A Business Guide to Metro Atlanta E-waste Disposal and ITAD
For businesses in Metro Atlanta, old electronics aren't just clutter—they're a serious liability. If you're retiring IT hardware without a solid plan, you're opening the door to costly data breaches, crippling regulatory fines, and brand-damaging environmental screw-ups.
A strategic IT Asset Disposition (ITAD) plan isn't a "nice-to-have" anymore. It's an absolute must for corporate risk management.
Why Your Business Needs a Metro Atlanta E-waste Strategy
Think about the sheer volume of technology being upgraded across Atlanta's corporate offices, healthcare systems, and schools. It’s creating a mountain of electronic waste. Just tossing out old computers, servers, and networking gear is a direct threat to your organization's security and its reputation. Without a formal plan, you're exposed to financial and legal fallout that goes way beyond a simple disposal fee.
This isn’t just a local problem, either. It’s a massive global issue. Projections show e-waste will blow past 60 million metric tonnes by 2025, and less than 25% of it gets properly recycled. That means a whole lot of toxic lead and mercury seeping into our environment. The problem hits especially close to home here, with Metro Atlanta leading the nation in data center growth. That fuels a constant surge of discarded servers and networking equipment that all need secure, compliant handling.
You can learn more about the environmental impact of electronic waste and see how it affects our local community firsthand.
The Real Costs of Getting It Wrong
For any business, the risks of improper Metro Atlanta e-waste disposal are very real. These aren't just hypotheticals; they're the kinds of events that can bring a company to its knees. The dangers break down into three main categories:
- Data Security Breaches: A single hard drive you thought was "wiped" can still hold thousands of sensitive files—customer data, financial records, you name it. A breach doesn't just cost money; it can permanently shatter your brand's credibility.
- Compliance Violations: If you're in healthcare, you know about HIPAA. The rules for protecting sensitive information are ironclad. Improperly disposing of a device with patient data on it can lead to fines that stretch into the millions.
- Environmental and Reputational Harm: Today’s customers and business partners care about corporate responsibility. If news breaks that your company is dumping e-waste improperly, the hit to your public image can undo years of hard work.
The core issue is that many businesses still see old electronics as trash, not as data-bearing assets that carry immense liability. Shifting that perspective is the first step to protecting your organization from these hidden dangers.
Building Your IT Asset Disposition Framework
A smart e-waste strategy for your Metro Atlanta business doesn’t start when the truck arrives. It begins long before a single piece of equipment leaves your facility, with a clear framework for understanding exactly what you have.
Flying blind without a comprehensive IT asset inventory is a huge risk. You're opening the door to data breaches, compliance failures, and missed chances to recover value from old hardware.
This first step is the bedrock of your entire IT Asset Disposition (ITAD) program. It turns a chaotic pile of electronics into a manageable, categorized list that drives every decision you make down the line. To get a better handle on the big picture, you can learn more about what IT asset disposition entails and why it's so critical.
Kicking Off Your Asset Inventory
Forget those clunky, complicated spreadsheets that no one can ever seem to keep updated. The real goal here is to create a practical, streamlined inventory that zeroes in on the details that actually matter for disposition. Your team needs to capture a few key pieces of information for every device on its way out.
A solid inventory should include:
- Asset Tag or Unique ID: Whatever internal tracking number your company uses.
- Serial Number: The manufacturer's unique number is essential for chain-of-custody tracking.
- Device Type: Is it a laptop, server, switch, or desktop? Simple.
- Data-Bearing Status: A quick "Yes/No" to flag anything that held sensitive information.
- Physical Location: Note the building, floor, or room to make the pickup process a breeze.
This isn't just about making a list; it's about spotting potential risks. A server that once held customer financial data needs a completely different level of handling than an old office phone system.
The most common mistake I see businesses make is underestimating the data hiding on forgotten devices. Peripherals, network gear, and even old printers can hold sensitive information. If you overlook them, they become a massive liability. A thorough inventory shuts down these security gaps right from the start.
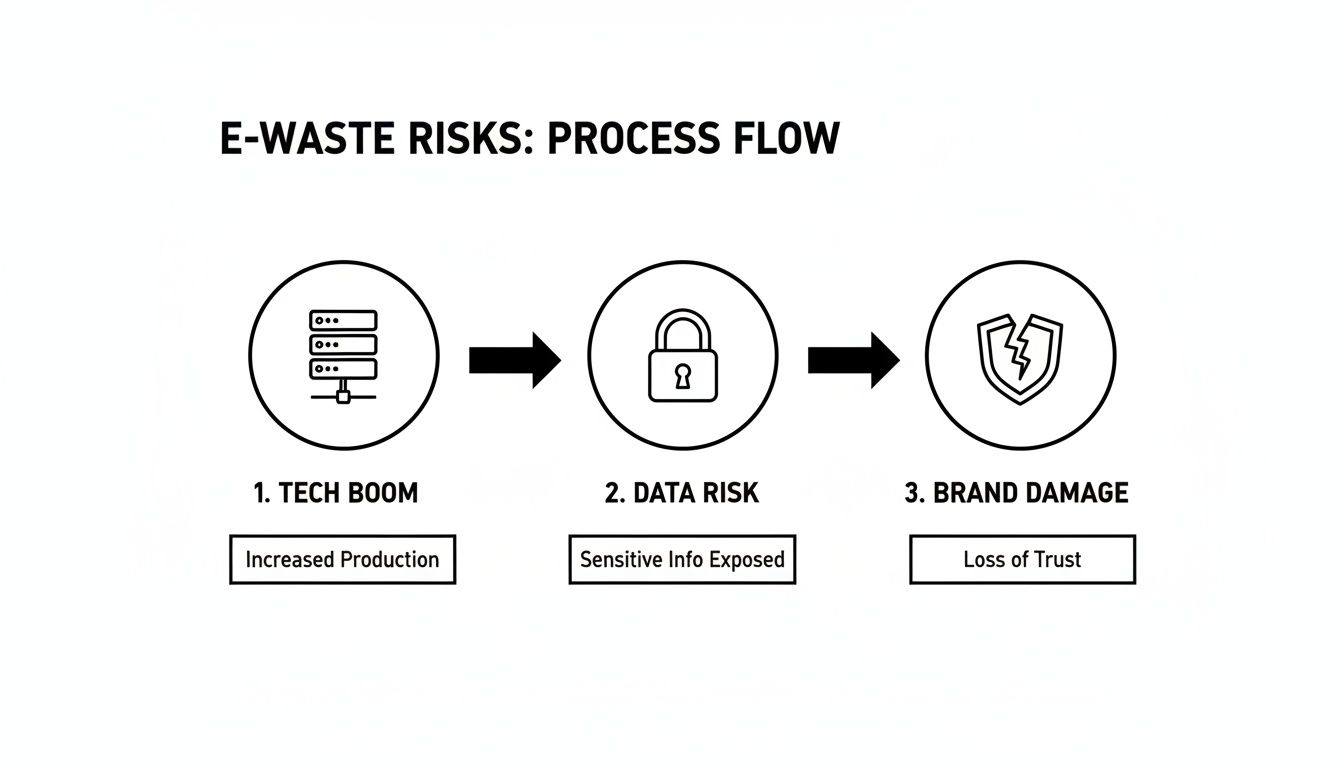
This infographic shows the direct line from routine tech turnover to the kind of brand damage that can happen if these risks aren't managed properly.
The flow from the tech boom to potential data exposure and brand damage makes it clear: a breakdown in your disposition process can have severe consequences for your business.
Classifying Assets for Security and Value
Once you have your inventory locked down, it's time to classify everything. This is where you sort your assets into clear categories to figure out their end-of-life path. Doing this helps you squeeze the most financial value out of your gear while locking down security and compliance for every single item.
This ITAD framework should also tie into your company's broader IT disaster recovery plan to keep business continuity and data security aligned.
By organizing your old equipment, you can map out a clear plan of attack. The table below offers a straightforward model for classifying your assets and deciding the next steps for your Metro Atlanta e-waste disposal.
IT Asset Classification for Disposition Planning
Use this table to categorize your retiring IT assets and determine the appropriate data destruction and disposal pathway for each.
| Asset Category | Common Examples | Data-Bearing Status | Recommended Action |
|---|---|---|---|
| Remarketing Candidates | Laptops (less than 5 years old), recent servers, networking switches | Yes | Secure data wiping (DoD 5220.22-M), cosmetic refurbishment, and resale to recover value. |
| Data Destruction Priority | Older hard drives, damaged servers, devices with proprietary data | Yes | On-site or off-site physical shredding to ensure data is irrecoverable. Certificate of Destruction is mandatory. |
| Recycling Only | Broken monitors, outdated printers, keyboards, cables, old phone systems | No | Responsible recycling through a certified vendor to recover raw materials like copper and plastic. |
| Component Harvesting | High-end servers, specialized equipment with valuable parts | Yes | Secure data destruction first, followed by disassembly to salvage valuable components like RAM, CPUs, and power supplies. |
This structured approach makes sure no device falls through the cracks. It gives you a clear, defensible process that protects your data, maximizes your ROI, and guarantees environmental compliance for all your retired IT assets.
Executing Ironclad Data Destruction
So you’ve inventoried every device holding company data. Now for the most critical part—making sure that data is gone for good.
Let's be clear: dragging files to the trash or reformatting a hard drive is a catastrophic mistake. It leaves behind easily recoverable data fragments, creating a direct path to a breach. For any organization handling sensitive information, proper data destruction isn't just a good idea; it's a legal and ethical mandate.
This is the step that separates responsible Metro Atlanta e-waste management from becoming the next cautionary tale on the evening news.
Software Wiping vs. Physical Shredding
When it comes to making data truly unrecoverable, you have two primary, industry-accepted methods. Knowing when to use software wiping versus physical destruction is key to a secure and efficient ITAD strategy.
Software-based data wiping uses specialized programs to overwrite every single sector of a hard drive with random data, essentially burying the original information. The gold standard here is the DoD 5220.22-M method, which runs multiple passes to guarantee complete sanitization. This is the perfect approach for newer, functional hard drives you might want to reuse or resell, allowing you to recoup some value.
On the flip side, physical shredding is exactly what it sounds like. We feed hard drives, SSDs, and other media into an industrial shredder that pulverizes them into tiny, unrecognizable bits of metal and plastic. There’s no coming back from that.
A common misconception is that one method is universally "better." The best strategy often involves both. Wiping is great for value recovery on working assets, while shredding is the non-negotiable choice for failed drives or when you need absolute, foolproof security.
When to Choose Each Method
Your decision to wipe or shred comes down to the asset's condition, its age, and your company's specific compliance needs. Let’s walk through a few real-world scenarios for businesses right here in Metro Atlanta.
- A healthcare provider decommissioning laptops with patient data: Functional laptops with resale value are great candidates for DoD-standard wiping, a cost-effective and compliant choice. But for any failed hard drives from those machines? Physical shredding is the only way to satisfy HIPAA's strict data protection rules.
- A law firm retiring servers with client case files: Given the extreme sensitivity of legal records, this situation almost always demands physical shredding for all drives, working or not. The peace of mind and bulletproof legal standing from irrefutable destruction far outweigh any potential resale cash.
- A school district upgrading a computer lab: With hundreds of desktops, a mixed approach is smartest. Wipe the functional hard drives for remarketing to help fund the next tech refresh. Any damaged or obsolete drives go straight to the shredder.
This logic applies to all kinds of institutions. For IT managers in colleges, K-12 districts, and government departments, getting rid of old computers and servers is a massive data breach risk if not done right. The business case for professional recycling is also compelling: recycling one million cell phones can yield 35,000 pounds of copper, 772 pounds of silver, and 75 pounds of gold, which helps offset the project costs. For a closer look at how local agencies are tackling this, check out this detailed city audit report.
The Certificate of Data Destruction: Your Legal Shield
No matter which method you choose, the job isn't done without the paperwork. A Certificate of Data Destruction is the formal document from your ITAD partner that serves as your legal proof of compliance.
This certificate is your official record, confirming your data was destroyed according to industry standards. Crucially, it should list the unique serial numbers of every single drive that was wiped or shredded, creating a clean, auditable paper trail from you to oblivion.
Here’s why it’s so essential:
- Compliance Verification: It shows you’re meeting regulations like HIPAA, FACTA, and GDPR.
- Liability Protection: If you ever face a legal challenge or audit, this document is your proof that you took the right steps.
- Chain-of-Custody Finalization: It officially ends your responsibility for the data, closing the loop on each asset’s lifecycle.
Never work with a vendor that can't provide a serialized Certificate of Data Destruction. It's your ultimate safeguard and a cornerstone of any defensible Metro Atlanta e-waste plan. To see how we handle this, you can learn more about our secure data destruction processes and certifications and how we ensure your data is gone forever.
Getting Your Gear Out the Door: Logistics and Pickup
Once your data is wiped or shredded, the next big job is getting all that hardware out of your building. For any IT manager, trying to coordinate the decommissioning and transport of hundreds of devices can feel like a logistical nightmare, especially if you're in the middle of an office move or a data center shutdown.
A smooth pickup is about more than just hauling away old gear. It's about minimizing the disruption to your daily operations while keeping a tight chain of custody from your door to the recycling facility.
Prepping for an On-site Decommission
Solid logistics always start with good on-site planning. Whether you're clearing out a multi-floor office in Midtown Atlanta or shutting down server racks, the trick is to prep the site so the removal team can get in and out quickly and quietly. This is where a vendor with a dedicated logistics crew is worth its weight in gold.
Instead of your own team spending days pulling servers from racks or untangling a spiderweb of cables, a professional ITAD partner handles all that heavy lifting. Their crew shows up ready to disconnect, palletize, and securely wrap everything for transport, freeing up your people to do their actual jobs.
To make things go smoothly, think about these practical steps:
- Clear the Way: Make sure there’s a direct, unobstructed path from where the equipment is to the loading dock or exit.
- Create a Staging Area: If you can, move all the e-waste to one secure, designated spot. It makes the pickup much faster.
- Confirm Access: Double-check loading dock availability, and be aware of any building rules on freight elevator use or moving hours.
A well-planned pickup is a quiet one. The goal is for the vendor's team to operate so efficiently that your other employees barely notice they are there. That level of quiet coordination is the hallmark of a true professional ITAD partner.
If you're managing the transport yourself, remember that certain items have specific shipping requirements. For example, it’s good to understand the logistics for shipping e-waste components like toners.
Secure Transport and Chain of Custody
The moment your assets leave your building is a critical point of vulnerability. This is where secure transport becomes non-negotiable. Your Metro Atlanta e-waste partner should be using their own dedicated fleet for pickups, not some random third-party courier.
This is the only way to maintain a truly secure chain of custody. A professional service will use locked, GPS-tracked vehicles to bring your assets directly to their secure facility. When they arrive, the sealed pallets are unloaded in a controlled-access area under video surveillance, guaranteeing that not a single asset goes missing.
The whole process should feel seamless and transparent, giving you confidence that your equipment is protected every step of the way. You can see how this works in practice by exploring the details of a professional commercial computer pickup service.
When You Can't Let Drives Leave: On-Site Shredding
In some high-security environments, even the most secure transport plan isn't enough to satisfy internal policies or regulatory demands. If you're a financial institution, healthcare provider, or government contractor, letting data-bearing devices leave your site intact is often a non-starter.
This is where on-site hard drive shredding is the only real answer. In this scenario, the vendor brings an industrial-grade mobile shredder right to your facility. You and your team can physically watch every single hard drive, SSD, and backup tape get turned into tiny metal fragments before the scrap material ever leaves your property.
This service offers the ultimate proof of data destruction. It completely eliminates transport-related risks and gives you indisputable evidence of compliance—the highest level of security you can get in the ITAD industry.
Choosing Your Metro Atlanta ITAD Partner
Picking the right partner for your Metro Atlanta e-waste is one of the most critical decisions you'll make in this entire process. This isn't just about finding someone to haul away old gear. It's about finding a strategic partner who protects you from six-figure data breach fines, ensures ironclad compliance, and basically acts as an extension of your own IT team.
The wrong choice can expose your business to staggering risks. A basic collector might just throw your server on a truck and call it a day. A true ITAD partner, on the other hand, documents every single step—from the moment it leaves your building to its final destruction—giving you an unbreakable chain of custody. Knowing the difference is everything.
Certifications That Actually Matter
When you start looking at vendors, you'll be hit with a lot of acronyms. Don't get lost in the alphabet soup. The one that truly separates the professionals from the pretenders is R2v3 (Responsible Recycling).
An R2v3-certified facility has passed rigorous, independent audits proving they meet the highest industry standards for:
- Data Security: They have proven, documented protocols for protecting data on every single device they touch.
- Environmental Responsibility: Their recycling processes are safe, sustainable, and transparent.
- Worker Health and Safety: They maintain a secure and safe environment for their employees.
Think of R2v3 as the absolute baseline. If a vendor doesn't have it, walk away. Without that certification, you have no guarantee your data is safe or that your old equipment won't end up illegally dumped, creating a massive liability that traces right back to you.
Evaluating Data Destruction and Security Protocols
Beyond the R2v3 cert, you need to get into the weeds of how they destroy data. A top-tier provider won't just offer one method; they’ll have both software wiping and physical shredding and can explain exactly when to use each.
The sheer volume of e-waste in Metro Atlanta is driven by our booming tech scene. Constant IT refreshes mean tons of old servers and laptops are always being retired. And the environmental cost is huge—producing just one new computer and monitor requires 1.5 tons of water, 48 pounds of chemicals, and 530 pounds of fossil fuels. Proper recycling slashes that impact. Local facilities with 50,000 sq. ft. operations are built to handle this volume, with data security at their core. You can learn more about Georgia's data center boom and its impact to understand the scale.
Here are the direct questions to ask any potential partner:
- Do you provide a serialized Certificate of Data Destruction for every single drive?
- Can you bring a mobile shredder to our facility for on-site hard drive destruction?
- What does your chain-of-custody documentation look like from pickup to final processing?
- How do you secure your facility? (You want to hear about controlled access, 24/7 video surveillance, and employee background checks).
Their answers will tell you everything you need to know about their commitment to security. For a clearer picture of what a professional operation entails, see this overview of what a dedicated electronic waste recycling company offers.
Before making a final choice, it's helpful to see a side-by-side comparison of what you're really getting.
ITAD Vendor Evaluation Checklist
| Evaluation Criteria | Basic E-waste Collector | Certified ITAD Partner (e.g., ACR) |
|---|---|---|
| Certifications | Unlikely to hold R2v3 certification. | R2v3 Certified, ensuring audited security and environmental practices. |
| Data Destruction | May offer basic wiping; often no proof. | Provides DoD-compliant wiping & physical shredding with serialized certificates. |
| Chain of Custody | Minimal or non-existent documentation. | Secure, GPS-tracked transport and unbroken, documented chain of custody. |
| On-site Services | Typically pickup only. | Offers on-site decommissioning, data destruction, and asset packing. |
| Insurance Coverage | Basic general liability, if any. | Carries robust data breach and pollution liability insurance. |
| Value Recovery | Focuses on scrap value only. | Actively remarkets viable assets to return value and offset costs. |
| Compliance | Little to no support for HIPAA, PCI, etc. | Deep expertise in regulatory compliance; provides necessary documentation. |
The checklist makes it clear: for any organization that handles sensitive data, a certified ITAD partner isn't a luxury—it's a necessity.
Logistics, Insurance, and Value Recovery
A partner's logistics are just as important as their security protocols. Do they run their own fleet of secure trucks, or do they subcontract transport? An outsourced driver is another weak link in your chain of custody. A true partner can also handle complex on-site work, like de-racking servers in a data center and palletizing everything for safe transport.
Insurance is another absolute must. Your ITAD partner needs to carry significant liability insurance that specifically covers data breaches and environmental pollution. Don't just take their word for it—ask to see their certificate of insurance.
Finally, a smart partner isn't just a cost center; they can be a revenue generator. Ask about their process for remarketing newer assets. They should be able to test, grade, and resell equipment that still has life in it, sharing that recovered value with you. This can often offset, or even cover, the entire cost of the service.
Your Top Questions About Business E-waste in Atlanta
When it comes to handling your company's old tech in Metro Atlanta, we know you have questions. For IT managers and business owners, getting straight answers on cost, security, and logistics is key to making the right call. Let's tackle the most common concerns we hear from businesses just like yours.
What's the Real Cost for Commercial E-waste Recycling in Atlanta?
For most businesses we work with, the service is often free. If you have a decent amount of valuable IT assets—think servers, laptops, and networking gear—reputable ITAD partners can usually provide complimentary pickup and data destruction.
Why? The value recovered from those reusable components is enough to cover the labor, transport, and recycling costs. This means your entire project can be cost-neutral.
Now, if you have a smaller load or a project with mostly low-value items (like old office phones or broken keyboards), you can expect a nominal fee. This simply covers the cost of doing things the right way—certified, secure recycling. The best move is always to get a custom quote based on your specific inventory. A high volume of good equipment can sometimes even put money back in your pocket.
The biggest factor driving your cost is the mix of equipment. A pallet of recent-generation servers is a high-value load that can pay for itself. A room full of old CRT monitors, on the other hand, will have a recycling fee because of the hazardous materials inside.
How Can I Be 100% Sure My Data Was Destroyed?
Absolute proof isn't just a promise; it's a documented, auditable process that leaves no room for doubt. A certified ITAD vendor delivers this assurance in two main ways.
First, there's secure data wiping that meets government standards like DoD 5220.22-M, a method that overwrites your drives multiple times. The second, and more final, method is physical destruction, where we feed the devices into an industrial shredder that turns them into tiny fragments.
For your records, you should always demand a formal Certificate of Data Destruction. This is more than a receipt; it’s a legal document proving your compliance. It must list the unique serial numbers of every single hard drive or SSD we destroy, creating an unbroken paper trail that protects your business from liability down the road. In an audit, this document is your best defense.
What Kind of Electronics Do You Take from Businesses?
A good ITAD partner should be a one-stop shop, equipped to handle the wide range of electronics a modern business uses. This is a huge time-saver for organizations that want a single solution for their Metro Atlanta e-waste.
Here’s a quick look at what that typically includes:
- Data Center & IT Gear: Servers, server racks, network switches, routers, firewalls, data storage arrays, and uninterruptible power supplies (UPS).
- Workstations & Laptops: Desktops, laptops, tablets, and all those LCD monitors piling up in the closet.
- Office Equipment: VoIP phones, projectors, docking stations, and peripherals like keyboards and mice.
- Specialized Hardware: Medical equipment, lab testing devices, and point-of-sale (POS) systems.
While we take most IT hardware, some items like old-school CRT monitors or giant office copiers might have a small recycling fee. That’s because they contain hazardous materials like leaded glass and mercury, which cost more to process safely. Always send over an inventory list so your vendor can give you a clear, transparent quote.
Why Is Chain of Custody Such a Big Deal for IT Assets?
Chain of custody is the documented trail that tracks your equipment from the second it leaves your building to its final destination. It is, without a doubt, the single most important security control in the ITAD process. It’s what prevents theft, loss, and the data breaches that follow.
Think of it as the evidence log for your company's most sensitive data. A truly secure chain of custody relies on a few key things working together:
- Secure Transport: Your assets travel in locked, GPS-tracked vehicles driven by badged, background-checked employees—not random third-party couriers.
- Controlled Facilities: When the truck arrives, your gear is unloaded into a secure, access-controlled facility under 24/7 video surveillance.
- Serialized Auditing: Every single device is scanned and tracked by its unique serial number through the entire workflow, from the loading dock to final destruction or resale.
This unbroken chain gives you end-to-end accountability. It’s the proof that no device went missing, protecting your organization from the massive financial and reputational fallout of a lost hard drive. When you're talking to a potential partner, always ask them to walk you through their chain-of-custody process step-by-step.
Ready to implement a secure, compliant, and cost-effective e-waste strategy for your Atlanta business? The team at Atlanta Computer Recycling is here to help. We provide end-to-end ITAD services, from on-site decommissioning and secure logistics to certified data destruction and responsible recycling. Get a free quote today and protect your organization's sensitive data.