Boost Efficiency with IT Lifecycle Management Atlanta GA

For any business in Atlanta, IT lifecycle management isn't just an item on a tech to-do list. It’s a core business strategy that has a real impact on your bottom line, day-to-day efficiency, and data security. It provides a strategic framework for managing every piece of technology your company owns—from employee laptops to critical data center servers—from the moment of procurement to the day of its final disposition.
Simply put, a formal program is the most effective way for Atlanta businesses to gain control of spiraling technology costs and mitigate significant compliance risks.
Why IT Lifecycle Management Is a Business Strategy
Too many companies treat their IT hardware as a recurring operational expense. They purchase laptops reactively, replace servers only when they fail, and allow retired equipment to accumulate in storage closets. This reactive, "deal with it later" approach is a formula for hidden costs, operational inefficiencies, and serious security vulnerabilities.
A formal IT Lifecycle Management (ITLM) program is designed to stop that destructive cycle before it starts.
Consider your company’s technology assets like a fleet of commercial vehicles. You wouldn’t acquire them at random, skip routine maintenance, and then abandon them when they become obsolete. Of course not. You would implement a strategy for acquiring, maintaining, and eventually divesting them to maximize value and minimize risk. ITLM applies that same strategic discipline to your computers, servers, and network infrastructure.
The Four Phases of IT Lifecycle Management
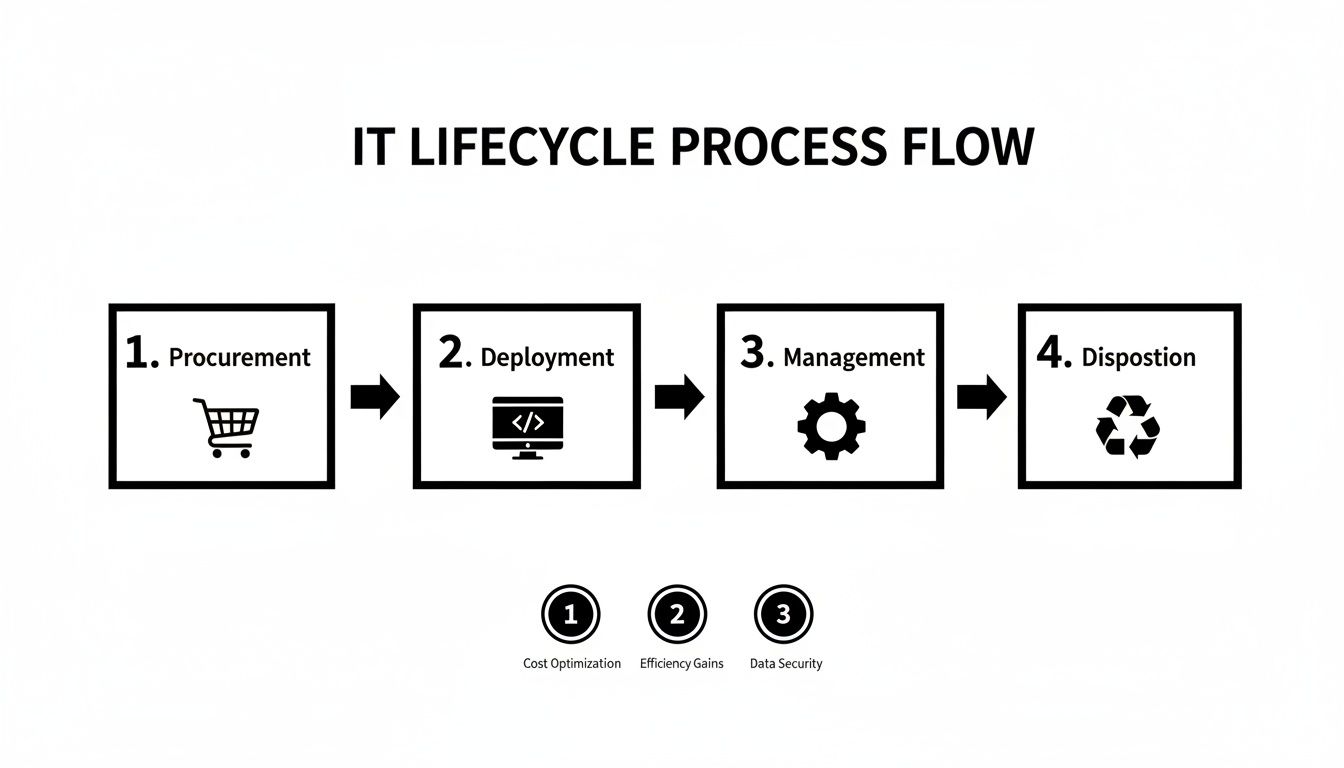
A well-designed ITLM program breaks the process down into four clear phases, each with its own goals and activities. This structure is what transforms your hardware from a simple expense into a strategic asset you can manage for maximum return on investment.
The table below provides a high-level overview of this framework.
| Phase | Key Activities | Primary Goal |
|---|---|---|
| Procurement | Needs analysis, vendor negotiation, purchasing, and establishing standards. | Acquire the right technology at the best possible price and terms. |
| Deployment | Asset tagging, software installation, configuration, and user setup. | Integrate new assets into the production environment with minimal disruption. |
| Management | Maintenance, software updates, security monitoring, and user support. | Maximize the asset's performance, security, and useful life. |
| Disposition | Data destruction, asset retirement, remarketing, and certified recycling. | Securely retire assets, protect data, and recover any remaining value. |
Following these four phases in a continuous loop creates a predictable, repeatable system for controlling costs and protecting your business.
When you begin viewing your technology through this lifecycle lens, your organization can finally shift from a reactive posture to a proactive one. That shift is absolutely critical for preventing data breaches, maintaining regulatory compliance, and optimizing your technology budget.
The Growing Importance of Secure Disposition
The final phase, IT Asset Disposition (ITAD), has become a massive economic driver, which underscores its strategic importance. The global ITAD market is projected to be worth as much as $99.82 billion by 2035.
North America is a mature market in this space, expected to account for up to 42.5% of global ITAD revenue in 2025. For an Atlanta-based organization, this regional strength means you have access to certified vendors and proven processes for meeting strict data security and environmental regulations. You can find more details on what's fueling this growth in the full market research report.
Ultimately, a proactive ITLM strategy is about protecting your business. It ensures every device is purchased wisely, used effectively, and retired securely. It’s more than just good IT—it’s a fundamental component of a successful, resilient enterprise.
For more details on structuring your own program, our guide on IT asset management best practices is an excellent resource.
Optimizing Procurement and Deployment
Effective IT lifecycle management in Atlanta, GA, doesn't start when you power on a new device. It begins much earlier, during the procurement and deployment phases. This is your opportunity to build a solid foundation for the entire program's success, shifting from reactive, last-minute purchases to a strategic approach that delivers long-term value.
Stop thinking of procurement as merely a purchasing function. It's a strategic planning session. The goal isn’t simply to buy more computers; it’s to acquire assets that solve specific business problems, are easy to manage, and retain as much value as possible throughout their service life. A thoughtful procurement process prevents overspending and saves your IT department from managing a chaotic collection of disparate hardware.
Strategic Procurement for Atlanta Businesses
A smart procurement strategy is centered on analysis and standardization. Instead of allowing each department to purchase different models, standardizing on a few approved configurations can dramatically reduce management complexity and operational costs. When your IT team only has a few models to support, everything from troubleshooting and repairs to software deployment becomes faster and more efficient.
This structured approach breaks down into a few key actions:
- Needs Assessment: Collaborate with department heads to determine their actual performance requirements. The graphic designer running Adobe Creative Suite requires a different machine than the accountant working primarily in Excel.
- Standardization: Based on those needs, define a short list of standard laptop and desktop models for different roles. This streamlines the entire process—purchasing, imaging, and support.
- Refresh Cycle Planning: Establish a predictable refresh schedule (typically three to four years) for your hardware. This makes budgeting far more predictable and ensures employees have reliable equipment that enhances productivity.
By standardizing equipment, organizations can reduce IT support costs by up to 15%. This happens because technicians become true experts on a smaller set of devices, enabling them to resolve issues faster and simplify parts inventory.
The Power of Disposition-Aware Procurement
Here’s a powerful strategy many companies overlook: disposition-aware procurement. This is the practice of considering a device's end-of-life value at the moment of purchase. Certain brands and models are known to retain their value better on the secondary market, while some are far easier to securely wipe and refurbish.
Building this consideration into your process means you choose hardware based on its total cost of ownership (TCO), not just its initial sticker price. That foresight directly boosts the value you can recover when it's time for disposition. For a deeper dive on how to structure this, our guide to IT procurement best practices lays out the details.
Flawless Deployment from Day One
Once the new equipment arrives, the deployment phase begins. This is where your new hardware is formally integrated into your company’s IT ecosystem. A disorganized deployment leads to immediate productivity loss and creates "ghost assets"—devices that are in use but never properly tracked.
A successful deployment process ensures every single device is secure, functioning correctly, and accounted for from its first day in service.
Key Deployment Best Practices
- Asset Tagging: Every piece of hardware must receive a unique asset ID tag. This tag is the foundation of your entire inventory system, allowing you to track that device from cradle to grave.
- Imaging and Configuration: Use a standard software image to install the operating system, company applications, and security policies. This ensures every machine is consistent and saves your team countless hours of manual setup.
- Inventory Integration: As each device is assigned to an employee, its asset tag, user assignment, and configuration details must be entered directly into your central IT asset management (ITAM) system. This real-time tracking is non-negotiable for managing the full lifecycle.
By locking down your procurement and deployment processes, Atlanta businesses can gain immediate control over their IT environment. This proactive start maximizes hardware performance, simplifies day-to-day management, and sets the stage for the highest possible value recovery down the road.
The Critical Role of IT Asset Disposition
It's easy to focus on the acquisition of new technology, but the management of retired equipment is just as critical—and often, far more dangerous for your business. The final stage of the IT lifecycle, IT Asset Disposition (ITAD), is frequently the most overlooked. This isn't just about clearing out a storage closet; it's a highly specialized process for retiring technology securely and in full compliance.
Mishandling this phase can result in crippling data breaches, steep compliance fines, and environmental penalties that can tarnish your company's hard-earned reputation in the competitive Atlanta market. The risks are simply too high to ignore.
Consider the implications: a single misplaced hard drive could contain sensitive customer data, employee PII, or company trade secrets. That one mistake can trigger a regulatory nightmare and expose your organization to immense liability. This is where a professional IT lifecycle management Atlanta GA program transforms a high-risk liability into a secure, documented, and worry-free final step.
More Than Just Disposing of Old Tech
Viewing ITAD as simple "disposal" is a significant misstep. A modern, professional ITAD program is a multi-layered strategy designed to protect your organization from every possible angle. It’s about systematically dismantling the risks tied to retired hardware while recovering any remaining financial value.
A solid ITAD strategy always includes these core components:
- Secure Logistics: This involves professional handling, packing, and tracked transportation of assets from your office to a secure processing facility, all under a documented chain of custody.
- Certified Data Destruction: Employing methods that guarantee data is 100% unrecoverable, from software-based wiping that meets government standards to physical shredding.
- Asset Remarketing: Identifying functional equipment that can be refurbished and sold on the secondary market, generating a financial return to offset the costs of your new technology.
- Responsible E-Waste Recycling: Ensuring all non-reusable materials and hazardous components are processed in an environmentally compliant manner by a certified recycler.
Each of these steps works in concert to build a defensive shield around your company during this vulnerable final phase.
The Final Word on Data: Wiping vs. Shredding
Data destruction is the absolute cornerstone of any legitimate ITAD service. There are two primary methods, and choosing the right one is essential for meeting compliance standards and guaranteeing total data security.
Data Wiping (Sanitization): This software-based approach overwrites the entire hard drive with random data, usually in several passes. The DoD 5220.22-M 3-pass method is a common standard that renders the original data forensically unrecoverable. This is the ideal solution for newer, functional drives that have resale value, as it preserves the physical hardware.
Physical Shredding: For older drives, non-functional hardware, or devices containing extremely sensitive data, nothing provides greater assurance than physical destruction. The hard drives are fed into powerful industrial shredders that tear them into small, irreparable metal fragments. This method offers undeniable proof that the data can never be accessed again.
A professional ITAD partner provides a Certificate of Data Destruction for every single drive they process, whether wiped or shredded. This document, which lists each drive by serial number, is your auditable proof of due diligence and compliance.
Why You Need an Atlanta ITAD Partner
For any organization in the Atlanta area, partnering with a local ITAD expert is the single most effective way to manage end-of-life assets. A dedicated partner takes the operational burden—and the liability—off your team's shoulders. They bring the specialized equipment, certified processes, and critical documentation needed to make your disposition program airtight.
They handle the complex logistics, perform certified data destruction, and navigate the maze of environmental regulations for you. This frees up your internal IT team to focus on their core mission, giving you peace of mind that your retired assets and sensitive data are completely protected. By outsourcing this critical function to a specialist, you gain an auditable trail that proves your commitment to security and compliance. To get a better sense of what this entails, you can learn more about what IT asset disposition involves and how a structured program can benefit your business.
Navigating Atlanta's Compliance and Data Security Rules
For any Atlanta business, IT lifecycle management isn't just about efficiency—it's a legal and security imperative. The final disposal stage is where your organization is most vulnerable. Allowing an old laptop to leave your premises without certified data destruction is equivalent to leaving unlocked filing cabinets full of sensitive corporate data in a public recycling bin. It’s a risk no business can afford to take.
Atlanta companies must navigate a complex web of data privacy laws. These are not abstract theories; they are strict regulations with severe penalties for non-compliance, including massive fines and irreversible damage to your corporate reputation. A solid IT lifecycle management Atlanta GA strategy turns this legal complexity into a clear, actionable plan for asset disposal.
Key Regulations Affecting Atlanta Businesses
While many laws apply, a few are especially critical for businesses operating in Atlanta—particularly those in healthcare, finance, and education. Understanding these regulations is the first step toward building a bulletproof disposal program.
- HIPAA (Health Insurance Portability and Accountability Act): This is non-negotiable for any entity handling health information. HIPAA demands auditable proof that Protected Health Information (PHI) is rendered completely unreadable and indecipherable before an asset is disposed of. A simple factory reset is grossly insufficient.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions, from local banks to investment firms, are bound by GLBA. It requires the protection of "nonpublic personal information" (NPI) and mandates the secure disposal of any customer records, including those on digital devices.
- FERPA (Family Educational Rights and Privacy Act): Schools and universities must protect the privacy of student education records. This applies to any device that ever stored student data, demanding secure data destruction before it can be recycled or resold.
The thread connecting all these regulations is accountability. It’s not enough to just claim you destroyed the data; you need documented, auditable proof that it was handled correctly. This is where a professional ITAD partner becomes absolutely essential.
Turning Compliance Into Action
Meeting these standards isn't just about good intentions; it requires specific, certified data destruction methods. A partner who is fluent in these regulations will provide solutions that match the sensitivity of your data, protecting you from liability.
The entire market is shifting in this direction. Regulatory compliance and environmental responsibility are now the top drivers for IT asset disposition services, compelling organizations to formalize their disposal processes. As hybrid work and cloud computing add layers of complexity, the need for specialized ITAD providers to manage a wide range of equipment across different locations has never been greater.
For Atlanta’s healthcare, education, and government sectors, these rules are absolute. A hospital system retiring laptops needs verifiable proof of HIPAA-compliant data destruction. A university managing thousands of computers requires certified disposal to meet federal e-waste standards.
Data Destruction Methods For Full Compliance
To ensure your organization is fully protected from data breaches and regulatory fines, your ITAD partner must offer a clear menu of data destruction services. The right choice depends on the asset's type, its age, and the sensitivity of the data it once held.
This table breaks down the most common methods and their best applications.
Data Security Methods Comparison
| Method | Process | Best For | Compliance Level |
|---|---|---|---|
| DoD 5220.22-M Wipe | Software-based overwriting of the entire drive with random data in multiple passes. | Newer, functional hard drives intended for resale or reuse. | High (HIPAA, GLBA) |
| NIST 800-88 Purge | A more advanced software or hardware-based method to sanitize media. | Devices storing highly sensitive information that may be remarketed. | Very High (All major regulations) |
| Physical Shredding | The hard drive is physically destroyed, torn into small metal fragments. | End-of-life, damaged, or non-functional drives, or for maximum security. | Absolute (Exceeds all standards) |
Each method provides a different level of security, and choosing the right one is key to both compliance and cost-effectiveness.
Ultimately, choosing a vendor that lives and breathes these rules is critical. Your partner in IT lifecycle management in Atlanta, GA, must deliver impenetrable security and auditable compliance. For more details on this, you can read our guide on achieving compliant IT disposal in Atlanta, GA.
Beyond just getting rid of old equipment, responsible ITAD is also about sustainability. Modern companies are actively contributing to a zero e-waste world through smart recycling and reuse programs. It’s a commitment that protects both your data and the environment.
How to Choose the Right ITAD Partner in Atlanta
Selecting the right local IT Asset Disposition (ITAD) vendor is one of the most critical decisions in your entire lifecycle management plan. This isn't just about finding the lowest price—it's about engaging a true partner you can trust to protect your company's sensitive data and ensure regulatory compliance.
The partner you choose becomes a direct extension of your security posture. For any Atlanta organization serious about IT lifecycle management, vetting potential vendors is a non-negotiable step. A single misstep by a subpar vendor could easily lead to a disastrous data breach or steep environmental fines. To protect your business, you need a clear framework for asking the right questions and demanding the right credentials.
Verifying Certifications and Chain of Custody
The first filter for any potential ITAD partner should be their industry certifications. These are not merely logos for a website; they are hard-earned proof that a vendor adheres to rigorous, third-party audited standards for data security, environmental safety, and worker protection.
Do not just take their word for it. Here are the essential credentials to demand:
- R2 (Responsible Recycling): This certification ensures the vendor follows established best practices for electronics recycling. An R2-certified partner guarantees your e-waste will not be improperly disposed of in a landfill.
- e-Stewards: Known for its exceptionally strict standards, e-Stewards certification is the gold standard for preventing the export of hazardous electronic waste to developing nations. It represents the highest level of environmental and social responsibility.
Beyond certifications, you must insist on a clear and unbroken chain of custody. This is the documented paper trail that tracks every one of your assets from the moment they leave your facility to their final destruction or disposition. A reliable partner will provide serialized reports at every stage, giving you an auditable record for compliance purposes.
Scrutinizing Data Destruction and Reporting
Data destruction is the absolute heart of any secure ITAD service. You need a partner who offers methods that align with your specific security requirements, whether you're bound by HIPAA, GLBA, or other strict regulations.
Get into the details and ask potential vendors direct questions about their process:
- Do they offer both software-based data wiping (to standards like DoD 5220.22-M and NIST 800-88) and physical destruction like shredding?
- Can they perform these data destruction services on-site at your Atlanta office for maximum security?
- What does their Certificate of Data Destruction include? It must list every asset by serial number and state the exact method of destruction used.
A vague or evasive answer regarding data destruction is a major red flag. A trustworthy partner will be completely transparent about their methods and should have no problem providing sample documentation to prove their process is thorough and auditable.
Finally, consider the broader business value. Does the vendor offer value recovery by remarketing functional equipment? This can significantly offset the costs of your disposition program. Do they carry sufficient liability insurance to protect your business in a worst-case scenario?
Asking these tough questions upfront is the only way to confidently select a partner who delivers the comprehensive security your Atlanta business requires. To help you compare your options, our overview of local electronic waste disposal companies can provide additional context.
Answering Your IT Lifecycle Questions
Even with the most well-structured plan, questions inevitably arise. As Atlanta businesses implement formal IT asset management programs, a few key concerns frequently surface. Here are the answers to the questions we hear most often from a commercial perspective.
What Is The Biggest Mistake Companies Make With IT Asset Disposal?
The most common—and costly—mistake is treating IT Asset Disposition (ITAD) as an afterthought rather than a strategic function. It’s easy to focus on the procurement of new technology, but without a clear plan for retired equipment, businesses often end up stockpiling devices in an unsecured closet or, worse, handing them off to an uncertified recycler.
This reactive approach creates massive risks, opening the door to data breaches and steep fines for non-compliance.
Can My Business Recover Money From Old IT Equipment?
Absolutely. This process is known as value recovery or asset remarketing, and it's a critical component of a financially sound ITAD strategy. A professional partner will assess your retired hardware to identify assets that retain market value.
Equipment such as recent-model laptops, servers, and networking gear can often be refurbished and resold. The revenue generated is returned to your business, helping to offset the capital expenditure for new equipment.
A key part of a successful IT lifecycle management Atlanta GA program is maximizing this return. Choosing hardware during procurement that holds its value and partnering with a vendor skilled in remarketing can turn retired assets into a revenue stream.
What Documentation Should I Expect From An ITAD Provider?
Your business must receive detailed, itemized reports. These documents are your official record and auditable proof of compliance, making them completely non-negotiable for protecting your business from liability.
At a minimum, you need to demand these two certificates for every batch of assets:
- Certificate of Data Destruction: This document lists every single asset by its serial number and confirms the exact method used to destroy the data, whether through software wiping or physical shredding.
- Certificate of Recycling: This is your proof that all non-reusable assets were processed and handled in accordance with all local, state, and federal environmental regulations.
Ready to build a secure, compliant, and cost-effective IT lifecycle program? Atlanta Computer Recycling provides end-to-end ITAD services for businesses across the metro area. From secure logistics to certified data destruction and value recovery, we handle every step.
Contact us today to schedule your free consultation at AtlantaComputerRecycling.com