Your Guide to Secure IT Disposal in Atlanta for Commercial Clients
Retiring old IT equipment is more than a logistical task for your Atlanta business—it’s a critical security and financial operation. A single discarded server or laptop still holding sensitive client data can quickly become a significant liability, impacting your bottom line and reputation.
This guide provides a practical framework for what secure IT disposal Atlanta businesses need to implement to protect their operations, data, and compliance standing.
The High Stakes of IT Asset Disposal for Atlanta Businesses
Whether you’re a Midtown law firm, a Buckhead financial services company, or a technology enterprise, managing end-of-life electronics is a high-stakes responsibility. Failing to implement a professional process exposes your business to tangible risks that extend far beyond a cluttered storage room.
A single improperly discarded hard drive can trigger a cascade of negative outcomes.
The stakes have never been higher. Regulatory pressure from frameworks like HIPAA, GLBA, and GDPR is mounting, while sophisticated data recovery techniques are now widely accessible. This isn't a hypothetical problem; it’s a direct threat with serious financial and reputational costs for Georgia-based companies.
Beyond the Storage Closet: Commercial Risks
Improper disposal is a direct threat to your business continuity and financial health. Consider the specific vulnerabilities your Atlanta-based company faces:
- Steep Regulatory Fines: Non-compliance with data privacy laws can result in crippling financial penalties that directly impact profitability.
- Irreversible Brand Damage: A public data breach traced back to a retired asset can destroy customer trust and market share built over years.
- Operational Disruption: Managing a data breach consumes significant resources, diverting key personnel from revenue-generating activities and disrupting core business functions.
Market data validates this concern. The global e-waste management market is projected to jump from USD 70 billion in 2024 to USD 81.27 billion in 2025, a surge driven by the increasing threat of ransomware and stricter privacy regulations. What was once an operational afterthought is now a board-level priority.
Your Initial IT Disposal Risk Assessment Checklist
Before initiating an IT disposal project, it's essential to assess your current risk exposure. This checklist is designed for Atlanta's IT and operations managers to gain a clear snapshot of their organization's posture.
| Risk Area | High-Risk Indicator | First Mitigation Step |
|---|---|---|
| Data Security | No formal, documented policy for wiping or destroying data on retired devices. | Implement a mandatory, documented data destruction policy for all retired assets. |
| Compliance | Unsure if current disposal methods meet HIPAA, PCI, or other industry requirements. | Review all relevant regulations and align your disposal process with the strictest applicable standards. |
| Chain of Custody | Assets leave the premises without a documented transfer of liability. | Engage a certified vendor who provides a detailed, serialized chain-of-custody report for auditable proof. |
| Vendor Vetting | Using a general e-waste recycler without data security certifications (e.g., NAID AAA). | Vet and select a partner specializing in secure ITAD that holds relevant certifications like R2v3. |
| Environmental | Unsure of the final destination of retired equipment (e.g., potential for landfill). | Partner with a certified e-Stewards or R2 recycler to guarantee responsible and compliant processing. |
This assessment isn't about creating fear; it's about strategic preparation. Proactive risk mitigation prevents significant financial and operational disruption later.
An effective ITAD strategy is a core component of modern risk management. It transforms a high-risk necessity into a streamlined, secure, and compliant process that protects your most valuable asset: your data.
To truly mitigate these risks, a comprehensive approach is necessary. This includes integrating essential data loss prevention techniques long before a device is scheduled for retirement. For large-scale projects, understanding the detailed steps of a professional data center decommissioning process is critical.
Mapping Your Assets For Secure Disposition
You cannot secure what you cannot track. Before a single device is decommissioned, your Atlanta business must establish a precise inventory. This is not just an administrative count; it is the creation of a strategic manifest that maps the risk and potential value recovery associated with every piece of equipment.
A detailed inventory is the foundation of a defensible secure IT disposal Atlanta strategy. Without it, your company is exposed to a data breach from a forgotten device. We’ve all seen it—an old server in a back closet or a box of outdated company phones. Each one represents a potential liability.
Beyond The Basic Count
A functional inventory for IT disposal is more than a list of makes and models. The objective is to build a data-rich catalog that informs every subsequent decision, from the method of data destruction to the potential for value recovery. A best practice is to consult with department heads to identify assets that may not be on the official IT roster.
For every asset, your inventory must capture these key data points:
- Asset Type: Server, laptop, mobile phone, network switch, etc.
- Serial Number/Asset Tag: The non-negotiable unique identifier for tracking.
- Physical Location: Department, office, or data center rack.
- Current User (if applicable): The last assigned employee or function.
With this framework established, you can layer in the context required for strategic disposition: risk and value.
Tagging For Risk And Value
With the baseline inventory complete, it's time to classify assets based on the data they contain and their physical condition. This is the most critical step in the process, as it dictates the required handling protocol for each device.
Data Sensitivity Level:
This classification should be your top priority. Categorize the type of data each device may contain.
- Level 1 (Low): General internal communications, non-sensitive project files.
- Level 2 (Medium): Proprietary business information, internal financial reports, or employee PII.
- Level 3 (High): Customer financial data, protected health information (PHI), or core intellectual property.
A server from your finance department (Level 3) requires a fundamentally different disposal protocol than a conference room display (Level 1).
A detailed inventory isn't just an administrative task—it's your first line of defense. It transforms a pile of old electronics into a clear, manageable set of assets, each with a defined risk profile and a prescribed path for secure disposition.
Physical Condition and Potential Value:
Next, assess each device's physical state to determine its potential for remarketing and value recovery.
- Condition: Is it fully functional, requires minor repair, or is it non-operational?
- Age/Model: Is it a recent model with resale value or a legacy system?
- Potential Action: Tag the asset for Resale, Reuse (internal redeployment), or Recycle.
For example, a batch of two-year-old, functional MacBook Pros has significant resale value and should be slated for certified data wiping. Conversely, a ten-year-old server with a failed power supply is a candidate for physical shredding and recycling.
This methodical approach is the core of a strategic IT asset disposal program that balances robust security with financial optimization. By creating this detailed map, your Atlanta business can proceed with a clear, documented, and secure plan for every retired asset.
Choosing The Right Data Destruction Method
Once your inventory of retired IT assets is mapped, you face a critical decision point: selecting the appropriate data destruction method for each asset category. This is the core of any effective secure IT disposal Atlanta strategy, and there is no one-size-fits-all answer.
The method you choose directly impacts your security posture, your budget, and your ability to recover value from retired equipment. The two industry-standard methods are certified data wiping and physical destruction, each serving a distinct business purpose.
Certified Data Wiping For Value Recovery
Certified data wiping is a software-based method of data sanitization. It uses specialized software to systematically overwrite every sector of a hard drive or SSD with random, meaningless data. This process renders the original information forensically unrecoverable and adheres to strict standards like the DoD 5220.22-M 3-pass method, a trusted benchmark for data erasure.
When is data wiping the optimal choice?
Data wiping is the preferred method for newer, functional, and high-value equipment. If your Atlanta business is retiring a fleet of recent-model laptops, powerful servers, or enterprise-grade networking gear, wiping preserves the hardware's physical integrity. This enables the assets to be safely refurbished, resold, or redeployed, maximizing your return on investment (ROI).
For any organization looking to offset the costs of a technology refresh, certified data wiping is the key. It securely decouples the data from the hardware, turning a potential liability into a tangible financial asset without compromising security.
Physical Shredding For Absolute Destruction
While wiping is a sophisticated process, physical destruction is definitive. This method involves feeding hard drives, SSDs, backup tapes, and other storage media into industrial shredders that reduce them to small, mangled pieces of metal and plastic. No software, recovery tool, or forensic lab can reconstruct the data. It is irrevocably destroyed.
This brute-force approach is non-negotiable in several key scenarios:
- Older or Non-Functional Devices: If a hard drive is damaged, end-of-life, or has no resale value, shredding is the most direct and secure disposition path.
- Highly Regulated Industries: For an Atlanta healthcare provider managing PHI under HIPAA, or a law firm handling sensitive client records, physical destruction provides the highest level of assurance and is often a core compliance requirement.
- Company Policy Mandates: Many organizations have internal security policies demanding physical destruction for any device that has stored proprietary R&D, financial data, or critical intellectual property.
This is a zero-tolerance approach to risk. When the data is so sensitive that even a negligible chance of recovery is unacceptable, shredding is the only viable option. You can explore the technical specifications of our process in our guide to secure data destruction.
Data Wiping Vs. Physical Shredding: A Practical Comparison
Choosing between these methods is a strategic decision that balances security requirements, sustainability goals, and financial returns. This comparison is designed to help Atlanta businesses select the right service for the right assets.
| Decision Factor | Certified Data Wiping | Physical Shredding |
|---|---|---|
| Best For | Newer, functional assets with resale value (laptops, servers, enterprise SSDs). | Old, damaged, or non-functional hard drives; high-security media. |
| Primary Goal | Securely erase data while preserving the hardware for remarketing or reuse. | Completely and physically destroy the storage media, rendering data unrecoverable. |
| Security Level | Extremely high; meets NIST 800-88 and DoD standards for data sanitization. | Absolute; provides the highest possible level of data security with zero chance of recovery. |
| Compliance | Fully compliant for most regulations, including HIPAA, when documented properly. | Often preferred for the strictest compliance mandates due to its irrefutable finality. |
| Outcome | Assets can be resold, donated, or redeployed; generates ROI. | Shredded material is sent for responsible metals and electronics recycling. |
| Documentation | Provides a Certificate of Data Erasure with serialized asset details. | Provides a Certificate of Destruction, confirming the physical shredding of assets. |
Ultimately, a sophisticated ITAD strategy often employs a hybrid approach. The asset inventory you created serves as the guide: newer, valuable assets are wiped, while older, higher-risk devices are shredded. This ensures every piece of equipment is managed in the most secure, responsible, and financially sound manner.
How To Vet A Secure IT Disposal Vendor In Atlanta
Selecting the right local IT asset disposition (ITAD) vendor is the most critical decision in this entire process. A qualified partner acts as an extension of your IT and security teams, not just a pickup service. With numerous providers available, how do you differentiate true experts from basic scrap haulers?
Choosing a provider for secure IT disposal Atlanta businesses can trust requires a rigorous vetting process that prioritizes qualifications, from industry certifications to on-the-ground security protocols.
Look For The Right Certifications
Certifications are your first and most effective filter. They are independent, third-party audits confirming a vendor adheres to the highest industry standards for security, environmental practices, and operational excellence. Always request proof of certification.
The two most important certifications to look for are:
- R2v3 (Responsible Recycling): This comprehensive standard covers the entire asset lifecycle, ensuring vendors follow best practices for electronics recycling, data security, and worker health and safety.
- e-Stewards: Often considered the gold standard for environmental protection, this certification guarantees that no hazardous e-waste is exported to developing nations or disposed of in landfills.
A vendor holding one or both of these certifications has made a significant investment in proving their commitment to professional, compliant operations.
Scrutinize Their Security And Insurance
Once certifications are confirmed, perform due diligence on their security infrastructure and liability coverage. A professional ITAD partner will be transparent and should welcome detailed questions about their processes and facilities.
When vetting a vendor, it's critical to understand their commitment to security and compliance, which is often demonstrated through a practical SOC 2 compliance checklist. Ask pointed questions about their physical and personnel security:
Does their facility have 24/7 monitored security with controlled access and full camera surveillance? Do they conduct background checks on all employees who handle client assets? These are baseline requirements, not premium add-ons.
Equally important is their insurance coverage. Request their Certificate of Insurance and look specifically for policies covering data breaches, errors and omissions, and environmental liability. This coverage protects your business from financial risk in the event of an incident.
Verify Their Local Experience And Compliance Knowledge
Finally, you need a partner who understands the specific business environment in the Atlanta area. Ask for local client references, particularly from companies in your industry, whether it's healthcare, finance, or technology. A vendor with deep experience in HIPAA or GLBA compliance will already be equipped to handle your unique challenges. Our guide to the top electronic waste disposal companies is an excellent starting point for your research.
This focus on certified, knowledgeable partners is more critical than ever. The global electronics recycling market is growing at a staggering rate and is projected to hit USD 147.9 billion by 2035. This expansion brings increased regulatory scrutiny. For Atlanta businesses, schools, and hospitals, partnering with a certified recycler is essential to stay ahead of evolving compliance standards. A local partner with proven expertise ensures your ITAD program is not only compliant today but also prepared for future requirements.
Executing A Flawless Chain Of Custody
After vetting your vendor and selecting the appropriate data destruction methods, the focus shifts from planning to execution. At this stage, a flawless chain of custody is the most critical component of your secure IT disposal Atlanta strategy.
A chain of custody is the documented, unbroken trail proving your sensitive assets were handled securely from the moment they left your facility to their final destruction. Without it, you are operating on trust alone, leaving your organization exposed. A robust chain of custody provides auditable proof of due diligence, offering a solid defense in the event of a compliance audit.
This process transforms abstract security policies into concrete, verifiable actions. It is the difference between assuming your data was destroyed and knowing it was.
The Anatomy Of An Unbroken Chain
An effective chain of custody is not a single document but a series of documented steps, each building on the last to create a seamless security narrative from pickup to final disposition.
A professional process should include:
- On-Site Inventory Scan: The vendor’s technicians scan the serial number or asset tag of every device being collected. This manifest is reconciled against your inventory, creating an official transfer of liability.
- Secure, Sealed Transport: Assets are loaded into a secure, locked vehicle. For high-security projects, devices are placed into sealed, tamper-evident containers before being loaded.
- GPS Tracking and Monitored Transit: The vehicle is tracked via GPS from your location directly to the vendor's secure processing facility, with no unauthorized stops.
- Secure Facility Check-In: Upon arrival, the seals on the vehicle and any containers are inspected and verified. The assets are scanned again as they are formally received into the secure, access-controlled facility.
This systematic methodology eliminates ambiguity and risk. Every step is recorded, timestamped, and reconciled, ensuring no asset is lost or mishandled.
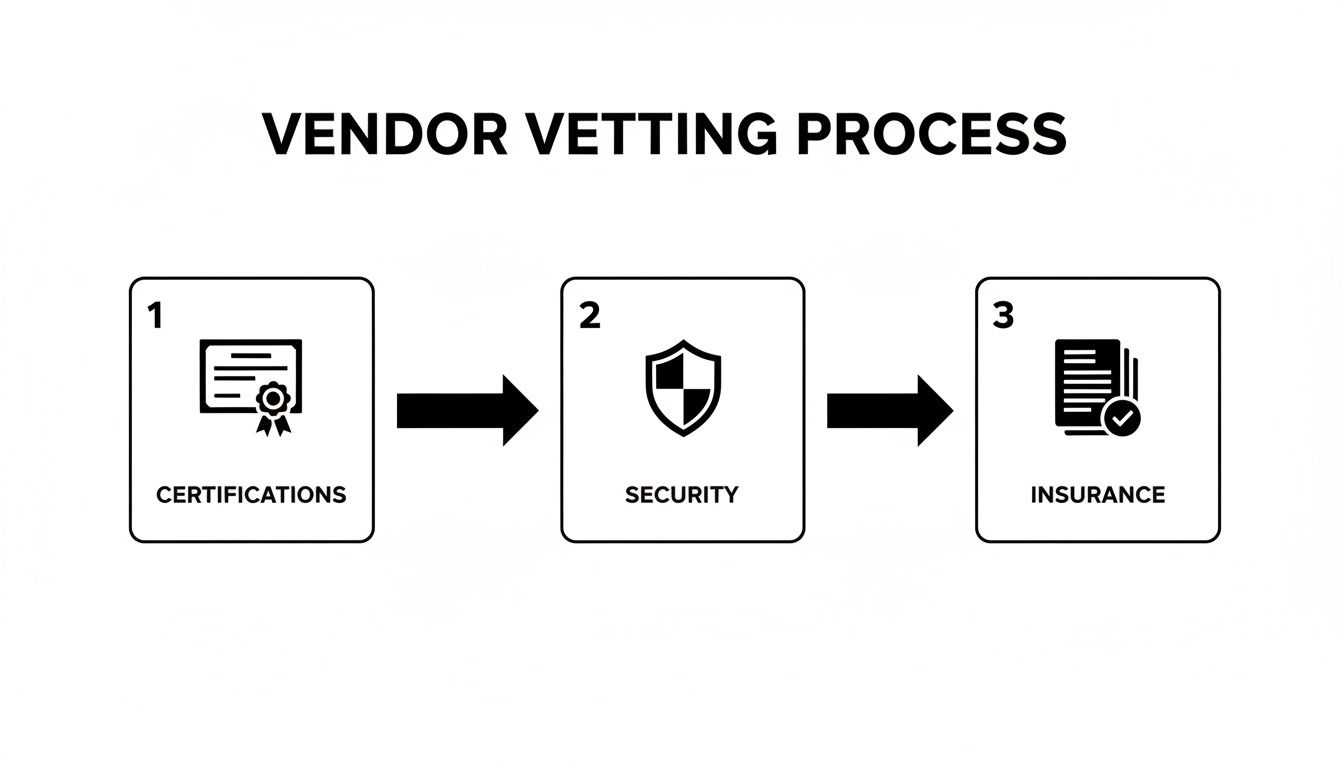
This flow chart highlights the key pillars to evaluate when vetting a vendor's security and processes.
From certifications to on-site security and proper insurance, a trustworthy chain of custody is built on this strong foundation.
Real-World Example: A Local Healthcare Clinic Pickup
Consider a healthcare clinic in Sandy Springs decommissioning 50 retired desktops containing Protected Health Information (PHI). For this client, an unbroken chain of custody is a strict HIPAA requirement.
The vendor arrives and scans each PC’s asset tag, generating a serialized pickup report signed by the clinic manager. The computers are loaded into locked bins sealed with uniquely numbered security tags. The GPS-tracked truck proceeds directly to the vendor’s metro Atlanta facility.
Upon arrival, the security seals are verified against the pickup report before being broken. The PCs are scanned again as they enter the destruction area. After the hard drives are physically shredded, the clinic receives the final, critical documentation.
The Certificate of Destruction isn't just a receipt. It's your legal, auditable proof that you fulfilled your duty of care. It should list the serial number of every single asset that was destroyed, linking back directly to the initial on-site inventory scan.
This final document closes the loop, confirming the date, location, and method of destruction, providing a clear, defensible record for any future compliance audit. You can learn more about what to look for in a valid Certificate of Destruction to ensure your records are airtight. This is the ultimate proof that your organization met its legal and ethical obligations.
Why a Proactive Disposal Strategy Isn't Just "Nice to Have"
Viewing secure IT disposal as a mere operational task is a significant strategic error. In the current business climate, it is a critical component of risk management and corporate responsibility. A proactive disposal strategy is no longer optional—it is essential for protecting your company's reputation, bottom line, and the customer trust you have worked hard to earn.
The practical steps outlined here—from a thorough inventory and strategic data destruction choices to a meticulous chain of custody—are the pillars of a modern ITAD program. It begins with a comprehensive understanding of your assets and culminates in a defensible process that withstands regulatory scrutiny.
It's About Protecting More Than Just Data
While data security is paramount, the broader objective is to protect the overall health of your business. A single data breach from a carelessly discarded asset can create cascading disruptions across your organization. The financial impact of fines and legal fees is only the beginning; the long-term damage to your brand and market position can be far more severe.
A well-planned strategy for secure IT disposal Atlanta businesses implement also serves as a powerful demonstration of corporate responsibility.
Consider this: the world generated a staggering 62 million tonnes of e-waste in 2022, but only 22.3% was properly collected and recycled. This growing environmental challenge underscores the importance of partnering with certified recyclers who ensure your retired assets do not contribute to the problem. You can dive deeper into the numbers in the latest global e-waste report.
Your Strategic Ally in Atlanta
For any organization in the Atlanta metropolitan area, engaging a local, certified expert is a distinct strategic advantage. A local partner understands Georgia's specific regulatory landscape and has direct experience helping businesses like yours navigate the complexities of compliance.
A proactive ITAD strategy transforms a potential liability into a controlled, documented process. It’s an investment in resilience, proving to clients, stakeholders, and regulators that you take data protection seriously at every stage of the asset lifecycle.
This is more than hiring a vendor; it is about gaining an ally committed to protecting your organization from preventable risks. They become an extension of your team, providing the expertise and infrastructure required to manage asset disposition securely, responsibly, and efficiently.
Ultimately, a proactive strategy ensures that when your technology's lifecycle ends, your company's security and reputation remain fully protected.
Answering Your Top Questions About IT Disposal in Atlanta
Even with a robust plan, questions inevitably arise when it's time to decommission corporate technology assets. Businesses across Atlanta frequently inquire about the practical aspects of the process—cost, scheduling, and the handling of diverse equipment types. Clarifying these details upfront ensures a smooth and efficient project.
What’s This Going to Cost, and How Soon Can You Be Here?
This is often the first question, and the answer is: it depends on the project scope. The final cost for secure IT disposal Atlanta services is determined by the volume and type of assets, your physical location, and any specialized services required, such as on-site data destruction.
A large-scale data center decommissioning will have a different cost structure than a small office retiring a dozen desktops. On-site hard drive shredding, for example, may have an associated fee but delivers immediate, verifiable proof of destruction that is non-negotiable for high-security environments.
- Logistics: Are the assets consolidated on a ground floor with a loading dock, or are they located across multiple floors of a high-rise? Logistical factors impact the labor and time required.
- Asset Value: If you are retiring newer equipment with residual value, the proceeds from remarketing can often offset or even exceed the project costs.
- Scheduling: For most standard pickups, a professional vendor can typically be on-site within a few business days. However, complex projects like a data center cleanout require greater lead time for planning and coordination.
The only way to get a precise figure is to request a detailed quote. A reputable partner will conduct a thorough discovery to provide a transparent estimate with no hidden costs.
How Do You Handle All Our Different Types of Gear?
A common concern is managing the wide variety of equipment in a typical corporate environment. A certified ITAD partner is equipped to handle nearly any electronic asset your business needs to retire.
This includes servers, printers, old company cell phones, networking switches, and even the office copier—which almost always contains an internal hard drive storing copies of sensitive documents. The same secure data destruction processes applied to servers are used for that copier's hard drive. The objective is to provide a single, secure, and comprehensive solution for all of your retired IT assets, ensuring no device falls through the cracks.
Ready to turn your retired IT assets into a secure, compliant, and closed chapter? The team at Atlanta Computer Recycling is here to help. We provide Atlanta businesses with certified data destruction and responsible electronics recycling, tailored to your specific needs. Get a free quote for your IT disposal project today.