Compliant IT Disposal Atlanta GA: A 2026 Guide for Your Business
As a business leader in Atlanta, whether you're overseeing a healthcare clinic in Sandy Springs or a growing tech firm in Midtown, retiring old IT equipment is a critical security function, not just a logistical task. A robust, compliant strategy for IT disposal in Atlanta, GA is essential to protect your organization from significant fines, reputation-damaging data breaches, and regulatory non-compliance.
This guide provides the actionable framework for a secure and defensible IT Asset Disposition (ITAD) program.
Why Compliant IT Disposal Is a Business Imperative
The old server in a storage closet or the stack of desktops replaced last quarter aren't just occupying valuable space—they represent a significant security liability. An improperly sanitized hard drive or a "recycled" server can become a direct conduit to a catastrophic data breach, exposing your company's sensitive client data, financial records, or proprietary trade secrets.
The consequences extend far beyond data loss.
For any Atlanta-based company, particularly those in regulated industries like healthcare, finance, or government contracting, the stakes are exceptionally high. A single oversight in your disposal process can trigger severe penalties under frameworks like HIPAA.
A single compliance failure can dismantle years of cultivated customer trust. Viewing IT asset disposition (ITAD) as a core security function—rather than just a recycling task—is the first step toward safeguarding your business's most critical asset: its data.
The Growing Demand for Secure ITAD
The need for professional, secure ITAD services is expanding rapidly. The global IT Asset Disposition market, valued at $18.61 billion in 2025, is projected to reach $38.22 billion by 2034, growing at an impressive 8.3% compound annual rate. This growth is driven by stricter data privacy regulations, accelerated technology refresh cycles, and an increased focus on corporate social responsibility.
This market trend confirms that forward-thinking companies now integrate secure disposal into their risk management strategies. Here’s why a compliant process is no longer optional:
- Protecting Sensitive Data: It begins and ends with ensuring every byte of proprietary and client information is forensically destroyed, making a breach impossible.
- Maintaining Legal Compliance: Adherence to federal and Georgia-specific regulations is the only way to avoid costly fines and legal challenges.
- Upholding Brand Reputation: Demonstrating to clients and partners that you prioritize data security builds a level of trust that marketing initiatives alone cannot achieve.
- Promoting Environmental Stewardship: Responsible e-waste recycling ensures hazardous materials are kept out of landfills. You can learn more about the environmental impact of electronic waste and understand its importance.
This guide will walk you through establishing a defensible ITAD strategy, transforming a potential liability into a secure, managed process for your Atlanta organization.
Understanding Your Legal Obligations in Georgia
Navigating the regulatory landscape for IT disposal can feel complex, but for any Atlanta business, it is a mission-critical task. Your legal responsibilities are not a generic checklist; they are determined by the specific type of data your organization handles.
For example, a law firm in Buckhead retiring servers containing privileged client information faces a different regulatory framework than a hospital system decommissioning patient check-in kiosks across metro Atlanta. The first step toward a secure and compliant IT disposal process in Atlanta, GA, is to identify which regulations apply to your business operations.
Key Federal Regulations You Can't Ignore
Several major federal laws establish the standards for data protection and carry severe consequences for non-compliance. Violations can lead to crippling fines, mandatory public breach notifications, and reputational damage that is difficult to repair. These are not suggestions—they are legal mandates.
Key regulations include:
- HIPAA (Health Insurance Portability and Accountability Act): This is the paramount regulation for any healthcare provider, insurer, or business associate handling Protected Health Information (PHI). If your retired equipment contains patient records, billing data, or any identifying health information, you are legally bound by HIPAA's strict data destruction rules. Our guide explains more about how IT requirements intersect with HIPAA compliance.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions—including banks, credit unions, and investment firms—are governed by GLBA. The law mandates that these companies safeguard consumers' "nonpublic personal information" (NPI) and maintain a documented plan for its secure disposal.
- FACTA (Fair and Accurate Credit Transactions Act): This law’s Disposal Rule applies to nearly every business. If your organization handles consumer reports or any documents with sensitive financial details, FACTA obligates you to take "reasonable measures" to destroy that data before disposing of the device.
Failure to meet these standards can be a costly error. Beyond specific federal laws, a comprehensive understanding of regulatory compliance is fundamental for any company disposing of technology assets.
Georgia's E-Waste and Data Disposal Rules
While federal laws focus on protecting the data, Georgia's state and local regulations dictate how you must manage the physical hardware. The state has specific rules designed to prevent the hazardous materials in electronics from contaminating landfills.
In Georgia, it is illegal for businesses to dispose of e-waste in municipal solid waste landfills. You cannot simply discard old computers, monitors, or servers in a commercial dumpster.
This regulation is rooted in the federal Resource Conservation and Recovery Act (RCRA), which holds your business—the "waste generator"—liable for its hazardous materials from "cradle to grave." This liability does not transfer when the equipment is picked up. If your old assets are disposed of improperly by a vendor, your company remains legally responsible.
This is a primary driver behind the booming Enterprise IT Asset Disposition market. Valued at $8.42 billion in 2025, it’s projected to reach $14.9 billion by 2029, fueled by a sharp focus on compliance and avoiding the astronomical costs of data breaches—estimated at a global $10.5 trillion.
For any business in the greater Atlanta area, partnering with a certified ITAD provider is not just a best practice; it is an essential component of a comprehensive risk management strategy. A certified vendor ensures your electronics are managed in full compliance with both data security laws and Georgia's environmental mandates, providing the necessary documentation to prove it.
Implementing Ironclad Data Destruction Methods
Understanding regulations is the first step; effective implementation is what ensures compliance. For any Atlanta organization, this means guaranteeing that every byte of sensitive data is rendered completely unrecoverable. Simply deleting files is insufficient and leaves your business exposed. The goal is to employ forensically sound methods that make data recovery impossible.
This is not a checkbox item for compliance; it's about building a digital fortress around your proprietary information. The objective is to make it physically and digitally impossible for unauthorized parties to access retired data. This is a non-negotiable component of any compliant IT disposal program in Atlanta, GA.
The Gold Standard: Data Wiping
For functional hard disk drives (HDDs), the undisputed industry benchmark is DoD 5220.22-M 3-pass data wiping. This Department of Defense standard is a software-based process that overwrites every sector of a drive with specific patterns three separate times.
The process is methodical:
- Pass 1: Writes a specific character (e.g., a zero) across the entire drive.
- Pass 2: Writes the character's complement (e.g., a one).
- Pass 3: Writes random characters and verifies the wipe was successful.
This method is the digital equivalent of shredding data at the binary level, making it unrecoverable even with advanced forensic tools. It is the ideal approach for assets intended for resale or redeployment, as it preserves the hardware's value while guaranteeing complete data sanitization. This method is designed specifically for traditional magnetic HDDs.
When Physical Destruction Is The Only Answer
In certain scenarios, software-based wiping is not feasible or sufficient. Physical destruction becomes necessary to guarantee data elimination, especially for:
- Solid-State Drives (SSDs): SSDs use wear-leveling technology that distributes data across memory chips, making it nearly impossible for software to guarantee every block has been overwritten.
- Damaged Hard Drives: If a drive is non-operational and cannot be powered on, wiping software cannot be executed.
- Optical Media: CDs, DVDs, and backup tapes cannot be "wiped" and must be physically destroyed.
Physical shredding utilizes industrial-grade equipment to grind drives and other media into small, mangled fragments of metal and plastic. This process completely obliterates the device and its data, offering absolute certainty of destruction. For more details, our guide on how to properly destroy old hard drives provides an in-depth look.
To help you select the appropriate method for your assets, here is a summary of the two primary approaches.
Data Destruction Methods At a Glance
| Method | Process | Best For | Key Benefit |
|---|---|---|---|
| DoD 3-Pass Wiping | Software overwrites data in three sequential passes. | Functional, magnetic HDDs intended for remarketing. | Preserves the hardware's value while ensuring data is unrecoverable. |
| Physical Shredding | Industrial machinery grinds media into small fragments. | SSDs, damaged drives, optical media, and end-of-life assets. | Provides absolute, verifiable proof of destruction for any media type. |
The optimal method depends on the media type and your organization's goals for the asset, such as value recovery or simple disposal.
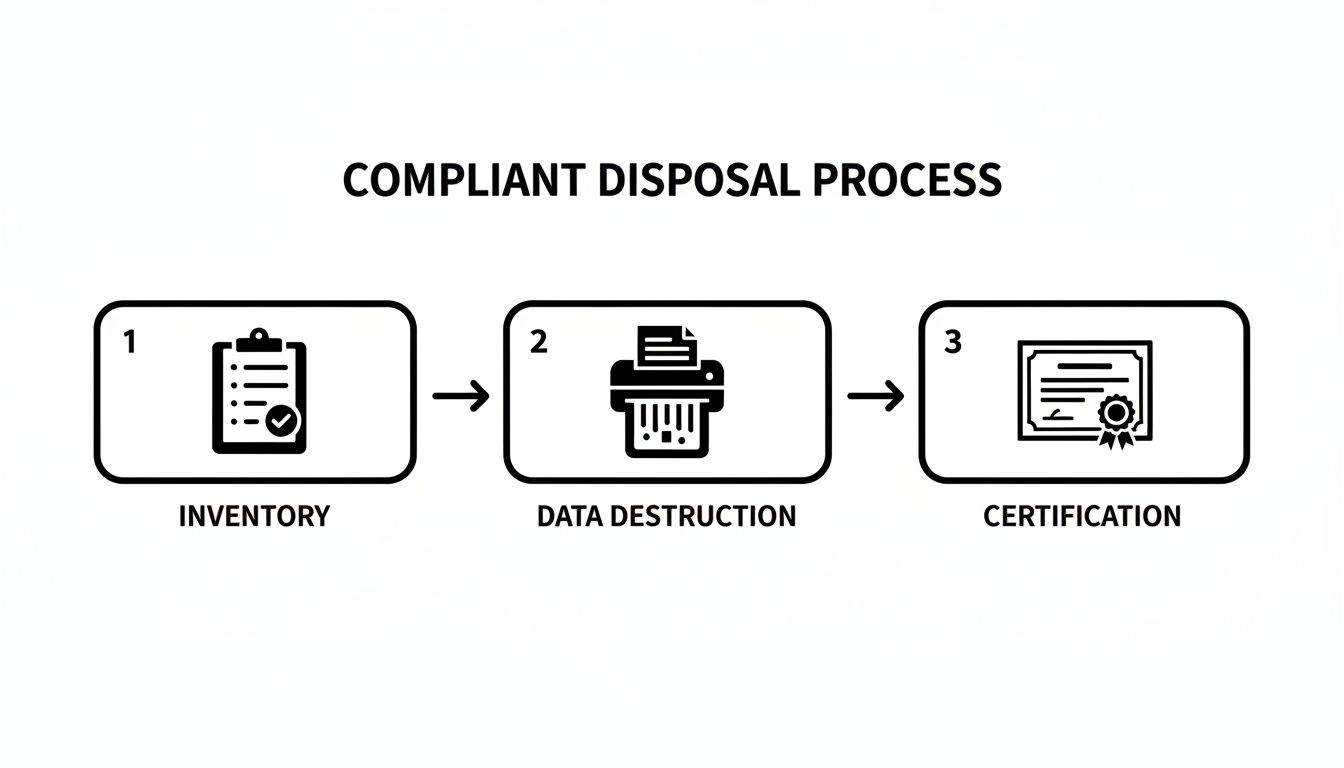
As this flowchart illustrates, compliant disposal is a managed system, not a one-time event, culminating in auditable proof of compliance.
The Importance of Documentation
Regardless of the method used, the process is incomplete without proper documentation. Your chain of custody and Certificates of Destruction are your most valuable tools for proving compliance.
Chain of custody is the unbroken paper trail documenting every touchpoint for every asset, from the moment it leaves your facility. It relies on serialized tracking to ensure complete accountability.
Upon completion of destruction, your ITAD partner must issue a Certificate of Destruction. This legally binding document is your official, auditable proof that data was destroyed in accordance with all relevant regulations. It lists asset serial numbers, the method used, and the date of destruction. In the event of an audit, this certificate is your definitive proof of compliance.
Making Asset Removal and Logistics Work for You
The physical logistics of removing retired IT equipment from your facility can be a significant operational challenge. Without proper planning, it can disrupt your entire business. For a busy hospital or a downtown Atlanta law firm, a chaotic pickup is more than an inconvenience—it's a security risk and a major productivity drain.
The goal is a seamless process. A professional ITAD partner coordinates with your team to ensure the removal is nearly invisible to your daily workflow. It should be a quiet, efficient operation where every asset is accounted for, securely packed, and transported without impeding your employees or business functions.
Planning for Zero Disruption
A smooth pickup is the result of a well-executed plan. A professional ITAD provider will develop a project plan with you that is tailored to your facility's unique requirements. This is particularly crucial for businesses seeking compliant IT disposal in Atlanta, GA, where every minute of operational uptime is valuable.
For instance, a large school district may need to refresh thousands of computers across multiple campuses during a short summer break. The vendor must operate within a tight window, coordinating with facilities staff and deploying an appropriately sized team to handle the high volume efficiently.
Alternatively, consider a corporation consolidating two downtown offices. The logistics involve booking freight elevators, navigating busy loading docks, and managing city traffic—all while minimizing disruption to other building tenants.
The true measure of a successful IT asset removal is not just hauling away old equipment. It's executing a plan with surgical precision, respecting your workspace, schedule, and security protocols from start to finish.
Best Practices for On-Site De-Installation and Packing
To ensure your asset removal is both efficient and secure, we recommend these proven best practices:
- Schedule Pickups During Off-Hours: Arranging removals after business hours or on weekends is the most effective way to avoid disrupting employees and clients.
- Establish a Secure Staging Area: Designate a locked room or a cordoned-off space where de-installed assets can be safely consolidated and inventoried before the pickup team's arrival.
- Coordinate with Building Management: Inform your property manager and reserve freight elevators and loading dock access well in advance to prevent last-minute delays.
- Insist on Professional Packing: Your ITAD partner should arrive with sturdy, sealed containers, pallets, and shrink-wrap to protect every asset and ensure no components are lost in transit.
Following these steps dramatically reduces the project's impact on your business operations. You can see how a professional team manages these logistics by reviewing our e-waste pickup services in Atlanta, GA.
Taking on a Data Center Decommission
Decommissioning a data center is the ultimate logistical challenge, far more complex than a standard office cleanout. With Metro Atlanta being a top-tier data center market, the demand for systematic, professional decommissioning grows annually as facilities upgrade.
A phased approach is critical. The process involves methodically de-racking servers, removing network gear, dismantling heavy cooling infrastructure, and managing bulky UPS systems. These facilities house not only valuable equipment but also hazardous materials like lead-acid batteries and refrigerants that require specialized handling under RCRA guidelines.
A successful data center project always includes:
- A Detailed Project Plan: Outlining every phase, from power-down sequences to the final site sweep.
- Specialized Teams: Technicians experienced in handling fragile server and network hardware, not just general movers.
- Meticulous Asset Tracking: Strict inventory control with serialized tracking for every server, switch, and PDU leaving the facility.
- Secure Transportation: Using locked, GPS-tracked trucks to guarantee a secure chain of custody from your site to the processing facility.
With the right partner, what appears to be a logistical nightmare becomes a managed, auditable, and secure project, turning a potential crisis into a smooth transition.
How to Choose the Right Atlanta ITAD Partner
Selecting a vendor for your IT asset disposition is the most critical decision in this process. You are not just finding someone to remove old electronics; you are partnering with a certified expert who will protect your company from data breaches, legal penalties, and reputational harm.
The right partner acts as an extension of your IT and compliance departments, understanding the gravity of your security responsibilities. A truly compliant IT disposal partner in Atlanta, GA, will help you navigate this complex field, not just complete a one-off transaction.
Non-Negotiable Vendor Certifications
The vetting process must begin with certifications. These are not merely logos for a website; they are hard-earned credentials that prove a vendor meets rigorous, third-party audited standards for data security, environmental responsibility, and operational excellence.
In the U.S. ITAD industry, two certifications are the gold standard:
- R2v3 (Responsible Recycling): This framework ensures electronics are managed safely and sustainably. It enforces strict requirements for data sanitization, testing, and tracking all materials through the downstream recycling chain, ensuring total accountability.
- e-Stewards: Often considered the most stringent standard, e-Stewards maintains a zero-tolerance policy for exporting hazardous e-waste to developing nations. It also mandates robust data security protocols and thorough vetting of all downstream partners.
Do not take a vendor's word for it. Always request their current certificate and verify its authenticity in the official R2 or e-Stewards directory. This simple step separates true professionals from unqualified operators.
The Vendor Vetting Checklist
Once you have confirmed a potential partner holds the necessary certifications, it is time to dig deeper. This decision has long-term implications, so a thorough evaluation is crucial. Use these points to guide your questions and ensure you are making a sound choice.
Proof of Adequate Insurance
Request their Certificate of Insurance. Look for Data Breach and Errors & Omissions coverage of at least $1 million. This provides a financial backstop in case of an incident. General liability coverage alone is insufficient.
A Transparent Audit Trail
Confirm they can provide a complete, serialized chain-of-custody from pickup to final disposition. They must track every asset by its serial number, documenting each touchpoint to create an unbroken, auditable record.
Clear Data Destruction Protocols
Ask them to detail their data destruction methods. Do they offer both DoD 5220.22-M wiping and physical shredding? Crucially, will they provide a detailed Certificate of Destruction listing the serial number of every drive processed?
Downstream Transparency
This is a critical point. Ask directly: "Who are your downstream partners, and are they also certified?" A certified ITAD company is required to vet its partners, but posing the question demonstrates your understanding of the risks associated with illegal e-waste exporting.
Focusing on these key areas will enable you to properly vet any vendor. For a more comprehensive guide, see our article on how to choose an electronic waste recycling company for your business.
Setting Realistic Expectations
Understanding typical costs and timelines is essential for effective budgeting and planning. Pricing is often contingent on the volume and type of equipment, logistics (such as stairs or de-installation), and the specific data destruction services required. Some vendors may offer value recovery for newer assets, which can help offset your costs. Always request a detailed, itemized quote.
The sheer volume of retired equipment is a growing challenge for businesses globally. E-waste is one of the fastest-growing waste streams on the planet, with a staggering 62 million metric tons generated in 2022 alone. That figure is projected to reach 82 million metric tons by 2030, driven largely by computers and laptops retired from enterprise environments like yours. You can explore these IT asset disposition trends to understand why a robust plan is so vital.
Your IT Disposal Questions Answered
Even with a detailed plan, practical questions inevitably arise when it's time to retire IT assets. We consistently hear the same concerns from businesses across Atlanta, ranging from disposal costs to handling specific equipment types.
Here are straightforward answers to the questions our team fields daily, based on our experience helping local companies navigate this process.
What Is the Difference Between Recycling and Compliant ITAD?
This is the most critical distinction. Standard e-waste recycling focuses on one objective: breaking down equipment into commodities like plastic and metal to divert it from landfills. It is an environmental service, but its scope ends there.
Compliant IT Asset Disposition (ITAD), in contrast, is a security-first process. While it incorporates responsible recycling, its primary purpose is to mitigate business risk. This involves:
- Secure Data Destruction: Using certified methods like DoD 3-pass wiping or physical shredding to ensure data is permanently destroyed.
- Chain-of-Custody Tracking: Creating an audit trail by serial number for every asset, from your facility to its final disposition.
- Certified Compliance: Providing proof, such as a Certificate of Destruction, that you have met your legal obligations under regulations like HIPAA or FACTA.
For any business handling client lists, financial records, or patient data, simple e-waste recycling is an inadequate solution. Compliant ITAD is the only process that effectively eliminates the legal and financial risks of a data breach.
Can My Small Business Get the Same Level of Service as a Large Corporation?
Yes, absolutely. A professional ITAD partner’s services are designed to be scalable. The core commitments to security, chain-of-custody, and certified data destruction remain the same, whether we are collecting a dozen laptops from a law firm in Decatur or decommissioning an entire data center in Sandy Springs.
The logistics are tailored to the scale of your project, not the quality of the service. You receive the same meticulous documentation and certified destruction, ensuring your business is fully protected, regardless of its size.
How Much Does Compliant IT Disposal in Atlanta Typically Cost?
There is no flat rate, as every project is unique. The final cost depends on several key variables, and understanding them will help you evaluate any quote you receive.
The main cost drivers include:
- Volume and Type of Assets: The quantity and weight of items (e.g., a pallet of laptops versus heavy server racks) affect labor and transportation costs.
- Data Destruction Method: On-site hard drive shredding has a different cost structure than software-based wiping performed at a secure facility.
- Logistical Complexity: Projects requiring on-site de-installation, navigating buildings without elevators, or after-hours service in downtown Atlanta involve more labor and planning.
- Value Recovery: Newer equipment that can be refurbished and resold can generate a return. This value can often offset—or in some cases, completely cover—the cost of the service.
Always request an itemized quote. A transparent partner will explain each line item, so you understand the complete cost structure.
What Happens if a Device Can Be Reused?
When we identify a device with potential resale value, security remains the top priority. The hard drive or SSD is professionally sanitized using certified data-wiping software. Only after we have verified that 100% of the data is destroyed do we consider the asset for refurbishment.
If the equipment can be remarketed, it creates a win-win scenario. It extends the hardware's useful life, which benefits the environment. For your business, it generates a revenue stream through value recovery that directly reduces the net cost of your ITAD project.
What Are My Responsibilities for Data Center Waste?
Beyond servers and switches, data centers contain a range of other regulated materials. Under the Resource Conservation and Recovery Act (RCRA), your business retains "cradle to grave" liability for all hazardous waste it generates.
This often includes materials you might not immediately consider:
- Lead-Acid and Lithium-Ion Batteries: From Uninterruptible Power Supply (UPS) systems.
- Refrigerants: Coolants from CRAC units are regulated under the Clean Air Act.
- Diesel and Oils: From backup generators and associated systems.
Engaging an ITAD vendor experienced in full data center decommissioning ensures these waste streams are managed and documented correctly, shielding your organization from significant legal liability.
Do I Need to Wipe Drives Before You Pick Them Up?
No, and in fact, we strongly recommend against it. Allow our team to manage this critical step. Certified data destruction is a core component of our service, and there are two key reasons why it is better to entrust it to a professional partner.
First, we use validated software and hardware, providing a level of assurance that an internal "format" command cannot match. More importantly, we issue a Certificate of Destruction. This auditable, third-party document serves as your official proof of compliance—a level of validation that an internal IT log cannot provide in an audit.
Ready to ensure your IT disposal process is secure, compliant, and hassle-free? Atlanta Computer Recycling offers end-to-end ITAD services for businesses across the metro area. We provide certified data destruction, detailed reporting, and responsible recycling to protect your data and your reputation. Contact us today for a transparent quote at https://atlantacomputerrecycling.com.