A Business Guide to Hard Drive Destruction Services

When decommissioning IT assets, professional hard drive destruction services are the only way to guarantee your organization's sensitive data is permanently eliminated. For any business, simply deleting files or reformatting a drive is insufficient. This leaves confidential corporate information exposed and recoverable, creating a significant security liability and compliance risk that no company can afford.
Why Hard Drive Destruction Is a Non-Negotiable for Modern Businesses
For many organizations, retiring old IT equipment is an operational afterthought—a task handled once new systems are deployed. However, that decommissioned server, old office laptop, or retired workstation still contains a complete history of sensitive information, from proprietary financial data and employee records to intellectual property. Relying on standard file deletion methods creates a dangerous illusion of security.
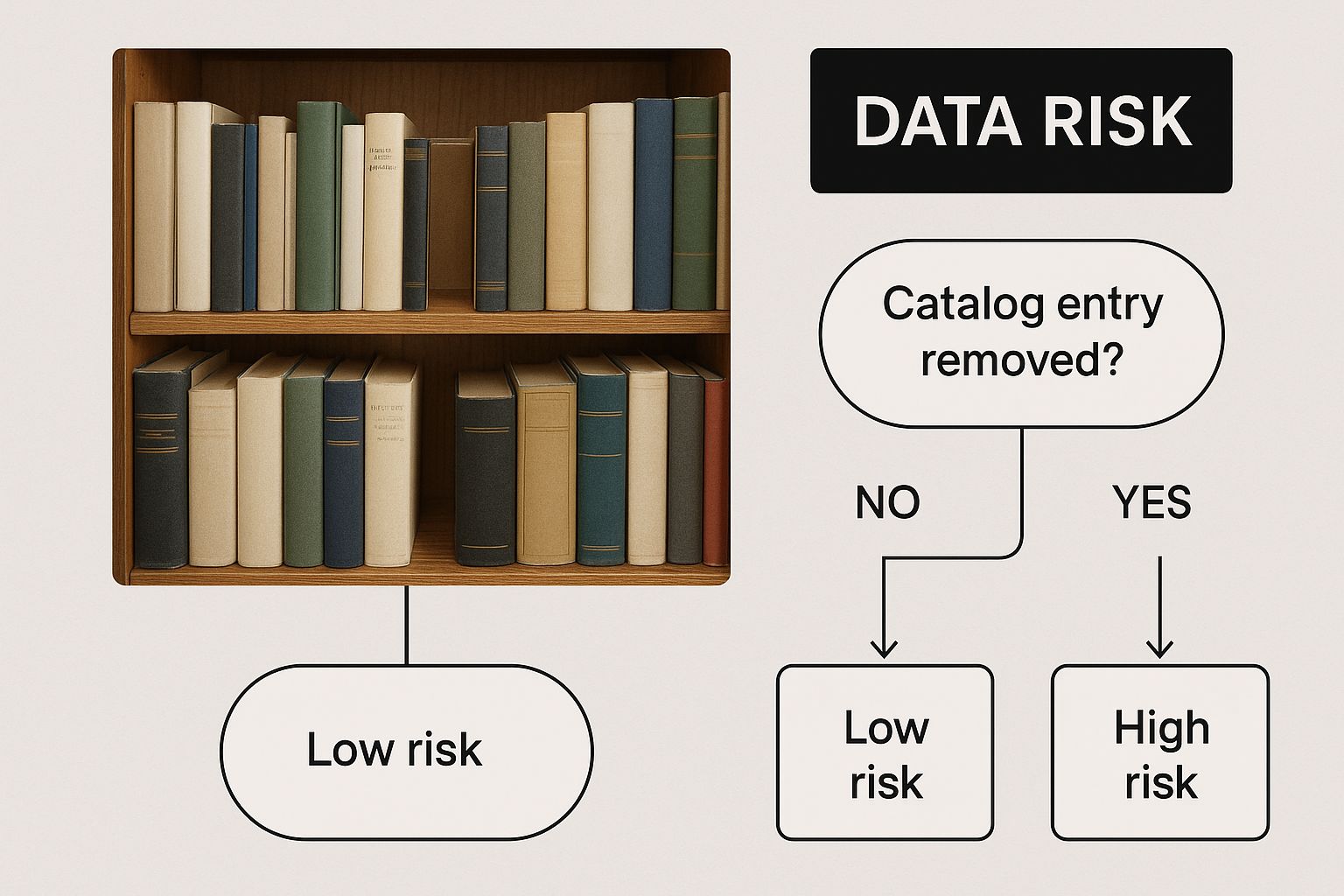
Think of it this way: deleting a file is like removing a chapter title from a book's table of contents. While it makes the information harder to find, the data itself remains on the "pages" of the drive, accessible to anyone with the right recovery tools. Professional hard drive destruction doesn't just erase the index; it feeds the entire book into an industrial shredder, making it impossible for anyone to ever read it again.
This infographic breaks down why that legacy hardware represents a persistent threat.
Even after data has been "deleted," it remains physically present on the drive's platters. Until the drive itself is completely destroyed, your business remains exposed.
The Rising Stakes of Data Security
As cyber threats become more sophisticated and data privacy regulations grow stricter, the consequences of a data breach are more severe than ever. A single, improperly discarded hard drive can lead to devastating financial penalties, complex legal challenges, and irreparable damage to your corporate reputation. It is no surprise that the demand for secure, certified disposal services is accelerating.
The global market for these services is expanding rapidly, projected to grow from USD 1.65 billion in 2024 to an estimated USD 5.05 billion by 2035. This is not a fleeting trend; it is a fundamental shift in how businesses approach data security—as an essential component of corporate governance, not an optional expense.
Data is a liability until it is properly destroyed. A formal data end-of-life policy isn't just a best practice; it's a fundamental component of corporate risk management and a necessary safeguard for protecting your customers, employees, and brand.
Beyond Data: A Responsible Approach
Security is not the only consideration. Responsible hardware disposal is also a critical environmental and corporate social responsibility (CSR) issue. When you partner with a certified destruction service, you gain assurance that once the data is eliminated, the residual electronic components are managed responsibly. This approach protects your business from data-related risks while addressing the environmental impact of electronic waste, aligning your security protocols with your corporate sustainability goals.
Comparing Destruction Methods: Software Wiping Versus Physical Shredding
When it’s time to retire your company’s IT assets, you’re faced with a critical decision: how do you ensure the data they contain is irretrievably destroyed? The choice typically comes down to two primary approaches: software-based wiping and physical shredding. Each method has its strategic place, and understanding the differences is key to making a secure, compliant, and cost-effective decision for your business.
Software wiping, or data erasure, is a process where specialized software overwrites every sector of a hard drive with random, meaningless data. This is typically done in multiple passes to ensure the original information is rendered unrecoverable by software-based tools. A related method, degaussing, uses a powerful magnetic field to neutralize the magnetic domains on traditional hard disk drives (HDDs), effectively erasing them.
To help you decide which path is right for your organization, let's break down the two methods side-by-side.
Table: Software Wiping vs. Physical Shredding: A Business Comparison
| Feature | Software Wiping / Degaussing | Physical Shredding |
|---|---|---|
| Data Security Level | Very High (Data is unrecoverable by software means) | Absolute (Data and drive are physically destroyed) |
| Hardware Reusability | Yes. The drive remains functional for reuse or resale. | No. The drive is completely destroyed and unusable. |
| Best For | IT asset remarketing, donations, internal redeployment. | End-of-life hardware, damaged drives, maximum security needs. |
| Compliance | Meets most standards; requires certified software/process. | The gold standard for HIPAA, DoD, and other strict regulations. |
| Cost-Effectiveness | Allows for value recovery, potentially offsetting costs. | A direct cost, but provides the highest level of liability protection. |
| Environmental Impact | Promotes circular economy by extending hardware life. | Materials are recycled, but the reuse potential is eliminated. |
This table provides a high-level overview, but the practical application is what truly matters. Your choice will depend entirely on your strategic goals for the retired equipment.
The Case For Software-Based Sanitization
The primary advantage of software wiping is hardware preservation. This makes it the ideal choice for businesses looking to recover value from their IT assets through reuse, resale, or donation. It is a strategic way to recoup a portion of the initial investment while adhering to strict data security protocols.
Key business benefits include:
- Asset Value Recovery: Redeploy drives internally or sell them on the secondary market to generate revenue.
- Environmental Friendliness: Reusing electronics is a core principle of the circular economy, reducing e-waste and extending the lifecycle of valuable hardware.
- Detailed Reporting: Professional services provide certified reports verifying that each drive was sanitized according to specific, recognized standards.
However, this method is not a universal solution. Wiping can be less effective on modern Solid-State Drives (SSDs) due to their unique data storage architecture. It can also be a time-intensive process when sanitizing a large volume of drives.
When Physical Shredding Is The Only Answer
For absolute data security, physical shredding is the definitive, irreversible solution. If software wiping is like overwriting a book, shredding is like feeding that book into an industrial pulverizer. There is zero possibility of reassembly or data recovery.
This method is the gold standard for organizations that operate under stringent regulatory requirements or handle highly sensitive intellectual property, especially when dealing with damaged or end-of-life hardware.
For the most sensitive data, there is no substitute for complete physical destruction. Shredding offers absolute certainty that information can never be compromised, providing a clear and defensible end to the data lifecycle.
Shredding guarantees compliance with the toughest data protection regulations, such as HIPAA and DoD standards. The market reflects this priority: spending on destruction equipment reached USD 2.69 billion in 2024 and is projected to climb to USD 3.75 billion by 2030, underscoring the corporate commitment to foolproof data disposal. Choosing a professional hard drive destruction service ensures the entire process is secure, with a certified chain of custody from the moment the drives leave your control.
Navigating Data Protection Regulations and Compliance Standards
For any modern business, data security is not just an IT function—it is a significant legal obligation. Failure to properly dispose of sensitive information stored on retired hard drives can result in crippling fines, litigation, and severe, long-term brand damage. Therefore, understanding the complex landscape of data protection regulations is essential for corporate governance.
These regulations are not suggestions; they are legally binding mandates that dictate how organizations must handle and destroy data. For instance, healthcare organizations are bound by the Health Insurance Portability and Accountability Act (HIPAA), which requires the permanent, secure destruction of any device containing protected health information (PHI). Similarly, any business handling consumer financial data must adhere to the Fair and Accurate Credit Transactions Act (FACTA).
The Gold Standards of Data Sanitization
To help businesses meet these stringent requirements, several key technical standards have been established to define what "secure destruction" entails. While not laws themselves, they serve as trusted benchmarks that certified hard drive destruction services follow to guarantee compliance and efficacy.
Two of the most recognized standards are:
- DoD 5220.22-M: This standard, originating from the Department of Defense, specifies a detailed process for overwriting data on hard drives. While developed for software wiping, its principles established a high bar for data sanitization.
- NIST SP 800-88: The National Institute of Standards and Technology provides a more current and comprehensive framework for media sanitization. It outlines methods for clearing, purging, and physically destroying data, making it the definitive guide for modern IT asset disposition.
Adherence to a standard like NIST 800-88 is more than a best practice—it is your best defense. It provides documented proof that your organization took deliberate, industry-accepted measures to prevent a data breach, which is invaluable during a legal or regulatory challenge.
Global Regulations and Market Demand
The need for compliance extends globally. The General Data Protection Regulation (GDPR) in Europe, for example, imposes substantial fines on companies that fail to protect the data of EU citizens, including during the disposal phase. This growing regulatory pressure is a primary driver of the booming global hard drive destruction market, as businesses worldwide seek to fulfill their legal obligations.
Understanding the specifics of various compliance regulations by industry is crucial for developing a robust data destruction policy.
Ultimately, partnering with a professional destruction service transfers the compliance burden from your internal team to certified experts. They provide a Certificate of Destruction, a formal document that serves as your legal proof of compliance. This certificate is a critical component of a sound IT asset disposition program and demonstrates due diligence, protecting your business from the severe penalties of non-compliance.
How to Choose the Right Hard Drive Destruction Partner
Selecting a partner for hard drive destruction is more than a simple vendor transaction; it is a critical security decision that protects your business from significant liability. Not all providers operate at the same standard, and choosing an unqualified vendor can expose your organization to the very risks you aim to mitigate.
A vendor’s process, certifications, and transparency are as important as the final act of destruction itself.
The selection process is analogous to entrusting a bonded courier with sensitive legal documents. You would not choose the lowest bidder without rigorously vetting their security protocols, tracking capabilities, and professional reputation. The same level of due diligence must be applied when selecting a partner to handle your company’s confidential information.
Verifying Certifications and Standards
Your initial screening criterion should be industry certifications, which provide independent verification of a vendor's security and operational integrity. The most respected credential in the data destruction industry is NAID AAA Certification.
This certification is not a mere marketing badge. It signifies that the company has passed stringent, unannounced audits covering all aspects of their operation, including:
- Employee Security: All staff with access to sensitive materials have undergone extensive criminal background checks and receive ongoing security training.
- Facility Security: The destruction facility is secured with monitored alarms, 24/7 video surveillance, and strict access controls.
- Process Integrity: The entire journey of your assets, from pickup to final destruction, is secured, documented, and fully auditable.
A provider holding NAID AAA Certification has demonstrated adherence to the highest industry standards for secure data destruction. Making this a non-negotiable requirement is the single most effective step you can take to ensure your data is handled responsibly.
Auditing the Chain of Custody
The point at which your hard drives leave your facility is often the most vulnerable. A secure chain of custody is the documented trail that tracks your assets from your premises to their final destruction. A reputable partner will provide a transparent, unbroken chain, offering complete visibility at every stage.
Do not hesitate to ask potential vendors detailed questions about their process. Do they utilize locked, GPS-tracked vehicles? Are their employees uniformed and clearly identifiable? How are your assets secured and inventoried upon arrival at their facility? The quality of their answers is a direct reflection of their security posture.
Essential Questions for Your Potential Partner
Beyond formal certifications and logistics, your due diligence should include a few key operational questions. This ensures a provider aligns with your organization's specific needs for security, compliance, and corporate responsibility.
- Do you offer on-site and off-site destruction? On-site shredding provides maximum assurance, as you can witness the destruction of your drives firsthand. Off-site services can be more efficient for large-volume projects but require absolute trust in the provider's secure transport and facility protocols.
- What does your Certificate of Destruction include? A legitimate certificate is more than a receipt. It must detail the destruction method, the exact date, and—critically—the serial numbers of every individual drive destroyed. This creates an unimpeachable audit trail.
- What is your environmental policy? After destruction, the shredded material constitutes e-waste. A responsible partner will have a certified electronics recycling program to ensure these materials are managed in an environmentally sound manner, preventing them from entering landfills. This is especially vital when decommissioning large-scale IT infrastructure.
Understanding the Costs of Professional Data Destruction
When planning for IT asset retirement, one of the first considerations for any business is the budget. The cost of professional hard drive destruction is not a flat-rate service; it is a variable expense determined by several key factors. It is best framed not as a cost, but as a critical investment in risk management.
The final price depends on the scope and specifics of your project. A small business retiring a dozen PCs will have a different cost structure than a data center decommissioning hundreds of enterprise servers. Vendors typically base their pricing on a few core components that shape the final quote.
Key Factors That Influence Pricing
To accurately forecast your budget, it is important to understand the primary cost drivers. Each factor influences the logistics, labor, and security protocols required for the project.
- Volume of Drives: This is typically the most significant factor. Most providers use a tiered pricing model where the cost-per-drive decreases as the quantity increases. A bulk project of 500 drives will have a substantially lower per-unit cost than a small batch of 10.
- Service Type (On-site vs. Off-site): Deploying a mobile shredding truck to your location (on-site destruction) offers maximum security and witness verification but comes at a premium. Transporting drives to a secure, certified facility (off-site destruction) is generally more cost-effective, particularly for larger volumes.
- Destruction Method: While physical shredding is the industry standard for end-of-life drives, alternative services like degaussing (for drives intended for reuse) may have a different pricing structure.
The fee for professional hard drive destruction is an operational expense that directly mitigates catastrophic financial risk. A single data breach can cost a company millions in fines, legal fees, and reputational damage, making secure disposal a remarkably cost-effective insurance policy.
The Real Cost: A Crucial Comparison
Evaluating the service fee in isolation is shortsighted. The true value becomes evident when compared to the potential cost of a data breach stemming from one improperly discarded drive. Fines under regulations like HIPAA or GDPR can easily reach millions of dollars, not including the substantial costs of customer notifications, credit monitoring services, and litigation.
Engaging a professional service guarantees a secure chain of custody and, most importantly, provides a Certificate of Destruction. This document is your official legal proof of regulatory compliance and serves as your primary defense in an audit or legal dispute. The most effective way to gain clarity for your project is to request a quote for professional data destruction from a certified provider. It’s the best way to understand the costs while exploring options for secure hard drive disposal that align with both your security requirements and your budget.
Frequently Asked Questions About Hard Drive Destruction
When retiring IT hardware, most businesses encounter the same set of questions regarding the process, its necessity, and the required documentation. Obtaining clear answers is essential for making an informed decision that protects your company from a data breach.
Here are answers to some of the most common questions about professional hard drive destruction.
Do I Really Need Professional Destruction for SSDs?
Yes, absolutely. Attempting to wipe a Solid-State Drive (SSD) using legacy software designed for traditional Hard Disk Drives (HDDs) creates a significant security vulnerability. SSDs manage data through a process called wear-leveling, which distributes data evenly across memory cells to prolong the drive's life. While beneficial for performance, this process complicates secure data erasure.
Wear-leveling can leave behind inaccessible data remnants that standard wiping utilities may not be able to locate or overwrite. The only method to ensure 100% data removal from an SSD is physical destruction, as it bypasses the drive's complex internal architecture entirely.
What Is a Certificate of Destruction and Why Is It Important?
A Certificate of Destruction is your official, legally-defensible proof that you disposed of data-bearing assets securely and in compliance with all applicable regulations. It provides a critical audit trail, demonstrating that your organization exercised due diligence in protecting sensitive information.
To be effective, a proper certificate must contain specific details that will hold up under scrutiny.
- Unique Serial Numbers: A complete inventory of the serial numbers for every individual drive destroyed.
- Method of Destruction: A clear description of how the drives were destroyed (e.g., physical shredding to a specific particle size).
- Chain of Custody Details: A log documenting the transfer of custody from your facility to the point of destruction.
- Date and Location: Confirmation of when and where the destruction took place.
Without this level of detail, your business is left exposed during a compliance audit or legal proceeding.
A Certificate of Destruction is not just paperwork; it is a critical liability shield. It formally transfers the responsibility for the destroyed data from your organization to the certified destruction vendor, protecting you from future claims of improper data handling.
Is On-Site or Off-Site Destruction Better for My Business?
The optimal choice between on-site and off-site destruction depends on your organization's internal security policies, budget, and operational constraints. Each service model offers distinct advantages.
On-site destruction involves a mobile shredding vehicle visiting your location. This offers the highest level of security and transparency, as you can witness the process directly. For businesses in highly regulated sectors like healthcare or finance, this is often a mandatory requirement to ensure immediate verification and peace of mind.
Conversely, off-site destruction involves the secure transport of your drives in locked containers to a certified destruction facility. This method is typically more cost-effective and efficient for large quantities of media, as the vendor can leverage larger, more powerful industrial equipment. If you choose this option, it is imperative to partner with a NAID AAA Certified vendor who can provide a flawless, documented chain of custody from collection to final disposal.
Ready to implement a secure, compliant, and responsible data destruction plan for your business? At Atlanta Computer Recycling, we provide certified hard drive destruction services tailored to the needs of Atlanta-area businesses, hospitals, and schools. Contact us today to ensure your sensitive data is gone for good. Learn more at https://atlantacomputerrecycling.com.