Certificate of Destruction Sample: Ensure Compliance & Secure IT Asset Disposal

A Certificate of Destruction (CoD) is the official, legally binding document that proves your company's sensitive data has been permanently and securely destroyed. Think of it as a death certificate for your data—it’s the final word confirming that retired IT assets no longer pose a risk to your organization. This document is your shield against liability and your proof of regulatory compliance.
Why a Certificate of Destruction Is Non-Negotiable for Your Business
When an old server, laptop, or hard drive leaves your facility, your responsibility for the data on it doesn't just disappear. Without definitive proof of destruction, your company remains on the hook for any data that might surface later. A Certificate of Destruction formally transfers that liability from your organization to your IT Asset Disposition (ITAD) partner.
It’s so much more than a receipt for service; it’s a critical legal and compliance instrument for any business.
This one document serves as your frontline defense during an audit. Whether it’s for HIPAA, SOX, or GDPR, auditors will demand an unbroken chain of custody that ends with certified data destruction. The CoD provides this final, crucial link in the asset lifecycle.
To help you communicate its importance, here's a quick overview for your key business stakeholders.
Certificate of Destruction At a Glance
| Aspect | Description for Your Business |
|---|---|
| Legal Proof | A legally binding record that verifies secure data destruction, transferring liability away from your company. |
| Compliance Shield | Your primary evidence for auditors to demonstrate compliance with regulations like HIPAA, GDPR, and SOX. |
| Risk Mitigation | Protects against fines, lawsuits, and brand damage by proving due diligence in data protection. |
| Chain of Custody | The final, critical document in the asset lifecycle, confirming the end of the data's journey. |
This table underscores why obtaining and retaining a CoD isn't just a best practice—it's an essential business function for protecting your company from every angle.
The True Cost of Unverified Destruction
Failing to secure a proper CoD can unleash severe consequences that go far beyond a simple compliance slap on the wrist. The potential fallout for any commercial enterprise is serious:
- Hefty Regulatory Fines: Data privacy laws like HIPAA can impose fines reaching millions of dollars for a single data breach traced back to improperly disposed-of hardware.
- Reputational Damage: A data breach can shatter customer trust that took years to build. The public fallout often causes more long-term harm than the initial financial penalty.
- Legal Liability: In the event of a breach, your organization could face lawsuits from affected customers, partners, and employees whose data was compromised.
- Competitive Disadvantage: Proving secure data handling practices is a key differentiator. A lack of proper documentation can disqualify you from contracts, especially in sensitive industries.
The scale of unaccounted-for electronic hardware is enormous. In 2022, the world generated a staggering 62 million tonnes of electronic waste, yet only 22.3% was formally collected and recycled. For IT managers in the Atlanta metro area, this means a massive amount of undocumented e-waste from hospitals, schools, and government agencies ends up in informal channels, creating huge compliance risks.
A Certificate of Destruction is more than a piece of paper. It is an enforceable record that confirms your vendor has assumed the responsibility and liability for destroying your data according to industry standards.
Your Shield Against Data Breach Fallout
Ultimately, a Certificate of Destruction acts as a powerful risk mitigation tool. It provides tangible evidence that your business acted responsibly and took verifiable steps to protect sensitive information. This documentation is invaluable for demonstrating due diligence to regulators, stakeholders, and clients. You can read more about the essential role of a Certificate of Destruction in a secure ITAD strategy.
By demanding and verifying a comprehensive CoD, you are not just ticking a box on a checklist. You are actively protecting your company’s financial health, its reputation, and its future.
Deconstructing a Compliant Certificate of Destruction
A Certificate of Destruction (CoD) is much more than just a piece of paper—it’s a legal instrument. But not all certificates are created equal. A vague, incomplete document offers a false sense of security and can crumble under the scrutiny of a compliance audit, leaving your business completely exposed.
Understanding the anatomy of a legally sound CoD is critical. It allows you to instantly tell the difference between a defensible, audit-proof record and one that’s practically worthless. Think of it like inspecting the title for a commercial vehicle—you need to know which fields are non-negotiable to prove the transfer of liability is legitimate.
A proper certificate tells the complete story of your data’s final moments, leaving no gaps for an auditor to question. It details the who, what, where, when, and how of the entire commercial service.
The Mandatory Components of a CoD
Every compliant Certificate of Destruction must contain a core set of information to be considered valid. These elements are the foundation of your legal proof and the first things an auditor will look for. If any of these are missing, it's a major red flag for your business.
These are the non-negotiable fields:
- Unique Serial or Tracking Number: This number ensures each CoD is a unique record. It prevents duplication and makes it easy to track within your asset management system.
- Client Information: The full legal name and address of your organization must be clearly stated, identifying exactly who the service was performed for.
- Service Provider Information: The name, address, and contact details of the ITAD vendor who performed the destruction are required to establish accountability.
- Chain of Custody Details: This section documents the transfer of all materials, including the date of collection and the physical location where the destruction took place.
- Destruction Method: The certificate has to state exactly how the data was destroyed. Vague terms like "disposed of" are unacceptable. It needs to specify methods like "Physical Shredding (2mm particle size)" or "NIST 800-88 Purge."
- Authorized Signature: A signature from an authorized representative of the ITAD partner legally attests that all the information provided is accurate.
A certificate lacking any of these core components simply fails to provide a clear and defensible audit trail for your business operations.
A Certificate of Destruction should function as an irrefutable legal statement. If it’s missing key details like a unique serial number or a specific destruction method, it cannot fulfill its primary purpose of transferring liability and proving compliance.
Value-Add Fields for Enhanced Security
Beyond the absolute essentials, a truly robust Certificate of Destruction includes additional details that provide an extra layer of security and transparency. While not always mandatory, these elements demonstrate a higher level of due diligence and make your documentation even stronger.
Demanding these from your ITAD partner is a best practice for any organization that's serious about data security.
Consider these high-value additions:
- Individual Asset Details: This means listing the specific serial numbers, asset tags, and device types (e.g., Dell Latitude 7420, Seagate Barracuda HDD) for each and every item destroyed. It provides granular proof that a specific piece of equipment was processed.
- Witness Information: Including the name and signature of an employee from your organization who witnessed the destruction process is powerful, especially for on-site services.
- Regulatory Statement of Compliance: A formal declaration that the destruction was performed in accordance with specific standards, such as HIPAA, NAID AAA, or R2v3 protocols.
These extra details create an ironclad record that connects your internal asset inventory directly to the final proof of destruction. They close any potential compliance gaps, making your documentation virtually unchallengeable during an audit. For more guidance on structuring your own documentation, you can explore a helpful certificate of destruction template to see these fields in action.
Certificate of Destruction Samples for Key Business Scenarios
Theory is one thing, but seeing a certificate of destruction sample in action is what really builds confidence. A CoD for a stack of shredded hard drives looks completely different from one that documents the sanitization of an entire data center. The asset itself and the regulations your business must follow dictate the level of detail required.
To bridge that gap from theory to reality, we’ve put together a few examples from common business situations. These will show you exactly what a compliant, audit-proof certificate looks like in the real world, so you know what to demand from your ITAD partner.
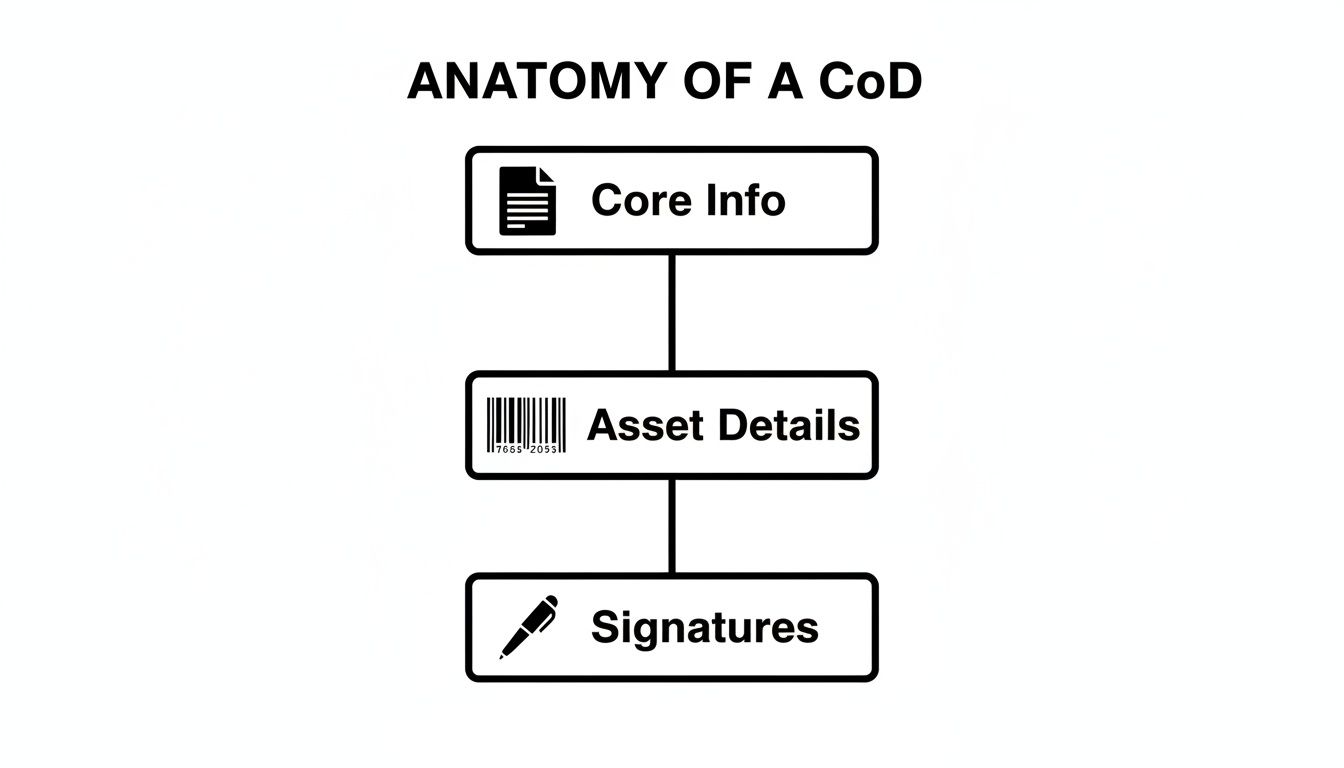
This flowchart breaks down the anatomy of a solid Certificate of Destruction into its most critical parts.
As you can see, a defensible CoD is built on three pillars: the core who, what, and when; the specific asset details; and the authorized signatures that make it official.
Sample 1: On-Site Hard Drive Shredding for HIPAA Compliance
Picture this: a large Atlanta hospital is retiring 500 old employee workstations. To comply with HIPAA, the organization needs absolute, undeniable proof that every last bit of Protected Health Information (ePHI) has been physically obliterated. For this level of security, they’ve contracted a commercial service for on-site shredding.
In this scenario, the CoD has to be airtight.
- Destruction Method: It can't just say "shredded." It needs to be specific, like "On-site physical shredding to 2mm particle size." This standard turns data platters into dust, going far beyond basic requirements.
- Asset Log: This is non-negotiable for HIPAA. The certificate must include a full manifest listing the serial number and asset tag of every single hard drive. This creates a direct, unbroken link between each physical device and its destruction.
- Chain of Custody: The CoD documents the exact date, time, and address where the shredding happened. It will also name the certified technicians who ran the shredder.
- Witness Signature: There's a line for the hospital's IT manager to sign, legally confirming they watched the entire destruction process unfold.
This isn't just a receipt—it's a legal affidavit. It gives the hospital an ironclad defense if any questions ever come up about a potential data breach from these specific computers.
Sample 2: Secure Data Erasure for a Corporate Laptop Refresh
A tech company is upgrading 200 laptops for its remote team. These are fairly new machines with good resale value, so the goal is to wipe all proprietary data clean while keeping the hardware intact for remarketing. It's a smart commercial decision for both security and sustainability.
Here, the certificate is all about proving the data sanitization process worked flawlessly.
When you’re erasing data, the Certificate of Destruction acts as proof that the data is gone, not just the device. It validates that a software-based process overwrote every sector on the drive, making the original information impossible to get back.
The key fields on this certificate of destruction sample would be:
- Erasure Standard: The CoD will explicitly name the method used, like "NIST 800-88 Purge" or "DoD 5220.22-M." This shows a recognized, government-approved standard was met.
- Software Verification: It will list the software tool used (like Blancco or KillDisk) and confirm a 100% verification pass for each and every drive.
- Asset-Specific Reporting: Just like with shredding, it needs an attached log with the serial numbers of each laptop and its corresponding hard drive.
- Erasure Status: You’ll see a clear "Success" or "Pass" next to every single asset. If any drive failed the wipe, it would be noted and would need its own physical destruction certificate.
This document gives the firm the confidence to resell those laptops, backed by defensible proof that their corporate data was professionally wiped. For a deeper dive, check out our guide on getting a certificate of destruction for hard drives where we break down these processes in more detail.
Sample 3: Complex Data Center Decommissioning
Now imagine a financial institution is shutting down an entire data center. This involves hundreds of servers, massive storage arrays, and all the networking gear. The challenge is the sheer volume and variety of equipment, all with different data-storing parts. The CoD for a project like this is a master document, often with hefty appendices.
The certificate has to roll up a mountain of information into a clear, auditable package.
- Project Identifier: It will have a unique project or work order number that ties everything together—from the first inventory list to the final report.
- Summary of Services: This provides a high-level overview, stating the total counts by category (e.g., 250 servers, 50 storage arrays, 100 switches).
- Methodology by Asset Type: The certificate clearly states what happened to each type of gear. For example:
- Servers & Storage Arrays: On-site hard drive shredding (2mm)
- Networking Gear (Switches, Routers): Factory reset and physical destruction of non-volatile memory chips
- Detailed Asset Manifests: This is the most critical part. The CoD will reference attached manifests—usually massive spreadsheets—that list every individual asset by serial number, asset tag, make, and model, along with its final destruction status. This provides a complete audit trail for thousands of individual components.
This consolidated approach gives the financial institution a single, authoritative document to prove compliance for the whole project, while the attached logs offer the granular detail any auditor would demand.
How to Properly Verify and Manage Your Certificates
Receiving the Certificate of Destruction from your vendor feels like the finish line, but it’s not. The real work of closing the compliance loop has just begun. Treating a CoD as just another piece of paper to file away is a huge missed opportunity—and a serious potential risk.
Think of it as the final inspection before you officially sign off on the secure end of your assets' lifecycle. This verification process turns a passive document into an active part of your risk management strategy. It’s your chance to scrutinize the details, confirm every promise was kept, and ensure the proof you’ve received will hold up under an auditor’s magnifying glass.
Your Internal Verification Checklist
Before archiving that certificate, your team needs to run a methodical check to confirm it's accurate and complete. This isn't about micromanaging your vendor; it's about ensuring the commercial service you paid for was delivered exactly as promised and documented perfectly. Don't just scan it—interrogate it.
Here’s a simple but essential checklist to guide your internal review:
- Cross-Reference Asset Details: This is non-negotiable. Pull up your internal asset inventory and meticulously match every serial number and asset tag on the certificate’s manifest against your records. Every single device needs to be accounted for.
- Confirm the Destruction Method: Does the method listed on the CoD line up with your service agreement? If you contracted for on-site shredding to a 2mm particle size, the certificate needs to state that explicitly, not just something vague like "physical destruction."
- Validate All Signatures and Dates: Make sure the authorized signature from your ITAD partner is there and that all dates—from pickup to final destruction—are accurate and align with your project’s timeline.
- Check for Unique Identifiers: A legitimate CoD will have a unique serial number or tracking ID. This is critical for creating an unambiguous audit trail that links this specific document to your specific assets.
This kind of detailed review provides certainty. Our guide on IT asset tracking software can help you build the kind of rock-solid internal inventory needed for this critical cross-referencing process.
Demystifying Technical Jargon on Your Certificate
Your CoD will likely include technical terms that define the security standard used. Understanding these is key to confirming you got the right level of service. For instance, if you see "NIST 800-88 Purge," it means the vendor used a software-based method to overwrite all data on a drive, making forensic recovery nearly impossible. This is a far cry from a simple "Clear" method, which only protects against basic software recovery tools.
Verifying your certificate isn’t about mistrusting your vendor; it's about fulfilling your own due diligence. An accurate, verified CoD is your proof that you took every reasonable step to protect your organization's data.
Just as robust processes are crucial for managing your Certificates of Destruction, similar principles apply to other highly sensitive records. Exploring a guide to Medical Document Management Systems can offer valuable insights into comprehensive data handling and compliance strategies. This due diligence ensures every piece of sensitive documentation, whether for IT assets or patient records, is properly managed.
Building an Audit-Proof Certificate Retention Strategy
Think of your Certificate of Destruction as a long-term legal asset. Its real power isn't in just receiving it—it's in being able to produce it the moment you need it, especially during a surprise compliance audit or a data breach investigation. A CoD lost in an old email inbox is as useless as not having one at all. That’s why building a formal retention strategy is just as vital as verifying the certificate in the first place.
This strategy transforms the CoD from a simple receipt into a dynamic tool for proving your ongoing compliance. It’s not about just filing away a document; it's about creating a secure, searchable archive that stands as a testament to your due diligence years after the assets are long gone. Without one, you’re leaving a massive hole in your data governance framework.
Defining Your Retention Timeline
So, how long should your business hold onto its Certificates of Destruction? There’s no single answer. The right timeline is a mix of regulatory mandates and smart corporate governance. Different industries play by different rules, and it's your responsibility to know which ones apply to your business.
Here are a few common benchmarks to get you started:
- HIPAA: For healthcare organizations, the Health Insurance Portability and Accountability Act is clear. Any documentation related to Protected Health Information (ePHI), including CoDs, must be kept for a minimum of six years.
- SOX (Sarbanes-Oxley Act): If you're a publicly traded company, you'll need to keep audit-related records for up to seven years. This absolutely includes CoDs for any retired financial systems.
- Corporate Governance: Even if no specific regulation applies, a solid best practice is to retain CoDs for at least three to five years as part of a standard asset lifecycle management policy.
The best move is to create a clear, written policy that defines your retention period. This creates consistency and prevents the accidental deletion of a critical compliance document.
Creating a Secure and Searchable Digital Archive
Let's be honest: a messy folder of scanned PDFs on a shared drive isn't an audit-proof strategy. A real digital archive needs to be organized, secure, and easy to search. When an auditor asks for proof of destruction for a specific server from two years ago, you need to find it in minutes, not hours.
Your digital archive should have these non-negotiable features:
- Centralized Location: All certificates go into one secure spot, like a dedicated network drive with restricted access or a secure cloud storage solution. No exceptions.
- Consistent Naming Convention: Create a standardized file naming system that makes searching a breeze. Something like
YYYY-MM-DD_VendorName_CoD-Serial.pdfworks wonders. - Metadata Tagging: Use metadata to tag each certificate with key info like asset serial numbers, the destruction date, and the vendor. This lets you quickly filter and find any certificate of destruction sample or specific record you're looking for.
An auditor won't wait around while you dig through old files. A well-organized digital archive immediately shows that your organization is mature and proactive about compliance, building trust right from the start.
Mock Audit Scenario Tracing the Asset Lifecycle
Picture this: an auditor is in your office reviewing your company’s HIPAA compliance. They point to a laptop from your asset inventory that was decommissioned three years ago and say, "Prove to me it was disposed of securely."
With a solid retention strategy, this is a simple task. You access your digital archive, search for the laptop's asset tag, and instantly pull up the corresponding CoD. The auditor can then see the entire lifecycle: from the initial purchase record straight through to its final, certified destruction. This clean paper trail is undeniable proof that your process works.
A lack of proper documentation creates serious risk. In North America, a shocking 9.4% of e-waste flows are formally documented. For Atlanta's healthcare and government facilities, this means bulk disposal of network gear and servers demands certified providers who issue verifiable certificates for data sanitization and physical destruction. You can learn more about how e-waste tracking impacts business risk by exploring research from the Baker Institute. A robust retention strategy ensures you fall into that compliant minority, not the exposed majority.
Why Your ITAD Partner Determines Your Certificate's Worth
A Certificate of Destruction is only as trustworthy as the company that issues it. That document, filled with official-looking serial numbers and signatures, holds zero real value if the processes behind it are flimsy, undocumented, or just plain insecure.
This is why choosing your IT Asset Disposition (ITAD) partner is the single most important decision you'll make in your entire data destruction strategy.
An uncertified vendor might hand you a document that looks the part, but it’s really just a false sense of security. Without rigorous, third-party validation of their procedures, how can you be sure your data was truly destroyed according to industry standards? At that point, the certificate is just a piece of paper, not a legal shield.
The Power of Industry Certifications
This is where industry certifications like R2v3 and NAID AAA become absolute non-negotiables. These aren't just fancy logos to slap on a website; they are your guarantee of a secure, auditable, and compliant destruction process from start to finish. A partner holding these credentials has been put through the wringer by independent auditors.
- NAID AAA Certification: This one focuses like a laser on secure data destruction. It verifies that a vendor follows strict protocols for everything from employee background checks and facility security to the destruction process itself.
- R2v3 Certification: This standard takes a wider view, covering the entire ITAD lifecycle. It ensures that every step—from environmental responsibility to data security—is handled ethically and safely.
When you work with a certified partner, every certificate of destruction sample they provide is backed by a proven system of accountability. It transforms the document from a simple claim into ironclad proof.
A credible ITAD partner provides more than a document; they provide verifiable peace of mind. Their certifications are your assurance that the certificate they issue will stand up to the toughest scrutiny during a compliance audit.
Ultimately, your vendor’s credibility becomes your credibility. When you need a trusted partner, you can learn more about finding the right electronic waste recycling company to protect your business. Don't settle for less—select a vendor whose proven processes ensure every certificate they issue is definitive proof of their commitment to your data security.
Frequently Asked Questions About Certificates of Destruction
When it comes to data destruction, the paperwork can seem just as complex as the process itself. Let's clear up some of the most common questions businesses have about the Certificate of Destruction.
Think of this as your quick-reference guide for navigating the final, crucial step of IT asset disposition.
Is a Certificate of Destruction a Legal Document?
Yes, absolutely. A Certificate of Destruction isn't just a piece of paper; it's a legally binding document. It serves as your official, notarized proof that data-bearing assets were properly destroyed according to specific industry standards.
More importantly, it formally transfers the liability for that data from your organization to the ITAD vendor who performed the service. In the eyes of auditors for regulations like HIPAA or SOX, the CoD is your primary evidence of due diligence. It proves you took legally defensible steps to protect sensitive information.
What Is the Difference Between a CoD and a Receipt?
A receipt just proves you paid for something. A Certificate of Destruction, on the other hand, is an affidavit—a sworn statement—that documents the how, when, where, and what of the entire data destruction process. It’s an official attestation, not just a financial transaction record.
A CoD includes critical details a simple receipt would never have, like:
- The exact destruction method used (e.g., NIST 800-88 Purge, physical shredding).
- A unique serial number for the certificate itself, creating an audit trail.
- An itemized inventory of the specific assets that were destroyed.
- An authorized signature that legally verifies the work was completed as described.
This level of detail is precisely what gives the certificate its legal and regulatory power.
Can We Create Our Own Certificate of Destruction?
You technically could create your own internal form, but it would hold virtually no weight in an official audit. A self-issued certificate completely lacks the independent, third-party validation that regulators and legal teams look for.
The entire value of a Certificate of Destruction comes from the independent, certified vendor who issues it. Their attestation is what makes the document a trustworthy and defensible piece of evidence.
An internally generated document is just your company vouching for itself. It fails to provide the objective, verifiable proof of compliance that auditors demand.
What Happens if We Lose a Certificate of Destruction?
Losing a CoD can create a serious compliance gap. Without it, you have no official proof that a specific laptop, server, or hard drive was securely disposed of, which could become a major liability during an audit or a data breach investigation. This is why having a solid digital retention strategy is so important.
Your first move should be to contact your ITAD partner immediately. Reputable, certified vendors maintain their own secure archives and should be able to issue a duplicate copy of the original certificate. This is one of the key reasons to always choose a professional, certified partner for your ITAD needs.
Even with a certificate of destruction, a robust data breach response plan is a crucial safeguard, complementing your secure IT asset disposal strategy and demonstrating comprehensive risk mitigation.
At Atlanta Computer Recycling, we provide NAID AAA and R2v3 certified data destruction services that come with audit-proof, legally defensible Certificates of Destruction. Protect your organization and ensure compliance by partnering with Atlanta's trusted ITAD experts. Learn more at https://atlantacomputerrecycling.com.