Hard drive destruction service: Secure, compliant data retirement for your business

When your company’s IT assets reach their end-of-life, what happens to the sensitive corporate data left on them? A professional hard drive destruction service is your guarantee that this information is permanently and physically destroyed, making it 100% unrecoverable. This is no longer just an IT task; it’s a core security and risk management function for any business upgrading or retiring old equipment. Simply deleting files or formatting drives is not a viable security strategy and leaves a backdoor open for catastrophic data breaches.
Why Simply Deleting Files Is a Major Business Risk
Looking at a fleet of decommissioned office computers, it's tempting to assume a factory reset is sufficient. That’s a ticking time bomb for your organization. The common belief that hitting "delete" makes a file vanish is a dangerous myth, and it’s one that exposes companies to massive financial and reputational harm.
Think of a hard drive like a corporate ledger. When you “delete” a file, you aren’t erasing the entries. You’re just removing that section from the table of contents. The information itself—your sensitive corporate data—is still present on the disk, waiting for anyone with basic recovery software to reconstruct it. Our guide on how to delete a hard drive digs deeper into why these common methods fail to meet business security standards.
The Hidden Dangers in Retired IT Assets
Every single discarded server, laptop, or desktop contains a detailed history of your business operations. This "ghost data" can be anything from financial statements and employee PII to intellectual property and trade secrets. Leaving this information intact on retired hardware isn't just poor data hygiene—it's a direct threat to your company’s solvency and reputation.
The fallout from a data breach originating from improperly disposed assets can be devastating. A single incident can spiral into:
- Crippling Financial Penalties: Fines for non-compliance with regulations like HIPAA, GDPR, or FACTA can easily run into the millions.
- Irreparable Brand Damage: Losing customer and partner trust can cause far more long-term harm than any fine, leading to a damaged reputation and lost revenue for years to come.
- Legal and Operational Chaos: Your business could become mired in lawsuits, forensic investigations, and mandatory public notifications that grind your operations to a halt.
Shifting from IT Task to Business Strategy
This is precisely why a professional hard drive destruction service should be viewed as a critical component of your business strategy, not just an item on the IT department's checklist. The demand for these services is exploding for a reason. The global market for hard drive destruction hit USD 1.5 billion and is expected to climb to USD 3.6 billion by 2032. What’s driving this growth? The staggering cost of failure, with the average data breach now costing an organization USD 4.45 million.
A proactive approach to data destruction is your best defense. Instead of reacting to a breach, you are actively preventing one from ever happening by ensuring that sensitive information ceases to exist in a recoverable form.
Recognizing these risks is the first step. The next is to integrate a secure disposition plan into your overall security framework, such as building a robust cybersecurity incident response plan. By physically shredding your old storage media, you completely eliminate the risk of data recovery. You turn a potential liability into a pile of harmless, recycled materials, guaranteeing your company's confidential information is gone forever.
Choosing Your Destruction Method: Shredding, Degaussing, and Wiping
When it’s time to retire business hardware, simply deleting files isn’t enough. Not all data disposal methods are created equal, and choosing the wrong one can leave your company’s most sensitive information dangerously exposed.
Understanding the fundamental differences between software wiping, degaussing, and physical shredding is a critical step in corporate data governance. Each approach works on a completely different principle, and the right choice hinges on your security requirements, the type of media being retired, and your industry’s specific compliance mandates.
Let's break down how they stack up for a commercial environment.
Software Wiping: The Digital Overwrite
Software wiping, or data erasure, uses specialized programs to methodically overwrite every sector of a hard drive with random data, often in multiple passes. This process is designed to bury the original information under layers of meaningless code, making it extremely difficult to recover.
This method makes sense for businesses looking to reuse or resell older equipment within a circular economy model. However, its effectiveness is only as good as the software used and the rigorous verification process that follows. For devices that are old, non-functional, or at the end of their useful life, wiping isn't always the most secure or cost-effective solution. You can learn more in our guide on how to wipe a hard drive clean.
Degaussing: The Magnetic Scramble
Degaussing uses brute force to neutralize the magnetic fields on the platters inside traditional hard disk drives (HDDs). A degausser is an industrial machine that generates an incredibly powerful magnetic field, instantly and permanently scrambling the magnetic coating where your data is stored.
The process is fast, effective for HDDs, and renders the drive completely inoperable.
The critical weakness of degaussing is its complete ineffectiveness on modern Solid-State Drives (SSDs). SSDs don’t store data magnetically; they use flash memory chips. A powerful magnetic field will have zero effect on the data stored on an SSD, leaving all sensitive corporate information perfectly intact.
This makes degaussing a highly specialized tool that is becoming obsolete as more businesses transition their IT infrastructure to SSDs. Relying on it without a clear understanding of your media inventory is a massive security gamble.
Physical Shredding: The Ultimate Failsafe
When data absolutely cannot be allowed to fall into the wrong hands, physical destruction is the only foolproof method. A professional hard drive destruction service uses industrial-grade shredders to literally tear storage devices into tiny, unrecognizable pieces of metal and plastic.
This is the data destruction equivalent of incinerating a sensitive corporate document. There are no ones and zeros to recover, no platters to analyze, and no memory chips left to read. The data—and the drive it lived on—ceases to exist in any recoverable form.
This method is the gold standard for corporate data security for several key reasons:
- It’s Irreversible: Once a drive is shredded, the data is gone forever. Reconstruction is physically impossible.
- It’s Versatile: Shredding works equally well on traditional HDDs, modern SSDs, backup tapes, mobile devices, and other data-bearing media.
- It’s Verifiable: Your team can witness the destruction process firsthand, providing undeniable proof that your data has been permanently eliminated and satisfying audit requirements.
For organizations in highly regulated industries like healthcare, finance, or defense, the absolute certainty that physical shredding provides is non-negotiable.
Data Destruction Method Comparison
Choosing the right data destruction method is crucial for protecting your business. This table breaks down the key differences between software wiping, degaussing, and physical shredding to help you make an informed decision based on your security and compliance needs.
| Method | How It Works | Best For | Effectiveness on SSDs | Compliance Level | Key Weakness |
|---|---|---|---|---|---|
| Software Wiping | Overwrites existing data with random ones and zeros. | Devices intended for reuse or resale. | Effective, but can be complex and time-consuming. | High, with proper verification. | Requires 100% verification to ensure no data remnants remain. |
| Degaussing | Uses a powerful magnetic field to scramble data on platters. | Rapidly disabling large quantities of traditional HDDs. | Completely Ineffective. Does not erase data on SSDs. | Varies; Not compliant for SSDs. | Is obsolete for non-magnetic media like SSDs. |
| Physical Shredding | Grinds the entire device into small, irrecoverable fragments. | Highest security needs; obsolete or damaged media. | 100% Effective. Destroys the physical storage chips. | Highest level of compliance. | The device cannot be reused in any capacity. |
Ultimately, physical shredding offers the highest level of security and complete peace of mind. It removes all doubt and provides a definitive, compliant end to your data's lifecycle, protecting your business from the catastrophic consequences of a data breach.
On-Site vs. Off-Site Destruction & The All-Important Chain of Custody
When you hand over retired corporate assets, their journey isn't over. The critical question for any risk manager or IT director is how to guarantee security from your facility to its final, fragmented end. This is where you face a key operational choice: on-site or off-site hard drive destruction.
The decision boils down to a simple question: where do you require the physical destruction to occur? Your answer shapes the entire engagement, from vendor selection to the level of assurance you have that your corporate data is irretrievably destroyed.
On-Site Destruction: The Ultimate Verification
On-site destruction brings the shredder directly to your business premises. A specialized, mobile shredding truck arrives at your facility, and your hard drives are destroyed right there under your team's supervision. You can physically witness each drive get fed into an industrial-grade shredder and turned into a pile of useless metal scraps.
This method offers unrivaled peace of mind and the strongest possible chain of custody. There’s zero risk of data exposure during transit because the drives never leave your property intact. For businesses in tightly regulated sectors like healthcare, finance, or legal services, witnessing the destruction is often a strict compliance requirement.
The demand for this level of assurance is growing rapidly. On-site data destruction is on track to capture 64% of the market. This trend is driven by heightened privacy concerns and the need for businesses to close any potential security gaps during transport and satisfy regulators like those enforcing HIPAA.
Off-Site Destruction and the Critical Chain of Custody
The alternative is off-site destruction, where a certified vendor collects your hardware and transports it to their secure facility for shredding. While you don't witness the event yourself, this is an incredibly secure process when it’s managed with a bulletproof chain of custody.
Think of the chain of custody as a detailed evidentiary log that tracks your hard drives from the moment they leave your control to their final destruction. It’s the foundation of trust for any off-site service and a critical piece of your compliance documentation.
A secure chain of custody isn't just a promise; it's a documented process. It ensures every touchpoint is secure, logged, and verifiable, creating an unbroken audit trail that proves compliance and protects your business from liability.
A vendor with a solid chain of custody will follow a strict protocol:
- Secure Collection: Drives are immediately placed into sealed, locked, and tamper-evident containers before leaving your office.
- GPS-Tracked Transport: The vehicle carrying your assets is tracked by GPS, providing a real-time, auditable log of its entire route.
- Secure Facility: The destruction facility itself has restricted access, 24/7 video surveillance, and strict operational protocols for all employees.
- Documented Verification: Every single step—from pickup and transport to arrival and the final shred—is documented with timestamps and signatures.
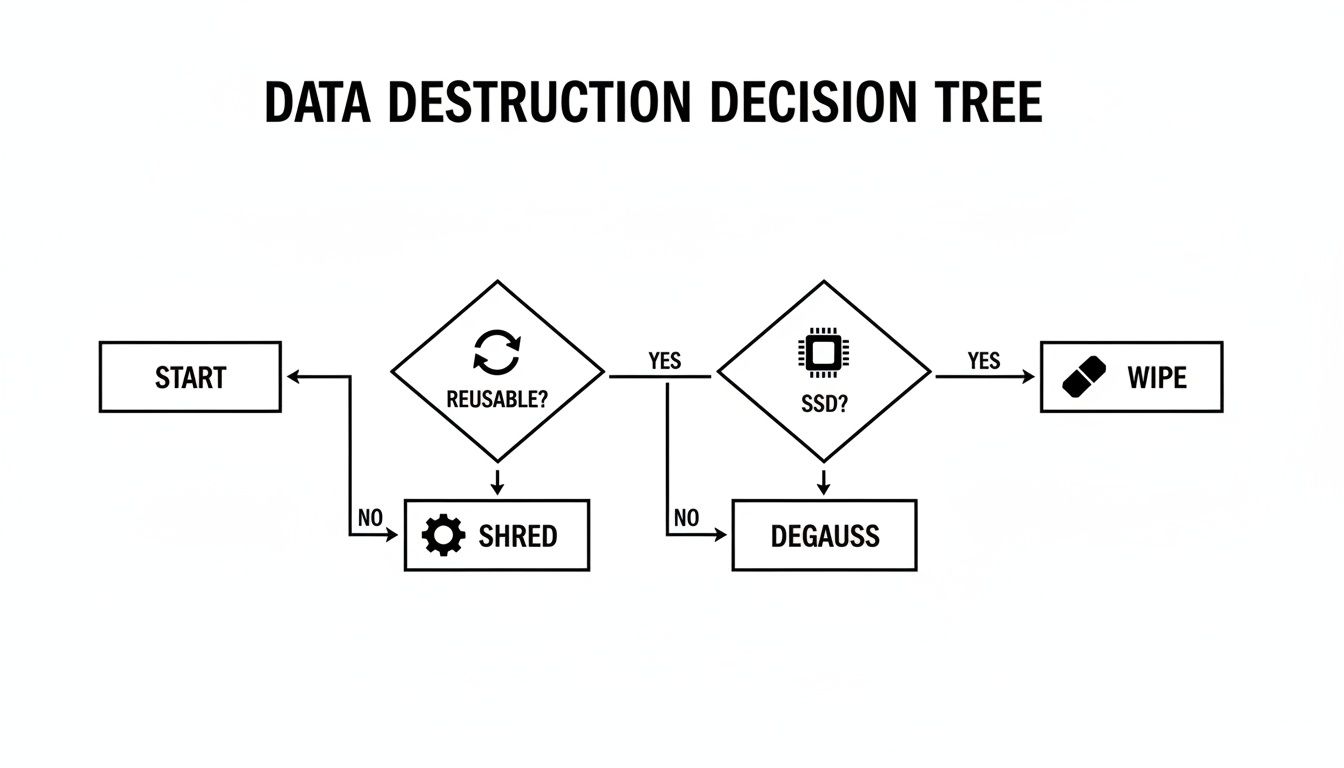
Choosing between on-site and off-site often comes down to a business decision. Does your risk profile or compliance framework demand the immediate, visual confirmation of on-site shredding, or does the logistical efficiency of a secure off-site process meet your requirements? This decision tree can help you visualize which path makes the most sense.
As the chart shows, the right method often depends on whether a device is reusable and its technology (like an HDD vs. an SSD).
Both on-site and off-site services can deliver secure, compliant destruction, but only if the processes are ironclad. As you weigh your options, you can learn more about local on-site shredding services to see how it works for businesses here in Atlanta. By understanding the details, you can confidently choose the right partner and method to protect your organization's most valuable asset: its data.
Meeting Compliance Mandates with Certified Destruction
For any modern business, disposing of old hard drives isn't just an IT task—it's a legal and regulatory obligation. A failure in this process is not a simple slip-up; it's a direct violation of federal and international laws that carry penalties stiff enough to cripple a company. Understanding these regulations is the first step to building a data retirement plan that is legally defensible.
At their core, most of these laws mandate the same outcome: when sensitive data reaches the end of its lifecycle, it must be made completely unreadable, indecipherable, and unusable. This requires a provable, permanent method of destruction.
Navigating Key Data Protection Laws
Several major regulations dictate exactly how businesses must handle and destroy data. While each has a different focus, they all demand strict end-of-life data security. A professional hard drive destruction service is structured to meet these precise standards.
-
HIPAA (Health Insurance Portability and Accountability Act): This is non-negotiable for healthcare organizations and their business associates. The HIPAA Security Rule requires that Protected Health Information (PHI) be rendered unreadable and indecipherable before disposal. Non-compliance can lead to fines running into the millions.
-
GDPR (General Data Protection Regulation): If your company handles the data of any EU resident, GDPR applies. It includes the "right to erasure," which means you must be able to completely and permanently delete an individual's data on request. Penalties for non-compliance are severe, reaching up to 4% of a company's global annual revenue.
-
FACTA (Fair and Accurate Credit Transactions Act): This federal law is designed to protect consumers from identity theft. It mandates that any document or device containing consumer information—such as credit reports or background checks—must be destroyed so thoroughly that the data cannot be reconstructed.
Violations have resulted in severe real-world consequences. In one infamous case, a healthcare system was fined $4.9 million after patient records were discovered in a public dumpster. It was a direct consequence of a failed in-house destruction process and a stark reminder of the financial and reputational stakes.
The Certificate of Destruction: Your Legal Proof
How do you prove to auditors and regulators that you have complied with these mandates? This is where the Certificate of Destruction becomes invaluable. It is much more than a receipt; it is a legally defensible record that serves as your official proof of compliance.
A Certificate of Destruction is your formal audit trail. It documents that your organization took responsible, verifiable steps to permanently destroy sensitive data, protecting you from liability in the event of a legal challenge or regulatory audit.
This critical document provides specific details, including the date and location of destruction, an inventory of the media destroyed (often by serial number), the destruction method used, and a signature from an authorized witness. Understanding the components of a valid Certificate of Destruction for hard drives is key, and our guide explains it in detail.
For any organization undergoing a security audit like SOC 2, this certificate is non-negotiable evidence. It demonstrates that your security controls extend through the entire data lifecycle, up to its final, secure disposition. For a deeper look into how auditors validate these processes, see this Ultimate Guide to SOC 2 Type 2 Compliance. When you partner with a certified destruction provider, you aren't just disposing of old hardware—you're reinforcing your entire security posture and building a bulletproof compliance record.
The Real Cost of Professional Data Destruction
What is the true price of risk mitigation for your business? When budgeting for a hard drive destruction service, it’s easy to focus on the line-item cost. But viewing this as a simple expense misses the strategic value. This isn't a cost; it's an investment in risk management.
While understanding the pricing structure helps with financial planning, the real ROI is measured in the disasters you prevent. The predictable, controlled cost of professional destruction is negligible compared to the astronomical, uncontained cost of a data breach. A modest operational expense today is your best insurance against a business-ending catastrophe tomorrow.
What Factors Influence the Price
The cost of professional hard drive destruction is not a single, fixed number. A few key variables determine the final price, allowing you to tailor the service to your specific operational needs and budget.
- Quantity of Drives: Volume is the primary pricing factor. Most providers offer tiered pricing, so the cost per drive decreases as the quantity increases. A project with 500 drives will have a significantly lower per-unit cost than one with only 20.
- On-Site vs. Off-Site Service: As covered earlier, on-site shredding (where a mobile shred truck comes to you) typically has a higher price point due to the added logistics, fuel, and dedicated equipment. Off-site destruction at a secure facility is often the more economical option.
- Special Reporting Needs: While a Certificate of Destruction is standard, if your compliance framework requires detailed asset tracking with serial number logging for every drive, this enhanced reporting will add to the total cost.
- Media Type: The pricing for standard hard drives is generally straightforward, but destroying other media like backup tapes, servers, or proprietary storage arrays may have a different pricing structure.
The demand for these services is growing rapidly for a reason. The global hard drive destruction market is projected to hit USD 5.05 billion, driven by heightened data security concerns and stringent regulations like GDPR, where fines can reach up to 4% of a company's global annual turnover. You can explore this market growth and its drivers in this detailed industry report.
The ROI of Preventing a Data Breach
Now, let's contrast the manageable cost of destruction with the chaotic, open-ended expense of a data breach. The numbers are staggering and powerfully illustrate the return on investment from professional shredding.
A single data breach now costs an average of $4.45 million. This isn't a theoretical, worst-case scenario; it's the statistical reality for hundreds of companies annually. Suddenly, the price of physically shredding your retired drives seems insignificant.
The costs of a breach spiral far beyond regulatory fines. Consider the financial chain reaction for your business:
- Regulatory Fines: HIPAA penalties alone can easily climb into the millions for failing to protect patient data.
- Legal Fees: Your business will be buried in legal battles, from class-action lawsuits to the cost of your own defense.
- Customer Churn: Trust is paramount. Once customers learn their data was compromised, a significant percentage will leave for competitors, impacting revenue for years.
- Brand Damage: The reputational damage can be the most lasting and costly consequence, making it incredibly difficult to attract new clients, partners, and talent.
When you invest in a certified hard drive destruction service, you are purchasing certainty. You are paying a small, fixed amount to completely eliminate the risk of these devastating and unpredictable outcomes. It’s one of the smartest, most cost-effective security decisions a business can make.
How to Choose the Right Destruction Partner
Selecting the right vendor is the final, and most critical, step in protecting your business from a data breach stemming from improper asset disposal. A true security partner does more than shred drives; they provide a documented, transparent, and fully auditable process that strengthens your organization's security posture. Making the right choice begins with asking the right questions—ones that separate a simple vendor from a genuine security expert.
This is not about finding the lowest bidder. It's about conducting thorough due diligence to ensure potential partners meet the highest standards of security, compliance, and professionalism.
The Non-Negotiable Vetting Checklist
When evaluating a hard drive destruction service, approach it as if you were hiring a key team member with access to your most sensitive information. Before signing any agreement, you need clear, direct answers to these crucial questions.
-
Are you NAID AAA Certified? This is the undisputed gold standard in the data destruction industry. NAID AAA Certification is not a one-time award; it signifies that the vendor is subject to surprise, unannounced audits that verify their security protocols, employee screening, and destruction processes. It is your independent assurance of their commitment to security.
-
Can you detail your chain of custody protocol? A vague answer to this question is a major red flag. A professional service should be able to articulate every step with confidence—from secure, locked collection bins and GPS-tracked vehicles to monitored facility access and strict receiving procedures.
The strength of your data security is only as good as the weakest link in the chain of custody. A detailed, transparent protocol is non-negotiable for ensuring your assets are protected from the moment they leave your sight until their final destruction.
Verifying a Partner’s Credentials
Beyond certifications, the operational details reveal a vendor’s true commitment to security. The personnel handling your sensitive media are just as important as the equipment they operate.
Ask these follow-up questions:
- Are your employees background-checked and trained? Any individual who may come into contact with your assets must have passed rigorous, recurring background checks. They should also receive formal, ongoing training on security protocols and compliance regulations. There should be no exceptions.
- Can you provide a sample Certificate of Destruction? This document is your legal proof that the job was done correctly. Scrutinize the sample. Does it include all essential details like unique serial numbers for each device, the date and location of destruction, and the signature of an authorized official?
An informed decision requires comparing qualified vendors. As you begin your search, our overview of vetted Atlanta-area electronic waste disposal companies can be a useful starting point.
Ultimately, the right partner won’t just answer these questions—they’ll answer them eagerly and in detail. They will demonstrate that they are not just another service provider, but a vital extension of your organization's security and compliance strategy.
A Few Common Questions About Hard Drive Destruction
When your business is considering professional hard drive destruction, a few key questions typically arise. These concerns center on ensuring the process is secure, efficient, and final. Here are clear, direct answers for a business audience.
Do I Need to Wipe My Hard Drives Before Shredding Them?
No, that is not necessary. Wiping a drive before shredding it is a redundant step. It's like redacting a document before putting it through a shredder.
The industrial shredding process physically demolishes the drive's data-holding platters and memory chips, making data recovery a physical impossibility. This single, decisive action is all that is required to achieve the highest level of data security.
How Can I Be Absolutely Sure My Data Is Gone for Good?
The best guarantee comes from partnering with a certified provider. A NAID AAA Certified vendor, for example, is held to the industry's most rigorous security standards, which are continuously verified through unannounced, third-party audits.
Your ultimate proof is the Certificate of Destruction. This is a legally defensible document that acts as your official audit trail. It details exactly what was destroyed, how, and when, protecting your business from any future liability.
Can You Destroy Things Other Than Hard Drives?
Absolutely. Professional destruction services are equipped to handle a wide variety of data-bearing media found in a corporate environment. This includes traditional hard drives (HDDs), modern solid-state drives (SSDs), backup tapes, USB flash drives, company smartphones, and even entire server units.
The same powerful shredding technology is used to ensure the data on any of these devices is permanently destroyed.
What Happens to All the Shredded Pieces Afterward?
The shredded material is not sent to a landfill. After destruction, the fragments of metal, plastic, and circuitry are securely transported to a certified recycling facility.
There, the materials are sorted and processed in accordance with strict environmental regulations. This final step ensures your data is not only secure but that the resulting e-waste is managed responsibly, supporting corporate sustainability goals and keeping hazardous materials out of landfills.
Ready to secure your company's data with a trusted, compliant process? Atlanta Computer Recycling offers certified on-site and off-site hard drive destruction services designed for businesses in the Atlanta area. Protect your organization, ensure compliance, and gain total peace of mind.
Schedule Your Secure Hard Drive Destruction Service with ACR Today