Atlanta Computer Recycling: A Strategic Guide for Commercial ITAD

For any IT Manager, CIO, or Compliance Officer in Atlanta, managing end-of-life technology isn't just a cleanup job—it's a critical component of corporate risk management. A strategic approach to Atlanta computer recycling is what stands between your proprietary data and a potential breach. It’s about protecting your enterprise, ensuring regulatory compliance, and meeting corporate sustainability goals. This guide outlines how to build a secure and compliant IT Asset Disposition (ITAD) plan that works for your business.
Developing Your Corporate ITAD Strategy in Atlanta
Whether you're a healthcare system in Midtown, a financial institution in Buckhead, or a logistics company near Hartsfield-Jackson, a formal IT Asset Disposition (ITAD) strategy is non-negotiable. This isn't about calling an e-waste company when a storage closet gets full. It's about transforming a significant data liability into a secure, documented, and value-driven business process.
A robust ITAD plan integrates data security, environmental responsibility, and financial recovery from day one. Without it, your organization is exposed to severe risks, from catastrophic data breaches and brand damage to steep non-compliance penalties.
Effective execution requires alignment between your IT, finance, and legal departments. Your primary objectives should be clearly defined:
- Absolute Data Security: Eradicating or destroying 100% of sensitive corporate information on every retired asset. No exceptions.
- Regulatory Compliance: Meeting and documenting adherence to industry-specific mandates like HIPAA, SOX, or GLBA.
- Maximum Value Recovery: Identifying all equipment that can be refurbished and resold to generate a positive return on investment and offset disposition costs.
- Environmental Responsibility: Ensuring every component is recycled ethically through a certified, zero-landfill process.
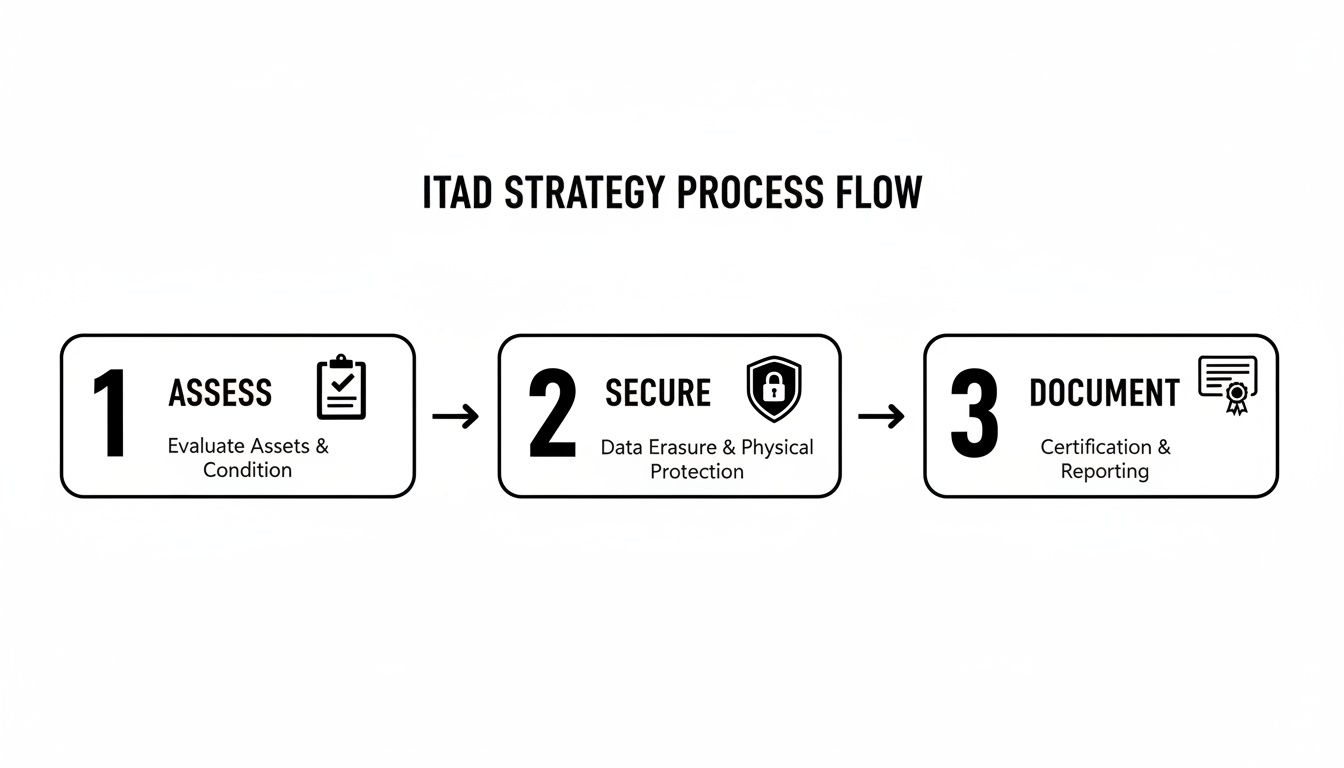
The goal is a repeatable, auditable, and defensible process. You assess your asset portfolio, secure the data, and document every step for your compliance and audit records.
Following a defined structure like this ensures no critical security or compliance step is missed as your IT assets reach their end of life.
The Growing Need for Professional ITAD
The challenge of managing electronic waste has evolved significantly. The e-waste recycling industry began formalizing with the Resource Conservation and Recovery Act (RCRA) in 1976.
By 2007, the EPA reported over 63 million computers were being discarded annually in the U.S. This staggering figure highlights why professional ITAD services have become indispensable, particularly in a major commercial hub like Atlanta.
When developing your corporate ITAD strategy, engaging a specialist partner is often the most efficient path. Analyzing how professional third-party logistics solutions manage complex asset logistics provides a solid model for operational excellence. Ultimately, your strategy must be clear and enforceable to protect your enterprise. You can learn more about how we manage secure IT asset disposal to see how a professional partnership delivers security and peace of mind.
Mastering Your Pre-Disposal Inventory and Planning
Here's a lesson learned from years of managing enterprise-level projects: a successful Atlanta computer recycling initiative is won or lost before a single piece of equipment is unplugged. The initial phase—meticulous inventory and strategic planning—is where you mitigate security risks and logistical bottlenecks. Rushing this stage is a recipe for chaos, unforeseen costs, and potential data exposure.
Your first task is to create a comprehensive asset log. This is more than a simple headcount of desktops. It's a detailed manifest that informs every subsequent decision, from the method of data destruction to the potential for value recovery. Get this right, and you establish the foundation for a seamless, auditable, and secure disposition process.
Building Your IT Asset Disposition Log
Creating this log requires precision. Each entry must capture the essential details your ITAD partner and internal compliance teams will require.
For each asset, your inventory list should include:
- Asset Tag or Serial Number: The unique identifier for tracking the device from your facility to final disposition.
- Device Type: Be specific. Is it a Dell Latitude 7420 laptop, a Cisco Catalyst switch, or an HP ProLiant server? The model details matter for valuation.
- Physical Location: Note the department, floor, or data center row where the asset is located.
- Data Sensitivity Level: Assign a risk classification (e.g., Low, Medium, High) based on the type of corporate data it stored.
- Condition and Age: A quick assessment of whether the device is functional and holds potential resale value.
This level of detail ensures nothing is overlooked. It’s the difference between a controlled, secure process and a haphazard cleanout where a server drive containing sensitive customer data slips through the cracks. This systematic approach is a cornerstone of professional IT asset management.
Segregating Assets for Security and Value
With a complete inventory, the next strategic move is to segregate assets into logical groups. This step is critical for both security and financial optimization.
Sort your assets based on two primary criteria: data sensitivity and remarketing potential.
A healthcare system in Atlanta, for example, would create a high-priority group for any laptop, server, or hard drive that ever stored Protected Health Information (PHI). These assets are immediately designated for the most secure data destruction method—likely physical shredding—to completely eliminate any risk of a data breach.
By proactively identifying and segregating high-risk assets, you not only satisfy compliance mandates like HIPAA but also create an auditable trail that demonstrates due diligence. This simple act of sorting is one of your most powerful risk mitigation tools.
Conversely, a technology company might have a batch of two-year-old developer MacBooks that hold no sensitive data. These would be categorized for "remarketing." Since they retain significant resale value, they are ideal candidates for DoD-standard data wiping, which sanitizes the drives while preserving the hardware for refurbishment and resale, maximizing your financial return.
Securing Internal Buy-In
Finally, a successful ITAD plan requires cross-departmental collaboration. An IT manager cannot execute a large-scale disposition project in a vacuum. You need alignment from key stakeholders who control budgets, facilities, and legal oversight.
Before proceeding, schedule a brief planning session with representatives from key departments:
- Finance: They need to understand the costs, the potential for value recovery, and the significant financial risks of non-compliance.
- Legal/Compliance: This team will want to validate that your proposed data destruction methods and documentation meet all regulatory and corporate governance requirements.
- Facilities Management: These are your logistical partners. They help coordinate site access, freight elevator usage, and staging areas for the pickup crew.
Presenting your detailed inventory and segregation plan demonstrates thorough preparation. It proves you've considered the security, financial, and logistical angles, making it far easier to get the necessary approvals to engage a trusted Atlanta computer recycling partner.
Choosing the Right Data Destruction Method
Once your inventory is sorted, you're at a critical decision point: selecting the method for permanent data eradication. This is not merely a technical task; it is the core of your security strategy. For any Atlanta business handling sensitive information—from financial records to client PII—flawless data destruction is non-negotiable. A single misstep can lead to a devastating data breach, erasing customer trust and incurring severe regulatory fines.
The decision balances security requirements, asset value, and compliance mandates. In professional Atlanta computer recycling, two industry-standard methods dominate: software-based data wiping and physical destruction. Each serves a specific purpose, and understanding their applications is key to an intelligent ITAD strategy.
When Data Wiping Makes Financial Sense
Consider a fleet of recent-model laptops or a high-performance server. While they may be at the end of their lifecycle for your company, the hardware itself retains significant market value. Physically destroying these assets would be destroying capital. This is where DoD 5220.22-M 3-pass data wiping is the optimal solution.
This process utilizes certified software to overwrite every sector of a hard drive with a pattern of ones, zeros, and random characters in three distinct passes. The result is a completely sanitized drive, rendering the original data forensically irrecoverable.
Consider this real-world scenario: A growing tech firm in Midtown is refreshing its sales team's two-year-old laptops.
- The devices are modern, high-spec, and fully functional.
- They contain sensitive sales forecasts and client data.
- Shredding them would mean forfeiting thousands of dollars in resale value.
By choosing DoD-standard wiping, the firm ensures all proprietary data is irretrievably destroyed. The laptops can then be safely refurbished and sold on the secondary market, generating revenue that offsets the cost of the entire recycling project. This is the ideal approach when you need to preserve hardware value without compromising on data security.
The Finality of Physical Shredding
Conversely, there are situations where data wiping is not the appropriate solution. The hardware may be too old, physically damaged, or your industry’s compliance framework may mandate complete physical elimination. For obsolete hard drives, failed solid-state drives (SSDs), or assets from high-security sectors, physical destruction is the only acceptable option. Shredding offers zero ambiguity—the device is pulverized into small fragments, making data reconstruction physically impossible.
Imagine a financial services company in Buckhead decommissioning a legacy data center. Its servers hold decades of sensitive client financial data.
- The hard drives are old and have no remarketing value.
- Regulatory compliance demands the highest possible level of data security assurance.
- The risk of even a single data fragment surviving is unacceptable.
Shredding is the only logical choice. The drives are fed into industrial shredders, and the resulting fragments are mixed with other scrap metal. This method provides absolute peace of mind and is often the required standard for organizations in healthcare, finance, and government. It is the definitive end for high-risk data.
The decision between wiping and shredding is a straightforward risk-versus-reward calculation. If an asset has remarketing value and data can be securely erased to a certified standard, wiping is the financially prudent choice. If the data risk is absolute or the hardware has no value, shredding is the only defensible path.
To help clarify the trade-offs, here is a direct comparison.
Data Wiping vs. Physical Shredding: A Comparison
| Attribute | DoD 5220.22-M Data Wiping | Physical Shredding |
|---|---|---|
| Security Level | High (forensically unrecoverable) | Absolute (media is destroyed) |
| Hardware Reuse | Yes – preserves asset value | No – hardware is destroyed |
| Best For | Newer laptops, servers, functional HDDs | Old/damaged drives, SSDs, high-risk data |
| Compliance | Meets most compliance standards | The highest standard for HIPAA, FACTA, etc. |
| Verification | Certificate of Data Erasure | Certificate of Destruction |
| Cost-Effectiveness | Can be offset by resale value | A direct cost, but necessary for high risk |
Ultimately, selecting the right method is about aligning your actions with your corporate risk tolerance and financial objectives.
For Atlanta businesses evaluating these options, it is vital to partner with a recycler who not only offers both services but also provides transparent, auditable documentation for your chosen method. To see how these processes integrate into a comprehensive security framework, explore the details of our certified secure data destruction services. We deliver documented solutions tailored to your organization's specific risk profile and financial goals, ensuring your Atlanta computer recycling program is both secure and sound.
Executing On-Site Logistics in Metro Atlanta
A well-defined ITAD plan is essential, but executing it without disrupting daily business operations is the true measure of success. The physical removal of retired IT assets—the logistics—is where a professional partnership demonstrates its value. Seamless execution ensures your equipment is transported from your facility to our processing center securely and efficiently, with minimal impact on your team's productivity.
Local expertise in the Atlanta metro area is a significant advantage. The logistics for a high-rise in Downtown Atlanta with stringent security protocols and limited freight elevator access are entirely different from a sprawling corporate campus in Alpharetta with dedicated loading docks. A partner who understands the local environment can anticipate and plan for these challenges.
Our professional on-site services are designed to manage all the heavy lifting. This includes everything from the careful de-installation of servers from live racks to securely packing and palletizing all assets for safe, insured transport.
Preparing for a Smooth Pickup
A small amount of preparation on your end can dramatically increase the efficiency of the handover process. Taking a few key steps before our team arrives prevents last-minute issues and allows our crew to work quickly and safely.
- Designate a Staging Area: Clear a secure, accessible space to consolidate your inventoried assets. An empty office, a corner of your warehouse, or a conference room near an exit is ideal.
- Confirm Site Access: Communicate any specific instructions, such as loading dock hours, security check-in procedures, or the need to reserve an elevator. These details are crucial for our logistics planning.
- Assign a Point of Contact: Designate one person from your team to meet our crew, verify the inventory against the work order, and sign off on the chain-of-custody transfer.
These simple measures are critical. A multi-floor office cleanout requires a different logistical approach than a single-room data center decommission. As a local provider specializing in Atlanta computer recycling, we have the operational flexibility to manage either scenario flawlessly.
A smooth pickup is not just about speed; it's about maintaining an unbroken chain of custody. By having all assets staged and inventoried, you ensure every device is accounted for from the moment it leaves your control—the critical first step in a secure and auditable disposition process.
The Value of Professional De-Installation
For complex hardware like data center equipment, professional de-installation is non-negotiable. Attempting to remove racked servers, switches, and SANs without the proper tools and expertise can lead to facility damage or employee injury. It is a specialized task best left to trained technicians.
A professional team arrives with all necessary equipment to:
- Safely power down and disconnect all units from the network.
- Carefully un-rack servers and networking gear.
- Organize and bundle cabling for recycling.
- Securely transport heavy equipment without damaging floors or doorways.
This professional handling not only ensures safety but also protects the potential remarketing value of your equipment. A server that has been professionally de-installed is far more likely to be suitable for refurbishment than one that has been mishandled.
Ensuring Compliance with Documentation and Chain of Custody
Once your assets are loaded and in transit, the process shifts to what is arguably the most critical phase for your compliance records: documentation. In regulated industries like healthcare and finance, an undocumented action is considered an action that never occurred. The paper trail is as crucial as the physical Atlanta computer recycling process, serving as your legal proof of due diligence.
This documentation shields your organization from the severe financial penalties and reputational damage of a data breach or environmental violation. It is your definitive answer to auditors, proving you executed every necessary step to protect sensitive data.
The Role of Chain of Custody
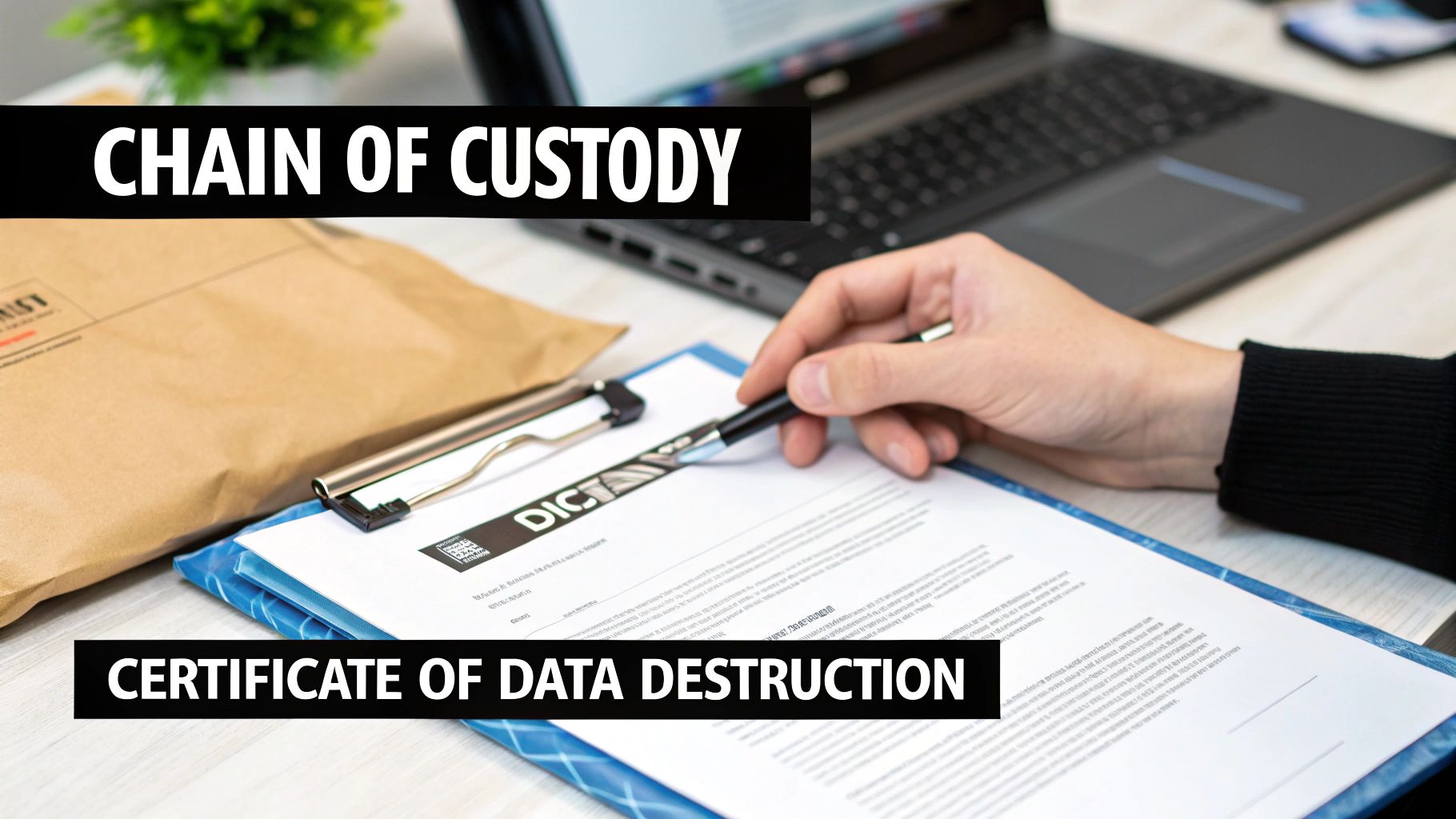
The moment our team signs for your inventory and it is loaded onto our secure, GPS-tracked vehicle, the chain of custody begins. This is an unbroken, chronological record that tracks every asset from your facility to its final disposition. It is the foundation of any defensible ITAD program.
A comprehensive chain-of-custody report clearly documents:
- Who handled the assets at each stage.
- What specific assets were processed, tracked by serial number.
- When each transfer of custody occurred.
- Where the assets were located at all times.
This meticulous tracking leaves no gaps where a device could go unaccounted for. For a hospital system disposing of laptops containing patient data, this level of accountability is essential for meeting strict HIPAA Security Rule requirements.
What Makes a Certificate of Data Destruction Valid
After the data on your drives has been wiped or physically shredded, you receive a Certificate of Data Destruction. This is the official document that formally transfers liability for the data from your organization to us. However, not all certificates are created equal.
A legitimate, audit-proof certificate must contain specific information to be valid under scrutiny. It is the final confirmation that your data was destroyed in accordance with industry-best practices.
Think of the Certificate of Data Destruction as the final receipt for your data security. It closes the loop on your IT asset's lifecycle and serves as the primary piece of evidence you'll present during a compliance audit to prove you met your legal obligations.
When you receive this document, verify that it includes these key elements:
- Unique Serial Numbers: A detailed list of the serial numbers from every single hard drive that was destroyed. A certificate without this is incomplete.
- Method of Destruction: A clear statement on how the data was destroyed—whether via DoD 5220.22-M wipe or physical shredding.
- Date and Location of Destruction: The specific date and the certified facility where the destruction took place.
- Authorized Signatures: Signatures from our authorized personnel, confirming the process was completed as stated.
This document is your essential proof of compliance and is vital for protecting your business. For a deeper look at this critical document, you can explore the components of a certified Certificate of Destruction and understand why the details are so important.
The Final Step: Recycling and Responsible Reuse
Once all sensitive data has been verifiably destroyed, your retired IT assets are ready for the final stage of their journey. This is where a company's commitment to corporate social responsibility is put into action. For any Atlanta business serious about its sustainability goals, this final step is a crucial piece of the ITAD puzzle.
The process begins with a simple question: can this device be refurbished for a second life, or has it reached its true end of life?
The Circular Economy in Action: Refurbishment and Reuse
For equipment with remaining operational life—such as recent-model laptops, servers, or networking hardware—reuse is always the highest priority. Extending the useful life of an electronic device is the most effective way to reduce its environmental impact. These assets undergo a rigorous process to prepare them for the secondary market.
- Testing and Grading: Every component, from the motherboard to the display, is thoroughly tested to determine its functional status and performance level.
- Minor Repairs and Upgrades: Technicians may replace a failing component or upgrade RAM or storage to enhance the device's value and utility.
- Cosmetic Refurbishment: The device is professionally cleaned and restored to make it market-ready.
By reintroducing this hardware into the market, we actively contribute to the circular economy. This reduces the demand for new manufacturing, which conserves immense amounts of energy and raw materials.
From E-Waste to Raw Commodities
When a device is obsolete, broken, or otherwise non-functional, it enters the de-manufacturing process. This is not simply shredding; it is a systematic dismantling of electronics into their base commodities. This ensures that hazardous materials are managed safely and valuable resources are recovered.
The process involves meticulously separating materials such as:
- Precious metals (gold, silver, palladium) from circuit boards.
- Aluminum and steel from computer chassis.
- Plastics from keyboards and monitor casings.
- Glass from screens.
This certified, zero-landfill recycling process is the final safeguard that prevents toxic materials like lead and mercury from contaminating local landfills and water systems. It is the critical final step that validates your environmental policy.
In Atlanta, this commitment to responsible e-waste management has a significant impact. Certified recyclers divert hundreds of millions of pounds of e-waste from landfills annually. These advanced systems process old electronics back into clean, raw commodities that re-enter the global supply chain, reducing the need for virgin material extraction. You can explore more about these large-scale recycling efforts to see their powerful impact firsthand.
Your Top Questions Answered
When navigating corporate IT asset disposition, many questions arise. Securing clear answers helps IT managers and business leaders across Atlanta plan their projects with confidence. Here are answers to the most common questions we receive.
What Does Commercial Computer Recycling in Atlanta Typically Cost?
The answer is: it depends on the specifics of your project. The final cost is influenced by a few key variables.
The volume and type of your inventory, the required on-site logistics—such as a full data center de-installation—and your chosen data destruction method all factor into the pricing. However, many of our core security services are often included at no additional charge.
For example, our standard DoD 5220.22-M 3-pass data wiping is typically included in our service. Furthermore, if your inventory includes newer, functional equipment, the value we recover from remarketing those assets can significantly offset or even entirely cover the recycling fees for the obsolete hardware. The best way to determine your cost is to provide an inventory list for a custom assessment.
How Can I Be Certain My Company's Data Is Secure?
This is the most critical question, and our entire process is built around providing that certainty. A reputable partner for Atlanta computer recycling doesn't just promise security—we prove it with a multi-layered, documented, and auditable system that mitigates risk at every stage.
Your data's security is guaranteed through an unbroken, documented chain of custody. This process includes secure, GPS-tracked transport from your facility, processing in our access-controlled centers, and official Certificates of Data Destruction for your compliance records.
Whether you choose software-based data wiping or physical shredding, the entire process is transparent and tracked. This provides you with the tangible proof required to satisfy both internal governance policies and external regulations like HIPAA or SOX.
What Types of Business Electronics Do You Accept?
As a dedicated commercial e-recycler, we are equipped to handle virtually any IT asset found in a corporate environment. We routinely manage equipment from complete office liquidations, complex data center decommissioning projects, and regular technology refresh cycles.
Our most commonly processed items include:
- Desktops, laptops, and servers
- Networking hardware such as switches, routers, and firewalls
- Data center equipment, including storage arrays and server racks
- Monitors, VoIP phones, and telecom systems
While we can manage nearly any commercial-grade electronic asset, we always recommend providing your specific inventory list in advance. This ensures we can plan for a smooth, efficient, and rapid pickup.
Ready to implement a secure, compliant, and responsible ITAD program for your business? The team at Atlanta Computer Recycling is here to guide you through every step. Contact us today for a no-obligation quote and consultation.