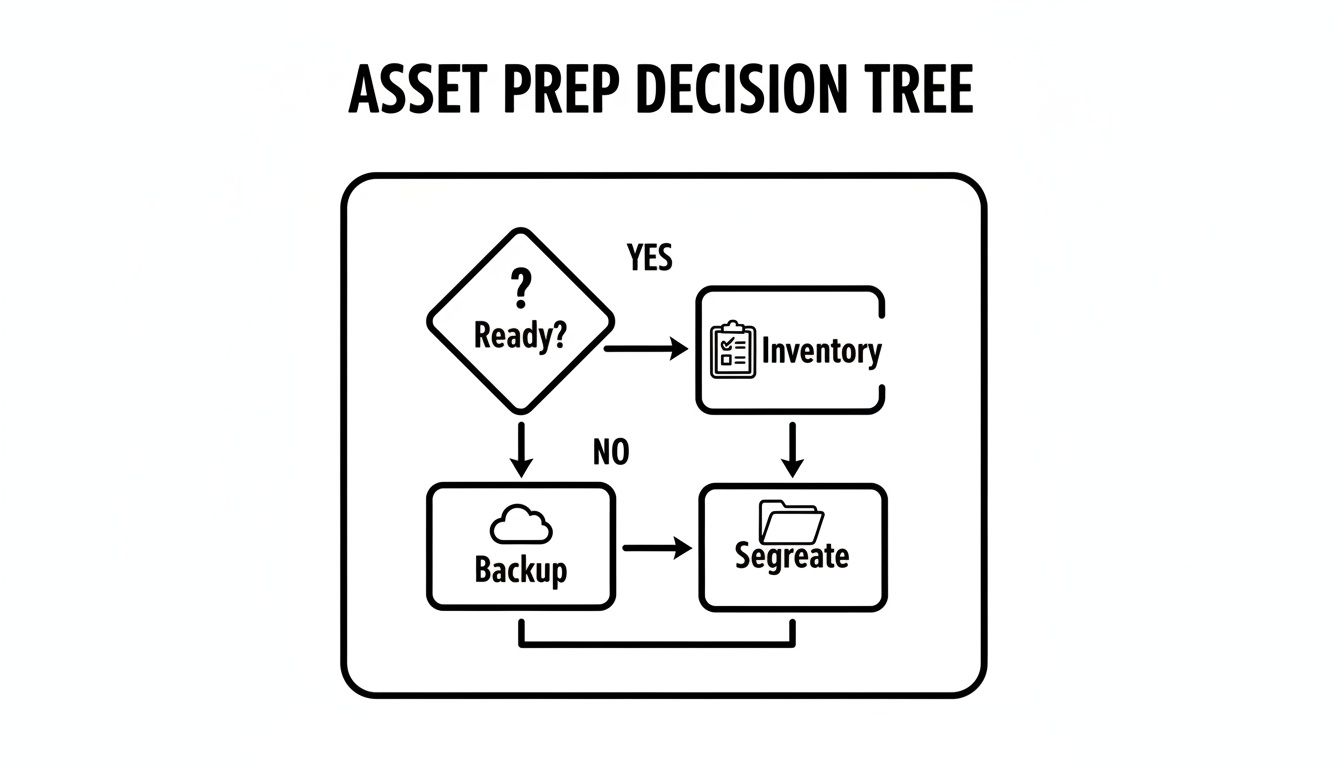
This flowchart illustrates how asset preparation leads to the wiping vs. shredding decision.
As shown, once backups are verified, you segregate assets into two streams: those destined for reuse (via wiping) and those designated for total destruction.
Choosing Your Data Destruction Method
Which method is right for your Atlanta business? The decision requires balancing security, compliance, and financial considerations.
| Factor | Data Wiping (e.g., NIST 800-88 Purge) | Physical Shredding |
|---|---|---|
| Security Level | High. Certified to make data forensically unrecoverable. | Absolute. The drive is physically destroyed, making recovery impossible. |
| Best For | Functional, newer equipment with resale or redeployment value. | Damaged, non-functional, or obsolete drives. Devices with highly sensitive data. |
| Asset Value | Preserves the hardware, allowing for remarketing and value recovery. | Destroys the hardware, eliminating any potential resale value. |
| Compliance | Meets requirements for HIPAA, SOX, and GLBA when certified. | Meets and often exceeds all major compliance requirements. |
| Verification | A digital certificate is generated, proving the wipe was successful. | A Certificate of Destruction is issued, confirming physical destruction. |
Ultimately, both paths lead to secure data destruction. The key is applying the right method to the right asset based on a clear corporate policy.
Making the Right Choice for Your Atlanta Business
Many of our corporate clients in the Atlanta area use a hybrid approach. Newer laptops and servers are wiped and remarketed to recover value, while older drives or those from the legal and finance departments are sent directly to the shredder. A professional ITAD partner can help you implement this strategy on an asset-by-asset basis.
The greatest risk is inaction. Data breaches from retired hard drives are a persistent threat, but our certified processes at Atlanta Computer Recycling eliminate 100% of that risk. We provide an unbreakable chain-of-custody from the moment we take possession of your equipment to the final certificate of destruction, whether you choose wiping or shredding.
For a more technical overview of the destruction process, please check out our guide on how to destroy old hard drives.
Meeting Compliance and Corporate Responsibility Mandates
For Atlanta businesses, disposing of old computers is about more than logistics; it's a matter of legal obligation and corporate responsibility. Failure to meet today's compliance and environmental standards exposes your company to heavy fines, legal action, and significant reputational damage.
Viewing IT asset disposition as a core part of your risk management strategy demonstrates to clients, partners, and regulators that you are serious about data protection and environmental stewardship.
Untangling the Complex Web of Compliance
Several key federal and industry regulations are not suggestions—they are legally binding rules that dictate how businesses must protect data, even on devices headed for disposal.
Every Atlanta business leader should be aware of these key regulations:
- HIPAA (Health Insurance Portability and Accountability Act): For any organization handling Protected Health Information (PHI), HIPAA mandates that data be rendered completely unrecoverable upon media disposal.
- SOX (Sarbanes-Oxley Act): Publicly traded companies must comply with SOX, which governs financial records. Improper disposal of computers with financial data can lead to audit failures and severe legal penalties.
- GLBA (Gramm-Leach-Bliley Act): This applies to financial institutions like banks, investment firms, and insurance companies. GLBA demands the protection of consumer financial data, making secure destruction an essential compliance task.
A Certificate of Destruction is your absolute proof in an audit. It’s the official, legally defensible document showing you took every required step to destroy sensitive data and meet your compliance obligations. Without it, you cannot verify your due diligence.
The Power of Documentation for Proving Due Diligence
How do you prove compliance with these strict regulations? The answer is meticulous documentation. A certified disposal partner provides an unbroken audit trail that protects your business from the moment your equipment leaves your premises.
This documentation must include a Certificate of Destruction. It is a formal statement that your media was destroyed according to specific, recognized standards. Equally important is a detailed chain-of-custody report, which provides a serialized log tracking every asset from pickup to final destruction. This documentation is your ultimate legal defense.
Corporate Responsibility and Atlanta's Push for Sustainability
Beyond legal requirements, your electronics disposal policy reflects your company's values. Committing to a zero-landfill policy aligns your brand with corporate social responsibility (CSR) and supports Atlanta's broader goals for a sustainable future. This is not just good ethics—it's smart business.
Partnering with a vendor holding certifications like R2 (Responsible Recycling) is essential. The R2 standard ensures your old equipment is managed in an environmentally sound manner, prioritizing reuse and resource recovery over landfilling. By choosing a certified partner, you participate in the circular economy. Explore our approach to environmentally responsible electronics recycling in Atlanta GA.
These sustainable practices are a direct response to the global e-waste crisis, which generates up to 60 million tons of discarded electronics annually. By choosing certified recycling, Atlanta's corporations, healthcare systems, and public agencies can divert tons of equipment from landfills and demonstrate leadership in sustainability.
How to Choose the Right ITAD Partner in Atlanta
Selecting a vendor for your company’s retired IT assets is a critical decision. A strong partner acts as an extension of your IT and security teams, while an unqualified one exposes your business to significant risk.
Not all e-waste recyclers are equipped to handle the rigorous demands of secure business computer disposal Atlanta GA companies require. You need a certified IT Asset Disposition (ITAD) partner, not a scrap hauler. This means asking detailed questions that go beyond price to verify their capability to protect you from data breaches and compliance failures.
Putting Their Security and Data Destruction to the Test
Data security is paramount. A prospective partner should welcome tough questions about their processes and provide confident, detailed answers. Vague responses are a major red flag.
Begin by probing the fundamentals of their data destruction methods:
- What data wiping standards do you follow? Demand specifics like “NIST 800-88 Purge” or “DoD 5220.22-M 3-pass.” An answer like “we wipe everything” is unacceptable.
- Can you perform on-site hard drive shredding? For your most sensitive data, witnessing the physical destruction of drives at your facility provides the highest level of assurance. This is a key service differentiator.
- How do you sanitize solid-state drives (SSDs)? Sanitizing an SSD is different from a traditional hard drive. A competent partner will understand this and explain their specific process for either wiping or shredding flash-based media.
Their ability to answer these questions confidently and accurately is a direct reflection of their expertise. Hesitation or a lack of detail is a clear indicator that they cannot be trusted with your data.
You are entrusting a vendor with the keys to your company's most sensitive information. You need to know not just that they will secure it, but precisely how they will secure it, who has access, and what protocols are in place at every step.
Verifying Logistics and Chain of Custody
A data breach can happen in transit. A secure chain of custody is non-negotiable and begins the moment a vendor arrives at your location.
Ask them to walk you through their entire logistical process:
- What does your on-site pickup process look like? Professionals should arrive in uniform, operate branded vehicles, and manage all packing and palletizing. A disorganized pickup indicates a weak security posture.
- Are your vehicles secured and GPS-tracked? Real-time monitoring of assets during transit is a crucial security feature that any serious ITAD provider must offer.
- How do you track my equipment? They must describe a detailed, serialized asset tracking system that links each item from your initial inventory to its final certificate of destruction.
For Atlanta businesses evaluating their options, understanding the differences between various e-waste disposal companies is a crucial part of your due diligence.
Confirming Compliance and Environmental Standards
Finally, a true partner must provide verifiable proof of their commitment to regulatory and environmental standards. This is about protecting your organization from legal and financial penalties.
Focus your final vetting on certifications and documentation:
- Will I receive a serialized Certificate of Destruction? The only acceptable answer is an unequivocal "yes." This document is your legal proof of compliance.
- What environmental certifications do you hold? Look for leading industry standards like R2 (Responsible Recycling) certification. This is your assurance that they adhere to the highest standards for secure and environmentally sound electronics recycling.
- What is your landfill policy? A reputable ITAD partner will have a strict zero-landfill policy, guaranteeing that all materials are recycled or repurposed, never dumped.
By asking these pointed questions, you empower your organization to select a genuine enterprise security partner who can fully protect your Atlanta business, not just a basic recycler.
Frequently Asked Questions About Computer Disposal
When managing the disposal of corporate electronics, IT managers and business owners across Atlanta often have the same critical questions. Addressing these concerns is essential for a secure and compliant process.
What Types of Equipment Can You Handle?
Your IT Asset Disposition (ITAD) partner should provide a single-source solution for all your retired electronics, not just desktops. This ensures a consistent and secure process under a single chain of custody.
A comprehensive provider should manage the full spectrum of business electronics, including:
- Servers and data center infrastructure (racks, PDUs)
- Networking hardware like switches, routers, and firewalls
- Laptops, desktops, and workstations
- Loose hard disk drives (HDDs) and solid-state drives (SSDs)
- Monitors, printers, and other peripherals
- Company-owned mobile phones and tablets
This all-inclusive approach streamlines logistics and ensures every data-bearing asset is accounted for within one secure, auditable process.
Is On-Site Data Shredding Really Necessary?
For the highest level of security and risk mitigation, yes. On-site shredding allows your team to witness the physical destruction of hard drives at your facility, ensuring data-bearing media never leaves your premises intact.
This completely eliminates the risk of a data breach during transit.
For many Atlanta businesses in regulated industries like healthcare, finance, or government contracting, this is a compliance mandate. If your company handles data governed by HIPAA, SOX, or GLBA, on-site shredding is the most direct way to prove you have met your data destruction obligations.
By witnessing the shredding process, you gain undeniable proof that sensitive information has been irretrievably destroyed. It’s the highest level of assurance for any secure business computer disposal in Atlanta GA.
What Documentation Should I Expect to Receive?
Your documentation is your proof of compliance. In the event of an audit, it is your first and most important line of defense, demonstrating that you performed the necessary due diligence.
A professional ITAD partner must provide two critical documents upon project completion:
First, a serialized Certificate of Destruction. This formal document confirms that your data was destroyed in accordance with recognized standards. Second, a detailed chain-of-custody report, which tracks your assets from your facility to their final disposition. You can review a sample to understand why a Certificate of Destruction is so important for your records.
How Much Does Secure Computer Disposal Cost?
The cost of secure disposal varies based on the volume and type of equipment, pickup logistics, and the services required (e.g., on-site shredding).
However, a key advantage of working with a true ITAD partner is the potential for value recovery.
Many of your retired assets, particularly newer equipment, may retain significant market value. We can often offset or even completely cover your disposal costs by remarketing these functional assets after certified data sanitization. Always request a detailed quote that breaks down any fees and clearly outlines the revenue-sharing model for resold equipment.
Your company's retired IT equipment should not be a source of risk. For a secure, compliant, and responsible solution for your retired electronics in the Atlanta area, trust Atlanta Computer Recycling. We provide end-to-end ITAD services designed to protect your data, your reputation, and your bottom line. Contact us today to schedule a consultation at https://atlantacomputerrecycling.com.