A Business Guide to IT Asset Disposal: Secure Data & Maximize Value
When your company’s technology reaches the end of its operational life, what happens next? A proper IT asset disposal strategy is what stands between your business and a potential data breach, ensuring you remain compliant and even helping you recover value from retired hardware. You wouldn't leave filing cabinets full of sensitive client documents in an old office, and the same rigorous logic must apply to your computers, servers, and hard drives.
What Is Strategic IT Asset Disposal?
Think of every piece of technology in your business as having a full life cycle—from procurement to retirement. IT Asset Disposal (ITAD) is the critical final stage of that life cycle. It is not simply about discarding old equipment; it's a structured business process for managing obsolete or unwanted hardware securely, legally, and in an environmentally sound manner.
This goes far beyond a simple trip to an electronics recycling center. A professional ITAD plan addresses several core business objectives at once, transforming a collection of potential liabilities into a well-managed operational process. For any Atlanta-based business, a formal ITAD program isn't just an IT task—it's a vital component of modern risk management and financial strategy.
The Core Drivers of Modern ITAD
A robust ITAD strategy is built on four key pillars. Neglecting any one of them exposes your organization to significant financial, legal, and reputational risks.
- Safeguarding Confidential Data: Every retired hard drive, server, or smartphone is a potential vector for a data breach. Proper ITAD ensures all sensitive corporate and customer information is permanently destroyed using certified data sanitization methods.
- Meeting Strict Compliance Regulations: Businesses in regulated sectors like healthcare (HIPAA) or finance (FACTA) face steep penalties for data mismanagement. A documented ITAD process provides an auditable trail to prove due diligence and maintain compliance.
- Upholding Environmental Responsibility: Electronics contain hazardous materials that can cause environmental damage if sent to a landfill. Responsible ITAD ensures obsolete devices are properly recycled according to all local and federal regulations, supporting corporate sustainability goals.
- Recovering Hidden Financial Value: Your retired equipment may no longer meet your operational needs, but it often retains significant market value. A strategic partner can refurbish and resell these assets, turning a depreciated cost center into a new revenue stream.
When you view ITAD as a strategic business function, it ceases to be a mere operational cost. Instead, it becomes a powerful tool for mitigating risk and recovering capital, ensuring an asset's retirement is as well-managed as its deployment.
The ultimate goal is to create a closed-loop system where technology is retired without ever compromising your security or compliance. This proactive approach protects your brand and your bottom line. Handled correctly, it also enhances your corporate social responsibility profile—a factor of growing importance to clients and stakeholders. To understand how this final stage is executed, you can explore the details of professional IT equipment recycling and its role in a comprehensive disposal plan.
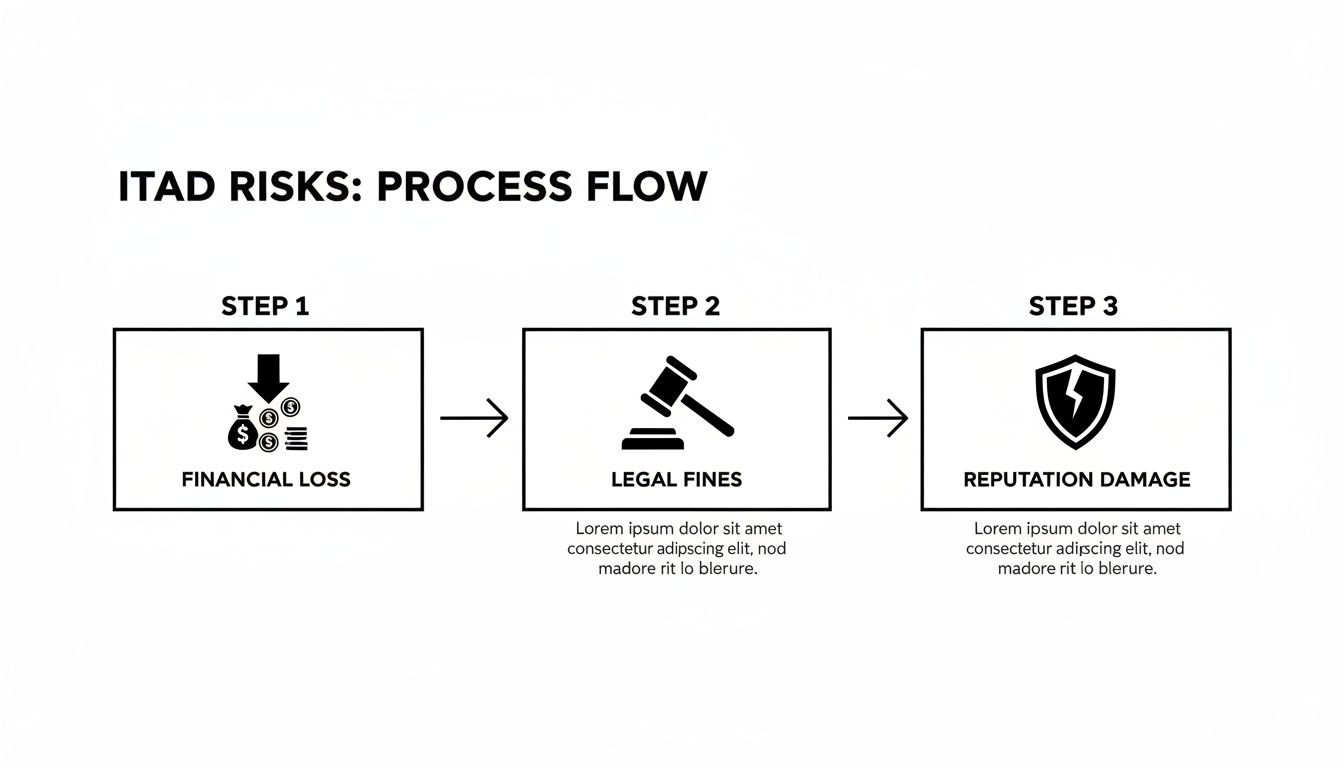
The Real Risks of Improper Disposal
Ignoring a formal IT asset disposal strategy is equivalent to locking your company's front door while leaving the server room wide open. This process is not about clearing out old equipment; it's a critical security function. Failing to manage this final stage of an asset's life invites serious financial, legal, and reputational disasters that can cause lasting damage to your business.
Consider a healthcare practice in Atlanta upgrading its server infrastructure. The old servers are stored in a back room and eventually given to a local scrap hauler. Months later, the practice is hit with crippling HIPAA fines because patient records were recovered from one of those inadequately wiped drives. This is not a far-fetched scenario—it is the reality for businesses that underestimate the resilience of stored data.
The High Cost of a Data Breach
A data breach traced back to improperly discarded hardware can be financially devastating. The average cost of a data breach continues to climb, with organizations spending millions on remediation, legal fees, and customer notifications. For small and mid-sized businesses, such an incident can be an existential threat.
Imagine a financial services firm whose entire reputation is built on trust and confidentiality. If client data is exfiltrated from a retired company laptop sold on a secondary market, the damage extends far beyond regulatory penalties. The loss of client trust can destroy the firm's brand and market position—a setback that could take years to overcome, if ever.
The greatest risk in IT asset disposal isn't the cost of doing it right; it's the catastrophic expense of getting it wrong. A single discarded hard drive can become a liability worth millions of dollars.
Navigating the Legal Labyrinth
For businesses operating in Atlanta, a complex web of federal and state regulations governs data protection and e-waste. Non-compliance is not a simple administrative error—it carries severe legal penalties. Understanding these obligations is the first step toward managing your risk profile.
Here are three key regulations every business leader should know:
- HIPAA (Health Insurance Portability and Accountability Act): This is non-negotiable for any organization handling protected health information. HIPAA requires that all patient data be rendered unreadable and indecipherable before the device it’s stored on is disposed of.
- FACTA (Fair and Accurate Credit Transactions Act): Aimed at preventing identity theft, FACTA mandates the proper disposal of consumer information. Any business handling credit reports, background checks, or similar data must securely destroy it.
- State and Local E-Waste Laws: Georgia has specific regulations for disposing of electronic waste to prevent hazardous materials from entering landfills. Businesses are responsible for ensuring their obsolete technology is managed in an environmentally compliant manner.
These regulations elevate IT asset disposal from a simple IT task to a legal necessity. For a deeper look at ensuring compliance for retired media, our guide on secure old hard drive disposal provides actionable steps.
Hidden Physical and Environmental Dangers
Beyond data security, retired IT assets contain tangible physical hazards. To fully appreciate the dangers within e-waste, particularly in devices with batteries, it's critical to understand what thermal runaway is—a violent, fire-starting chemical reaction that can occur in lithium-ion batteries. Improperly storing old laptops and servers can create a serious fire risk within your facility.
Furthermore, these devices are laden with toxic materials like lead, mercury, and cadmium. If improperly discarded, these toxins can leach into the soil and groundwater, causing long-term environmental damage and potential liability for your company. A professional ITAD partner is not just insurance against a data breach; it’s your safeguard against these severe financial, legal, and environmental threats.
Your Step-by-Step Secure ITAD Workflow
Executing IT asset disposal correctly requires a proven, step-by-step process that protects your business from start to finish. This workflow is a blueprint for transforming a chaotic collection of old tech into a secure, compliant, and even profitable operation. Each step is a link in a chain of custody, creating an unbroken line of security from your facility to the final recycling plant.
For any business, formalizing this workflow is the single most important part of retiring technology. It eliminates guesswork, assigns clear responsibility, and ensures no device—or the sensitive data on it—is unaccounted for. This methodical approach is your best defense against the financial penalties and reputation damage that result from a mishandled disposal.
A single misstep can trigger a cascade of serious problems, including financial loss, regulatory fines, and lasting damage to your brand.
This is why a secure, fully documented workflow is not just a best practice—it is an operational necessity.
1. Initial Asset Inventory and Tracking
You cannot secure what you do not track. The first step in any professional ITAD workflow is a thorough inventory. This involves creating a detailed manifest of every asset slated for retirement, logging key details such as serial numbers, asset tags, device types, and physical locations.
This inventory serves as the foundation for all subsequent actions. Of course, this process assumes a secure environment from the outset; strong layered data center security strategies are critical for protecting assets throughout their life cycle. Once inventoried, each asset is tagged and its status updated in your management system, officially commencing its retirement journey.
2. Certified On-Site Data Sanitization
With the inventory complete, the next mission is data destruction. This is arguably the most critical stage, where you ensure your sensitive corporate information is irretrievably destroyed. For most businesses, performing this on-site provides the highest level of security, as sensitive data never leaves your premises intact.
Certified data sanitization uses specialized software to overwrite a hard drive multiple times with random data, rendering the original information unrecoverable. The industry benchmark is the DoD 5220.22-M standard, a protocol that uses a three-pass overwrite method to ensure total data eradication. This software-based approach is ideal for assets that may be resold or reused, as it preserves the hardware's integrity while guaranteeing data security.
3. Physical Hard Drive and Media Destruction
In some cases, software-based wiping is not the appropriate solution. For hard drives that have failed, are too old to have resale value, or contained exceptionally sensitive data, physical destruction is the only method to be 100% certain the information is permanently gone.
This process utilizes industrial-grade shredders to pulverize hard drives, SSDs, backup tapes, and other media into small, mangled fragments. Once a drive has been physically shredded, there is zero possibility of data recovery.
The choice between wiping and shredding is a critical risk management decision. Wiping enables value recovery from the asset, while shredding provides the ultimate security guarantee for high-risk data or non-functional drives. A qualified ITAD partner will help you determine the optimal approach for each asset.
Data Destruction Methods Compared
Selecting the appropriate data destruction method is key to a secure disposal strategy. This table outlines the three primary options to help your business decide what best fits its security needs, compliance mandates, and asset portfolio.
| Method | Description | Best For | Compliance Level |
|---|---|---|---|
| Data Wiping/Erasure | Uses specialized software to overwrite existing data multiple times, making it unrecoverable. | Reusable assets (laptops, servers) where value recovery is a priority. | High |
| Physical Shredding | Mechanically destroys the drive by grinding it into small metal fragments. | End-of-life or damaged drives, or for the highest level of data security. | Highest |
| Degaussing | Exposes magnetic storage media to a powerful magnetic field, scrambling the data pattern on the platters. | Magnetic tapes and older hard drives (not effective on SSDs). | High |
Ultimately, a blended approach using these methods, guided by a professional ITAD vendor, will yield the most secure and cost-effective outcome for your organization.
4. Secure Logistics and Chain of Custody
Once data has been sanitized or the drives destroyed, the physical hardware must still be transported. This is where an unbreakable chain of custody becomes critical. It is a formal, documented trail that records every individual who handles your assets, from the moment they leave your facility until they reach their final disposition.
A secure logistics plan includes:
- Secure, locked, and sealed containers for all transport.
- GPS-tracked vehicles to monitor the shipment in real-time.
- Background-checked, uniformed security personnel handling the assets.
- Detailed logs signed at every handoff point.
A robust chain of custody is your verifiable proof that no asset was lost, stolen, or tampered with en route. This documentation is non-negotiable for any compliance audit.
5. Asset Remarketing for Value Recovery
Do not assume your retired IT equipment is worthless. Much of it, especially servers, laptops, and networking hardware that are only a few years old, retains significant resale value. A strategic ITAD program can turn this equipment into a source of revenue.
Your ITAD partner will test, refurbish, and sell these functional assets on secondary markets. A portion of the proceeds is then returned to your business, helping to offset—or even completely cover—the costs of the disposal service.
6. Certified Recycling and Full Reporting
The final step is the responsible disposition of all materials that cannot be resold. This involves sending the remaining components to a certified electronics recycler who will break them down into their constituent commodities—such as plastics, metals, and glass—for reuse in new products. This process keeps hazardous e-waste out of landfills and ensures your company fulfills its environmental obligations.
Upon completion, you should receive a comprehensive reporting package. This final documentation is your proof of a secure and compliant process and must include:
- A final, serialized inventory of every asset processed.
- Certificates of Data Destruction for each drive that was wiped or shredded.
- The complete chain of custody log.
- Certificates of Recycling to confirm environmental compliance.
This reporting closes the loop on every asset and provides the auditable proof required by regulators, auditors, and executive leadership. For a closer look at retiring server hardware, our detailed server decommissioning checklist is an excellent resource to ensure no detail is overlooked.
How to Choose the Right ITAD Partner in Atlanta
Selecting a partner for your IT asset disposal is more than a logistical choice—it’s a critical security decision. The right vendor acts as an extension of your team, shielding your business from liability. The wrong one can expose your Atlanta-based company to staggering financial and reputational risks.
This decision should not be based on the lowest pickup fee. It requires a careful vetting of a partner's security protocols, compliance certifications, and logistical capabilities to ensure they can fully protect your organization. You need a provider who delivers a transparent, secure, and completely auditable process from initial pickup to final reporting.
Verifying Industry Certifications
Certifications are your first line of defense against unqualified vendors. They provide independent, third-party validation that a company adheres to strict industry standards for both data security and environmental processing. They should be considered a non-negotiable requirement.
For any business in Atlanta, two certifications represent the gold standard:
- R2 (Responsible Recycling): This certification ensures a vendor follows best practices for electronics recycling, covering environmental safety, worker health, data security, and downstream material tracking.
- e-Stewards: Often regarded as the most stringent standard, e-Stewards certification guarantees that no hazardous e-waste is illegally exported and that all data is handled with the highest level of security.
When you engage a certified partner, you are not just hiring a disposal service; you are investing in a proven framework for risk management. These certifications are your assurance that their entire operation has been audited and verified by an independent body.
Before signing any agreement, request copies of their current certification documents. Any reputable vendor will readily provide them.
Confirming Data Destruction Standards
Your data is your most valuable and vulnerable asset. Its complete and permanent destruction is the primary objective of any ITAD project. You must be certain that a potential partner’s methods meet or exceed established government and industry benchmarks.
The most recognized standard is DoD 5220.22-M, a three-pass data overwrite protocol developed by the Department of Defense. This method effectively sanitizes hard drives, making data recovery virtually impossible. Inquire if potential vendors provide this level of wiping and if they also offer physical shredding for failed drives or media that contained highly sensitive information.
Assessing On-Site Service Capabilities
Your assets are most secure when they are within your own facility. A top-tier ITAD partner understands this and should offer a full suite of on-site services to eliminate the risk of data exposure during transit. This is especially critical for organizations in healthcare or finance that must maintain a flawless chain of custody.
Key on-site services to look for include:
- On-site data wiping: Sanitizing hard drives before they leave your premises.
- On-site hard drive shredding: Bringing a mobile shredding truck to your location for ultimate security.
- Professional de-installation and packing: Safely and efficiently removing servers, racks, and other complex infrastructure.
Offering these services demonstrates a vendor's commitment to a security-first methodology, allowing you to witness the destruction of your data firsthand.
Scrutinizing Chain-of-Custody Documentation
An unbroken chain of custody is your documented proof that every asset was securely handled at every stage of the process. This is not a simple receipt; it's a detailed, serialized log that tracks each device from your facility to its final disposition.
A proper chain-of-custody report must include:
- Serialized inventory lists of all collected assets.
- Signatures at every point of transfer.
- Secure, GPS-tracked transportation logs.
- Final Certificates of Data Destruction and Recycling for your records.
This documentation is what you will rely on to pass compliance audits and demonstrate due diligence. If a vendor is vague about their process or cannot provide detailed sample reports, it is a significant red flag. To see what a responsible process entails, reviewing the services of a certified electronic waste recycling company can provide a valuable benchmark.
Ultimately, a reliable partner will welcome scrutiny. Ask them directly: "Can you provide a serialized Certificate of Data Destruction for every single data-bearing asset you process?" Their response will reveal their commitment to accountability.
Custom ITAD Solutions for Atlanta Industries
Not all IT asset disposal challenges are the same. A large hospital system in Atlanta faces entirely different compliance and data security requirements than a university refreshing thousands of student laptops. A one-size-fits-all approach to ITAD is ineffective; different industries require specialized strategies that address their unique operational realities, regulatory burdens, and hardware profiles.
A secure and effective plan hinges on understanding these distinctions. An experienced ITAD partner recognizes that the definition of "sensitive data" and the logistics of equipment removal vary dramatically between sectors. This tailored approach is what transforms a potential liability into a well-managed, secure business process.
Healthcare ITAD: HIPAA Compliance and Beyond
For Atlanta's healthcare providers, IT asset disposal is fundamentally a matter of patient safety and stringent legal compliance. The Health Insurance Portability and Accountability Act (HIPAA) imposes severe penalties for data breaches involving Protected Health Information (PHI). This data resides not only on servers but on network appliances, medical devices, and administrative workstations.
A single improperly discarded hard drive containing patient records can trigger a multi-million-dollar fine and cause irreparable reputational damage. A healthcare-focused ITAD program must therefore prioritize absolute, verifiable data destruction.
This requires:
- Guaranteed Data Destruction: Employing DoD 5220.22-M 3-pass wiping for reusable assets and on-site physical shredding for failed drives or devices that stored highly sensitive PHI.
- Complete Audit Trails: Providing serialized Certificates of Data Destruction for every data-bearing asset to create an unbreakable audit trail for HIPAA compliance.
- Specialized Equipment Handling: Possessing the expertise to securely retire specialized medical equipment, which often contains embedded storage media.
Education Sector: Logistics and Student Privacy
Educational institutions, from K-12 districts to large universities, manage enormous fleets of devices. Their primary challenge is logistical—decommissioning thousands of laptops, desktops, and tablets simultaneously during academic breaks. Concurrently, protecting student data under regulations like the Family Educational Rights and Privacy Act (FERPA) is a critical priority.
An effective ITAD solution for the education sector must be designed for security and efficiency at scale. This involves coordinating large-scale pickups from multiple campus locations, providing secure on-site storage during transitions, and ensuring every device is meticulously tracked. The goal is to minimize disruption while maximizing the financial return on still-valuable equipment, which can help fund the next generation of technology for students.
Data Center Decommissioning: Maximizing Value
Data centers are the engines of the digital economy, and decommissioning one is a monumental undertaking. This process involves removing hundreds or even thousands of servers, storage arrays, and networking switches—all filled with enterprise-grade hardware and mission-critical data. For data center operators, the primary objectives are speed, security, and maximizing financial value recovery.
A successful data center decommissioning project is a precise, military-style operation. It demands meticulous planning to ensure a swift, secure removal of assets with minimal operational disruption, all while extracting the maximum possible value from enterprise-grade hardware.
The global ITAD market underscores the scale of this need. The industry was valued at USD 17.5 billion in 2025 and is projected to reach USD 40.1 billion by 2035. Large enterprises drive 66.9% of that market share through their massive hardware refresh cycles. You can explore more data on these trends and discover market insights from industry analysts.
By partnering with a vendor skilled in asset remarketing, data centers can transform a complex decommissioning project into a significant revenue event, offsetting project costs and providing a substantial boost to the IT budget. For businesses in any of these sectors, understanding the local options for managing this process is crucial for responsible operations. You can learn more about professional electronics recycling in Atlanta to see how a certified partner handles these diverse industry needs.
Common Questions About IT Asset Disposal
Even with a well-defined plan, the execution of IT asset disposal can raise practical questions. For most Atlanta businesses, the final step before engagement is clarifying the details—the difference between service types, cost structures, and true compliance requirements.
Obtaining clear answers to these common questions demystifies the process and highlights the value a professional ITAD partner provides.
What Is the Difference Between ITAD and E-Waste Recycling?
While related, ITAD and e-waste recycling are driven by fundamentally different objectives. E-waste recycling is primarily focused on environmental responsibility. Its main function is to safely dismantle old electronics to recover commodities and keep hazardous materials out of landfills. It is a critical component of corporate sustainability.
IT Asset Disposal (ITAD), however, is a comprehensive, security-first business strategy. Its core priorities are guaranteed data destruction, maintaining a secure chain of custody, and recovering financial value from reusable assets. Responsible recycling is simply the final step in a robust ITAD plan, not the entire process.
Is Software-Based Data Wiping Enough to Be Compliant?
For meeting strict standards like HIPAA, simply deleting files or performing a factory reset is grossly insufficient. That data is easily recoverable with basic software tools. Professional ITAD services must use certified data sanitization methods, such as the DoD 5220.22-M standard, which overwrites data multiple times until it is completely unrecoverable.
However, for failed drives, legacy equipment with no resale value, or devices that stored highly sensitive data, physical destruction is the only method that provides 100% certainty. This is where industrial shredding is necessary.
A trustworthy ITAD partner will provide a serialized Certificate of Destruction to formally document either process. This certificate is your official record for any compliance audit, proving you met your legal obligations for data security.
Can We Actually Make Money from Our Old IT Equipment?
Yes. This is one of the most significant and often overlooked benefits of a strategic ITAD program. Many retired assets, particularly enterprise-grade servers, networking gear, and laptops that are only a few years old, retain substantial value on the secondary market.
A professional partner has established market channels and the technical expertise to:
- Test and grade all incoming equipment.
- Refurbish functional assets to maximize their resale price.
- Sell the equipment through a global network of buyers.
A portion of that revenue is then shared back with your company. In many cases, the financial return can offset or even exceed the cost of the service, transforming a compliance requirement into a revenue-generating activity.
How Much Does a Professional IT Asset Disposal Service Cost?
The cost of ITAD services is influenced by factors like the volume and type of equipment, the scope of on-site work required (e.g., de-installation or shredding), and logistics. However, viewing ITAD as a simple expense is a strategic error. It is an investment in risk management.
Consider this: the potential fines from a single data breach or compliance failure can easily reach six or seven figures. Compared to that catastrophic risk, the cost of a professional service is a minor and justifiable business expense. Furthermore, as noted above, the value recovered from resold assets can often cover the entire service cost, effectively making the process budget-neutral or even profitable.
Ready to implement a secure, compliant, and value-driven ITAD strategy for your Atlanta business? Atlanta Computer Recycling offers end-to-end solutions, from on-site data destruction to certified recycling, all tailored to your industry's specific needs. Protect your data and recover hidden value from your retired assets. Contact Atlanta Computer Recycling today to schedule your free consultation.